Featured News
-

 228Incidents
228IncidentsQatar National Bank Hacked, Hackers Leak 1.4GB Database
Hackers leak 1.4GB database of information after breaching Qatar National Bank.A group of unknown hackers have claimed to have hacked into the...
-
 199Data Security
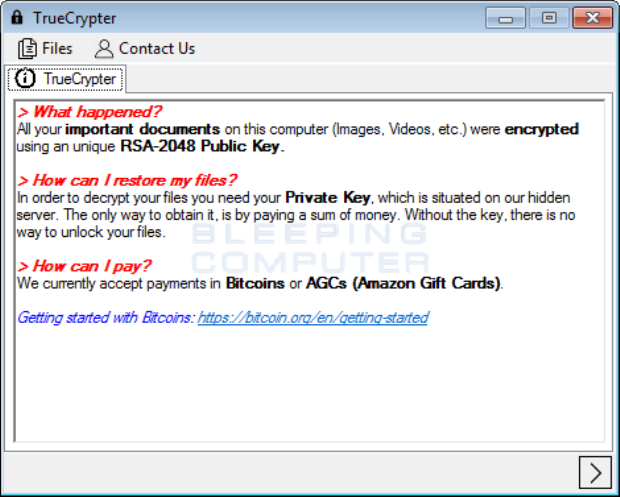
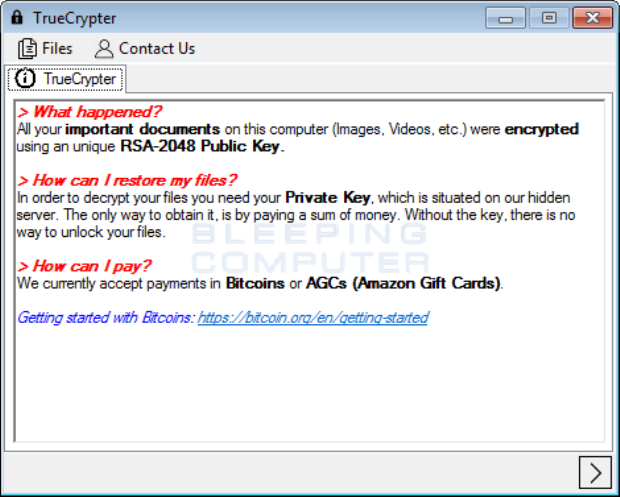
199Data SecurityTrueCrypter Ransomware accepts payment in Bitcoins or Amazon Gift Card
Yesterday, a new ransomware called TrueCrypter was discovered by AVG malware analyst Jakub Kroustek. This ransomware encrypts your data using AES-256 encryption and then...
-

 211News
211NewsAnonymous Leaks 1TB of Data from Kenya’ Ministry of Foreign Affairs
Anonymous leaked confidential documents from the ministry servers against government corruption. The online hacktivist Anonymous has conducted a sophisticated cyber attack on the government...
-

 125Cyber Crime
125Cyber CrimeSextortion, Cyber Stalking: U.S. Embassy Official Facing 4 Years in Prison
In 2015, Ford was charged with sextortion and cyberstalking scheme — Now, he has been sent to prison for four years and...
-

 220Geek
220GeekNode.js Version 6 LTS Released — World’s Fastest Growing Open Source Platform
Short Bytes: To ensure an improvement performance experience for its 3.5 million users, Node.js Foundation has released Node.js Version 6 with Long...
-

 116Geek
116GeekThe Next Einstein, Sabrina Pasterski, Built Her Plane And Flew It Solo At 14
Short Bytes: Just 23 years old, Sabrina Pasterski is being termed as the ‘next Einstein’ by the Harvard University. From building her own...
-

 225Cyber Crime
225Cyber CrimeRansomware and the Internet of Things
A report from the Institute for Critical Infrastructure Technology warns that ransomware could be hitting more than just your regular computer in...
-

 136Data Security
136Data SecurityRUMMS: THE LATEST FAMILY OF ANDROID MALWARE ATTACKING USERS IN RUSSIA VIA SMS PHISHING
Recently we observed an Android malware family being used to attack users in Russia. The malware samples were mainly distributed through a...
-
 371Geek
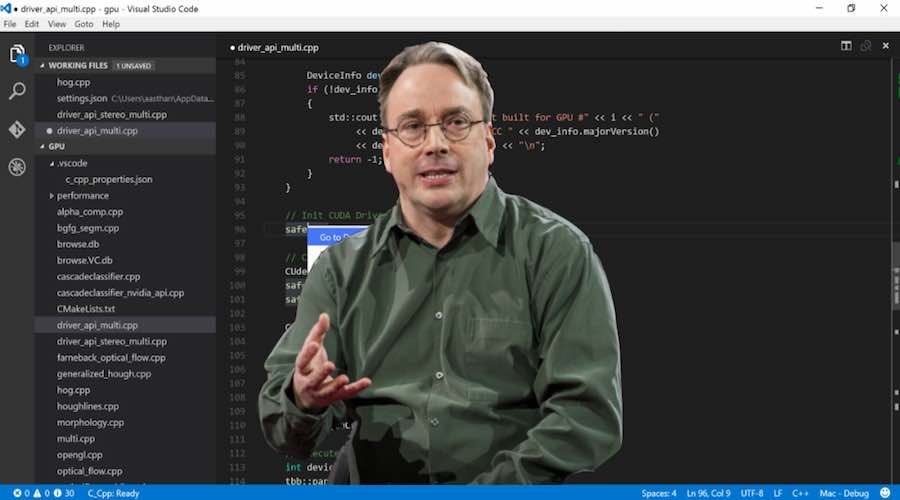
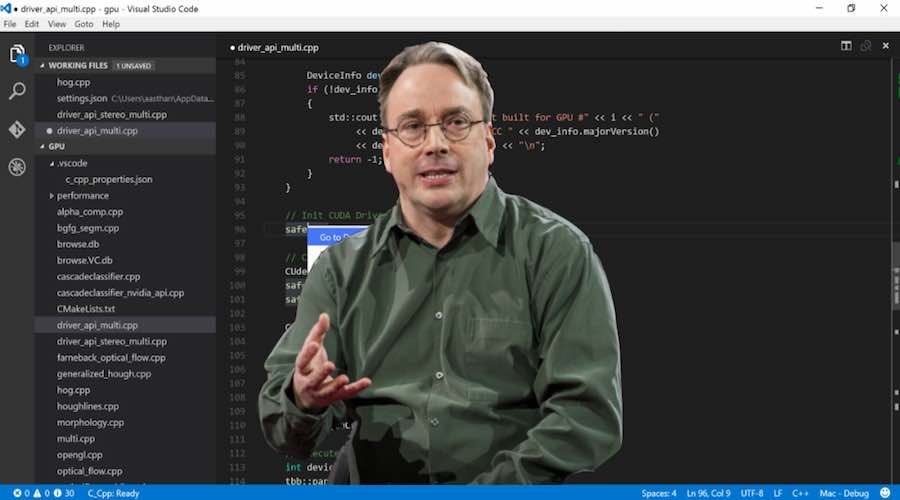
371GeekWhy Linux Creator Linus Torvalds Thinks That C++ Programming Language Sucks?
Short Bytes: You might know that Linux creator Linus Torvalds is a big supporter of C programming language. However, he doesn’t share...
-

 109Data Security
109Data SecurityHacking group “PLATINUM” used Windows’ own patching system against it
Unknown group attacked South East Asian targets, sometimes for years at a time. Microsoft’s Windows Defender Advanced Threat Hunting team works to track down...
-
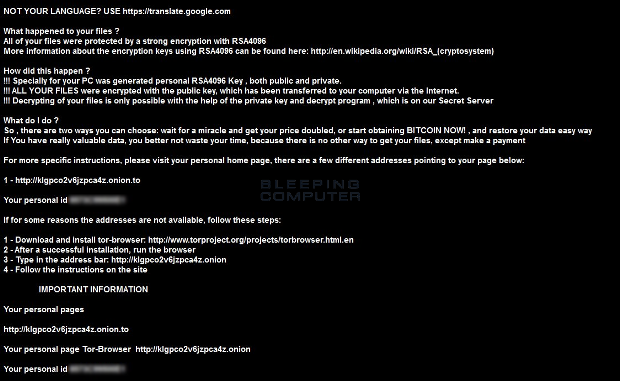
 298Malware
298MalwareDecrypted: Kaspersky releases free decryptor for CryptXXX Ransomware
Last week Kafeine posted an analysis of a new ransomware called CryptXXX on the Proofpoint blog. Based on their analysis they determined that...
-

 272Hacked
272HackedHow Hackers Earned $100,000 Just By Sending A DDoS Threat In Emails
Short Bytes: According to a recent revelation, a hacking group called Armada Collective collected more than $100,000 just by sending a DDoS threat...
-

 206Data Security
206Data SecurityHundreds of Spotify credentials appear online – users report accounts hacked, emails changed
A list containing hundreds of Spotify account credentials – including emails, usernames, passwords, account type and other details – has popped up on...
-

 149Vulnerabilities
149VulnerabilitiesFacebook Bug Allowed Attackers to Take Over Accounts on Other Sites
Facebook vulnerability breaks down the convenience of social login authentication. Insufficient security validation allows attackers to impersonate Internet users and gain password-less...
-
 334Geek
334GeekFacebook Users Hit with ‘irregularities of content’ Phishing Scam
Cyber criminals are targeting innocent Facebook users with yet another phishing scam — This time, it’s quite a sophisticated one so watch...
-

 261Cyber Events
261Cyber EventsUnited Cyber Caliphate (UCC), formation of a mega hacking group by ISIS
Pro-ISIS hackers from all over the world have joined hands to make a new hacking unit to target the US and West. Hackers...
-

 196News
196NewsBeautifulPeople Dating Site, 1.1 Million Users Data for Sale on Dark Web
Approximately 1.1 Million people suffer data hacks from the dating website BeautifulPeople. The big news was broken on Twitter where Troy Hunt...
-
 327News
327NewsQatar National Bank Hacked, 1.4GB Database Leaked
A group of unknown hackers claims to breach the security of Qatar National Bank and leak banking details of Qatari Royal Family,...
-

 77Incidents
77IncidentsDating website ‘Beautiful people’ hacked, 1.1 m members data leaked
BeautifulPeople.comLeaks Very Private Data of 1.1 Million ‘Elite’ Daters. This is a shame hack, a website called site BeautifulPeople.com which only accepts those people who...
-
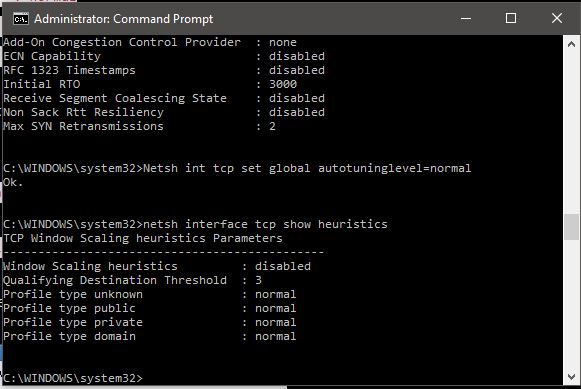
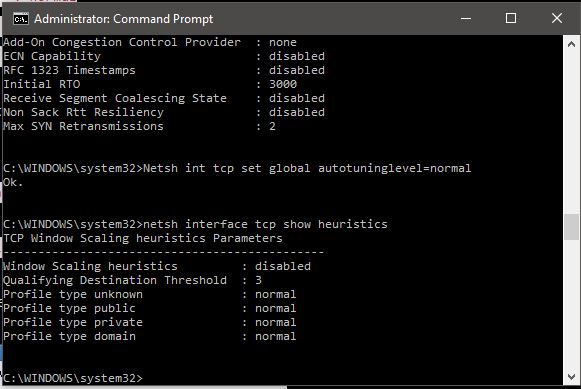 506How To
506How ToSpeed Up Internet Using CMD (Command Prompt)
Short Bytes: To speed up the internet using cmd, we have come up with some Windows tweaks. Some of these tweaks and...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




