Vulnerabilities
-

 154
154iOS WebView Bug Can Force iPhones to Make Calls While UI Freezes
A bug in the iOS WebView component allows an attacker to force someone’s iPhone to dial any number, while also locking the...
-

 71
71D-Link DIR routers found with buffer overfow flaw
D-Link DIR model router’s Home Network Administration Protocol (HNAP) service contains a stack-based buffer overflow that has not been patched by the...
-
 98
98Google stops AdSense attack that forced banking trojan on Android phones
Malicious ads exploited zero-day flaw in Android that auto downloaded files. Google has shut down an operation that combined malicious AdSense advertisements...
-

 181
181How to Exploit Belkin WEMO gear to hack Android devices
Belkin’s WeMo home automation firmware that’s in use in several IoT devices has recently been found vulnerable to an SQL injection. Belkin’s...
-

 210
210Fix for critical Android rooting bug is a no-show in November patch release
Linux users already got a fix for “Dirty Cow.” Android users aren’t so fortunate. Android users waiting for a fix for a...
-

 194
194INSIDE THE RIG EXPLOIT KIT
Today’s most prolific exploit kit is RIG, which has filled a void left by the departure of Angler, Neutrino and Nuclear. That...
-

 77
77Bugging devices found at Iran nuclear talks hotel, say Swiss officials
A number of computers at a five-star Geneva hotel that has hosted sensitive talks, including Iranian nuclear negotiations, were found to be...
-

 92
92Cisco job applicants warned of potential mobile site data leak
Cisco has emailed users of its mobile careers site, warning of two occasions when their data could have been exposed. Users of...
-

 123
123How to block the ultrasonic signals you didn’t know were tracking you
Your phone can talk to advertisers beyond your back, beyond your audible spectrum. Dystopian corporate surveillance threats today come at us from all...
-

 153
153Universal hijack hole turns DIY Wix blogs into botnets
Communications failure leads to zero day, late patch, natch. Millions of do-it-yourself websites built with the Wix web maker were at risk...
-
 424
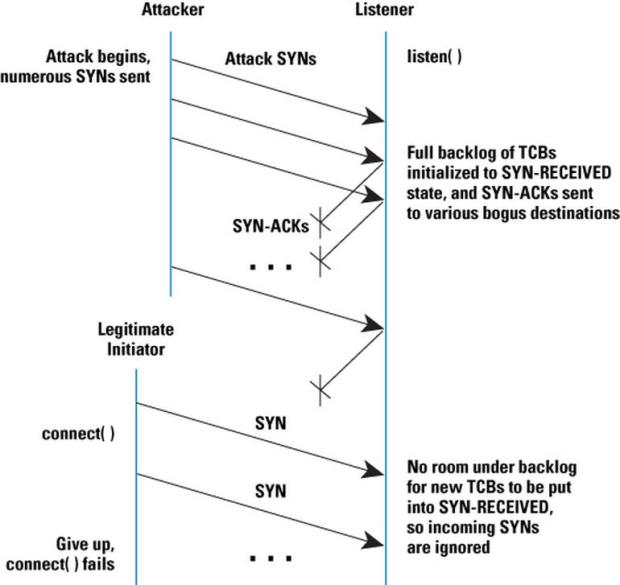
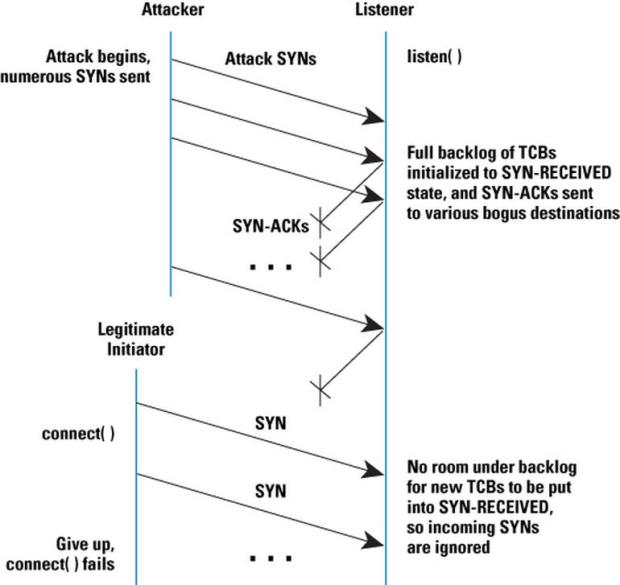
424Linux developers under denial of service attack
The Linux Plumbers Conference’s internet has been slowed to a crawl. SANTA FE, NM — If you can’t reach your favorite Linux...
-

 139
139Vulnerability Spotlight: Remotely Exploitable Bugs in Memcached Identified and Patched
Our efforts to make the internet safer and protect our customers involves, amongst many other things, researching and identifying zero-day vulnerabilities in...
-

 252
2520-day SAP vulnerability published, here’s what you can do
The information about a 0-day SAP vulnerability was published on LinkedIn on October 28, 2016. A researcher disclosed details of the vulnerability...
-

 195
195GOOGLE REVEALS WINDOWS KERNEL ZERO DAY UNDER ATTACK
A Windows zero-day vulnerability is being used in an unknown number of attacks, Google disclosed today, 10 days after it privately reported...
-
 170
170Joomla! readies patch for core vulnerability so critical it isn’t talking
Patch to drop 1400 UTC, Tuesday. And the haste of its release suggests this is scary. The world’s second-favourite content management system,...
-
 196
196It’s nearly 2017 and JPEGs, PDFs, font files can hijack your Apple Mac, iPhone, iPad
Apple has distributed a fresh round of security updates to address remote-code execution holes in iOS, macOS, Safari, and the firmware for...
-
 94
94Cracking of Sphinx Trojan DGA Opens the Door for Botnet Takedown
This post takes a quick look at Sphinx’s domain generation algorithm (DGA). Sphinx,another Zeus-based banking trojan variant, has been around circa August...
-
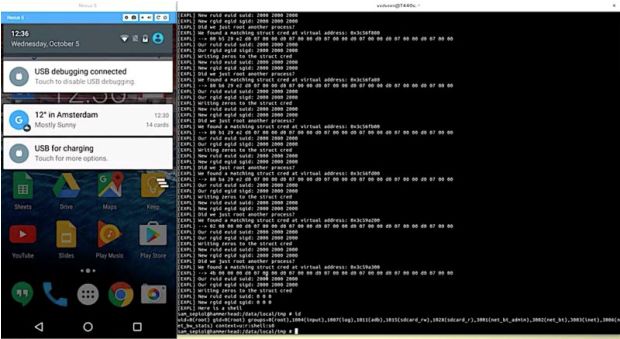
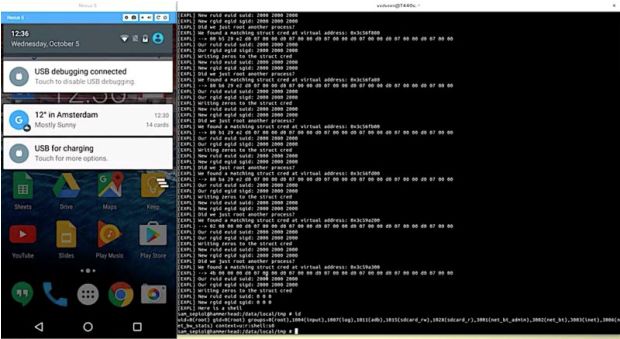 203
203Using Rowhammer bitflips to root Android phones is now a thing
Permission-less apps take only seconds to root phones from LG, Samsung and Motorola. Researchers have devised an attack that gains unfettered “root” access...
-

 104
104InTheCyber discovered a serious flaw in messaging systems
Researchers at InTheCyber firm have discovered a new easy exploitable and dangerous vulnerability affecting messaging systems. InTheCyber – Intelligence & Defense Advisors...
-

 69
69ADULT FRIENDFINDER VULNERABILITY LEAVES MILLIONS EXPOSED
Adult website Adult FriendFinder may have been compromised by a hacker who said he has gained access to the site’s backend servers and posted...
-
 102
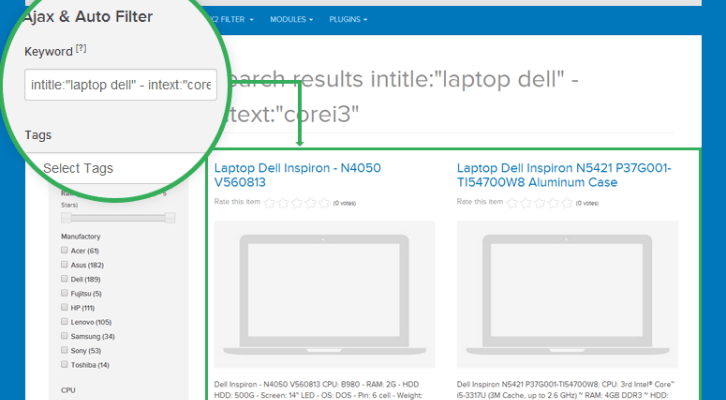
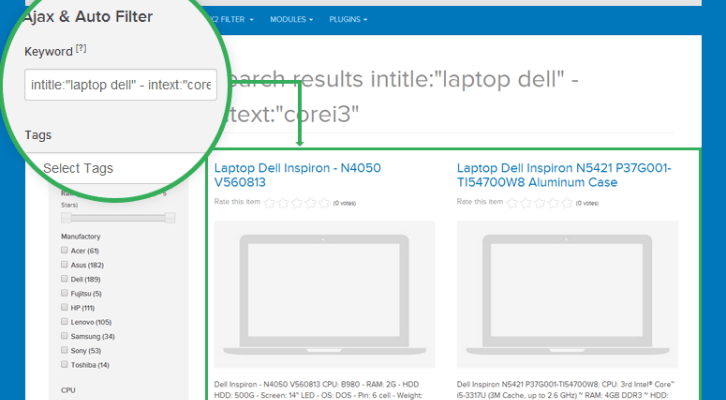
102SQL Injection zero-day in component ja-k2-filter-and-search of Joomla
Information Security experts have discovered an SQL injection zero-day vulnerability in Joomla component ja-k2-filter-and-search. Information Security Researchers Dimitrios Roussis and Evangelos Apostoloudis...






