Featured News
-

 192Hacked
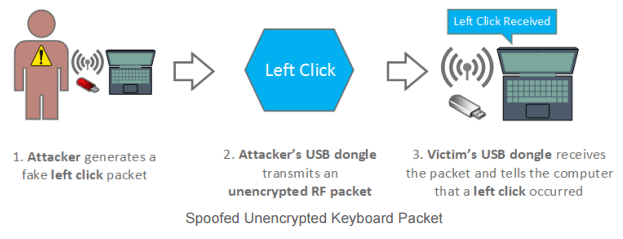
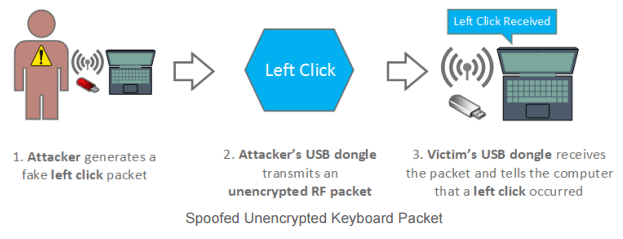
192HackedMousejack: Hacking Computers Via Your Mouse With 15 Lines Of Code And Radio Dongle
Short Bytes: A new hack, known as ‘Mousejack’, performed by the security firm Bastille Networks, shows that your wireless mouse and keyboards...
-

 323Surveillance
323SurveillanceEncrypted Email Startup Tutanota Reaches 1 Million Users
Necessity is the mother of invention, the old adage has proved its worth again when a German-based company has successfully won the...
-

 95Malware
95MalwarePorn clicker trojans keep flooding Google Play
ESET researchers have found 343 malicious porn clicker trojans on Google Play over the last seven months – and their numbers keep...
-

 78Malware
78MalwarePorn clicker trojans at Google Play: An analysis
ESET researchers have found a large campaign of malicious porn clicker type apps on Google Play. These trojans belong to a single...
-

 83Malware
83MalwareMalware targets India’s largest private bank
Over 4,000 branches and 13,000 ATMs were targeted through a massive phishing campaign. Customers of ICICI, India’s largest private bank, have become...
-
 137Data Security
137Data SecurityMousejack attack – Hijack Wireless Mouse/Keyboard Dongles from 100 meters to control PCs
Mousejack attack – Researchers at Bastille firm demonstrated how to hack computers by exploiting a flaw in many wireless mouse and keyboard...
-

 90Malware
90MalwareAndroid ransomware variants created directly on mobile devices
Attackers used legitimate tools on mobile devices to create variants of Android.Lockdroid.E. Symantec has seen several variants of a known ransomware family (Android.Lockdroid.E)...
-
 269Geek
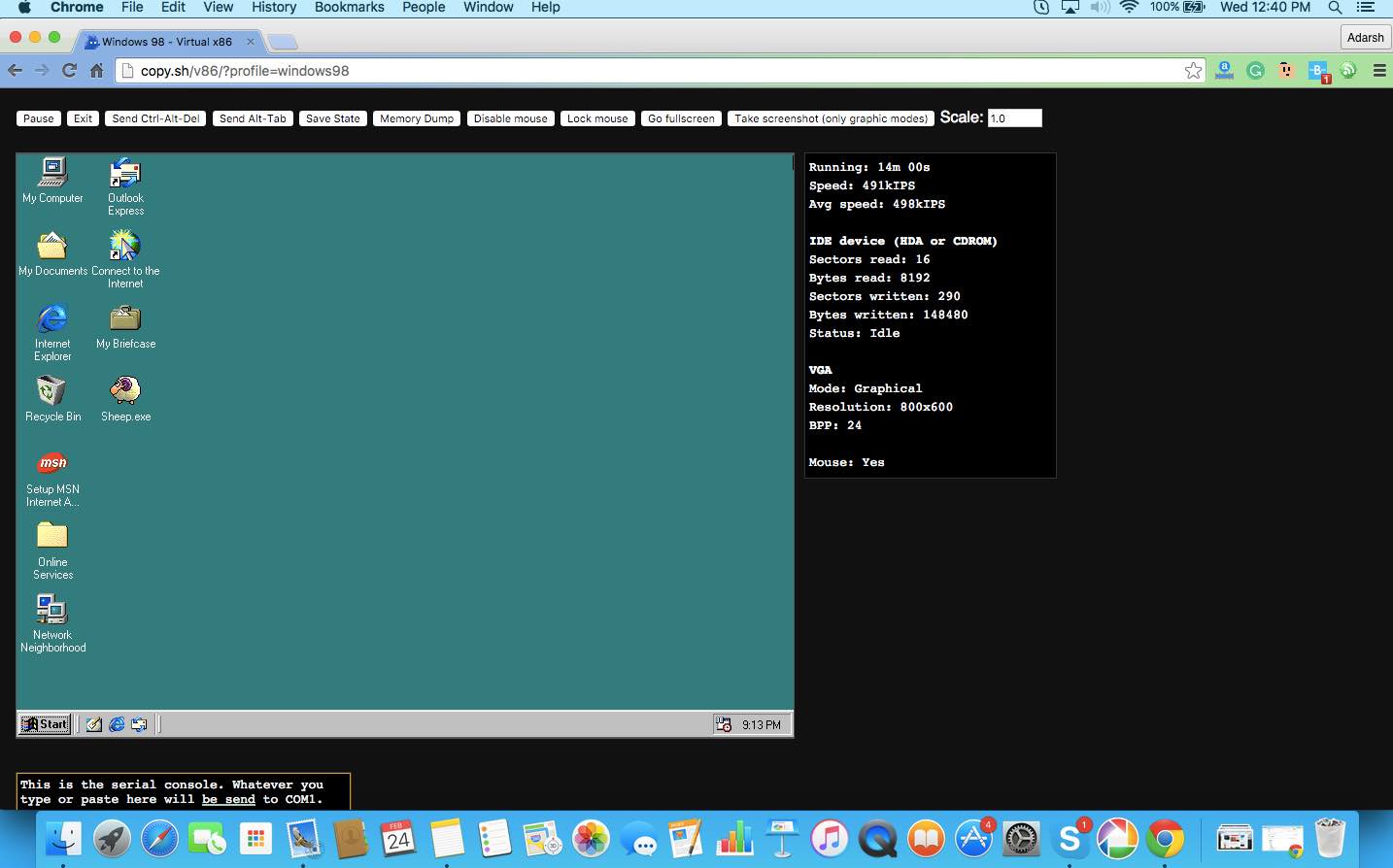
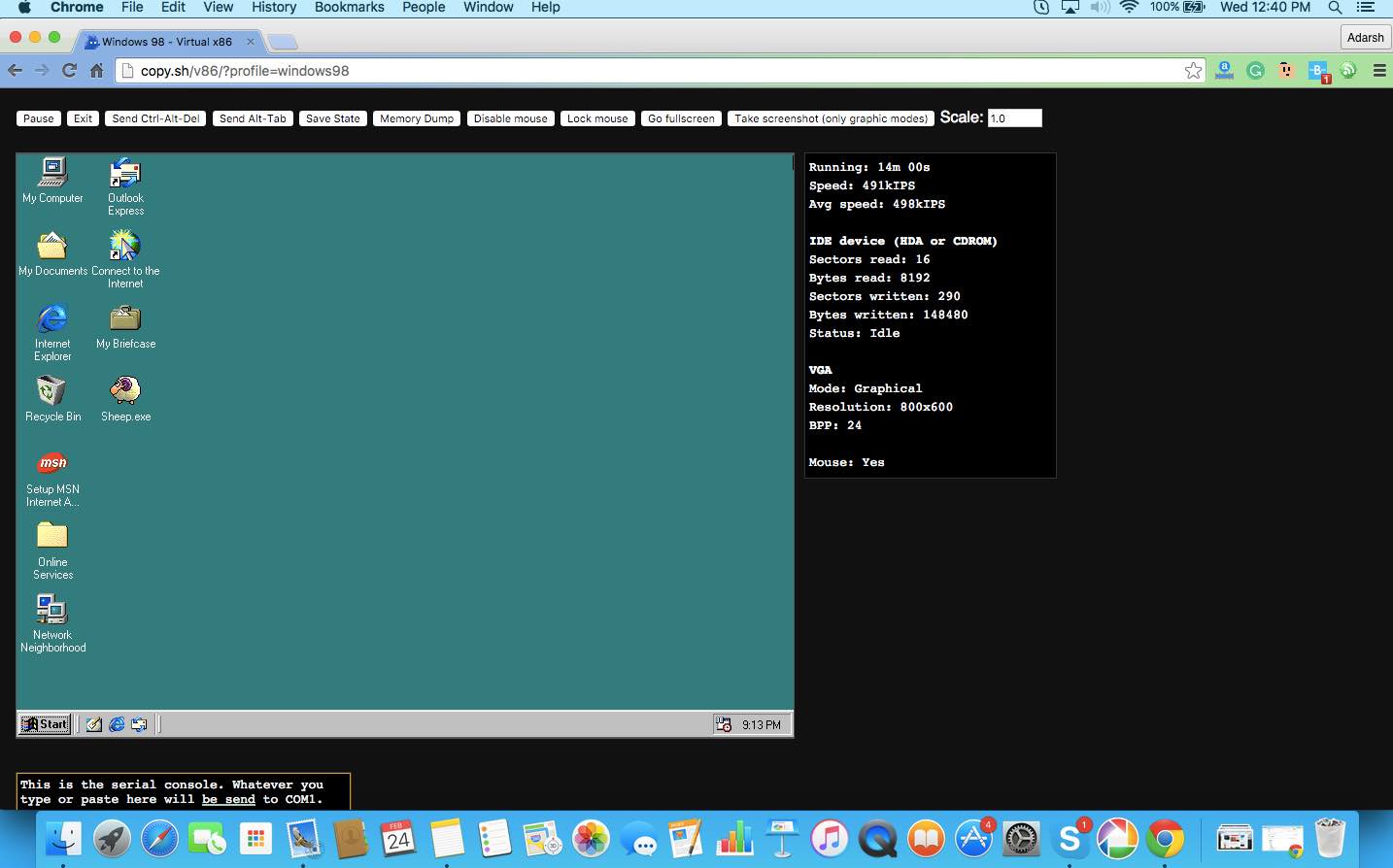
269GeekRun Windows 98 And Linux In Your Web Browser, Thanks To JavaScript And NodeJS
Short Bytes: A coder, known as Fabian on GitHub, has created x86 architecture based emulations that allow you to run Windows 98,...
-

 193Vulnerabilities
193VulnerabilitiesNew Silverlight Attacks Appear in Angler Exploit Kit
Exploits for a vulnerability in Microsoft Silverlight have found their way into the dangerous Angler Exploit Kit a little more than a...
-
 276Incidents
276IncidentsAnonymous hacked the France’s Ministry of Defense portal CIMD (Centre d’Identification des Materiels de la Defense)
Anonymous hacked the CIMD portal managed by the France’s Ministry of Defense to protest against French foreign arms trade operations. The Anonymous...
-

 279Data Security
279Data SecurityYears old DNS Bug can be used to spread Malware across World Wide Web
Old is gold for sure but in this case old is bad and bold Google’s security researcher Dan Kaminsky along with Redhat...
-

 317Cyber Crime
317Cyber CrimeMan Who Hacked and Stole Celebrity Nude Photos Pleads Guilty
Remember The Fappeneing? It looks like the police have got their guy! The 29-year-old Andrew Helton was accused of accessing nude images...
-

 272Cyber Events
272Cyber EventsMost Americans Want Apple to Cooperate with the FBI- Claims Pew Survey
The survey shows Americans are actually supporting FBI on the iPhone encryption issue. We all know about the heated debate going on...
-

 412Geek
412GeekWhat Is Programming And Why You Should Learn To Code?
Short Bytes: With the advent of new online opportunities, learning how to code is easier than ever. Read more to know why...
-

 172Data Security
172Data SecurityNSA Data Center Experiences Up to 300 Million Cyber-Attacks per Day
Six years ago, the cyber-attacks barely reached 25,000. Utah officials are saying that the number of cyber-attacks they’ve seen against local state organizations...
-
 183Android Hacking
183Android HackingTurn old Smart Phone to Security Camera
If you have a lot of old smart phones at home, but don’t know what to do with them? Well here’s a...
-
Malware
Android porn clicker on Google Play: Appendix
Trojan clicker servers Google Play information Package names of trojan clickers found on the infected servers
-

 238Kids Online
238Kids OnlineDigital childhoods: How different nations bring up their kids
ESET has looked deeper into what parents in the United States, Germany, the United Kingdom and Russia regard as the appropriate age...
-

 459Kids Online
459Kids Online4 internet‑savvy countries agree: Kids go digital too early
Online surveys by ESET show that a majority of parents in Russia, the United Kingdom, Germany and the United States are not...
-
 57Data Security
57Data SecurityRussian bank employees received fake job offers in targeted email attack
Employees at six Russian banks were sent spoofed emails delivering Trojan.Ratopak in a narrow, targeted attack. In December 2015, employees from several...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




