Featured News
-
 84Incidents
84IncidentsWebmail firms probe login ‘leak’ 272 Million
Several popular webmail providers are investigating a report that millions of their users’ login details are being shared online by a hacker....
-
 89Malware
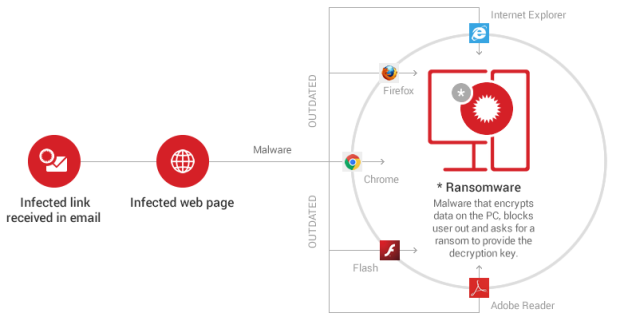
89MalwareNew CryptMix Ransomware Promises to Give Money to a Children’s Charity
CryptMix is a mashup of CryptXXX and CryptoWall. A new type of ransomware created and distributed by a group of crooks calling themselves...
-
 318Geek
318GeekHere’s Your Chance to Use IBM’s Remotely Accessible Quantum Computer
Quantum Computing- No More a Thing of Distant Future — IBM wants us all to use it remotely accessible Quantum Computer… for free!...
-

 315News
315NewsOpIcarus: Hacktivists Shut Down Central Bank of Cyprus with DDoS Attack
OpIcarus has found another target and this time it’s the Central Bank of Cyprus. A group of hacktivists shut down the official...
-

 232Geek
232GeekWindows ‘God Mode’ Feature Exploited by New Malware to Avoid Identification
Researchers have identified a new malware taking advantage of Windows God Mode and infecting users. Malware in a Window OS is not...
-

 184Geek
184GeekA Google Engineer Forced Amazon To Ban Bad USB Type-C Cables With His Reviews
ShortBytes: A Google engineer named Benson Leung spent months reviewing bad USB Type-C cables on Amazon. He spent so much time reviewing them...
-

 225Geek
225GeekUbuntu 16.04 LTS vs. Windows 10 — NVIDIA And AMD Graphics And Drivers Compared
Short Bytes: With the release of polished Ubuntu 16.04 LTS, it’s time to compare the performance of different graphics cards and drivers...
-
 173Geek
173GeekMicrosoft’s Word Flow Keyboard for iPhone Makes Texting Easy
This keyboard makes it easy for people to chat with just one hand — It’s only available in US-based iOS stores. Now...
-

 251Data Security
251Data SecurityHow Traffic to This YouTube Video Predicts ISIS Attacks How Traffic to This YouTube Video Predicts ISIS Attacks
A YouTube video’s best day, traffic-wise, is usually the day it gets posted. Clicks generally decline quickly and post-launch spikes are rare....
-

 153Data Security
153Data SecurityQatar National Bank Declares Systems ‘Fully Secure’ Sequel To Cyber-attack
Following the recent security breach suffered by the Qatar National Bank has assured that its systems are “fully secure”. Sequel to a...
-

 333How To
333How ToHow To Disable Write Protection In SD Card Or Pen Drive?
You might have struggled with situations where Windows isn’t able to copy anything to a write-protected storage media. This article will help...
-

 116Malware
116MalwareFBI Announcement: Paying The Ransom is a Bad Idea
Hey Folks! So late last year a quote was going around about a comment for the Special Agent in charge of the...
-

 165Vulnerabilities
165VulnerabilitiesImageTragick Exploit Used in Attacks to Compromise Sites via ImageMagick 0-Day
imageMagick project hopes to publish a patch today. Two Russian security researchers revealed a few hours ago a vulnerability in the ImageMagick image...
-

 344Geek
344Geek10-year-old Kid Hacks Instagram, Gets $10,000 Reward from Facebook
A 10-year-old kid from Finland found a bug allowing access to Instagram servers and delete any text posted by Instagram users. If...
-

 357Geek
357GeekFake Google Chrome Update Leads to Android Malware Stealing Personal Data
Android Users Beware- This New Malware can Retrieve Banking Information and Track your Texts For Android users, using their devices has become...
-

 131News
131NewsNew anti-hacking law promises life imprisonment to vehicle hackers
If you are an IT security researcher or a hacker and living in the Michigan State you may consider to move somewhere else...
-

 115News
115NewsPwnedList Gets Pwned, shutting down service in few days
PwnedList is a tool that allows an average person to check if their accounts have been compromised — The company has decided...
-

 150Incidents
150IncidentsHacker who stole from banks ordered to pay $7 million
A hacker whose creation stole bank account details from over a million computers across the globe has been ordered to pay $6.9...
-

 68Data Security
68Data SecurityAustralian computer scientist claims he is Satoshi Nakamoto who created bitcoins
Australian computer scientist claims he is the elusive Bitcoin creator, Satoshi Nakamoto. The hunt for creator of world’s most popular cryptocurrency, the Bitcoin...
-

 75Data Security
75Data SecurityMichigan Senate Bills Would Give Car Hackers Life In Prison
The FBI sent out a PSA just over a month ago warning us all about the risks of car hacking, but drivers...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




