Featured News
-
 166Vulnerabilities
166VulnerabilitiesNew Simple Attack on Squid Proxies Leverages Malicious Flash Ads
Popular ISP utility exposed to new cache poisoning attack. Squison is the name of a recently discovered security bug in the Squid proxy...
-
 192Data Security
192Data SecuritySilk Road 3.0 Pops Up on the Dark Web, Once Again
Silk Road makes another appearance, but will it last? A new instance of the infamous Silk Road marketplace has popped up on the...
-

 128Data Security
128Data SecurityEverything We Know About How the FBI Hacks People
RECENT HEADLINES WARN that the government now has greater authority to hack your computers, in and outside the US. Changes to federal...
-

 170Data Security
170Data SecurityGhostShell Returns, Exposes a Bunch of Companies with Open FTP Servers
GhostShell, the Romanian hacker who recently revealed his true identity in a very candid exposé, has returned to the world of hacking...
-
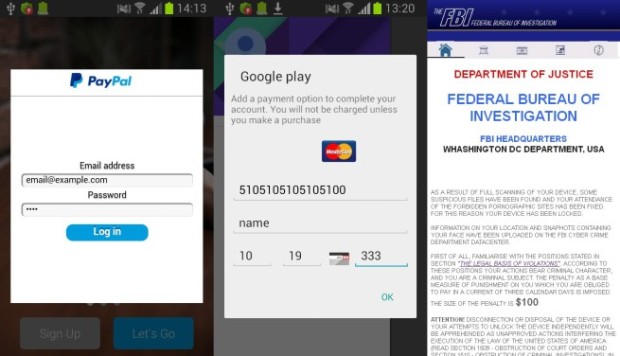
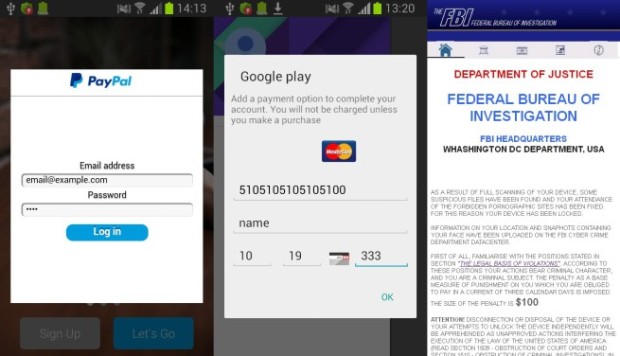 99Malware
99MalwareAndroid.SmsSpy.88.origin
A Trojan for Android designed to steal user login credentials needed to access online banking programs and to steal money from victims’...
-

 220Geek
220GeekLinus Torvalds Releases Linux 4.6 With New Features — Download Now
Short Bytes: After seven release candidates, the Linux 4.6 kernel was officially released by Linus Torvalds on May 15. As the third...
-

 282Geek
282GeekApple Deletes App That Informed Users If Their iPhone is Hacked
Apple has removed a security App from its app store claiming it’s misleading and confusing for users — The app was developed...
-

 350Geek
350GeekThePirateBay.se is now ThePirateBay.org
Good news for The Pirate Bay fans — Though The Pirate Bay’s .SE domain is now a thing of past, the .org domain...
-
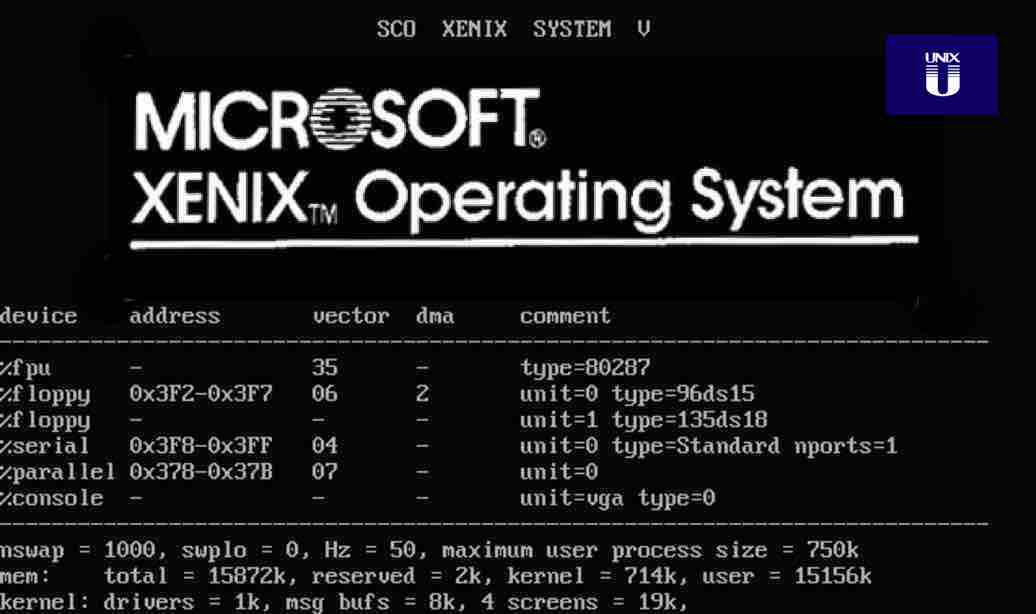
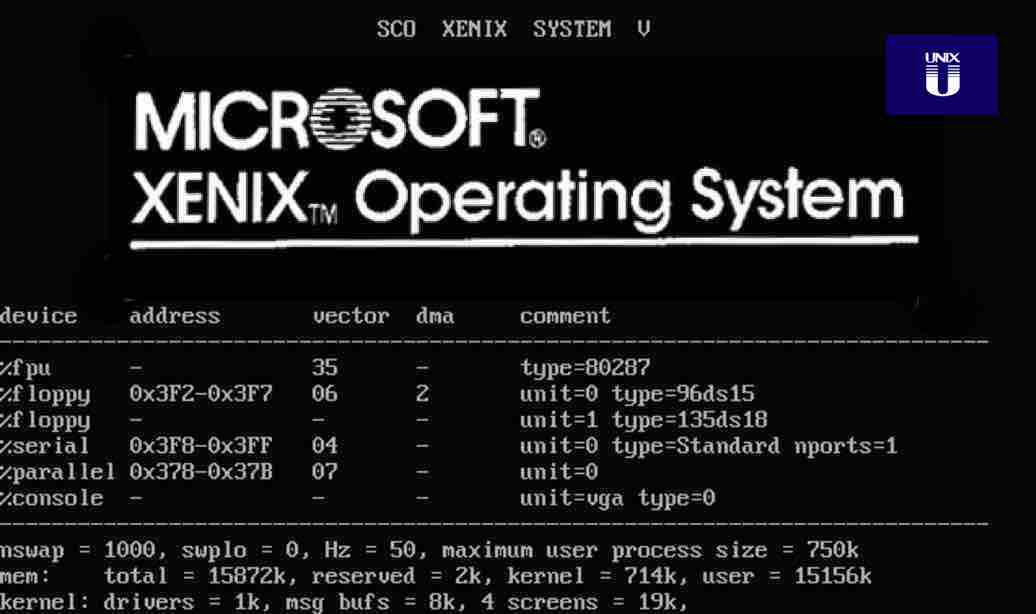 216Geek
216GeekHistory Of Xenix — Microsoft’s Forgotten Unix-based Operating System
Short Bytes: Long before Linus Torvalds wrote Linux, Microsoft was the king of Unix world. The company, somehow, developed Xenix, the most...
-
 319Geek
319GeekItalian Military Adopts Open Source LibreOffice And Saves 29 Million
Short Bytes: As a result of last year’s announcement that Italian Ministry of Defence will ditch Microsoft’s Office suite and adopt open...
-

 318News
318NewsAnonymous Shut Down 5 More Banking Websites for OpIcarus
Anonymous OpIcarus is underway and the new targets include banking sites in France, UAE, Philippine, Tunisia, Trinidad and Tobago! It looks like the online...
-

 256Geek
256GeekGovernment Spy Truck Guided As Google Street View Car on the Prowl in Philadelphia
In a modern technology case of do not judge a book by its cover, a Philadelphia police surveillance van designed as a...
-
 357Geek
357GeekRed Hat Enterprise Linux 6.8 Released With New Features — The Most Popular Server Linux
Short Bytes: Red Hat recently announced the latest iteration of its widely popular enterprise Linux — Red Hat Enterprise Linux 6.8. This release comes with...
-

 232Exploitation
232ExploitationCJExploiter – Drag and Drop ClickJacking Exploit Tool
CJExploiter is drag and drop ClickJacking exploit development assistance tool. First open the “index.html” with your browser locally and enter target URL...
-

 112How To
112How ToHow To Make iPhone Apps Work on Linux Using Cydia
First of all your iPhone must be jailbroken before you can use Cydia to make iPhone apps work on Linux. Log on...
-

 188Hacked
188HackedISIS Launches Mobile App For Children, Uses Guns And Missiles For Teaching Alphabets
Short Bytes: After releasing dedicated chat and radio apps, ISIS has released their first app directed specifically at children. This app aims...
-

 108Data Security
108Data Security4 Ways to Protect Against the Very Real Threat of Ransomware
RANSOMWARE IS A multi-million-dollar crime operation that strikes everyone from hospitals to police departments to online casinos. It’s such a profitable scheme...
-

 64Incidents
64IncidentsTwo billboards in Alabama hacked to run Marco Rubio Porn Meme
Marco Rubio Memes flash on 2 Alabama billboards after apparent hack. Alabama citizens may have had the fright of of their life...
-

 100Geek
100GeekPixelSynth — JavaScript-based Chrome Experiment Converts Your Images Into Music
Short Bytes: Ever imagined how your picture will “sound” if converted into music? Now, using a new Chrome Experiment called PixelSynth, you...
-
 165Data Security
165Data SecurityHancitor and Ruckguv Reappear, Updated and With Vawtrak On Deck
Proofpoint researchers have recently observed the re-emergence of two malware downloaders that had largely disappeared for several months. Hancitor (also known as...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




