Featured News
-

 134Data Security
134Data SecurityUkrainian Hacker Admits Role in Hacking Three Business Newswire Services
More suspects are expected to admit their crimes as well. Vadym Iermolovych, 28, of Kiev, Ukraine, pleaded guilty yesterday for his role in...
-

 134Data Security
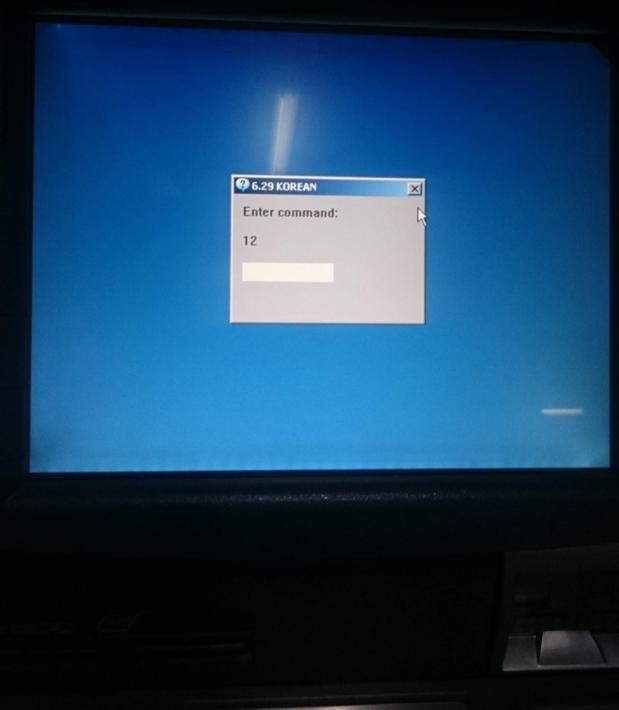
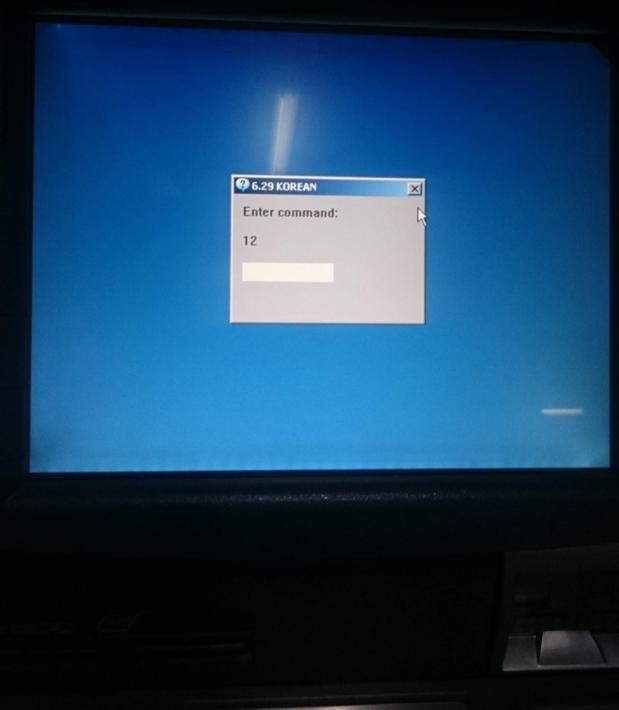
134Data SecurityTech Support Scammers Get Serious With Screen Lockers
Tech support scammers are well aware of what is going on in the malware scene and often rip off ideas and concepts from...
-
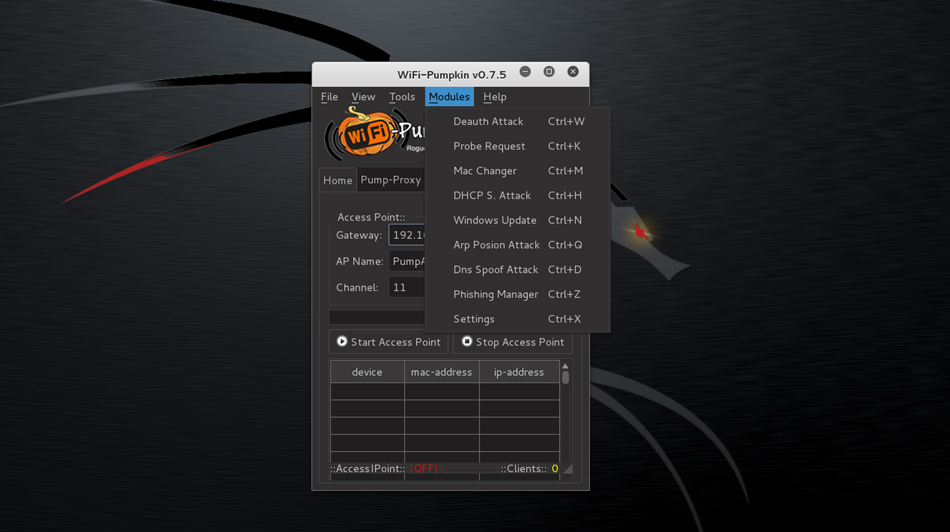
 107Hack Tools
107Hack ToolsWIFI Pumpkin – Framework for Rogue Wi-Fi Access Point Attack
WiFi-Pumpkin is a security tool that provides the Rogue access point to Man-In-The-Middle and network attacks. Installation Kali 2.0/WifiSlax 4.11.1/Parrot 2.0.5 Python...
-

 215Incidents
215IncidentsClick Fraud: 1M machines hacked for AdSense revenue
Online advertising is a multi-billion dollar business mostly ran by Google, Yahoo or Bing via AdSense-like programs. The current generation of clickbots such as...
-
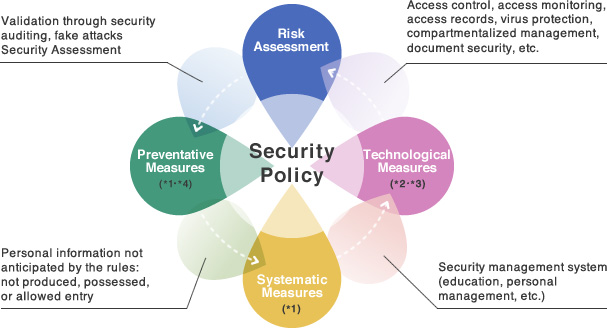
 73Data Security
73Data SecurityHow to implement Data Security Management System?
According to the global perspective of enterprise data security company; integrity, confidentiality, availability, auditability, and non-repudiation are the five fundamental pillars for...
-
 212Incidents
212IncidentsBank Hack – How to steal $25 Billion with a few lines of code
A security expert discovered security flaws that could let anyone to steal as much as $25 Billion from one of the biggest...
-
 152Data Security
152Data SecurityATM Malware “Skimer” Makes a Comeback After Seven Years
Crooks can steal money from ATMs using special credit cards. Skimer, a malware family targeting ATMs, has received a major update the past...
-

 157News
157NewsAnonymous Target North Carolina Government Sites Against anti-LGBT Law
Can a Bathroom Bill Compel Anonymous to Take Down Websites in North Carolina? — Sure it can! Anonymous, the world’s most active...
-

 87Data Security
87Data SecurityGoogle ‘Could Face Record $3.4 Billion’ Antitrust Fine
Google faces a record antitrust fine of around 3 billion euros ($3.4 billion) from the European Commission in the coming weeks, British...
-
 391Data Security
391Data SecurityHow to do secure data destruction of information from storage devices?
There are statistical evidences supported by data destruction companies which present that in countries like Mexico, Brazil, United States, Colombia, Costa Rica,...
-
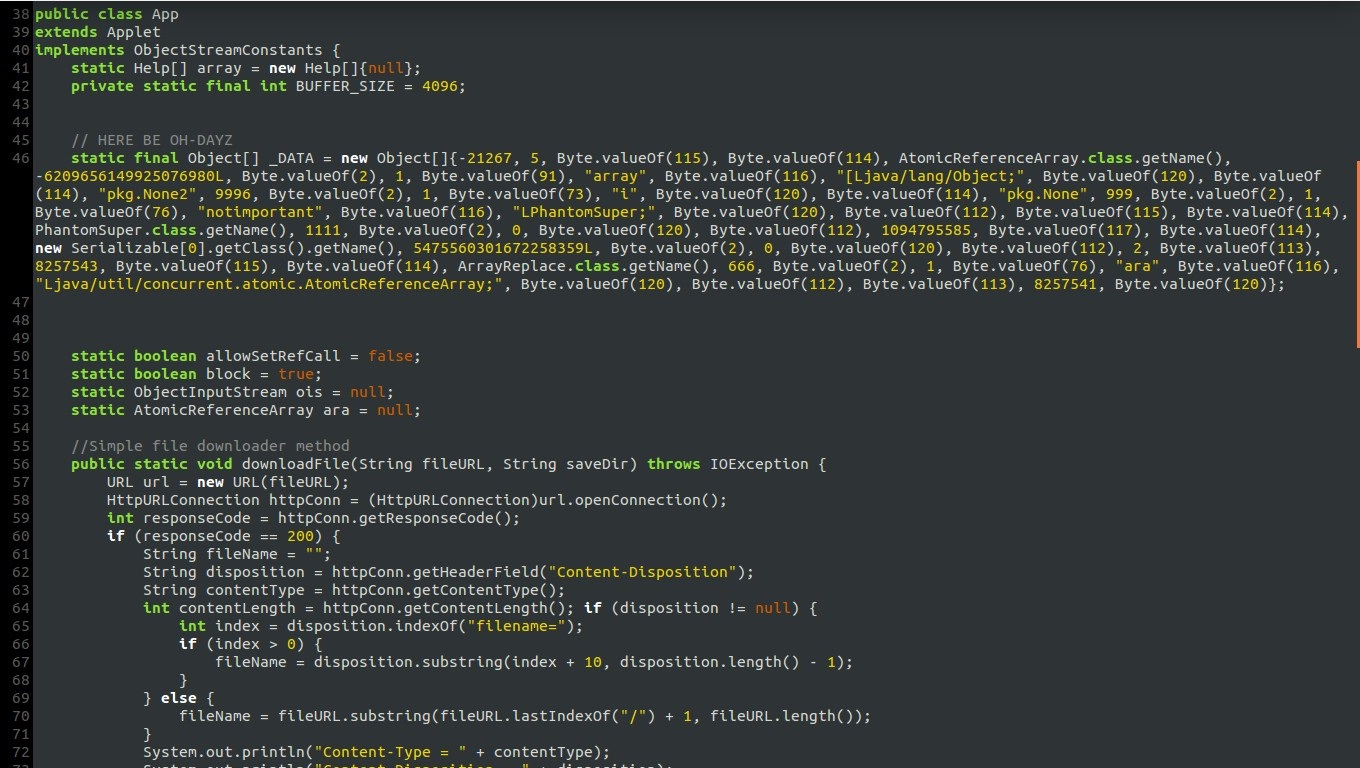
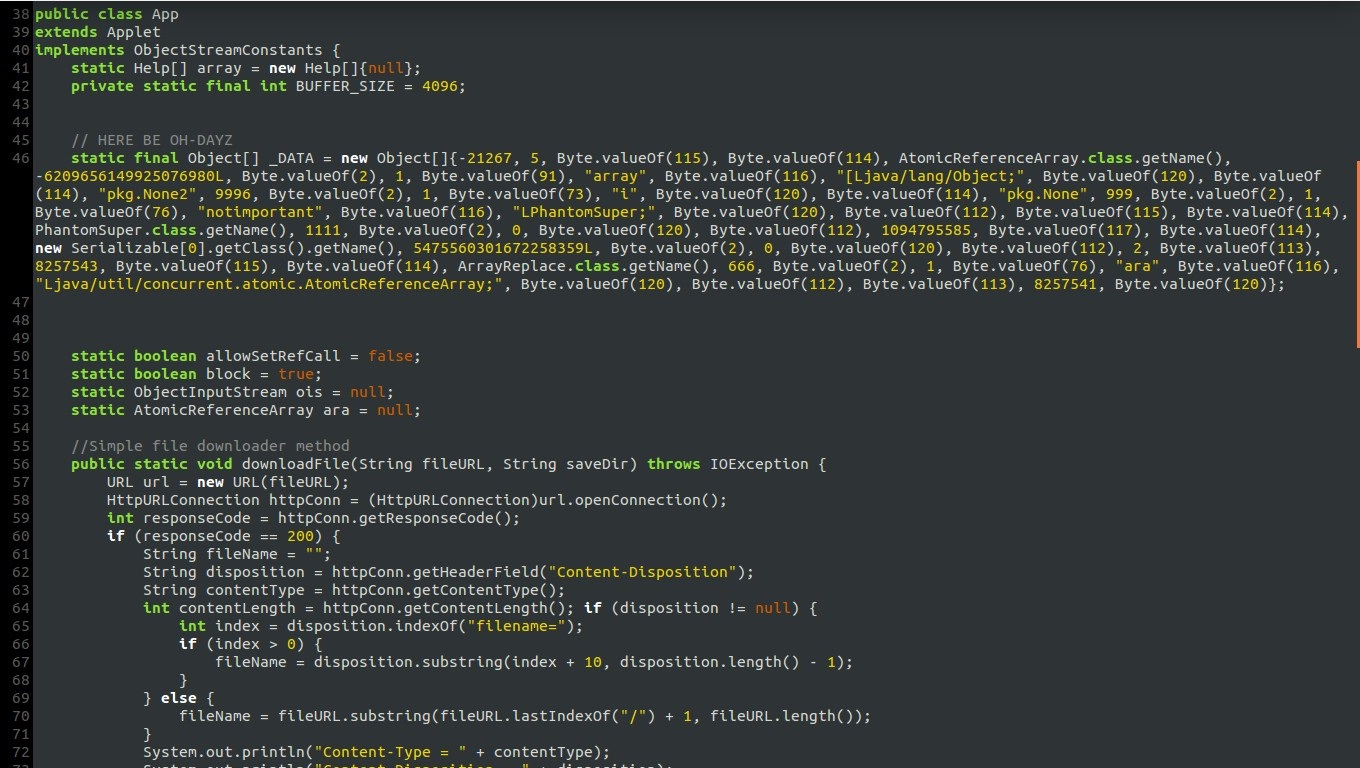 195Data Security
195Data SecurityHow to do malware reverse engineering
Malicious Software can be Virus, Worm, Trojan Horse, Rootkit, Bot, DoS Tool,Exploit kit, Spyware. The objective of malware analysis is to gain...
-
 167Data Security
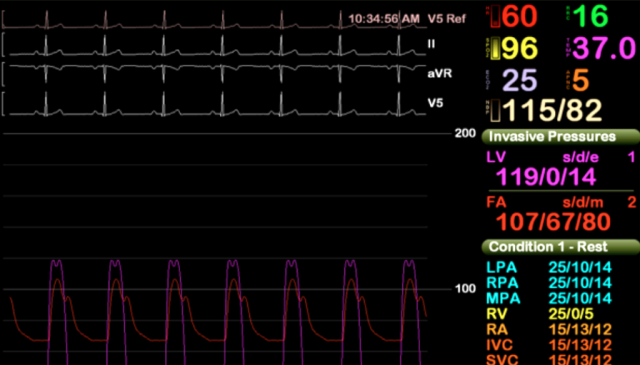
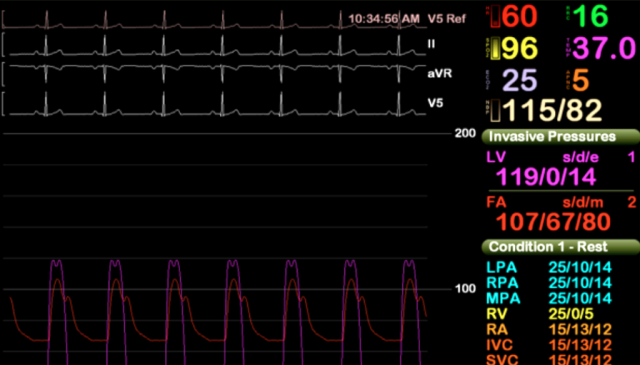
167Data SecurityThat time a patient’s heart procedure was interrupted by a virus scan
Securing computers has never been easy. It’s especially hard in hospitals. A heart patient undergoing a medical procedure earlier this year was put...
-
 236Hacked
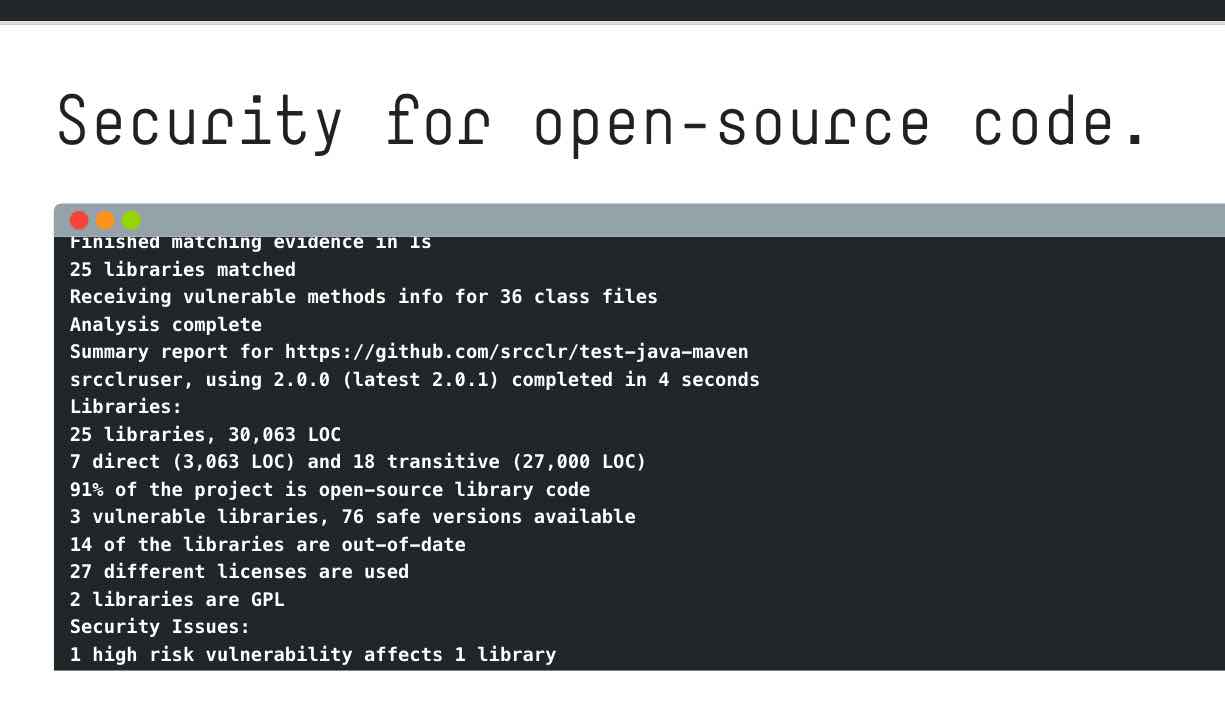
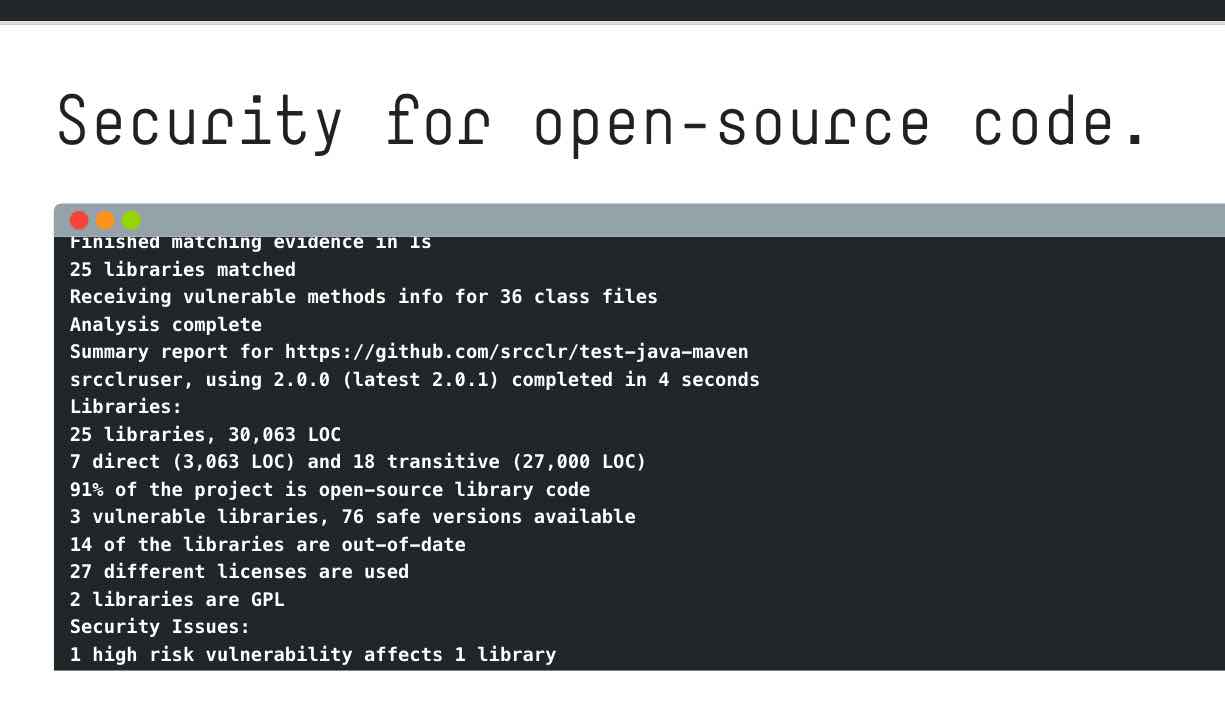
236HackedSourceClear’s Free Tool “Open” Finds Vulnerabilities In Your Open Source Code
Short Bytes: SourceClear’s Open is a new tool to find potential threats in the open source code. This tool works for different...
-

 170Incidents
170IncidentsJohn McAfee Apparently Tried to Trick Reporters Into Thinking He Hacked WhatsApp
John McAfee, noted liar and one-time creator of anti-virus software, apparently tried to convince reporters that he hacked the encryption used on...
-
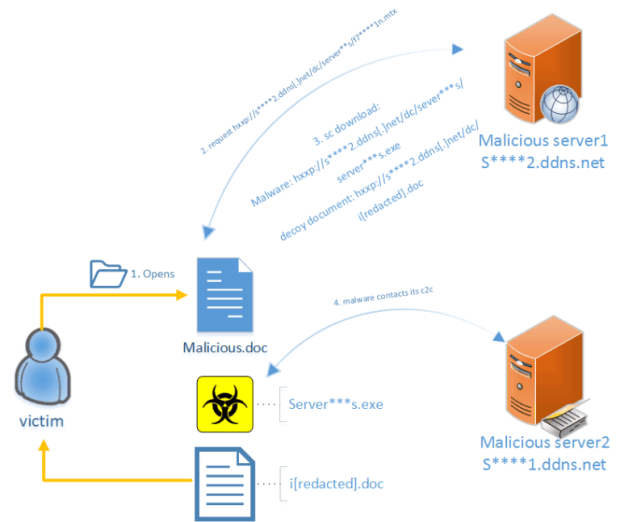
 177Vulnerabilities
177VulnerabilitiesCVE-2016-4117 – FireEye revealed the exploit chain of recent attacks
The FireEye researcher Genwei Jiang revealed the exploit chain related to phishing attacks leveraging CVE-2016-4117 flaw recently fixed by Adobe. Security experts...
-
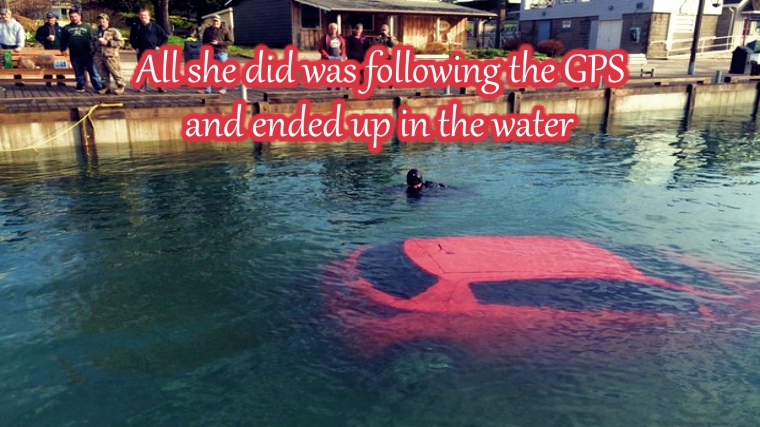
 240Geek
240GeekWoman Follows GPS, Goes Straight into Lake
A woman driver found herself in ”deep water” after following a GPS which directed her car right into Lake Huron in Ontario, Canada....
-

 363News
363NewsNulled.IO Hacking Forum Hacked, Trove of Data Stolen
Nulled.io, one of the largest buying and selling forum for hacked content has been hacked and almost everything has been stolen! The...
-

 224Cyber Crime
224Cyber CrimePrivacy and security fears – predictably – impact US online commerce
US government data say 45% curtail online activity due to privacy and security fears, which is sad but not surprising because we...
-

 352News
352NewsPornHub Gets Hacked Days After Launching Bug Bounty Program
A teen hacker has taken over PornHub servers and sold the data for $1000 — PornHub claims it’s just a hoax! The famous adult...
-

 202News
202NewsOpAfrica: Anonymous Deface South African University, Huge Data Leaked
Anonymous hacks university of Limpopo website leaks a trove faculty and student data for OpAfrica! New World Hackers (NWH), a group of hackers linked...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




