Vulnerabilities
-
 332
332Joomla! 3.7.1 is released to address a critical SQL Injection Vulnerability
A critical SQL Injection Vulnerability( CVE-2017-8917) with Joomla! 3.7, if you are Joomla user it’s you need to update immediately. Joomla! is a...
-
 139
139New Joomla SQL Injection Flaw Is Ridiculously Simple to Exploit
The Joomla CMS project released today Joomla 3.7.1 to fix an SQL injection flaw that allows attackers to execute custom SQL code...
-

 198
198Malware Uses Fake WordPress API Domain to Steal Sensitive Cookies
Security researchers from Sucuri have found hacked WordPress sites that were altered to secretly siphon off cookies for user and admin accounts...
-
 210
210You Can Steal Windows Login Credentials via Google Chrome and SCF Files
Just by accessing a folder containing a malicious SCF file, a user will unwittingly share his computer’s login credentials with an attacker...
-
 117
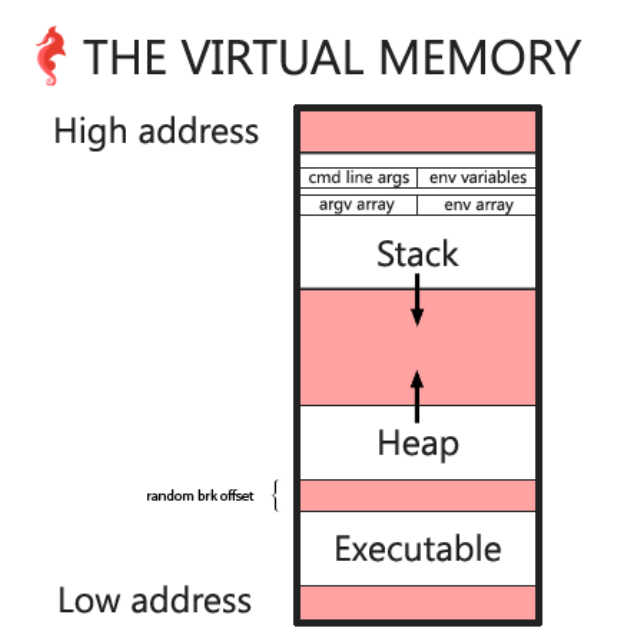
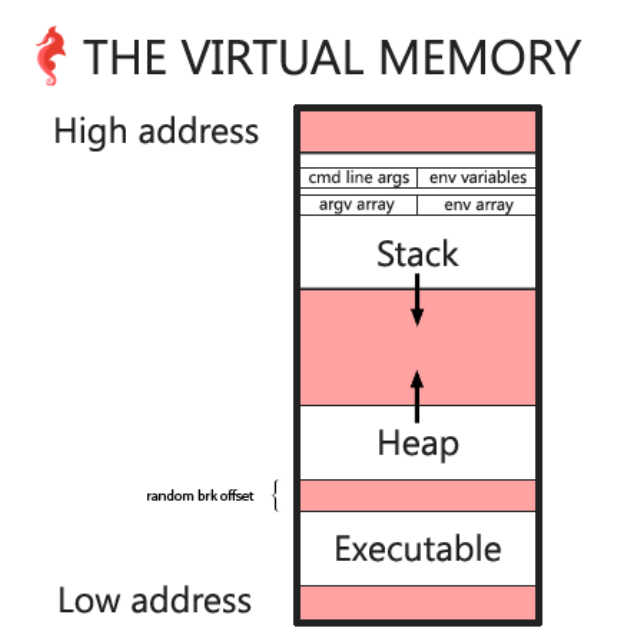
117Hack the Virtual Memory: malloc, the heap & the program break
The heap In this chapter we will look at the heap and malloc in order to answer some of the questions we...
-
 154
154New Shadow Brokers Message Teases Data From Nuke Programs, Windows 10 Exploits
Today, the Shadow Brokers have published a new message teasing new exploits for people who register for a new membership program the...
-

 190
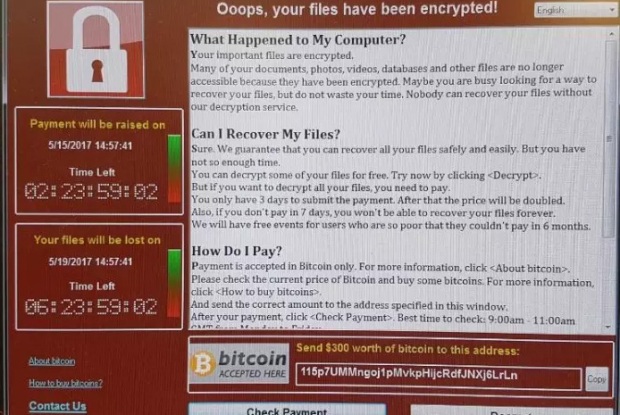
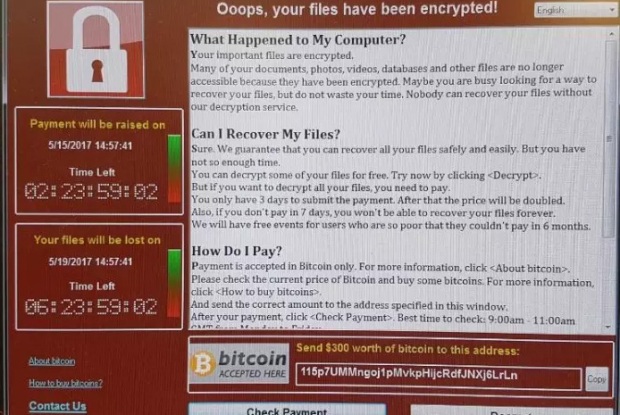
190Virulent WCry ransomware worm may have North Korea’s fingerprints on it
Identical code ties Friday’s attacks to hacks on Sony Pictures and $1bn bank heist. A researcher has found digital fingerprints that tie...
-
 119
119How To Protect Yourself From WannaCry Ransomware?
Short Bytes: WannaCry 2.0 or WannaDecrypt0r 2.0 ransomware is turning out to be one of the biggest security threats of recent times. It...
-

 90
90Why “Just Patch It!” Isn’t as Easy as You Think
At the Zero Day Initiative (ZDI), we see patches in a way few do. We get the initial report from a researcher,...
-

 199
199An NSA-derived ransomware worm is shutting down computers worldwide
Wcry uses weapons-grade exploit published by the NSA-leaking Shadow Brokers. A highly virulent new strain of self-replicating ransomware shut down computers all...
-

 100
100Vanilla Forums has a plain-flavoured zero-day
PHPMailer bug leads to remote code execution via HTTP. Updated The popular Vanilla Forums software needs patching against a remote code execution...
-

 196
196OnePlus OTAs: Analysis & Exploitation
In this blog post we present new trivial vulnerabilities found on OnePlus One/X/2/3/3T OxygenOS & HydrogenOS. They affect the latest versions (4.1.3/3.0)...
-
 185
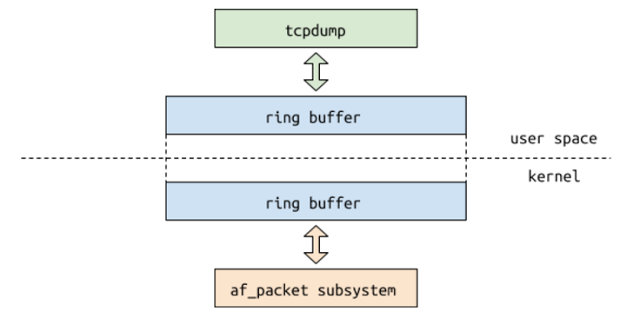
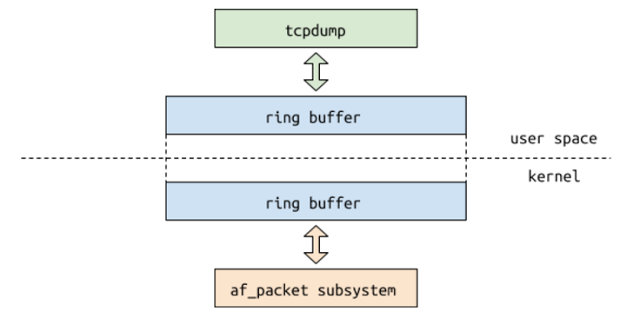
185Exploiting the Linux kernel via packet sockets
Lately I’ve been spending some time fuzzing network-related Linux kernel interfaces with syzkaller. Besides the recently discovered vulnerability in DCCP sockets, I...
-

 220
220Sednit adds two zero-day exploits using ‘Trump’s attack on Syria’ as a decoy
The Sednit group, also known as APT28, Fancy Bear and Sofacy, is a group of attackers operating since at least 2004 and...
-

 174
174SESSION HIJACKING, COOKIE-STEALING WORDPRESS MALWARE SPOTTED
Researchers have identified a strain of cookie stealing malware injected into a legitimate JavaScript file, that masquerades as a WordPress core domain....
-

 157
157iCloud Keychain vulnerability allowed hackers to Steal sensitive data
Apple has recently fixed an iCloud Keychain vulnerability that could have been exploited by hackers to steal sensitive data from iCloud users....
-
 189
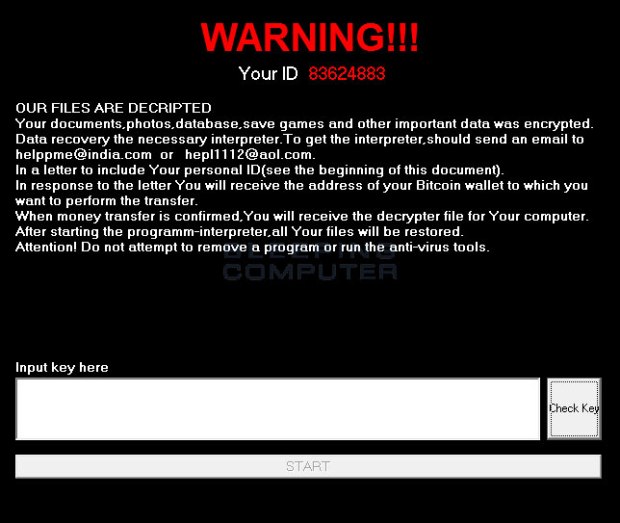
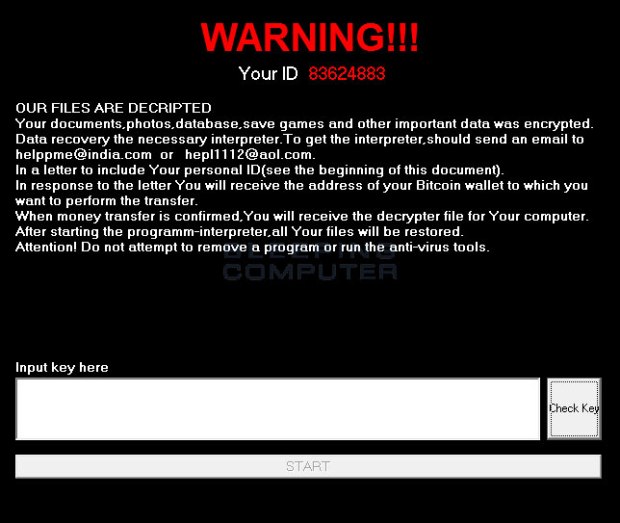
189RSAUtil Ransomware ([email protected]) Installed Via Hacked Remote Desktop Services
Today we are going to take a quick look at a new ransomware called RSAUtil that was discovered by Emsisoft malware researcher xXToffeeXx. RSAUtil is distributed...
-
 139
139Cisco patches switch hijacking hole – the one exploited by the CIA
Telnet security flaw fix finally lands – or just use SSH, yeah? Cisco has patched a critical security flaw in its switches...
-

 170
170HIKVISION PATCHES BACKDOOR IN IP CAMERAS
Hikvision, a Chinese manufacturer of video surveillance equipment, recently patched a backdoor in a slew of its cameras that could have made...
-

 110
110Snake malware ported from Windows to Mac
Snake, also known as Turla and Uroburos, is backdoor malware that has been around and infecting Windows systems since at least 2008....
-

 173
173Google Project Zero team the worst Windows RCE vulnerability in recent memory
Hackers at the Google Project Zero team have discovered another critical Windows RCE vulnerability, the worst Windows RCE in recent memory. Security...






