Vulnerabilities
-

 298
298A flaw in the Yahoo Email service allowed hackers to access target’s emails
The Finnish security expert Jouko Pynnönen discovered a vulnerability in the Yahoo email service that allowed hackers to read anyone messages. A...
-

 223
223Uber asks to track your location even when you’re not using the app
The last update for the Uber app raises great concerns because it asks to track users’ location even when they’ve been dropped...
-

 87
87Porn website hacked, 380,000 accounts spilled online, xHamster claims fhack
xHamster is a free porn website and does not need details of credit or debit cards. If you are one of those...
-
 93
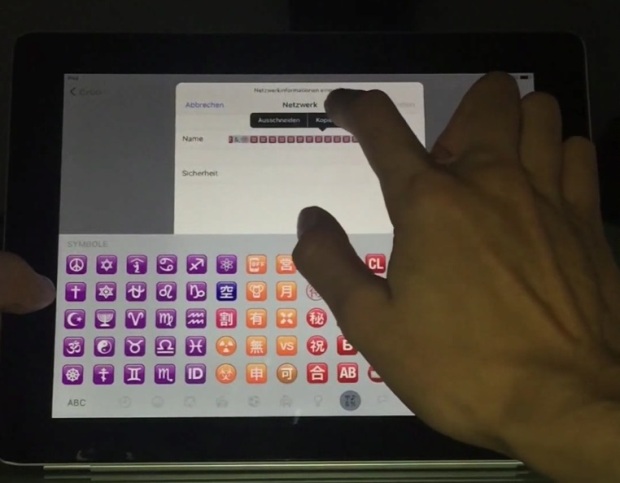
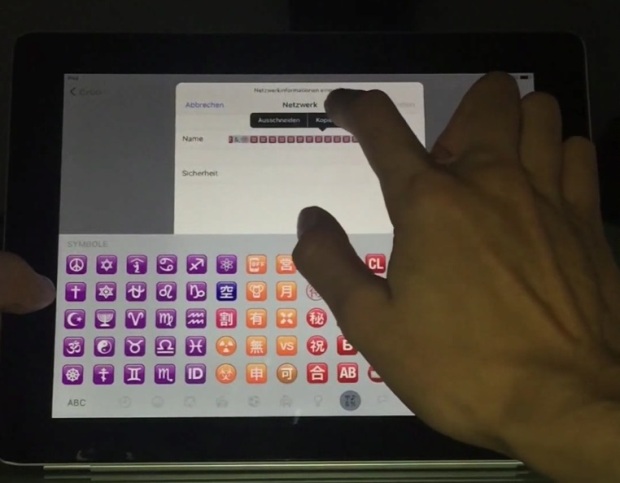
93Researchers Bypass Apple’s Activation Lock on iPhones and iPads
Two researchers have found a way to bypass the Apple Activation Lock on both iPhones and iPads, running the two most recent...
-
 134
134Mozilla and Tor release urgent update for Firefox 0-day under active attack
Critical code-execution flaw resides in Windows, Mac, and Linux. Patch now. Developers with both Mozilla and Tor have published browser updates that...
-

 168
168Firefox 0day in the wild is being used to attack Tor users
Publicly released exploit works reliably against a wide range of Firefox versions. There’s a zero-day exploit in the wild that’s being used...
-
 217
217PAYPAL FIXES OAUTH TOKEN LEAKING VULNERABILITY
PayPal fixed an issue that could have allowed an attacker to hijack OAuth tokens associated with any PayPal OAuth application. The vulnerability...
-
 134
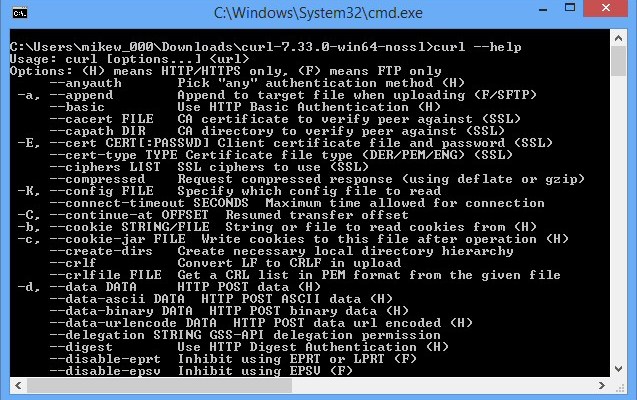
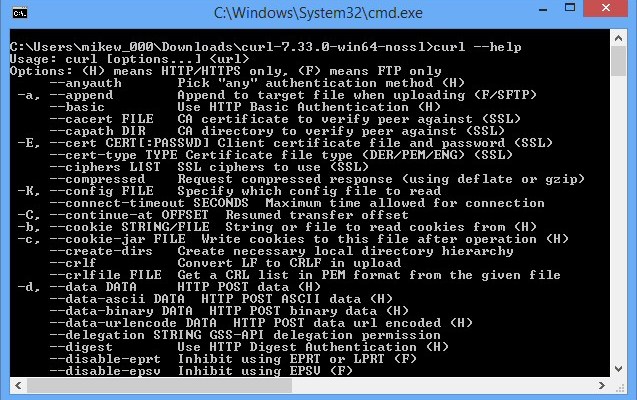
134An audit revealed dozen vulnerabilities in the cURL
Security experts who conducted an audit on cURL discovered nearly a dozen vulnerabilities that were patched in the last release. The cURL...
-

 197
197The Kangaroo Ransomware not only Encrypts your Data but tries to Lock you out of Windows
The Kangaroo ransomware is the latest ransomware from the developer behind the Apocalypse Ransomware, Fabiansomware, and Esmeralda. What makes this version stand...
-

 75
75Newly discovered router flaw being hammered by in-the-wild attacks
Researchers detect barrage of exploits targeting potentially millions of devices.Online criminals—at least some of them wielding the notorious Mirai malware that transforms...
-
 173
173Hacker found issues in Uber UberCENTRAL Tool that exposed user data
Bounty hunter Kevin Roh has discovered several security vulnerabilities in the Uber UberCENTRAL Tool that exposed user data. Security expert and bounty...
-

 223
223Hackers Hijack Madison Square Garden Payment Systems, Credit Card Data at Risk
MSG acknowledges attack aimed at its payment systems. “If you used the credit card to pay for items at Madison Square Garden...
-

 180
180Threat actors leverage InPage Zero-Day in targeted attacks in Asia
Security researchers from Kaspersky Lab are warning of targeted attacks with InPage zero-day against a number of organizations in Asia. According to experts...
-

 196
196EXPLOIT CODE RELEASED FOR NTP VULNERABILITY
A researcher has released a proof-of-concept exploit for a vulnerability in the Network Time Protocol daemon that could crash a server with...
-
 204
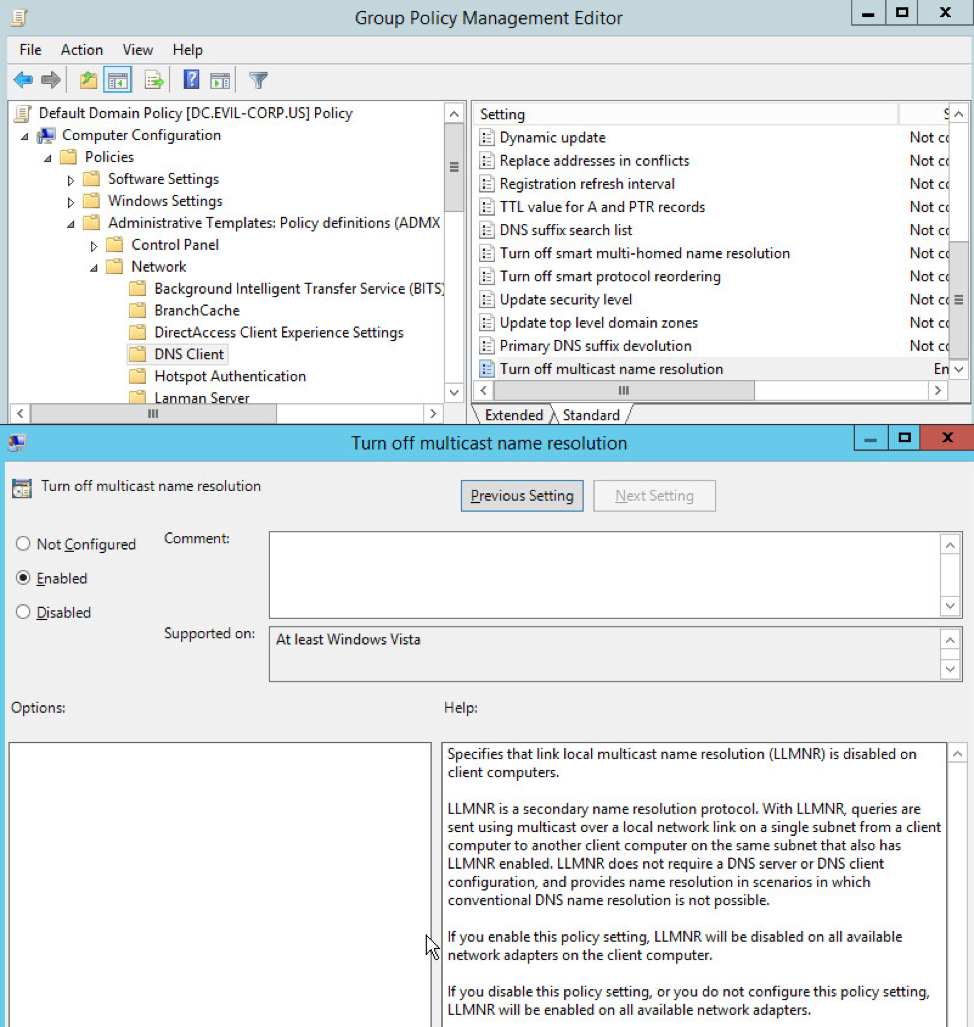
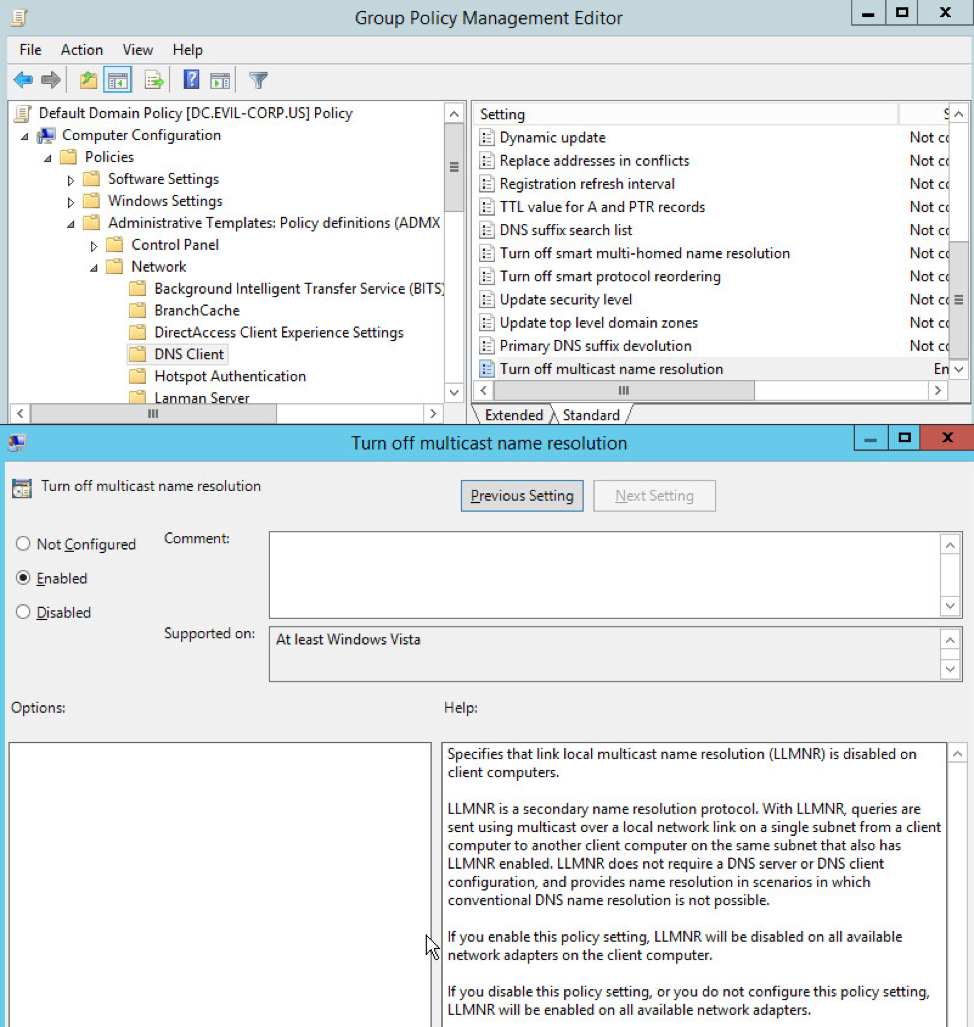
204BLOCKING LOCAL NETWORK HIJACKING ATTACKS
Adversaries who have compromised one system in a network frequently hijack the network traffic of other systems on the same subnet to...
-

 92
92Hackers Program Bank ATMs to Spew Cash
After crimes in Taiwan and Thailand, the FBI warns of similar potential attacks in U.S. Cybercriminals who once earned millions by breaking...
-

 74
74Kapustkiy breached an Italian Government website, exposing 9,000 of 45,000 records
Hacker Kapustkiy breached into an Italian Government website (Dipartimento della Funzione Pubblica) exposing 9,000 users of 45,000. A few days ago I...
-

 145
145Powerful backdoor/rootkit found preinstalled on 3 million Android phones
Firmware that actively tries to hide itself allows attackers to install apps as root. Almost three million Android phones, many of them...
-
 153
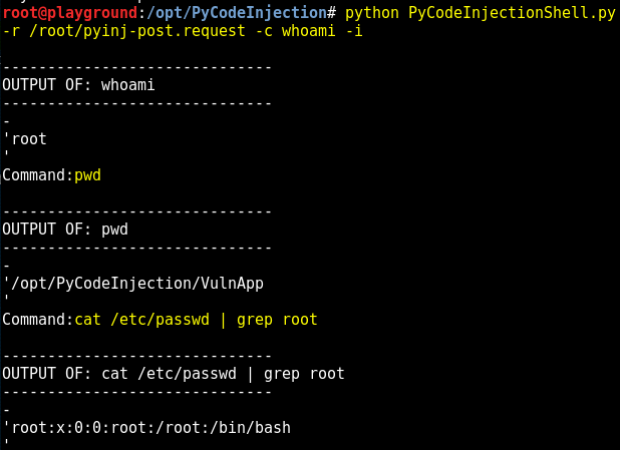
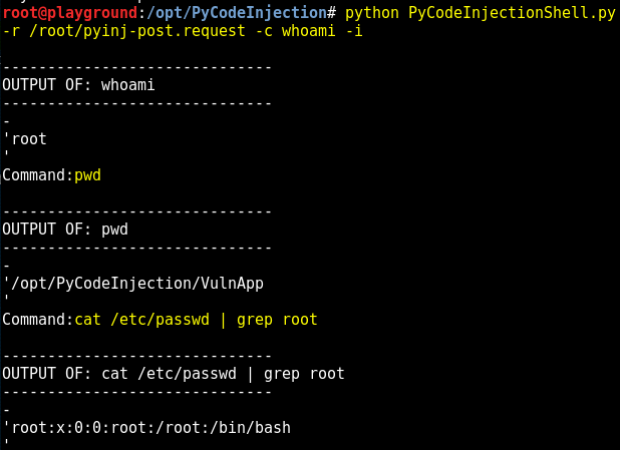
153Exploiting Python Code Injection in Web Applications
A web application vulnerable to Python code injection allows you to send Python code though the application to the Python interpreter on...
-

 177
177OAUTH 2.0 HACK EXPOSES 1 BILLION MOBILE APPS TO ACCOUNT HIJACKING
Third-party applications that allow single sign-on via Facebook and Google and support the OAuth 2.0 protocol, are exposed to account hijacking. Three...
-

 89
89Cylance Discloses Voting Machine Vulnerability
The following proof of concept video demonstrates the techniques Cylance researchers used to compromise a Sequoia AVC Edge Mk1 voting machine. The...






