Featured News
-

 256Data Security
256Data SecurityHow Traffic to This YouTube Video Predicts ISIS Attacks How Traffic to This YouTube Video Predicts ISIS Attacks
A YouTube video’s best day, traffic-wise, is usually the day it gets posted. Clicks generally decline quickly and post-launch spikes are rare....
-

 157Data Security
157Data SecurityQatar National Bank Declares Systems ‘Fully Secure’ Sequel To Cyber-attack
Following the recent security breach suffered by the Qatar National Bank has assured that its systems are “fully secure”. Sequel to a...
-

 337How To
337How ToHow To Disable Write Protection In SD Card Or Pen Drive?
You might have struggled with situations where Windows isn’t able to copy anything to a write-protected storage media. This article will help...
-

 118Malware
118MalwareFBI Announcement: Paying The Ransom is a Bad Idea
Hey Folks! So late last year a quote was going around about a comment for the Special Agent in charge of the...
-

 167Vulnerabilities
167VulnerabilitiesImageTragick Exploit Used in Attacks to Compromise Sites via ImageMagick 0-Day
imageMagick project hopes to publish a patch today. Two Russian security researchers revealed a few hours ago a vulnerability in the ImageMagick image...
-

 348Geek
348Geek10-year-old Kid Hacks Instagram, Gets $10,000 Reward from Facebook
A 10-year-old kid from Finland found a bug allowing access to Instagram servers and delete any text posted by Instagram users. If...
-

 361Geek
361GeekFake Google Chrome Update Leads to Android Malware Stealing Personal Data
Android Users Beware- This New Malware can Retrieve Banking Information and Track your Texts For Android users, using their devices has become...
-

 133News
133NewsNew anti-hacking law promises life imprisonment to vehicle hackers
If you are an IT security researcher or a hacker and living in the Michigan State you may consider to move somewhere else...
-

 118News
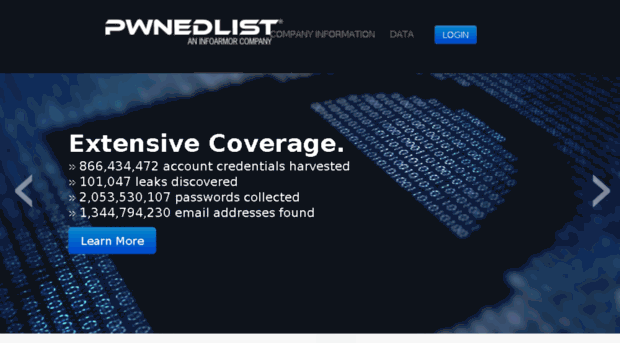
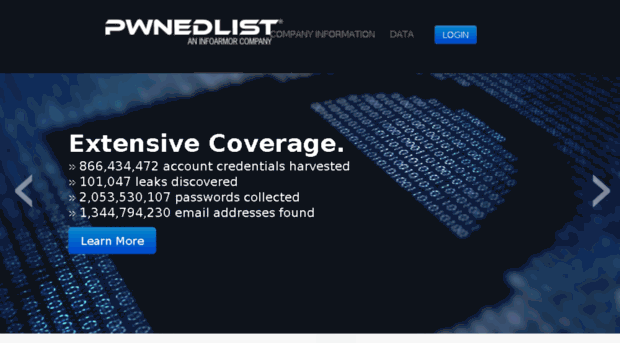
118NewsPwnedList Gets Pwned, shutting down service in few days
PwnedList is a tool that allows an average person to check if their accounts have been compromised — The company has decided...
-

 154Incidents
154IncidentsHacker who stole from banks ordered to pay $7 million
A hacker whose creation stole bank account details from over a million computers across the globe has been ordered to pay $6.9...
-

 70Data Security
70Data SecurityAustralian computer scientist claims he is Satoshi Nakamoto who created bitcoins
Australian computer scientist claims he is the elusive Bitcoin creator, Satoshi Nakamoto. The hunt for creator of world’s most popular cryptocurrency, the Bitcoin...
-

 76Data Security
76Data SecurityMichigan Senate Bills Would Give Car Hackers Life In Prison
The FBI sent out a PSA just over a month ago warning us all about the risks of car hacking, but drivers...
-
 199Hacked
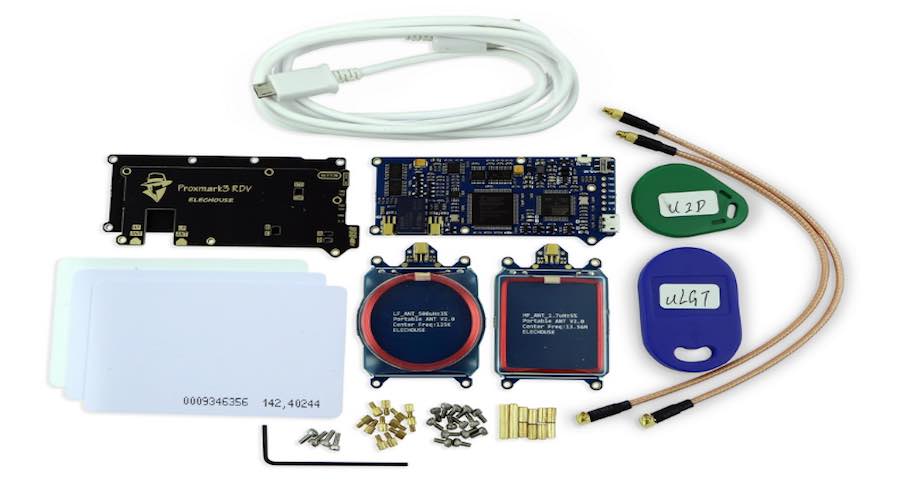
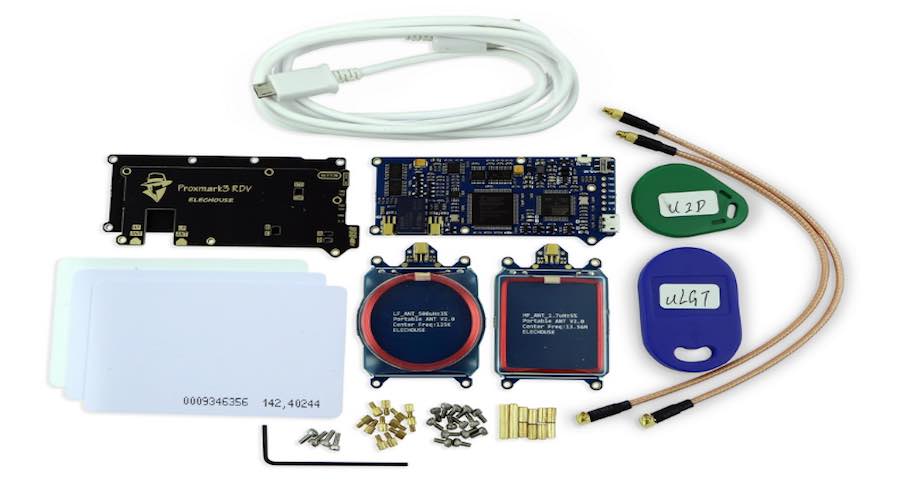
199HackedHere’s How Hackers Can Break Into Any Office With This Easily Available Device
Proxmark Short Bytes: In a recent demonstration, a team of white hat hackers showed how an attacker can compromise the corporate security...
-
 79Incidents
79IncidentsA flaw in the PwnedList service exposed millions of credentials
A serious expert discovered a flaw in PwnedList service that could have been exploited to access millions of account credentials managed by...
-
 258Vulnerabilities
258VulnerabilitiesValve Fixes Steam Crypto Bug That Exposed Passwords in Plaintext
19-year-old college student fixes Steam’s crypto. Valve has updated the Steam gaming client to fix a severe security issue in the application’s crypto...
-

 313News
313NewsAnonymous Target Bank of Greece Website with Massive DDoS Attack
Anonymous shut down the bank of Greece website in a powerful DDoS attack — Vows to target more banks against financial corruption....
-

 318Geek
318GeekConsider Selfie Sticks Old-School — Time to use Hover Drones for Selfies
You can now walk along with this drone and it will take selfies for you! We all know that while using a...
-

 108Data Security
108Data SecurityFlaws in Samsung’s ‘Smart’ Home Let Hackers Unlock Doors and Set Off Fire Alarms
A SMOKE DETECTOR that sends you a text alert when your house is on fire seems like a good idea. An internet-connected...
-

 251Malware
251MalwareDecrypted: Alpha Ransomware accepts iTunes Gift Cards as Payment
A new ransomware called Alpha Ransomware was discovered and analyzed this week by Katja Hahn, S!Ri, MalwareHunterTeam, and Michael Gillespie. This ransomware encrypts your data...
-
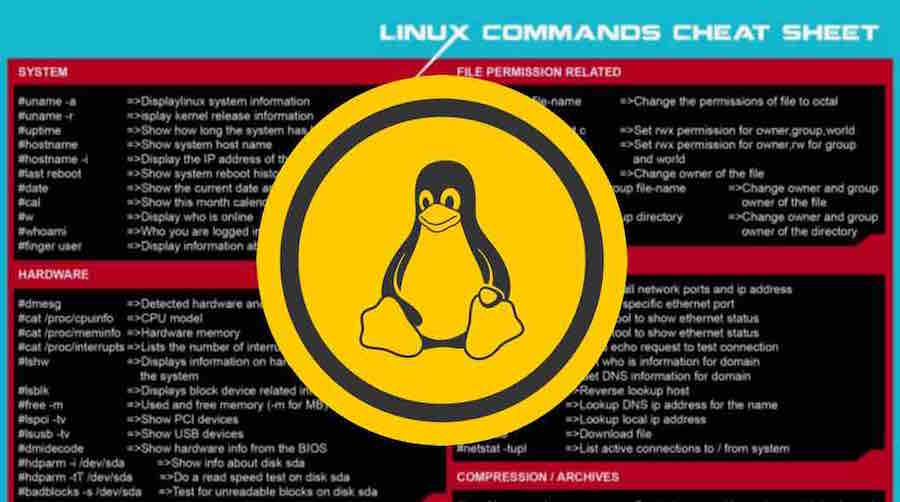
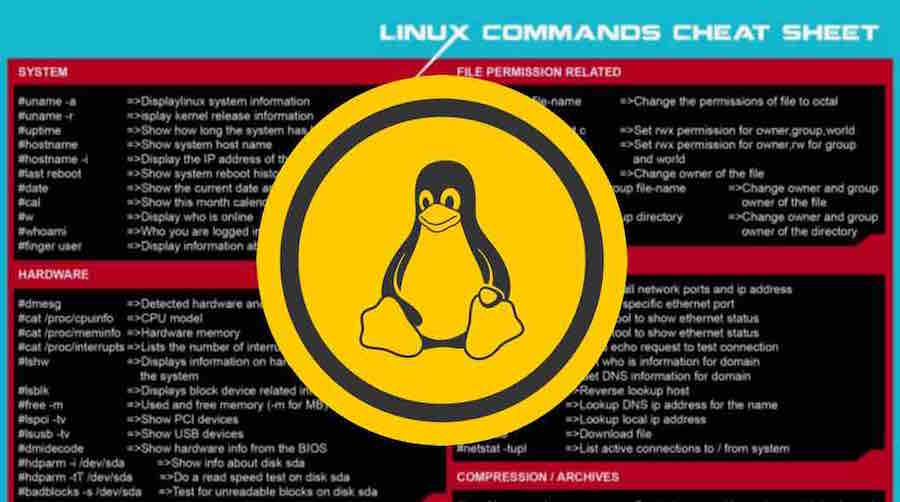 276Geek
276GeekLearn The Basic Linux Commands With This Awesome Cheat Sheet
Short Bytes: Here I’m sharing a useful Linux commands cheat sheet that you can print and keep it as a learning guide...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




