Featured News
-
 285Geek
285GeekJapan Just Made Computer Programming A Compulsory Subject In Its Schools
Short Bytes: With an aim to improve children’s creative and logical thinking, Japan has decided to make programming a compulsory subject in...
-

 418How To
418How ToHow To Install All Kali Linux Tools On Ubuntu Using “Katoolin” Script?
Short Bytes: Many Ubuntu Linux users are willing to use the tools of Kali Linux but they don’t want to install another...
-
 207Hacked
207HackedOplcarus: An Anonymous Hacker Reveals The Motivation Behind Latest Attacks
Short Bytes: Here is an account of the operation against banks and financial institutes, named “OpIcarus”, by Anonymous. It reveals the purpose...
-
 102Data Security
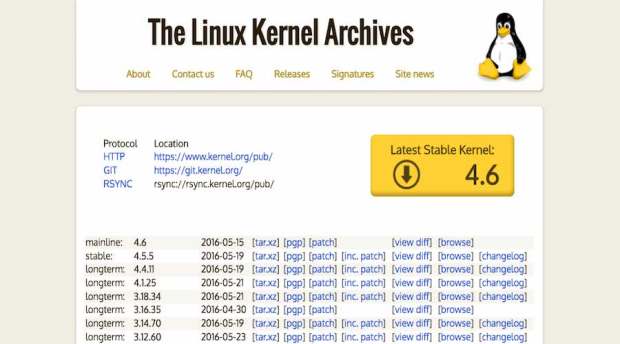
102Data SecurityLinux Kernel Website Kernel.org Banned By Norton
Short Bytes: Symantec’s automated threat analysis system, Norton Safe Web, claims that Linux kernel’s website kernel.org contains 4 threats and shows a...
-

 103Incidents
103IncidentsTeenager charged over Mumsnet hack and DDoS attack
An 18-year-old man has been charged by British police in connection with an internet attack that saw Mumsnet hacked, users’ accounts breached,...
-

 95Malware
95MalwareDMA Locker 4.0 – Known Ransomware Preparing For A Massive Distribution
From the beginning of this year, we are observing rapid development of DMA Locker. First, the threat was too primitive to even...
-

 86Data Security
86Data SecurityTARGETED ATTACKS AGAINST BANKS IN THE MIDDLE EAST
In the first week of May 2016, FireEye’s DTI identified a wave of emails containing malicious attachments being sent to multiple banks...
-

 310Incidents
310Incidents1.4 Billion Yen Stolen in Japanese ATMs in less than 3 Hours
Over 1.4 billion Yen was reportedly stolen in a span of two and a half hours across automated teller machines (ATMs) found...
-

 300Cyber Crime
300Cyber CrimeHacker Sentenced for Reporting Flaws in Police Communications System
Slovenian Student Gets Sentenced for Reporting Configuration flaws in Tetra Protocol Is it possible that somebody could be sent to jail for...
-

 243News
243NewsHackers Destroy Fur Affinity Art Gallery Website
Hackers target Fur Affinity art gallery website delete everything — Thanks to the backup the site is up and running once again!...
-

 235Scams
235ScamsTech support scams go with a Bing
Microsoft takes a shot at preventing support scammers from exploiting Bing Ads, explains David Harley, senior research fellow at ESET.
-

 87Incidents
87IncidentsHow To Hack The Police: Vigilante Hacker Publishes Online Tutorial Video
The hacker responsible for leaking 400GB of data from Italian spyware firm Hacking Team has published a tutorial video showing those seeking...
-
 411Geek
411GeekWhy Linus Torvalds Doesn’t Like Using Debian Or Ubuntu Linux?
Short Bytes: In many interviews, Linux creator Linus Torvalds has revealed that he prefers Fedora on his machines. But, why does he...
-

 125Incidents
125IncidentsShuttered Instagram holes opened 20 million accounts to hijack
Phone numbers exposed in borked verification portal Security consultant Arne Swinnen says Instagram has shuttered brute force authentication holes that allowed hijacking...
-
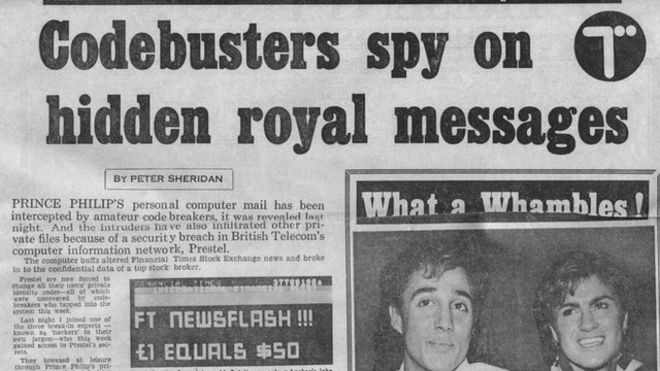
 86Incidents
86IncidentsArchive of historic BT ’email’ hack preserved
The hack made headlines in the UK and international press An archive detailing a historic hack and its fallout has been handed...
-

 295Hacked
295HackedStudent Hacks Teacher’s Email Account, Sends Porn To Parents, Teachers, And Students
Short Bytes: A teenager student from Gilbert recently broke into the email account of his teacher and used it to send pornographic...
-

 419Cyber Crime
419Cyber CrimeCriminals Steal 1.44 billion Yen ($13 million) from 1,400 ATMs in 2½ hours
Have you watched Nicolas Cage’s movie Gone in 60 Seconds? — Well, here’s something bigger than that and it’s 1.44 billion Yen gone...
-
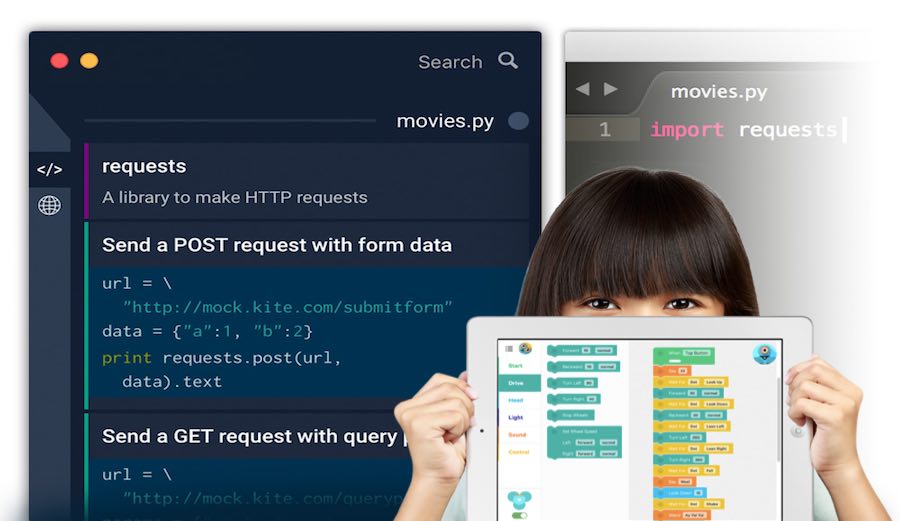
 255Geek
255GeekPython, Go, And Scala — Best Programming Languages You Should Learn To Boost Your Salary
Short Bytes: The 2016 Workforce-Skill Preparedness Report of PayScale, a salary tracking site, is out with many interesting trends related to the...
-
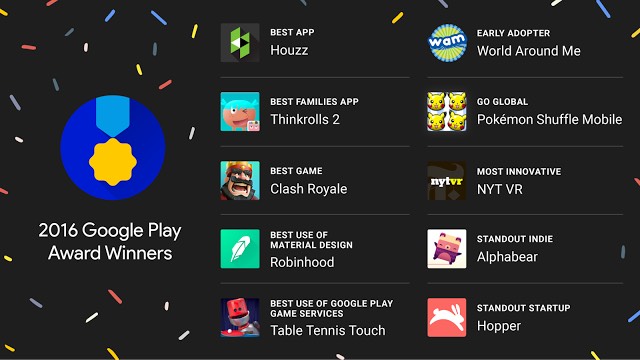
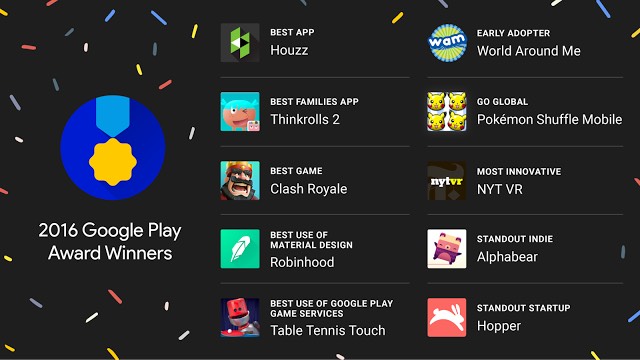 278Lists
278Lists10 Best Android Apps And Games Of 2016 — According To Google
Short Bytes: Google has unveiled its list of the 10 best Android apps and games of 2016. These apps are basically the...
-
 212Geek
212GeekHow Linux Is Built — How Does It Affect Your Daily Lives?
Short Bytes: Linux secretly plays one of the biggest parts in our technology-filled lives by running our phones, computers, websites, ATMs, power...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




