Featured News
-
 195Hacked
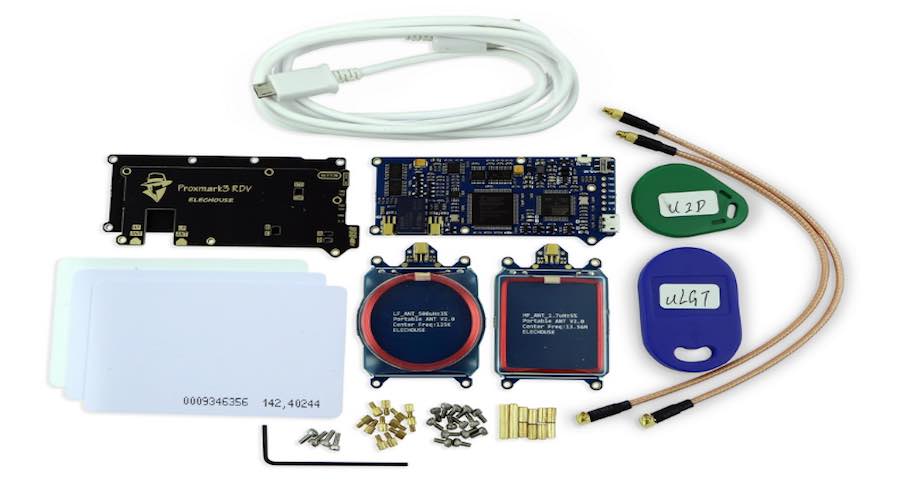
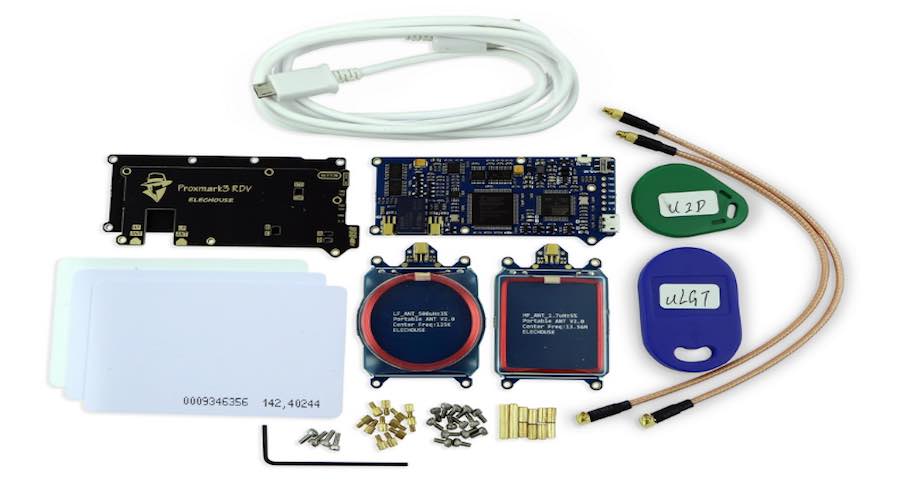
195HackedHere’s How Hackers Can Break Into Any Office With This Easily Available Device
Proxmark Short Bytes: In a recent demonstration, a team of white hat hackers showed how an attacker can compromise the corporate security...
-
 74Incidents
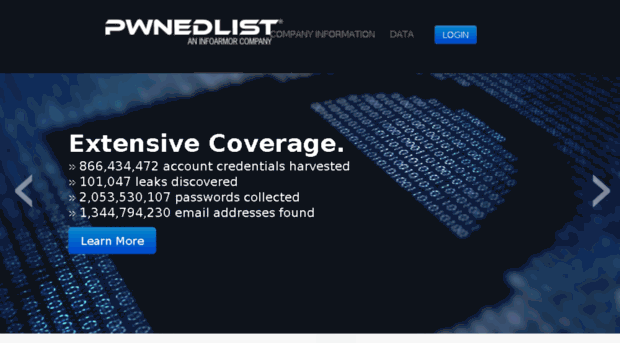
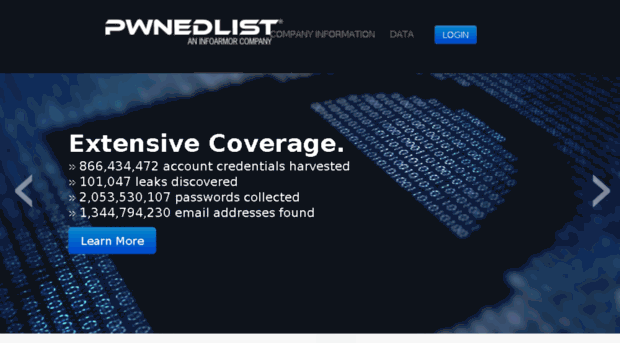
74IncidentsA flaw in the PwnedList service exposed millions of credentials
A serious expert discovered a flaw in PwnedList service that could have been exploited to access millions of account credentials managed by...
-
 255Vulnerabilities
255VulnerabilitiesValve Fixes Steam Crypto Bug That Exposed Passwords in Plaintext
19-year-old college student fixes Steam’s crypto. Valve has updated the Steam gaming client to fix a severe security issue in the application’s crypto...
-

 312News
312NewsAnonymous Target Bank of Greece Website with Massive DDoS Attack
Anonymous shut down the bank of Greece website in a powerful DDoS attack — Vows to target more banks against financial corruption....
-

 316Geek
316GeekConsider Selfie Sticks Old-School — Time to use Hover Drones for Selfies
You can now walk along with this drone and it will take selfies for you! We all know that while using a...
-

 107Data Security
107Data SecurityFlaws in Samsung’s ‘Smart’ Home Let Hackers Unlock Doors and Set Off Fire Alarms
A SMOKE DETECTOR that sends you a text alert when your house is on fire seems like a good idea. An internet-connected...
-

 245Malware
245MalwareDecrypted: Alpha Ransomware accepts iTunes Gift Cards as Payment
A new ransomware called Alpha Ransomware was discovered and analyzed this week by Katja Hahn, S!Ri, MalwareHunterTeam, and Michael Gillespie. This ransomware encrypts your data...
-
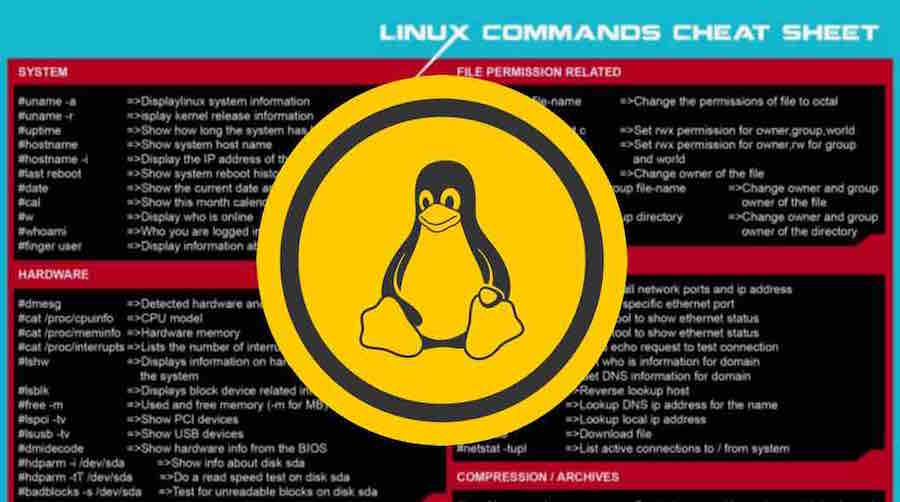
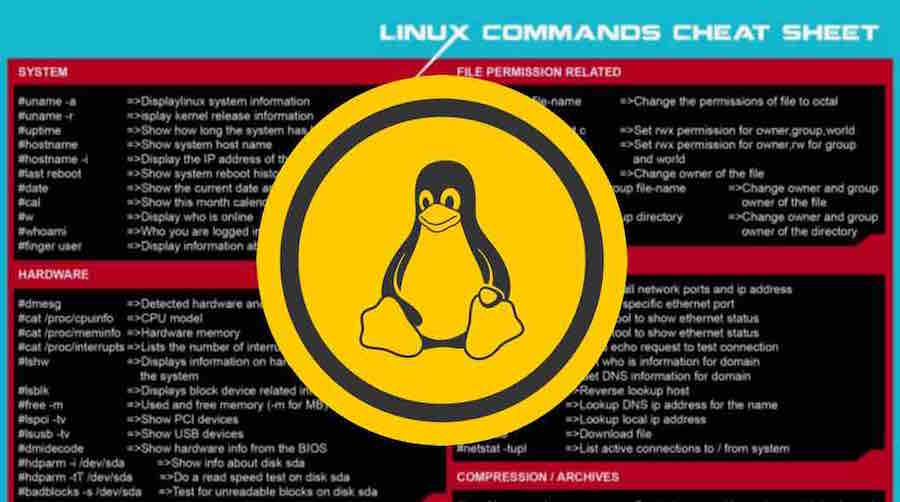 271Geek
271GeekLearn The Basic Linux Commands With This Awesome Cheat Sheet
Short Bytes: Here I’m sharing a useful Linux commands cheat sheet that you can print and keep it as a learning guide...
-

 300Anonymity
300AnonymityHow To Setup VPN On Kali Linux For Anonymity
Virtual Private Networks (vpn) create an encrypted ‘tunnel’ between your computer and the host server, with the internet traffic going in and...
-

 140Data Security
140Data SecurityGovernment role in cyber security for protecting private sector companies
Cyber security refers to the set of solutions, services and trainings that can be implement by a company or an organization for...
-

 72Incidents
72IncidentsCanadian Gold-Mining firm Goldcorp hacked
Canadian Gold-Mining Company Goldcorp suffered a major data breach, 14.8 GB Data Stolen, the hackers plan to release more data dumps soon....
-

 245Vulnerabilities
245VulnerabilitiesGarage4hackers Webcast – Bypass Modern WAF’s Exemplified at XSS
Watch now and learn to Bypass Modern WAF’s Exemplified at XSS in another Series of Garage4hackers Ranchoddas Webcast. Garage4hackers presents Ranchoddas Webcast...
-
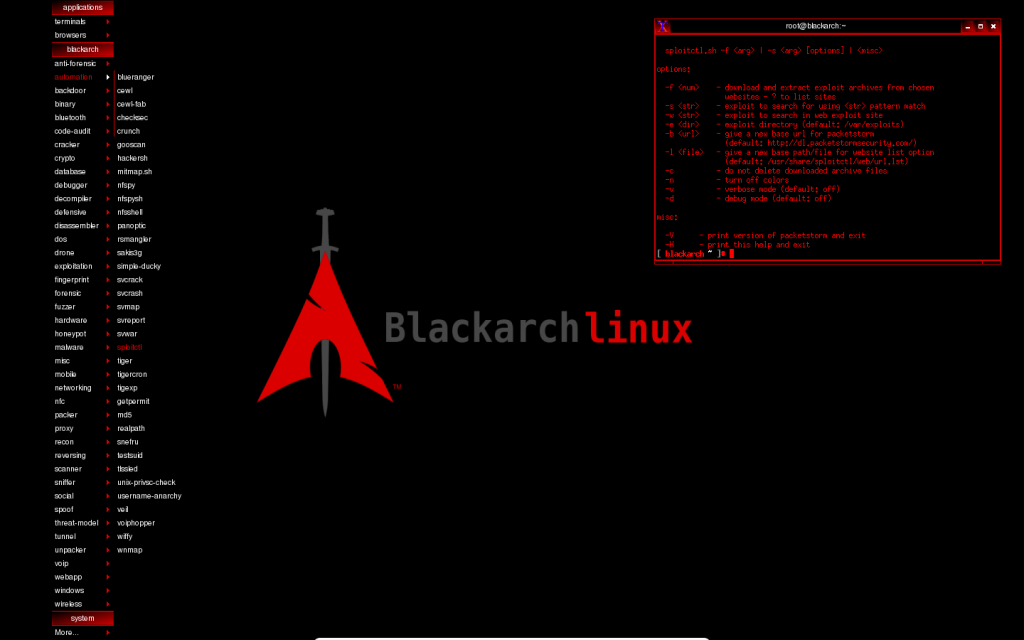
 235Operating Systems
235Operating SystemsNew BlackArch Linux version released
BlackArch Linux version 2016.04.28 released for ethical hackers and security researchers with 1400 pentesting tools If you are an ethical hacker or a...
-
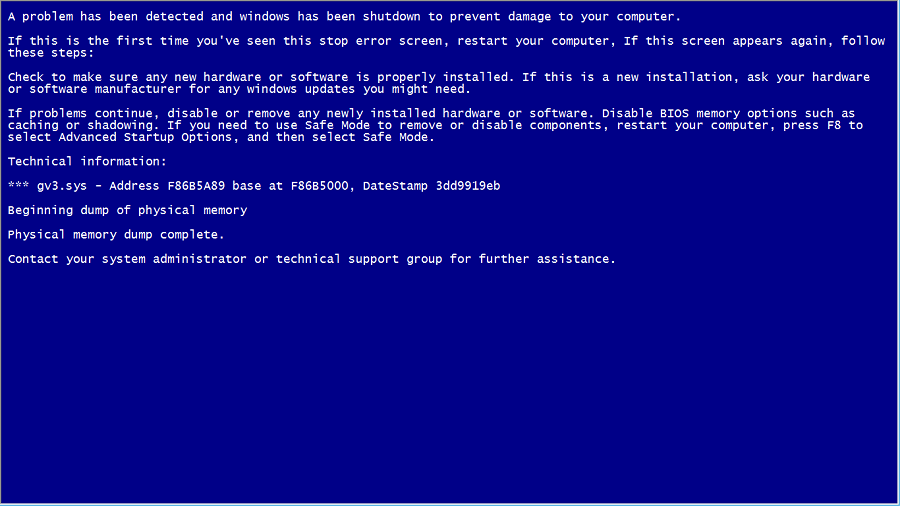
 409How To
409How ToHow To Create A Fake BSOD And Play Prank On Your Friends?
Short Bytes: This article will help you create your own fake Blue Screen Of Death (BSOD) and play a prank on your...
-

 288News
288NewsQatar National Bank Accepts Data Breach while Hackers Release Inside Video
Turkish hackers were behind the QNB’s data breach — The QNB has accepted that they were hit with a cyber attack Last...
-

 317News
317NewsLifeboat Hacked, Millions of Minecraft Passwords Stolen
Minecraft users have to change their passwords ASAP because Lifeboat company didn’t disclose about the data breach that took place in early...
-
 153Information Gathering
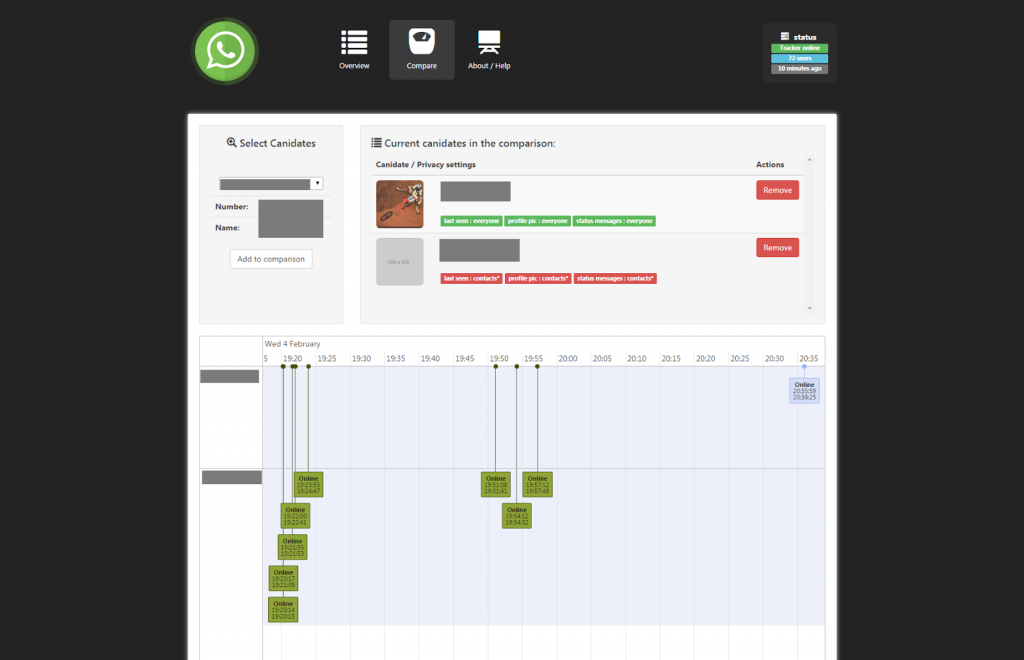
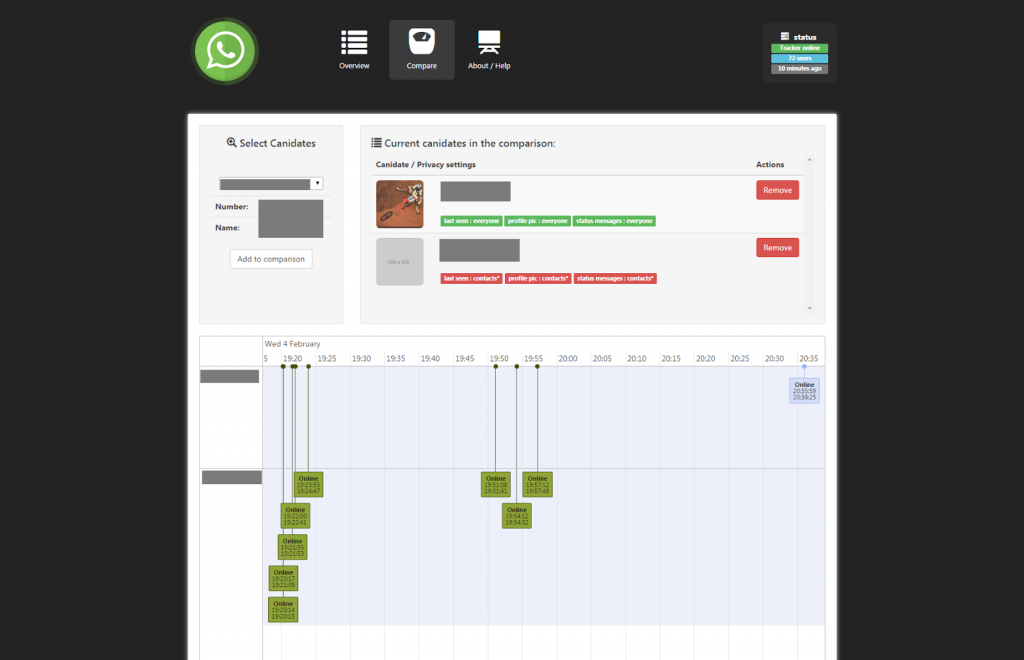
153Information GatheringWhatsSpy – Trace the moves of a Whatsapp User
WhatsSpy Public is an web-oriented application that tracks every move of whoever you like to follow. This application is setup as an...
-
 319Geek
319GeekNew Android Malware RuMMS Targeting Users through Smishing
The malware is targeting Russian users but it’s about time when the same tactics will be used by other cyber criminals outside...
-

 216Backdoors
216BackdoorsSideDoor – Debian/Ubuntu Backdoor Using A Reverse SSH Tunnel
Sidedoor maintains a reverse tunnel to provide a backdoor. sidedoor can be used to remotely control a device behind a NAT. Sidedoor...
-

 242Geek
242Geek“Kill JavaScript, Java, And Ruby Programming Languages” — Were You Going To Sign This Petition?
Short Bytes: There are few programming languages that are hated by many. But, a crazy person took his hate to the next level...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




