Featured News
-

 313News
313NewsAnonymous Hacker Behind “OpJustina” Arrested by The FBI
Disney Cruise Ship Rescues Anonymous-associated Hacker and Hands him over to the FBI. The twists and turns of fate are hard to...
-

 121Hacked
121HackedGoogle, Microsoft, Facebook, Twitter, WhatsApp Are Backing Apple Against FBI
Short Bytes: The Cupertino-based company was asked by the US court to unlock the Syed Rizwan Farook’s iPhone 5C which the FBI...
-

 190Vulnerabilities
190VulnerabilitiesVXE Flaw allowed threats to bypass FireEye detection engine
Researchers at Blue Frost Security firm discovered a flaw in the FireEye Virtual Execution Engine (VXE) that allows an attacker to completely...
-

 285Geek
285GeekiPhone Encryption Debate Lingers On – Google Extends Support to Apple
Google Stands with Apple on the Encryption Issue — Yes, this is Big and this comes as a Surprise no doubt! The...
-

 245Hacked
245HackedNitro Zeus: USA’s Secret Cyber War Plan To Destroy Iran’s Complete Infrastructure
Short Bytes: Alex Gibney is known for his investigative documentaries that garner a unanimous applause from the critics. During the reporting for his...
-

 193Data Security
193Data SecurityRemotely Disabling a Wireless Burglar Alarm
Countless movies feature hackers remotely turning off security systems in order to infiltrate buildings without being noticed. But how realistic are these...
-

 128Cyber Crime
128Cyber CrimeHow the threat experts see it …
A unique survey among threat experts has revealed that most cyberattacks against a typical IT infrastructure take less than 24 hours to...
-

 109Incidents
109IncidentsWordPress Sites Leveraged in Layer 7 DDoS Campaigns
We first disclosed that the WordPress pingback method was being misused to perform massive layer 7 Distributed Denial of Service (DDoS) attacks back in...
-

 301Hacked
301HackedAnonymous Hacker Arrested By The FBI In Hospital Computer Hacking Case
Short Bytes: Martin Gottesfeld, the alleged Anonymous hacker responsible for 2014’s hacking attack at Boston Children’s Hospital, has been arrested by the FBI....
-

 163Vulnerabilities
163VulnerabilitiesMillions of AirDroid Users Exposed to Severe Vulnerability
A new vulnerability in the AirDroid App was revealed by Check Point. This vulnerability affects the 50 million AirDroid users around the...
-
 288Hacked
288HackedThe Most Important Fight For Data Security: Why Apple Must Win Against FBI?
ShortBytes: In response to the Federal court order which was issued to Apple, the maker of iPhone, to help the FBI hack...
-

 103Malware
103MalwareWhy Tim Cook is right to call court-ordered iPhone hack a “backdoor”
Custom version of iOS could undo years of work Apple put into securing iPhones. Tuesday’s court order compelling Apple to hack the iPhone...
-

 342Geek
342GeekApple defiant in San Bernardino Shooting Case; says no to backdoor access
Judge Issues Order to Apple to Unlock iPhone Vital in the San Bernardino Shooting Case — Apple refuses to follow orders The...
-

 119Data Security
119Data SecuritySouthampton University Creates 5D Storage Disc That Can Store 360TB Data
The mindblowing invention will revolutionise the way we store data Last year the researchers came up with a processor capable of transmitting...
-

 176How To
176How ToHow To Access Your Chrome Passwords Remotely From Any Browser?
Short Bytes: Google has introduced a new online feature where a user can sync its passwords to Google and access Chrome passwords...
-

 317Cyber Crime
317Cyber CrimeCybercriminals Hack Hospital PCs Demand Whopping 9000 BTC Ransom
Ransomware Infects Hollywood HealthCare Facility Computers – Attackers Demand $3.6M Computers are an integral part of almost every field and industry nowadays...
-

 269Data Security
269Data SecurityThe NSA’s SKYNET program may be killing thousands of innocent people
“Ridiculously optimistic” machine learning algorithm is “completely bullshit,” says expert. In 2014, the former director of both the CIA and NSA proclaimed that...
-

 233Vulnerabilities
233VulnerabilitiesHow to bypass this LG smartphone’s fingerprint security in just 30 seconds
A troubling vulnerability has been uncovered that may make you think twice about ever even temporarily allowing a friend, partner or acquaintance...
-

 180Malware
180MalwareDridex: Financial Trojan aggressively spread in millions of spam emails each day
Built to harvest the banking credentials of victims, the virulent Dridex is now one of the most dangerous pieces of financial malware...
-
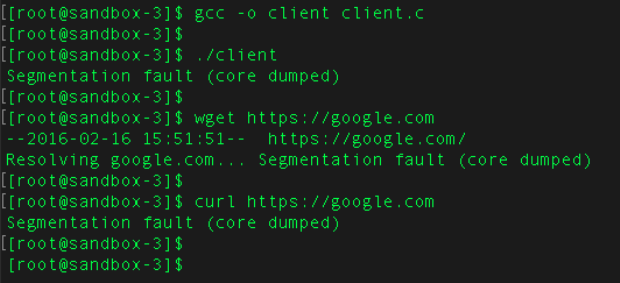
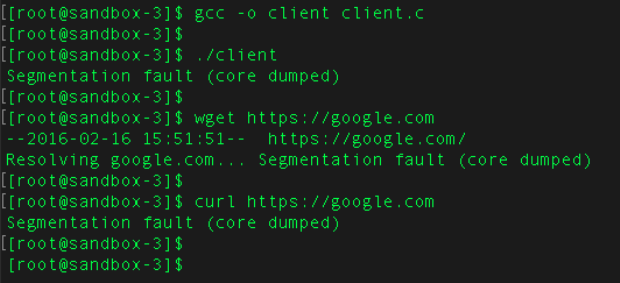 146Vulnerabilities
146VulnerabilitiesExtremely severe bug leaves dizzying number of software and devices vulnerable
Since 2008, vulnerability has left apps and hardware open to remote hijacking. Researchers have discovered a potentially catastrophic flaw in one of the...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




