Featured News
-

 249Lists
249Lists21 Top Programming Languages On GitHub And Stack Overflow – January 2016
Short Bytes: RedMonk has just published its list of the top 21 programming languages of 2016 Q1. This list is based on...
-

 235Cyber Crime
235Cyber CrimeAnonymous Hit Italian Government Sites Against Trans Adriatic Pipeline Project
Anonymous Italy Launches #OperationGreenRights- Targets Italian Government Portals with DDoS Local government portals of Apulia and Basilicata regions in southern Italy have...
-
 177Geek
177GeekFacebook Reactions — What’s it all About?
The legendary Like button will no longer be gracing our Facebook pages as frequently as it regularly does since Facebook Reactions are...
-

 287How To
287How ToHow To Enable Windows 10 Fast Startup: The Ultimate Windows 10 Guide
Short Bytes: Windows 10 Fast Startup feature is an inbuilt feature of Windows 10 which saves some Windows 10 files upon shutdown...
-
 219News
219NewsAnonymous France’ Trio Due to be Sentenced in March for Targeting Police sites
Anonymous activists’ Trio Due to be Sentenced in March for Targeting French Police and Government French judicial system is known for its...
-

 98Cyber Crime
98Cyber CrimeWhy cybercrime isn’t fun and (video) games
Research shows that the average age of cybercrime suspects last year was just 17 years-old. We Live Security asks why, and suggests...
-

 213Vulnerabilities
213VulnerabilitiesFTC Forces Asus to Comply with 20 Years of Security Audits
Asus lied about its routers’ security, it delayed security patches for months, and now it’s paying the price. A few months back, the...
-

 94Data Security
94Data SecurityThe DoD funded the Carnegie Mellon University’s research on Tor Hacking
A judge has confirmed that US Departement of Defense funded the Carnegie Mellon University to conduct research on the Tor hacking. In...
-
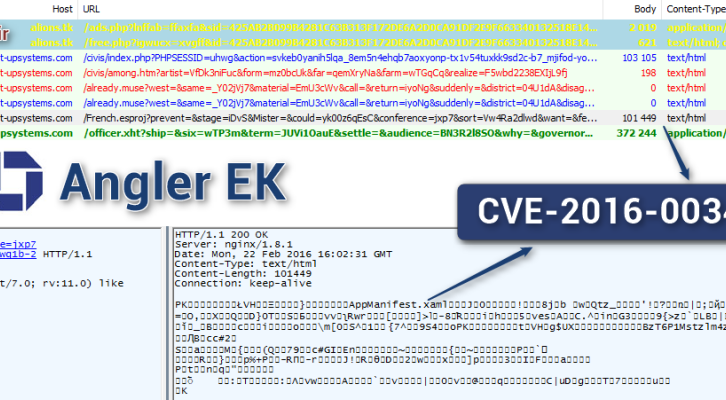
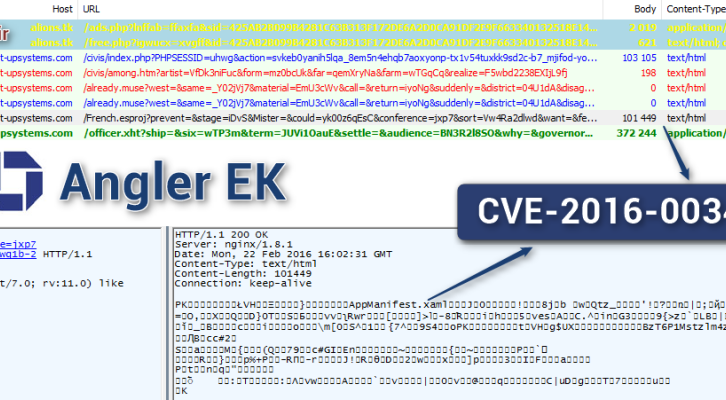 182Vulnerabilities
182VulnerabilitiesAuthor of the Angler EK integrated recently Silverlight exploit
The security researcher Kafeine confirmed that the authors of the Angler EK have integrated the exploit for a recently patched Microsoft Silverlight...
-

 67Malware
67MalwareMalware and skimmers, explosions and hammers: How attackers go after ATMs
Survey, YouTube offer proof that people are blowing up ATMs to get the cash inside. What was the best way to steal...
-

 95Data Security
95Data SecurityThis journo got hacked while covering the FBI vs Apple iPhone hack story
Journalist gets hacked while writing the FBI vs Apple iPhone hack story. The recent United States court’s order to Apple for hack San...
-

 303Cyber Events
303Cyber EventsNissan Leaf Maybe At Threat Because of Vulnerable APIs
Security researchers show how an attacker can access Nissan Leaf electric car by exploiting vulnerability in APIs By using the Application Program...
-

 270Geek
270GeekHow To Code Your Own Personal Assistant Using Python Programming
Short Bytes: In this article, I’m sharing the efforts of a programmer to create his own python-powered personal assistant. Using open source...
-
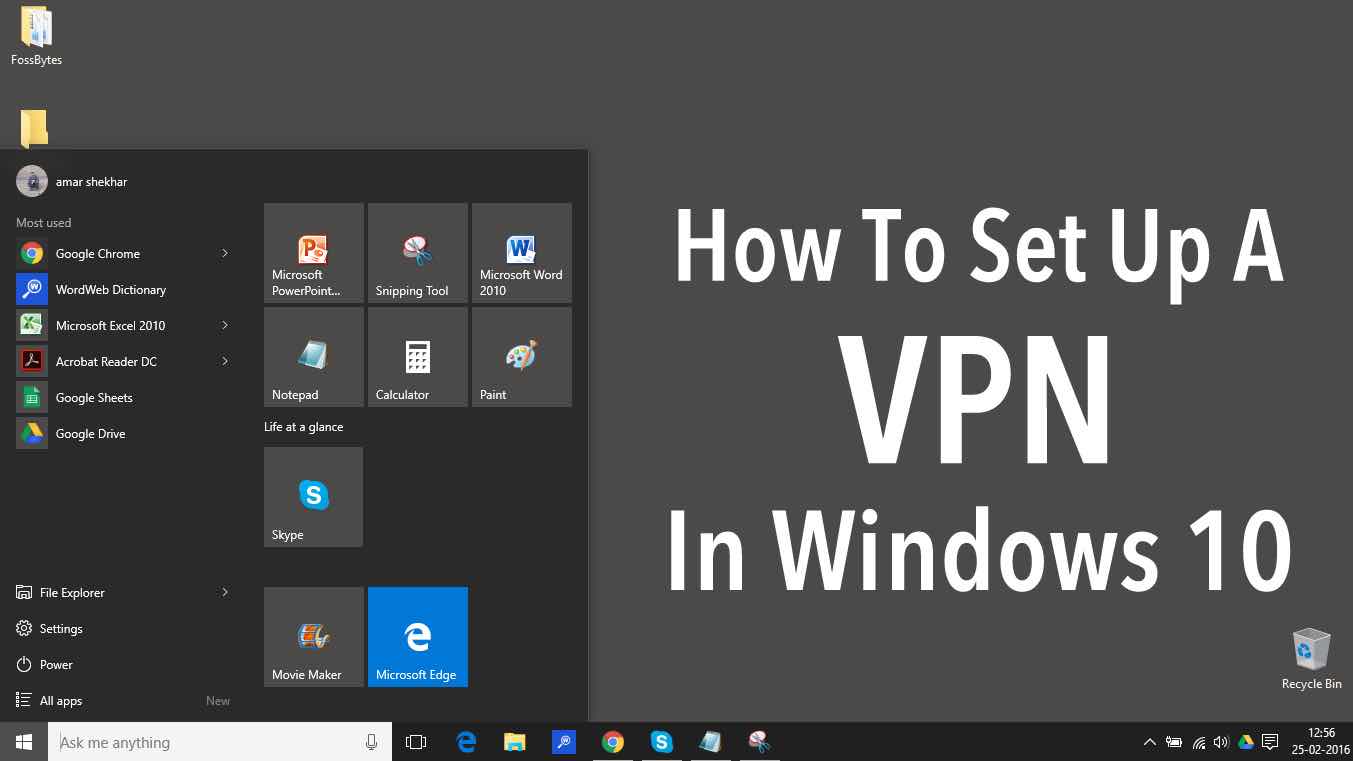
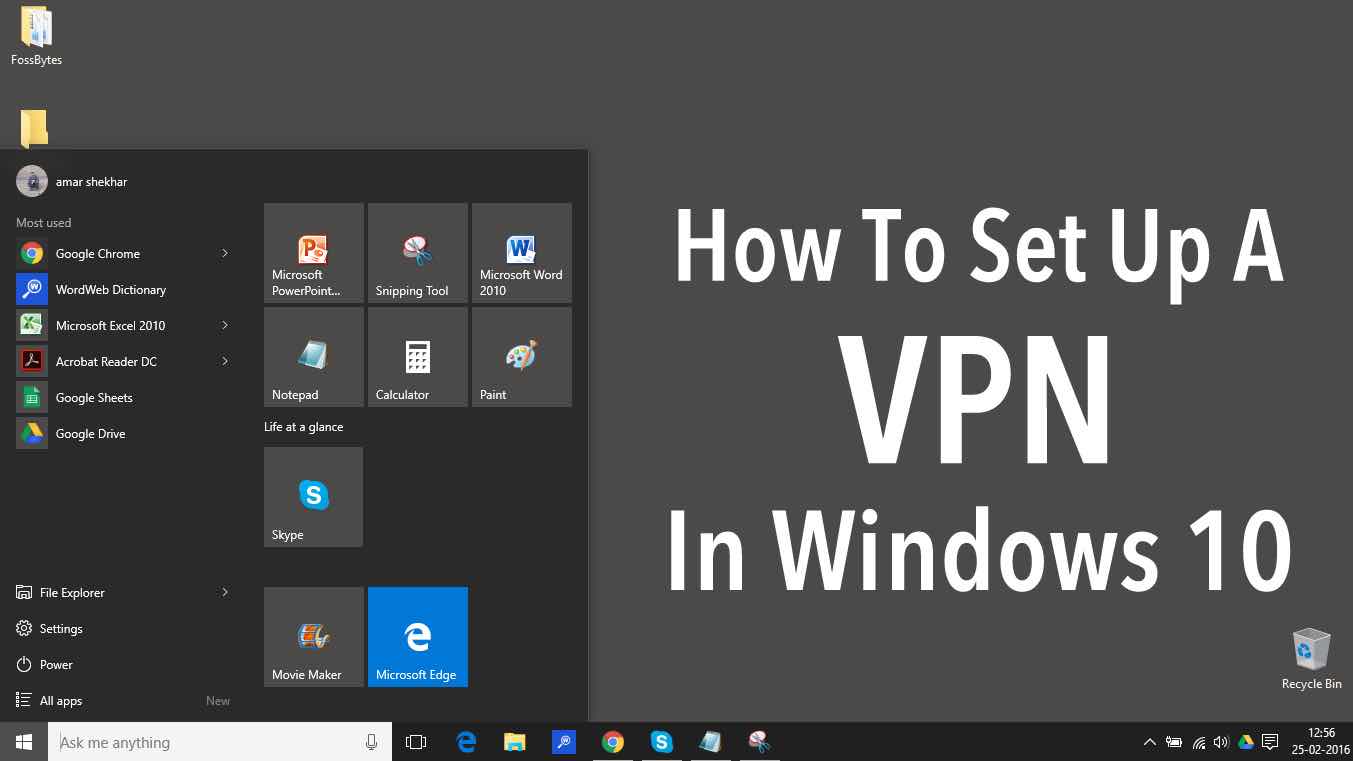 363How To
363How ToHow To Set Up A VPN In Windows 10: The Ultimate Guide
Short Bytes: How to set up a VPN in Windows 10? — This question is often asked by many Windows 10 users. This...
-
 230Geek
230GeekWhat Code Should You Learn in 2016?
Why you should learn to code? Apple Founder Steve Jobs once said in an interview: “I think everybody in this country should...
-

 341Hacked
341HackedAcecard: One Of The Most Advanced Android Trojans Of Our Time
Short Bytes: AceCard has become one of the most advanced Android Trojans with severe dangerous capabilities like sneaking into any social or...
-

 194Data Security
194Data SecurityRemotely hacking a Nissan LEAF via vulnerable APIs
The security expert Troy Hunt discovered that it is possible to remotely control features of a Nissan Leaf via API. The popular...
-

 171Malware
171MalwareGerman police can now use spying malware to monitor suspects
Limited power to eavesdrop contrasts painfully with UK’s far-ranging Snooper’s Charter. German police are now permitted to infect a suspect’s computers, and...
-

 311Lists
311ListsWindows Keyboard Shortcuts Cheat Sheet For Windows 10
Short Bytes: With the launch of Windows 10, Microsoft also launched newer Windows keyboard shortcuts. These Windows Keyboard shortcuts use almost all the alphabets...
-
 205Data Security
205Data SecurityRicochet peer-to-peer messenger uses power of the dark web to escape metadata
Ricochet is the most secure encrypted anonymous messenger that sends no metadata. The security experts have approved a new internet messaging tool...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




