Featured News
-
 230Hack Tools
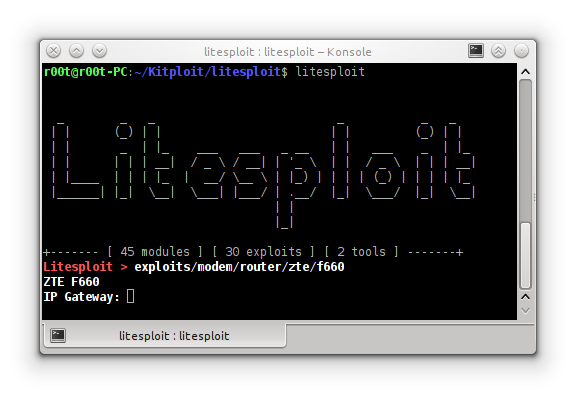
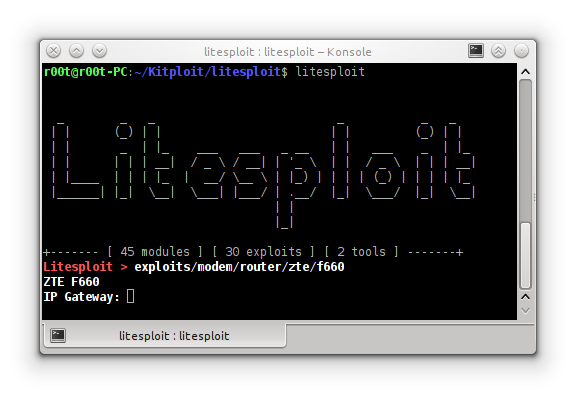
230Hack ToolsLitesploit – Library and Intepreter for Penetration Testing Tools
Litesploit is a library and intepreter for penetration testing tools. This includes exploits, tools and litepreter. Litesploit support for Linux like ubuntu...
-

 211Data Security
211Data SecurityChinese ARM vendor left developer backdoor in kernel for Android, other devices
Allwinner’s ARM Linux kernel includes “rootmydevice” code that gives apps root. Allwinner, a Chinese system-on-a-chip company that makes the processor used in...
-

 65Incidents
65IncidentsWhat the hack? More than 88,000 .sg accounts stolen by hacker
Last week, US-based cyber security firm Hold Security recovered 272.3 million stolen accounts from a fraudster. What the hack? More than 88,000...
-

 89Data Security
89Data SecurityFacebook wants to teach you how to hack
Can you capture the flag? Facebook’s Capture the Flag program can be used to teach basic security skills. Facebook wants to teach...
-
 167Incidents
167IncidentsCompression tool 7-Zip pwned, pain flows to top security, software tools
Attackers can score user privileges thanks to heap corruption hassle Some of the world’s biggest security and software vendors will be rushing...
-
 104Data Security
104Data SecurityAndroid Malware Promises Porn, but Roots Device and Installs Other Malware
Android malware is not unusual; we’ve even seen it pop up in Google’s Marketplace app on several occasions. Increasing in both sophistication...
-

 86Data Security
86Data SecurityMozilla Begs Court for Details About Pedophile Tor Hack to Keep Firefox Safe
In 2015, the FBI hacked Tor to identify users of child sex websites. Now, Mozilla is begging courts to divulge to it...
-

 247Geek
247GeekElectron 1.0 Released By GitHub — Build Native Apps Easily For Linux, Windows, And OS X
Short Bytes: GitHub has just released the version 1.0 of Electron, its free and open source application building platform. After two years of...
-
 587How To
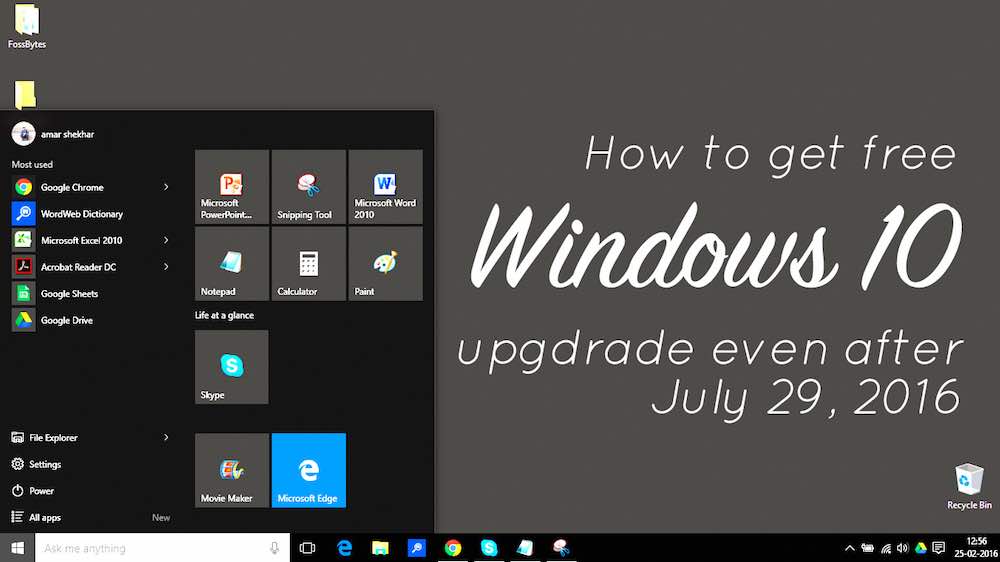
587How ToHow To Get Windows 10 Upgrade For Free Even After July 29, 2016?
Short Bytes: Microsoft is killing the free Windows 10 upgrade offer after July 29, 2016. But, what to do if you want...
-

 275Hacked
275HackedStory Of A Bored Reddit Hacker — “I Stole Tons Of Subreddits Just For Fun”
Short Bytes: A bored hacker has been playing around with several subreddits for almost a week and there is nothing that Reddit...
-
 187Hacked
187HackedAllwinner’s Linux Kernel Code Has An Easy-to-use Root Debug Backdoor
Short Bytes: The code of Linux kernel of Chinese chipmaker Allwinner contains an easily exploitable root backdoor. Combined with networked services, this could...
-

 112News
112NewsThis Hacker Got Bored, Wanted Some Fun So He Defaced Several Subreddits
A hacker is taking over subreddits and exposing Reddit’s poor security! Some hack for cause, some hack for money but @TehBVM on...
-

 301Cyber Crime
301Cyber CrimeUS Congress Dumps Yahoo Mail Over Phishing Attacks
Yahoo mail Hammered by Congress for its Inefficiency in Preventing Phishing Attempts Symantec’s newest threat report claims that email phishing scams have...
-

 207Geek
207GeekFedora 24 Beta Is Released — Linux Fans, This Is The Future Of Linux Desktop
Short Bytes: Fedora 24 Beta release is out for testing with the latest features. This latest build is powered by the newest...
-

 297News
297NewsMicrosoft Disabling Controversial Wi-Fi Sense Feature in Windows 10
Microsoft Disabling Controversial Wi-Fi Sense Feature in Upcoming Windows 10 Anniversary Update Windows 10 users can breathe a sigh of relief because...
-

 360How To
360How ToHow To Get Faster Internet Connection Speed – The Complete Guide
Short Bytes: To get a faster internet connection speed, one can practice different methods and hacks. These methods to accelerate your internet speed...
-

 200Data Security
200Data SecurityPornhub Bug Bounty Program: Report critical flaws, earn $25,000
The famous adult content website Pornhub has decided to let hackers report security flaws and vulnerability on its computer system and earn...
-
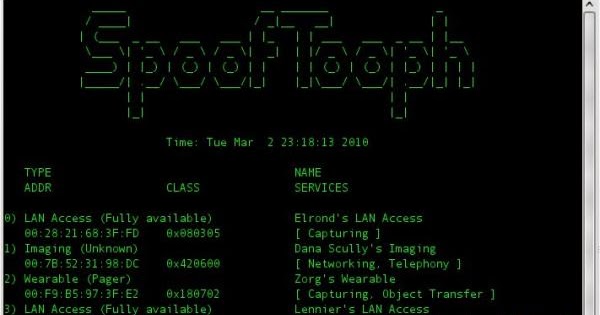
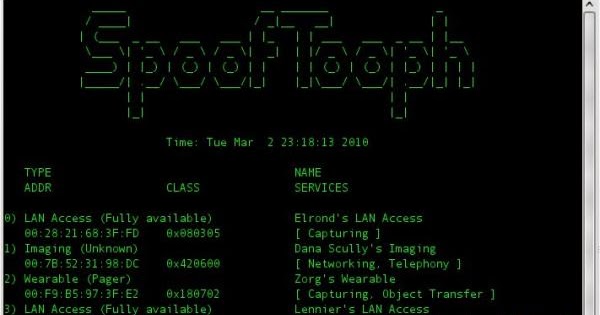 211Spoofing
211SpoofingSpoofing a Bluetooth device
Spooftooph is designed to automate spoofing or cloning Bluetooth device Name, Class, and Address. Cloning this information effectively allows Bluetooth device to...
-

 146Data Security
146Data SecurityHey FBI, India can Hack iPhones but Doesn’t Want Backdoors
Maybe the FBI should team up with India because that country’s government says it can hack into Apple’s iPhones. Both think access...
-

 330Hacked
330HackedFacebook Open Sources Its Hacking Game Platform Capture the Flag (CTF)
Short Bytes: Facebook has open sourced its hacking game platform Facebook Capture the Flag (CTF). Students and schools can take advantage of...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




