Featured News
-
 69Data Security
69Data SecurityAndromeda distributors craft new strategies for attacks
Most of popular botnet Andromeda’s (also known as Gamarue) distribution channels have been discovered and analyzed by antivirus vendors. This has forced Andromeda’s...
-

 156Vulnerabilities
156VulnerabilitiesFive-Year-Old SAP Vulnerability Affects Over 500 Companies, Not 36
Onapsis and US-CERT warned about attacks against 36 companies, another security firm begs to differ. The impact of a five-year-old security issue affecting...
-

 316Geek
316GeekSamsung File Patent for Projector Smartwatch That Uses Skin as Display Screen
Samsung is working on a projector smartwatch that will use your skin as a display screen! Innovation and out-of-the-box thinking have remained...
-

 261News
261NewsSQL Injection Flaw: Hardcore Fetish Forum Hacked, 100k Users’ Data Leaked
The Rosebutt Board (NSFW forum) has faced a massive data breach — The leaked data also includes .gov emails — If you...
-

 325Cyber Events
325Cyber EventsSo long .SE, The Pirate Bay loses domain name court battle in Sweden
After a long battle, The Pirate Bay has to say bye to its .SE domain! The Pirate Bay is no more. At...
-

 269Geek
269GeekBest Choice for Teens’ Cyber Safety – Parental Control App!
Teens spend more time on the web than staying out, it’s your responsibility to keep an eye on them and their online activities...
-

 207Incidents
207IncidentsSecond bank hit by ‘sophisticated’ malware attack, says Swift
The financial messaging network says a commercial bank was targeted in an attack with ‘deep knowledge of operational controls’. Swift, the global financial...
-

 170Kids Online
170Kids OnlineOnline safety for families across the years
When it comes to online safety, it can be difficult to understand what's suitable for different age groups. Our guide offers advice...
-

 79Malware
79MalwareAnother Eurovision contestant? Even malware can ‘perform music’
In contrast to the Eurovision contestants, malware writers try to make their creations as stealthy as possible. But thanks to unique behavior...
-
 79Vulnerabilities
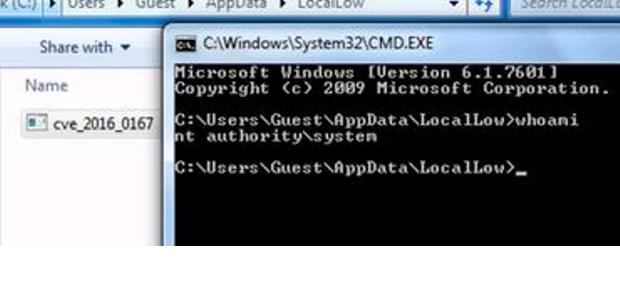
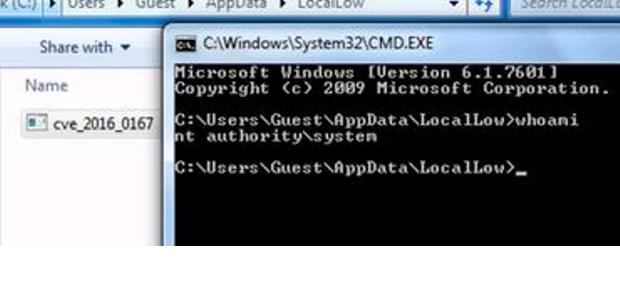
79VulnerabilitiesMicrosoft Windows zero-day exposes companies to credit card data theft
The boom in PoS systems in the US has its drawbacks. Researchers from FireEye have disclosed the details of cyberattack group leveraging a...
-
 63Incidents
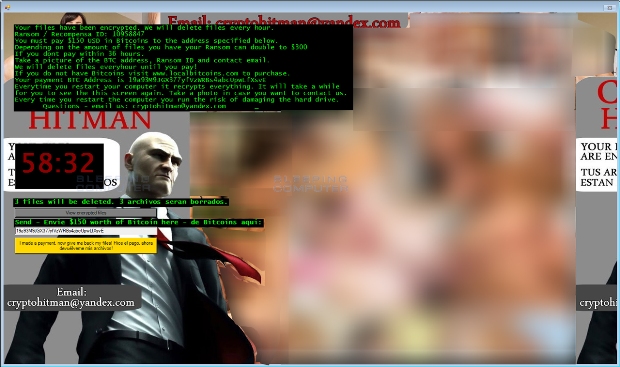
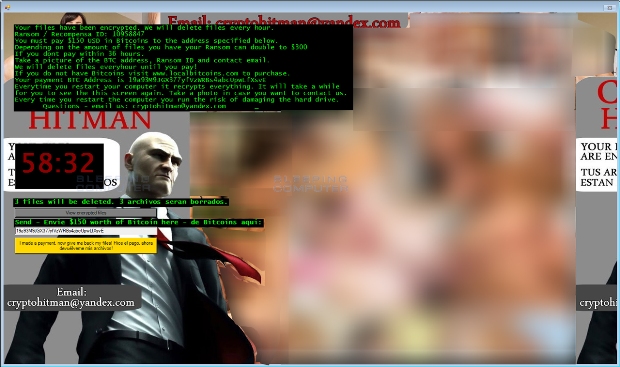
63IncidentsJigsaw Ransomware becomes CryptoHitman with Porno Extension
The notorious Jigsaw Ransomware has rebranded itself as CryptoHitman and now uses the character from the popular Hitman video games and movies. In addition to...
-

 168Hacked
168HackedUndercover Uncovered: Govt. Spy Truck Found Disguised As Google Street View Car
Short Bytes: A new case has popped up where a government vehicle was found disguised under the name of Google Street View car...
-

 93Vulnerabilities
93VulnerabilitiesKinky fetish forum hacked, hackers leak 100,000 user details
Hardcore fetish forum, Rosebutt Board hacked, traceable personal details leaked. The online hardcore fetish forum called Rosebutt Board was hacked by unknown hackers...
-
 99Malware
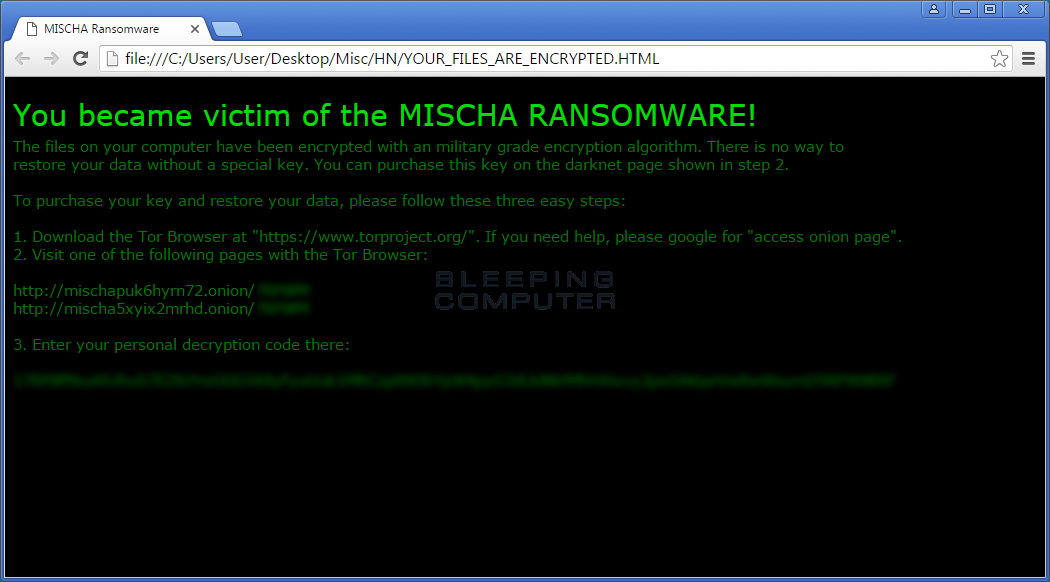
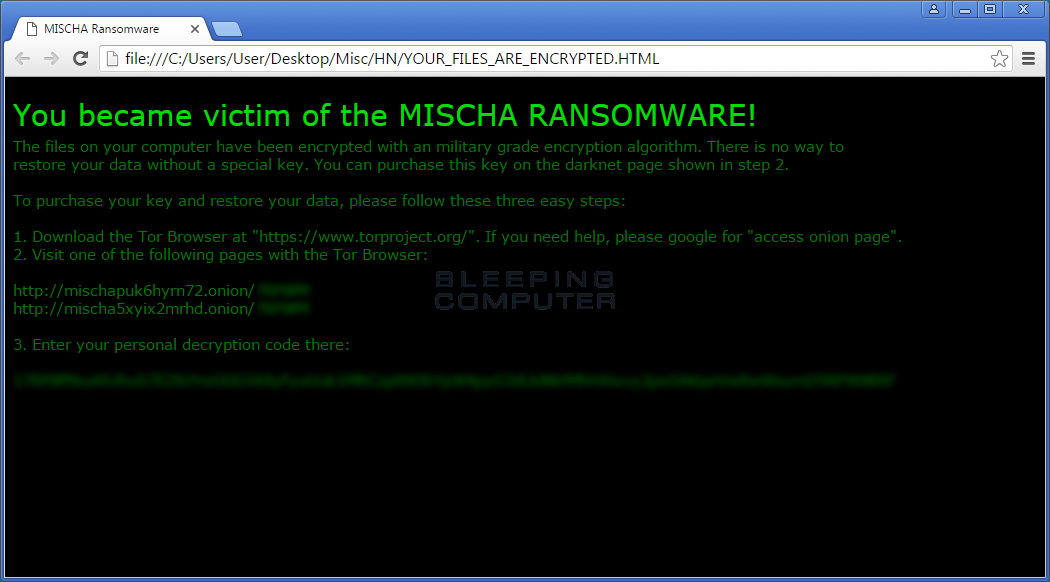
99MalwarePetya is back and with a friend named Mischa Ransomware
A new installer for Petya was released that also installs the Mischa Ransomware if it is unable to gain Administrative privileges. In the...
-
 190Hacked
190HackedMozilla To FBI: “Tell Us About The TOR Bug Used To Hack 1000+ Pedophiles”
Short Bytes: Recently, Mozilla filed a brief with the court, urging the FBI to reveal the technique used to hack 1000+ computers...
-

 259News
259NewsOpIcarus: Anonymous Shut Down 4 More Banking Websites
Anonymous, BannedOffline group and Ghost Squad are still conducting short term cyber attacks on banking sites around the world — Here is...
-
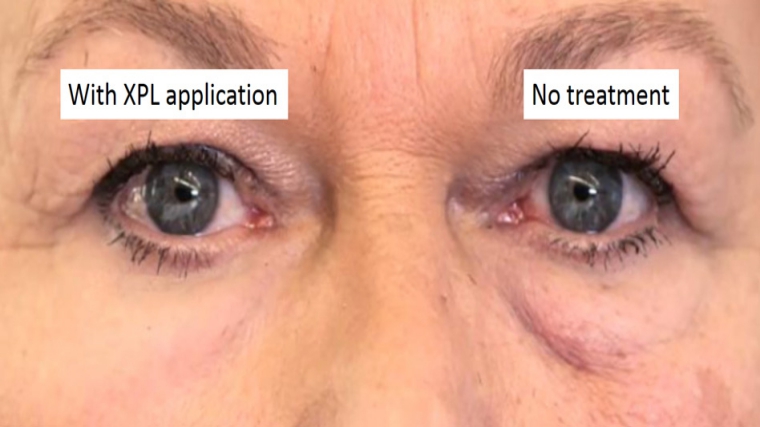
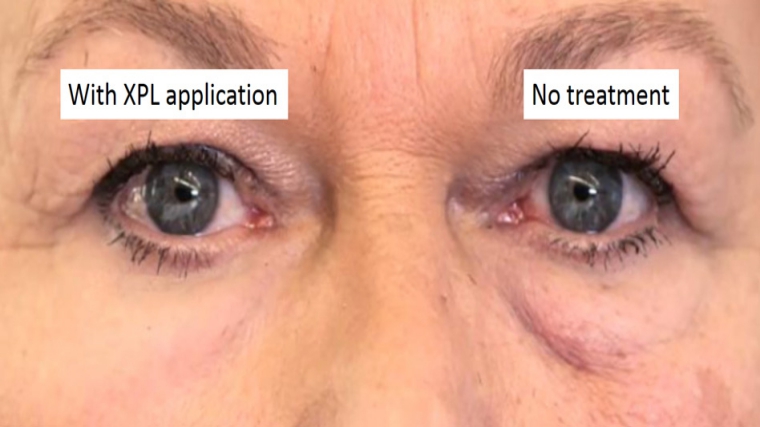 226Geek
226GeekRevolutionary Tech from MIT Researchers: Skin Cream Remove Wrinkles Instantly
This Miraculous Skin Cream can Remove Wrinkles Instantly Reducing wrinkles and preventing the signs of aging from affecting our youthful appearance and...
-
 272Data Security
272Data Security8 Reasons why you shouldn’t upgrade your system to Windows 10
Microsoft is forcing users to upgrade their OS from Win 7 and Win 8 to Win 10 — But, here are 8...
-

 227Information Gathering
227Information GatheringIPGeoLocation – A tool to retrieve IP Geolocation information
A tool to retrieve IP Geolocation information Powered by ip-api Requirements Python 3.x Features Retrieve IP or Domain Geolocation. Retrieve your own...
-

 216Geek
216GeekReview: An Undetectable Android Spying Software that No One Can Perceive
In the wake of the latest report that shows that Jihadist groups are using Telegram, Signal, and WhatsApp for chatting, and Gmail...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




