Featured News
-

 280Data Security
280Data SecurityPassword Security — Who’s to Blame for Weak Passwords? Users, Really?
Password Security — Who’s to Blame for Weak Passwords? Users, Really? The vulnerability of people falling into the traps of online miscreants...
-

 137Scams
137ScamsThe security review: Remtasu and Facebook cheat sheet
From an outbreak of malicious spyware to the UK’s bill on investigatory powers, here’s our comprehensive breakdown of cybersecurity news from the...
-

 301Mobile Hacking
301Mobile HackingHow to obtain Blackberry engineering screen
Firstly, what is the advanced help screen? Basically, it’s a way to dive deeper into your OS and see what’s going on...
-

 323OSINT
323OSINTHow to trace an email address
Here is all the things that you need to trace an email address : Google Chrome (or a good and fast browser)...
-

 299Cyber Crime
299Cyber CrimeNetflix Users Targeted with Phishing and Malware Scams Stealing Credit Card Data
Malware in Netflix Apps Steals Credit Card details of Users— Symantec Researchers Netflix Apps delivering more than movies: Netflix has become excessively...
-
 216Data Security
216Data SecurityRussian Hackers Spying On Your Linux PC Using Sophisticated Malware “Fysbis”
Linux Backdoor Called Fysbis Used by Russian Hackers. A new malware family known as Fysbis (or Linux.BackDoor.Fysbis) is aiming Linux machines by setting...
-

 147Incidents
147IncidentsHackers Demand $3.6 Million From Hollywood Hospital Following Cyber-Attack
Hospital staff severely impeded in their day-to-day work. The Hollywood Presbyterian Medical Center, a 430+ beds hospital in the middle of Los Angeles,...
-

 167Data Security
167Data SecurityMan charged of Laundering $19.6 Million earned with PBX system hacking
Pakistani citizen Muhammad Sohail Qasmani admits laundering Millions from massive computer hacking and telecommunications fraud scheme. A Pakistani citizen, Muhammad Sohail Qasmani...
-
 320Geek
320GeekFacebook Secret Groups Favorite Platform for Paedophiles to Share Images
Facebook is known for its censorship but when it’s about deleting secret groups filled with Paedophiles the social media giant is slower than a...
-

 185How To
185How ToHow to Block Valentine’s Day from Facebook
You may have countless reasons to hate Valentine’s Day. Here, I won’t start discussing all of them because there are tons of...
-

 258Geek
258GeekLatest Android Malware with Rooting Abilities Can Wipe Your Data
If you think you have seen it all then you are wrong — Here comes a malware that will make your phone...
-

 167News
167NewsIranian Hackers Breached Computer of Ex-Israeli Army Chief-of-Staff
Computers of 1800 Key Personalities including Ex-Israeli Army Chief-of-Staff Penetrated by Iran-Sponsored Hacker Last year, some private pictures of IDF’s women soldiers were...
-

 171Geek
171GeekEasiest Way to Improve Your Phone’s Battery Life – Deleting Facebook App
Facebook app uses your smartphone battery more than any other app — It’s time to get rid of the app and use...
-

 552Courses & Ebooks
552Courses & EbooksCEH v9 – Certified Ethical Hacker v9 Course PDF + Tools DOWNLOAD
This is the worlds most advanced ethical hacking course with 18 of the most current security domains any ethical hacker will ever...
-
 181Data Security
181Data SecurityKaspersky Researcher Shows How He Hacked His Hospital While Sitting In His Car
Short Bytes: When we visit a hospital, we put our complete trust in our doctor and the medical equipment that he/she uses....
-
 196News
196NewsFBI Demands Removal of its Employees’ Leaked Data from the Internet
The United States Department of Homeland Security had its data leaked online — FBI is forcing websites to remove the data ASAP....
-
 159Malware
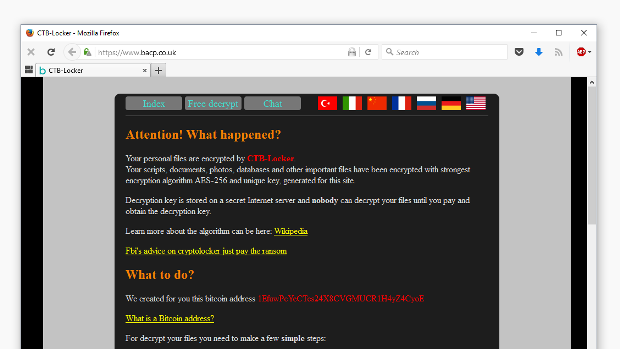
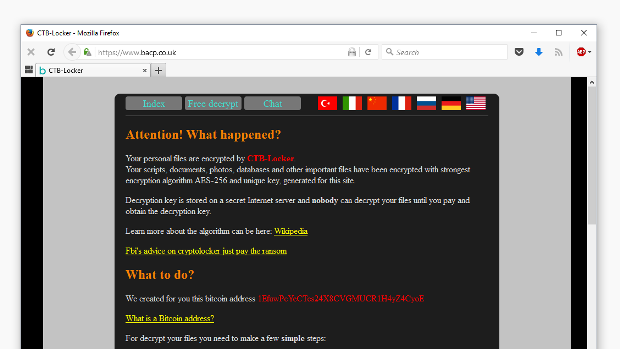
159MalwareFirst Time Ever: Ransomware Hits Website and Defaces Homepage
CTB-Locker ransomware spotted on a Linux machine. The website of the British Association for Counseling & Psychotherapy (bacp.co.uk) has been hit by...
-
 121Data Security
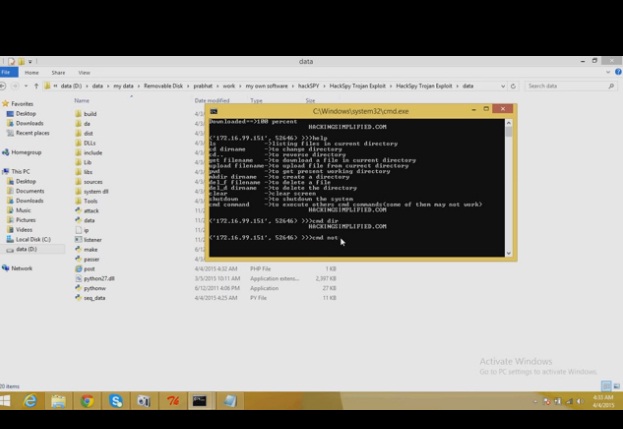
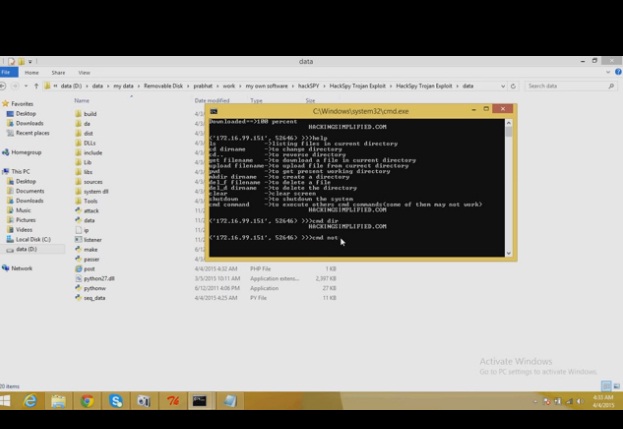
121Data SecurityHackSpy Trojan Exploit
HackSpy Trojan Exploit this tool make undetectable trojan virus….which can help you to spy on other computers…….. this version consists of a trojan...
-
 303Data Security
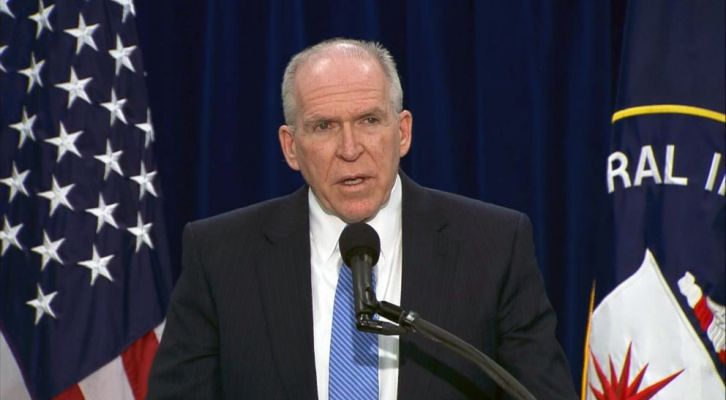
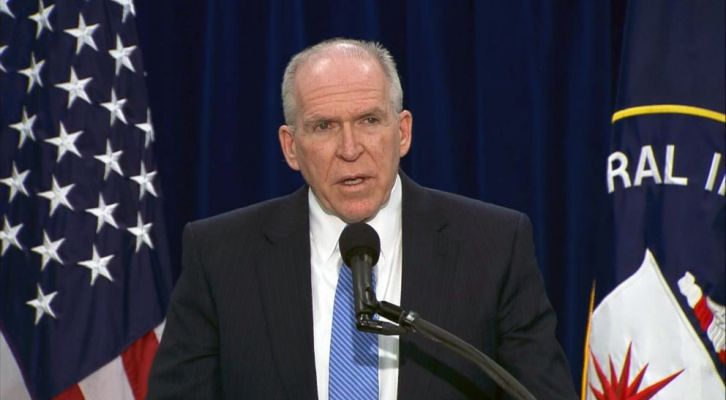
303Data SecurityUK police arrested teenage hacker who allegedly hacked CIA and FBI officials
UK Police and FBI have arrested a teenager suspected to be Cracka, the hacker who hacked the CIA Director John Brennan. The...
-

 89Malware
89MalwareHow malware moved the exchange rate in Russia
After an investigation period, details were published about a unique cyberattack on a Russian bank where a malware placed trade orders for...
The Latest
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications
-
 Malware
MalwareNSA, FBI Alert on N. Korean Hackers Spoofing Emails from Trusted Sources
-
 Vulnerabilities
VulnerabilitiesFour Critical Vulnerabilities Expose HPE Aruba Devices to RCE Attacks
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Vulnerabilities
VulnerabilitiesWhen is One Vulnerability Scanner Not Enough?
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Vulnerabilities
VulnerabilitiesNew “Goldoon” Botnet Targets D-Link Routers With Decade-Old Flaw
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareZLoader Malware Evolves with Anti-Analysis Trick from Zeus Banking Trojan
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024




