Latest News
-

 78Data Security
78Data SecurityAuthors digitally signed Spymel Trojan to evade detection
Zscaler ThreatLabZ detected a new infostealer malware family dubbed Spymel that uses stolen certificates to evade detection. In late December, security experts...
-

 265Incidents
265IncidentsGhost Squad Hackers Hack Ethiopian Websites In Response To Killing Of Protesting Students
Short Bytes: Ghost Squad Hackers group has taken down multiple .gov websites in Ethiopia. The collective has blamed the government for killing...
-

 173News
173NewsISIS Terrorists Kill Female Journalist, Hack Facebook Account
The terrorists first murdered the female journalist Ruqia Hassan and then hacked her Facebook account to spy on her contacts. The terrorist from...
-

 250Data Security
250Data SecurityAnti-NSA Blackphone Not So Secure After all
A security flaw in Blackphone 1 smartphone allowed anyone to take control of the device Blackphone 1 smartphones, one of many privacy-focused...
-
 229Lists
229Lists11 Top Technology Predictions For 2016 | fossBytes
Short Bytes: Technologies like IOT, 3D printing, VR camera and Tesla skimmed through entire 2015. But which technology in 2016 is going...
-

 332News
332NewsFBI Hacked Tor To Hunt Down Paedophiles On The Deep Web
FBI has taken down a site involved in Child pornography through some hacking techniques that have never been used in the history...
-

 217Geek
217GeekWindows 10 usage stats show user privacy is a very real concern
Microsoft has released stats regarding Windows 10 usage worldwide which proves the point that user privacy is a very real concern Although,...
-
 105Geek
105GeekOne Javascript Tip A Day, Keeps Code Bugs Away
Short Bytes: In this article, I bring to you a new project called Javascript Tips that promises to deliver you one Javascript tip per...
-

 132Privacy
132PrivacyShould I stay or should I go … to Windows 10?
It has been almost half a year since Microsoft released Windows 10, and the decision whether or not to migrate computers to...
-

 93Data Security
93Data SecurityRemote Exploitation of Microsoft Office DLL Hijacking (MS15-132) via Browsers
A number of weeks back, security researcher Parvez Anwar posted a number of DLL hijacking vulnerabilities within Microsoft Office on Twitter [1]....
-

 283Opinion
283OpinionCES 2016: Day 1 – surviving the swarm
As ever, ESET is once again in attendance at CES in Las Vegas, offering you expert insight into all the security aspects...
-

 177Vulnerabilities
177VulnerabilitiesDrupal Update Process Flawed by Multiple Bugs, Attackers Can Take Over Sites
IOActive’s Fernando Arnaboldi has sounded the alarm on three major flaws in Drupal’s update process that may allow attackers to poison Drupal...
-

 92Malware
92MalwareLet’s Encrypt Now Being Abused By Malvertisers
Encrypting all HTTP traffic has long been considered a key security goal, but there have been two key obstacles to this. First,...
-
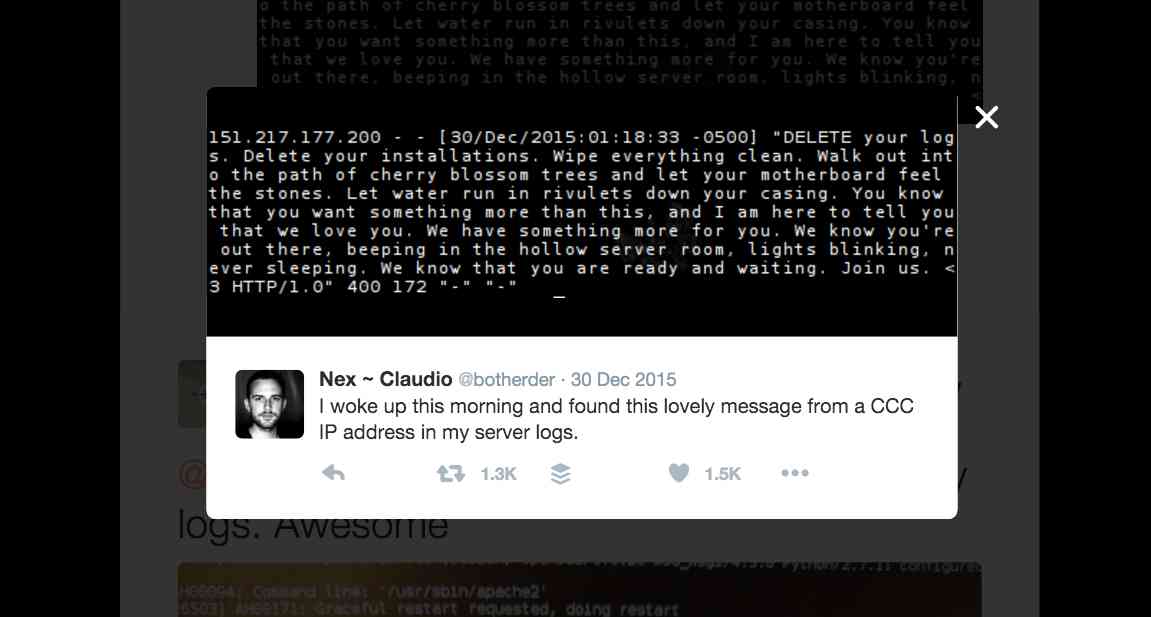
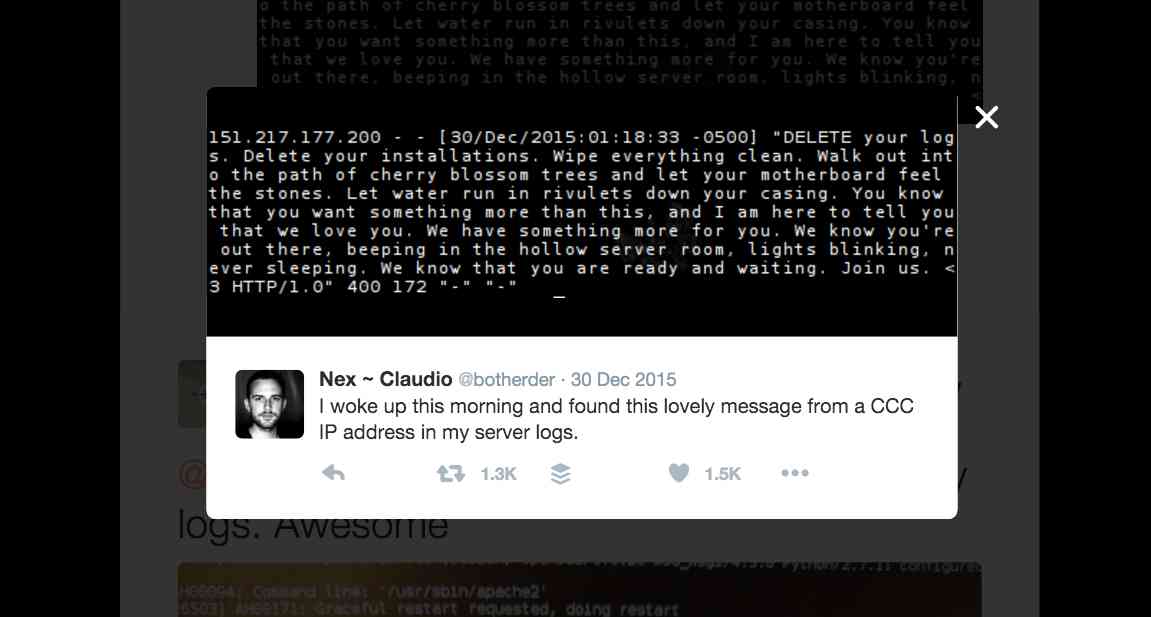 314Hacked
314HackedHow Hackers Invaded 30 Million Web Servers On The Internet With A Poem
Short Bytes: From an IP address associated with 32nd Chaos Communication Congress (32c3) taking place in Germany, some unknown hackers sent a...
-

 206Vulnerabilities
206VulnerabilitiesSevere Silent Circle Blackphone vulnerability lets hackers take over
The security-focused smartphone contained vulnerabilities which allow hackers to control the device’s modem and call functions. Researchers have revealed a severe vulnerability in...
-
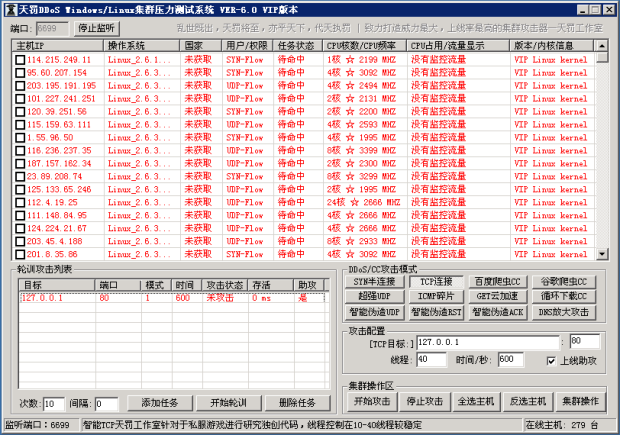
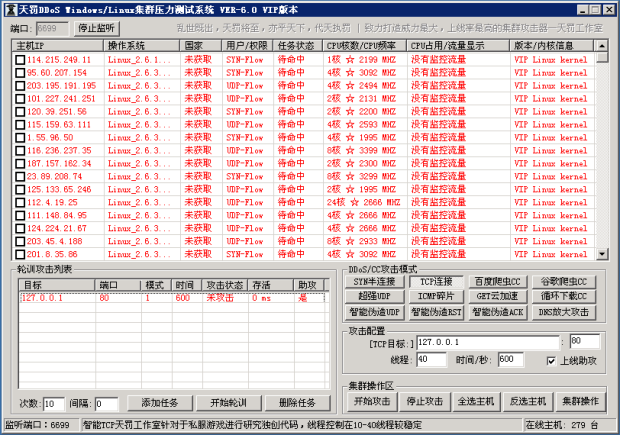 166Data Security
166Data SecurityWindows and Linux Malware Linked to Chinese DDoS Tool
Malware was infecting machines, adding them to its botnet.Similar-looking malware targeting both Linux and Windows computers has been linked to a DDoSing...
-
 433Data Security
433Data SecurityTOR Anonymity: Things Not To Do While Using TOR
Short Bytes: Being Anonymous online is the need of the hour, and TOR browser does that job quite efficiently and honestly. But...
-

 390Cyber Events
390Cyber EventsExploit Flash Heap Isolation for a chance to “win” $100,000
Exploit Flash Heap Isolation for a chance to “win” $100,000 If you can exploit Adobe’s Heap Isolation mitigation in Flash player version...
-

 284Geek
284GeekGoogle fixes vulnerabilities in Android where rooting is a double-edge sword
Google had to intervene to fix a few vulnerabilities that risked exposing its Nexus devices and related Android operating system to remote...
-

 273News
273NewsAnonymous Hacks Thailand Police, Expose Wrongdoing in Murder Investigation
Anonymous Responds to Thai Police’s Flawed Murder Investigation by Hacking 14 Thai Websites The hackers at Anonymous are yet again busy in...



