Featured News
-

 305Geek
305GeekIf You Don’t Upgrade to Windows 10 Now – You Will Have to Pay $119 Later
Microsoft will charge you $119 from 29th July 2016 in order to update your operating system from Windows 7 and Win 8...
-

 279News
279NewsIndia Blames ISI for Spying on Military Through Gaming and Music Apps
Pakistani Intelligence Agency ISI is using Smartphone Malware for Spying upon its Military and Security Forces- Claims Indian Government. Pakistan’s intelligence agency...
-

 114Malware
114Malware“I’m with Stupid” Locky network gets hacked and dissed
A few months ago, we reported on a white hack against Dridex where the malicious payload was removed and an Avira antivirus...
-
 70Data Security
70Data Security7 Password Experts on How to Lock Down Your Online Security
AS FAR AS made-up holidays go, “World Password Day” doesn’t quite have the same cachet as, say, Father’s Day, or even National...
-
 306Opinion
306OpinionInterop: Getting a few more years out of your tech
Remember when a 100 gigabyte hard drive was huge? I try not to think about it, but I also remember when no...
-
 385How To
385How ToHow To Remove Virus From USB Or Any Drive On Windows 10 Using CMD
Most of the viruses modify the attributes of a file or a folder such that they become very hard to access. Some...
-
 251Geek
251GeekFuture Of Ubuntu Linux Desktop After Ubuntu 16.10 — Unity 8 And Snaps
Short Bytes: Unity 8 with Mir and Snaps are the future of Ubuntu Desktop after Ubuntu 16.04 Xenial Xerus, according to Canonical’s Will...
-

 162Malware
162MalwareNew Skype spam leads to Trojan download
Today, we’ve been alerted about an ongoing spam campaign against Skype users. The majority of those affected are in India, Japan, and...
-
 61Data Security
61Data SecurityKnowing Or Distributing This Illegal Prime Number Could Get You Arrested
Short Bytes: There are some very certain prime numbers that are illegal. Yes, having them in your possession or sharing them with...
-

 112Vulnerabilities
112VulnerabilitiesCritical Qualcomm security bug leaves many phones open to attack
Fix still isn’t available for most users, and many will probably never get it.For the past five years, a vulnerability in many...
-

 310Data Security
310Data SecurityThe Art of Hiding Cellphone, Laptop Cameras From Hackers and Government
Security agencies can spy on you through your laptop and smartphone cameras — It’s time to cover them. With new and modern...
-

 277News
277NewsAfter Hacking Bush, Guccifer admits Hacking Hillary Clinton’s Private Email Server
After George W. Bush and Colin Powell, Guccifer admits Hacking Private Email Server of Hillary Clinton and it was very easy. Marcel...
-

 243Sql Injection
243Sql InjectionWhitewidow – SQL Vulnerability Scanner
Whitewidow is an open source automated SQL vulnerability scanner, that is capable of running through a file list, or can scrape Google...
-

 238Lists
238Lists12 Google Products Which Make Google A Better Company Than Other Tech Giants
Short Bytes: Google products represent an individual brand in themselves. Over the years, Google products like Google Drive, Google Maps, YouTube, Google’s...
-
 271News
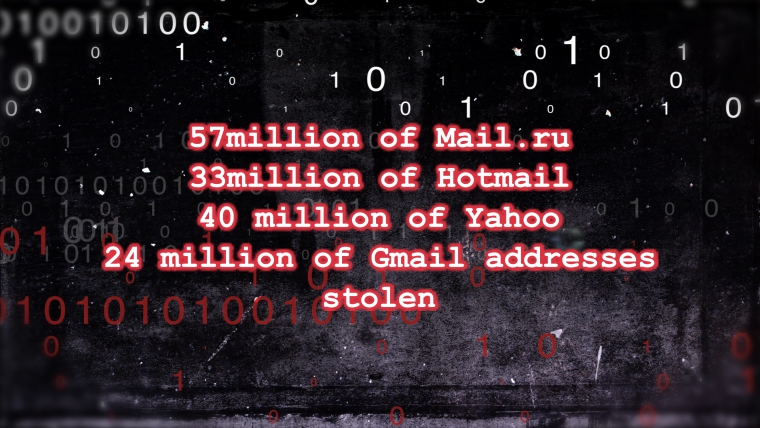
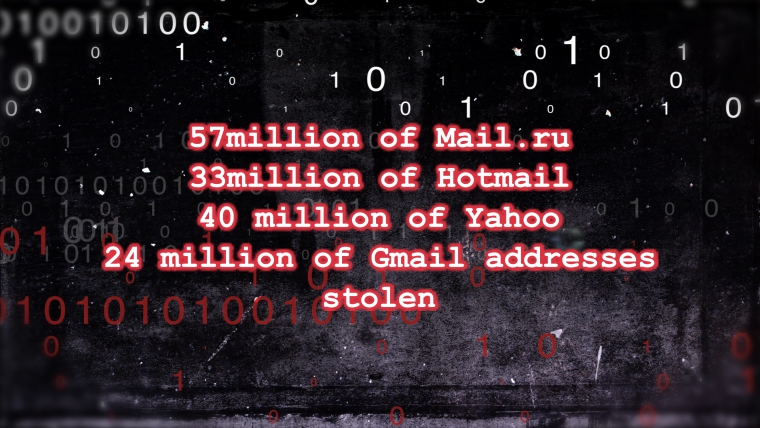
271NewsMassive Data Breach Hits Russian Users of Gmail, Yahoo and Hotmail
Massive Data Breach Hits Russian Users of Gmail, Yahoo and Hotmail — Russian Hacker Steals 250 million Email Addresses and Passwords and...
-

 288Geek
288GeekiPhone Users Hit with iCloud Account Deactivation Phishing Scam
iPhone users in the United Kingdom have been targeted with yet another phishing scam designed to steal their iCloud accounts — The...
-

 390Password
390PasswordForget about passwords: You need a passphrase!
Forget about passwords – it's all about passphrases. Longer, more complex and easy to remember, they will help you be more safe and...
-

 183Data Security
183Data SecurityPetya: the two-in-one trojan
Today, we have encountered a new threat that’s a blast from the past. The Petya Trojan (detected by Kaspersky Lab products as...
-
 286Hacked
286HackedHow To Create A Super Secure Password To Defeat Hackers
Short Bytes: Deciding a security-focused password is tougher that one might think. Even the most security-conscious users commit the mistake of forming...
-
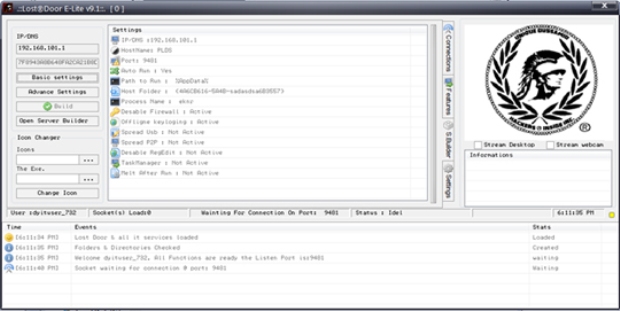
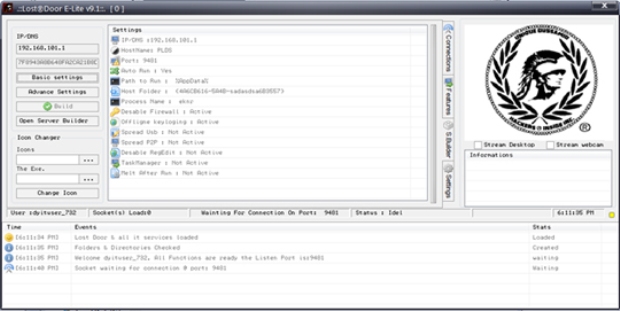 160Data Security
160Data SecurityLost Door RAT: Accessible, Customizable Attack Tool
We recently came across a cyber attack that used a remote access Trojan (RAT) called Lost Door, a tool currently offered on...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




