Featured News
-

 263News
263NewsAnonymous Hacks South African Job Portal Against Child Labour
Anonymous hackers breached a South African job portal which hosts job fair for the locals — However, Anonymous decided to leak the...
-

 168Data Security
168Data SecurityIRS website attack nets e-filing credentials for 101,000 taxpayers
Breach comes a year after a previous hack compromised 300,000 people. The US Internal Revenue Service was the target of a malware attack...
-

 224Hacked
224HackedThese Vigilante Hackers Aim To Hack 200,000 Routers To Make Them More Secure
Short Bytes: Remember the white hat hackers — The White Team — responsible for creating the Linux.Wifatch malware last October? The same hackers...
-

 334Hacked
334HackedThis Malware In 1,163 Android Apps Can Root Your Smartphone Without Your Permission
Short Bytes: Third party app stores cannot always guarantee the user safety with each app they hand out to a user. On...
-
 105Vulnerabilities
105VulnerabilitiesTwitter bug allows hackers to hijack big Twitter accounts like @God, @Vagina etc
A password reset flaw allowed hacker to hijack numerous Twitter accounts from their original owners. Twitter followers of @god, @emoji, and @vagina were...
-

 362Data Security
362Data Security10 Famous Bug Bounty Hunters of All Time
If you are following HackRead you must be aware of what is bug bounty and how it works but did you know...
-
 232Geek
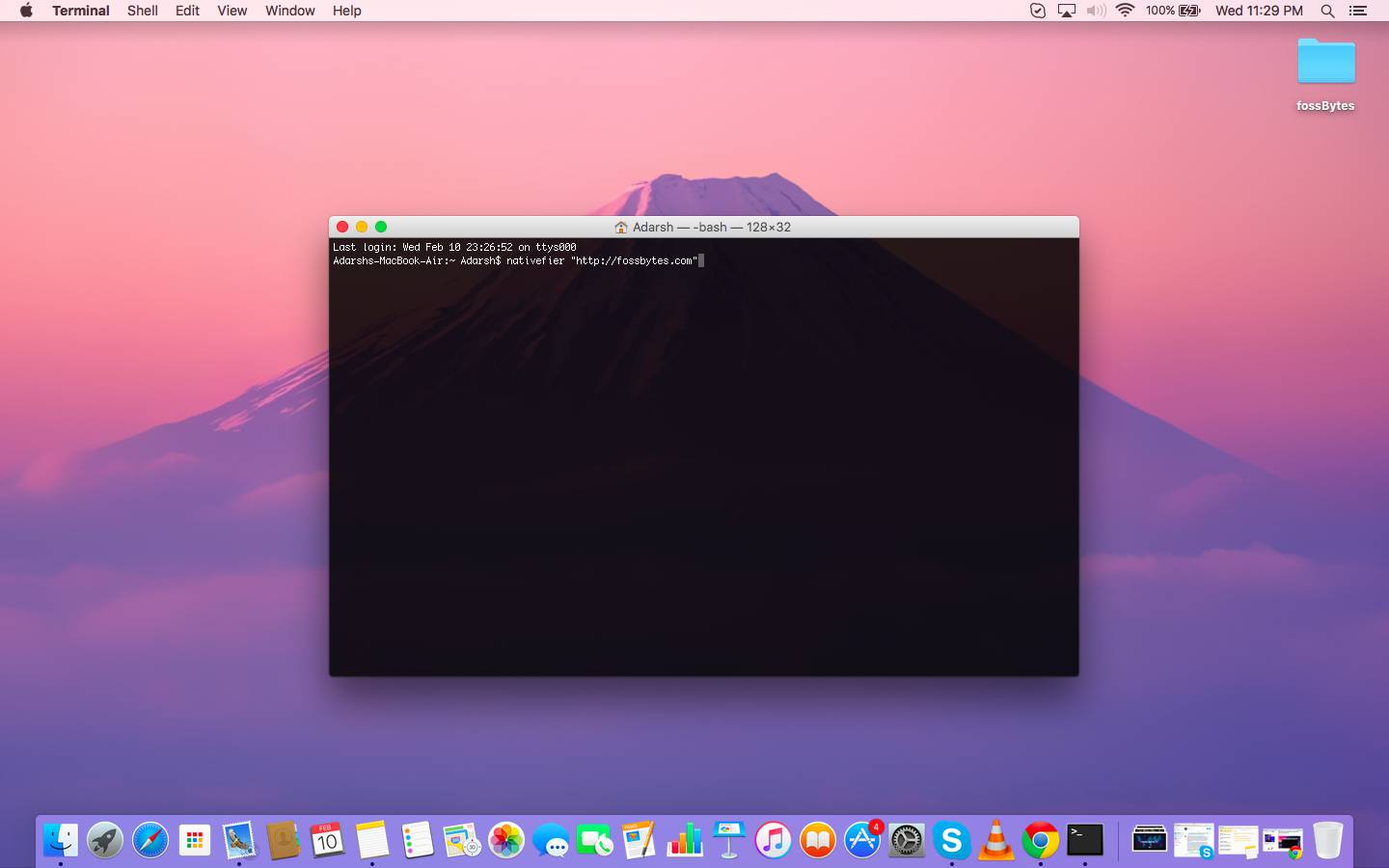
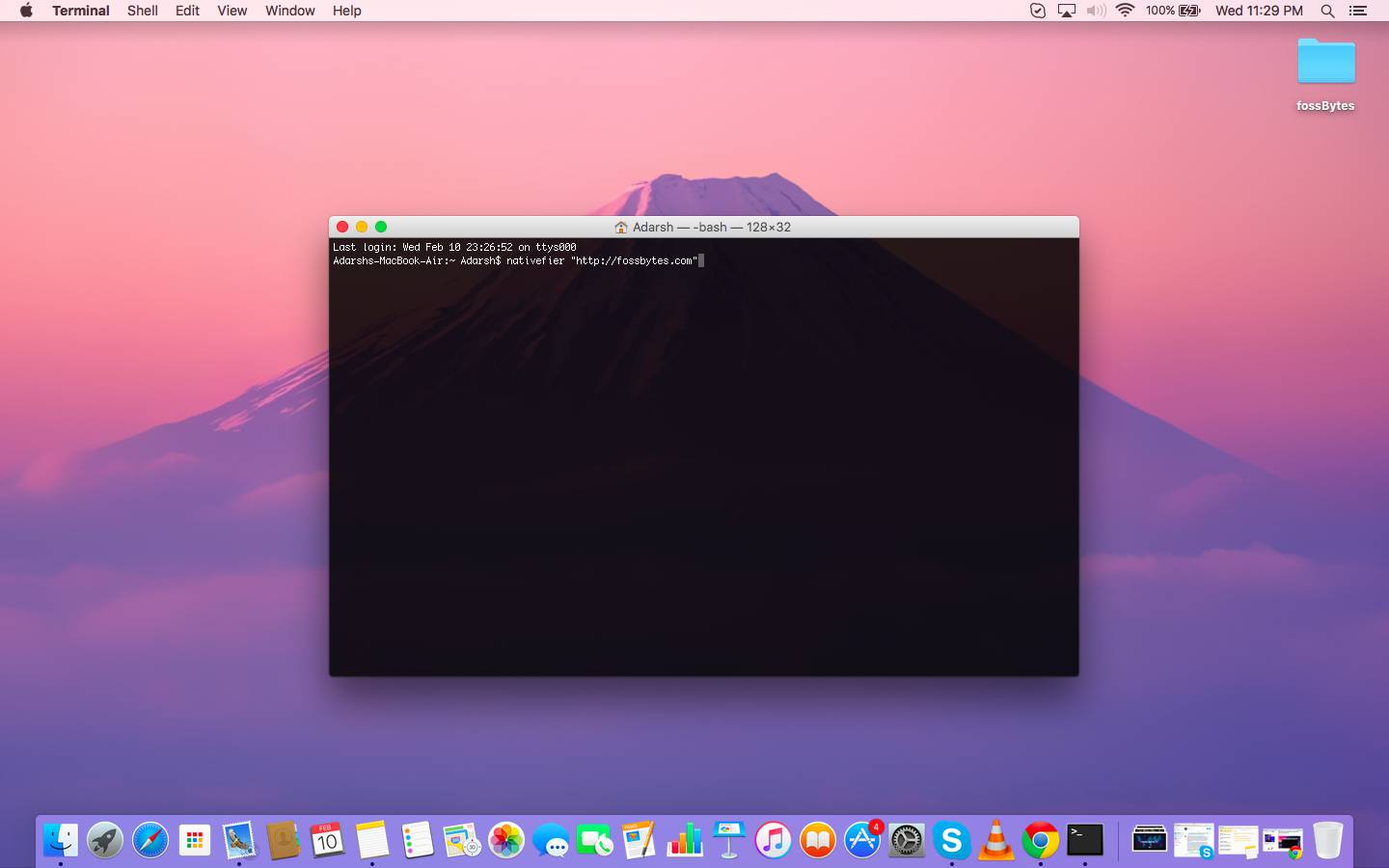
232GeekNativefier Instantly Converts Any Website Into a Desktop Program Using Command Line
Short Bytes: Nativefier is based on the Node.js runtime environment which can convert any web page into an automated desktop application. Nativefier does this...
-

 105Privacy
105PrivacyICS calls for latest Draft Investigatory Powers Bill to go further to protect privacy
The UK's Intelligence and Security Committee has deemed the latest Draft Investigatory Powers Bill as a “missed opportunity”, according to its latest...
-

 240News
240NewsAnonymous Wants Saudi Arabia Out from Olympics for Battering Human Rights
The Online Hacktivist Anonymous Demands Exclusion of Saudi Arabia from Olympics for Battering Human Rights Saudi Arabia has always been criticized by...
-

 174Vulnerabilities
174VulnerabilitiesRemote Code Execution: All Versions Of Windows Hit By ‘Severe’ Security Vulnerabilities
Short Bytes: As a part the latest Patch Tuesday, Microsoft released 13 security patches for all version of Windows and other software like...
-

 188Data Security
188Data SecurityHearthstone add-ons, cheating tools come with data-stealing malware
Attackers have disguised information-stealing and Bitcoin malware as third-party add-ons and cheats for Blizzard’s online card game. Hearthstone, a free-to-play card game...
-

 3.6KData Security
3.6KData SecurityHow to Hack the Power Grid Through Home Air Conditioners
TENERIFE, SPAIN—THERE ARE many ways we know of to cause a blackout. You could hack industrial equipment to spin a generator out...
-

 312Data Security
312Data SecurityVigilante Hackers Fight Lizard Squad For Control Of 150,000 Home Routers
Home routers with little to no security are far too common. They’re dangerous from a number of perspectives: as peeping holes for spying on people’s...
-
 113Malware
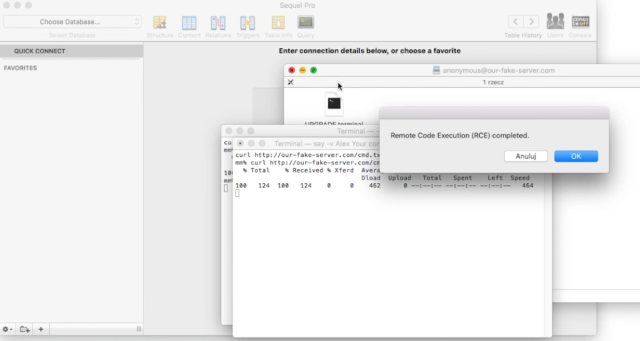
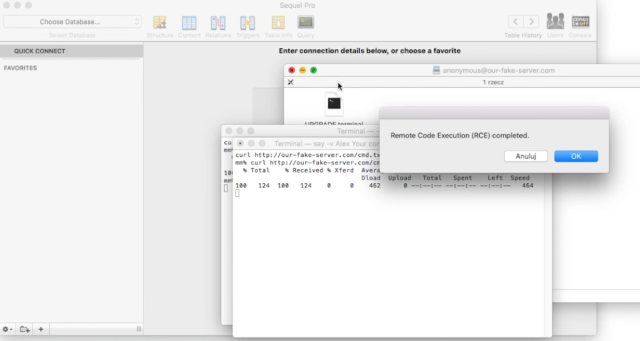
113MalwareRent the infamous AlienSpy backdoor is now quite easy
Security experts at Kaspersky have spotted in the wild a new variant of AlienSpy RAT Family openly offered with a model of...
-
 175Vulnerabilities
175Vulnerabilities“Huge” number of Mac apps vulnerable to hijacking, and a fix is elusive
Apps that use 3rd-party updater over insecure HTTP channels subject to MiTM attacks. Camtasia, uTorrent, and a large number of other Mac...
-

 163Data Security
163Data SecurityFacebook Hacking Tool Is Here To Hack Your Accounts, But Here’s A Catch
Short Bytes: Your desire to master the art of Facebook hacking can harm you in a big way. Recently, a variant of Remtasu...
-

 215Geek
215GeekFacebook’s Sneaky User Data Sharing Hammered by French Privacy Regulators
French privacy advocates tell Facebook to stop spying on its citizen within 3 month It’s a fact that European countries are not...
-
 247How To
247How ToHow To Get Pluralsight Courses For Free | 6 Months Subscription
Short Bytes: Pluralsight has one of the biggest collections of programming video courses. Here’s a simple way that tells you how to...
-

 199Hacked
199HackedCyber-Crime Barely Pays $30,000 A Year To A Black Hat Hacker
Short Bytes: In the war between good versus evil, ”Good’ makes more money than ‘Bad’ even if ‘Bad’ is good at finding the...
-

 168Cyber Events
168Cyber EventsNorth Korea Bears the Brunt of Satellite Launch- Becomes Target of Anonymous
A group of hackers famously known as New World Hackers (NWH) is claiming to attack a number of state websites in North...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




