Featured News
-

 313Cyber Crime
313Cyber CrimeCrooks Sending Phishing Links in Text Messages To Steal PayPal Account
Text Messages are a Hacker’s Latest Weapon to Dole out PayPal Phishing Scams. The easiest way cybercriminals can try to hack your...
-

 235Geek
235Geek11 Skills And Programming Languages To Become A Professional Web Developer
Short Bytes: Apart from learning the basic skills like HTML and CSS, the road to becoming a successful web developer needs some...
-
 344Malware
344MalwareAndroid has some critical remotely‑exploitable security holes. But can you get the patch?
Remote code execution vulnerabilities have been found in the Android operating system, and patches released for Nexus devices. But what about your...
-

 151Malware
151MalwareEmail from your photocopier? It could be a malware attack
Twenty years ago, the first Word macro malware spread across the planet. Embedded inside a Word document, and rather unhelpfully given a...
-

 147Data Security
147Data SecurityMicrosoft makes Windows 10 a ‘recommended update’ for Windows 7 and 8.1 users
Microsoft has been accused of pushing Windows 10 rather aggressively, and the company’s latest move is going to do nothing to silence...
-

 184Incidents
184IncidentsNASA hacked by AnonSec that hijacked a $222m Global Hawk drone
Anonsec group hacked NASA network and released a data dump of data online. The hackers also hijacked a Global Hawk drone. Hackers belonging...
-

 164Data Security
164Data SecurityCorrupt Silk Road Investigator Re-Arrested for Allegedly Trying to Flee the US
JUST WHEN THE Silk Road’s saga of dirty money and double-dealing seemed to be winding down, one of the federal agents who...
-

 270Data Security
270Data SecurityAudit shows Department of Homeland Security 6 billion U.S. Dollar firewall not so effective against hackers
A multi-billion U.S. Dollar firewall run by the Department of Homeland Security meant to detect and prevent nation-state hacks against the government...
-

 294Data Security
294Data SecurityYour HP Printer’s Hard Drive Can Be Used by Hackers To Host Malicious Files
Security researcher Chris Vickery has discovered that hackers can abuse HP LaserJet Printers and host malicious files on their hard drive. The famous...
-

 147News
147NewsTOR Traffic Data leak Caused by Misconfigured Apache Servers
An unmodified default setting in Apache Web Servers revealed crucial details related to TOR traffic that passed through that server. It is...
-

 281How To
281How ToHow To Find Out Who Has Ignored Your Facebook Friend Request
Short Bytes: It’s very easy to find out who has ignored your friend request on the largest social networking site Facebook. You can...
-

 77Data Security
77Data SecurityJSPatch hot patching technique puts iOS users at risk
Security experts at FireEye are warning attackers can exploit the JSPatch hot patching technique to serve malicious code and put iOS users...
-
 187Geek
187GeekRunning ‘rm -rf –no-preserve-root /’ Command In Linux Can Kill Some Laptops Permanently
Image: Arch Linux Short Bytes: The mere thought of permanently damaging your laptop is daunting. But, what if you are trying to...
-
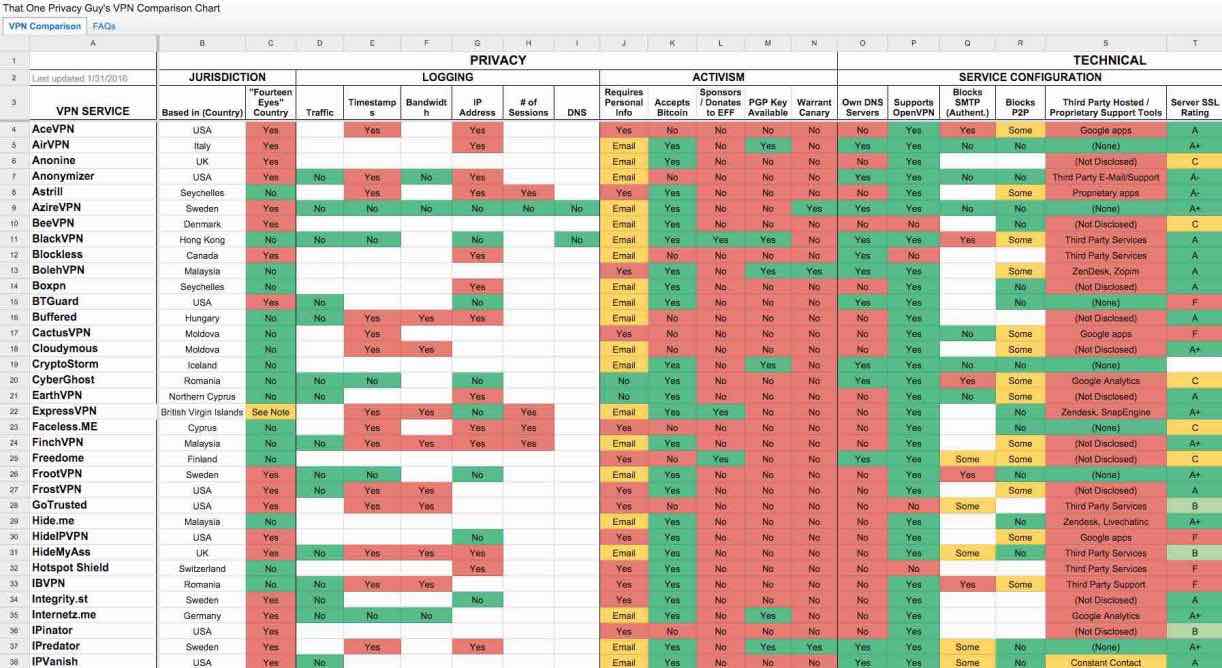
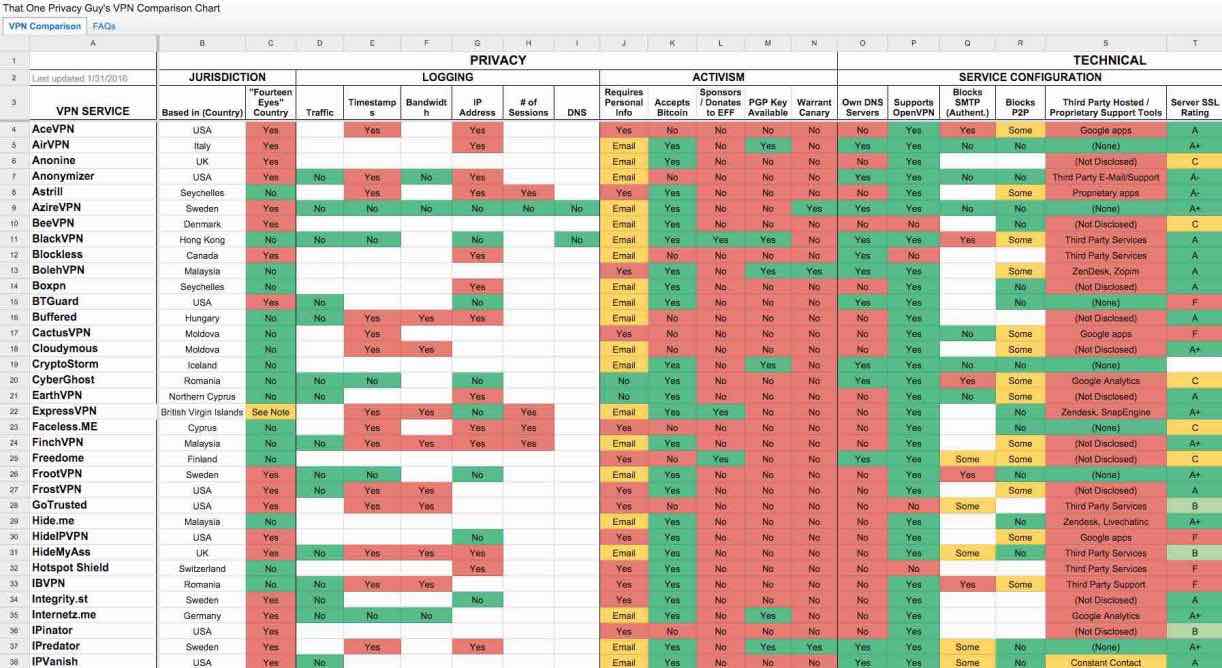 223Lists
223ListsThe Ultimate VPN Comparison Chart Featuring More Than 100 VPN Services
Short Bytes: Selecting the right VPN service to fulfill your needs is a monumental task. Keeping in mind the same, a Reddit...
-

 172Data Security
172Data SecurityAre Hackers Keeping a Hidden Stash on Your HP Printer’s Hard Drive?
Unprotected HP printer HDDs can be abused if not protected. Security researcher Chris Vickery has discovered that HP LaserJet printers may be abused...
-

 275Data Security
275Data SecuritySnowden Leak Proves That NSA And GCHQ Spied On Israeli Drones Using Open Source Tools
Short Bytes: According to the latest documents provided by Edward Snowden to The Intercept, NSA and GCHQ were involved in surveillance activities...
-

 165Vulnerabilities
165VulnerabilitiesThere’s a lot of vulnerable OS X applications out there.
Lately, I was doing research connected with different updating strategies, and I tested a few applications working under Mac OS X. This...
-
 109Incidents
109IncidentsDefault settings on Apache Web servers can reveal details about Tor traffic
Default Settings In Apache Servers Can Leak Details about Tor traffic. This has happened the second time in this week. Leaving default setting...
-

 362News
362NewsThis is how hacked Israeli drone feeds look like
To date, it has always been reported that drones can potentially be hacked and a few cases where they, in fact, had...
-
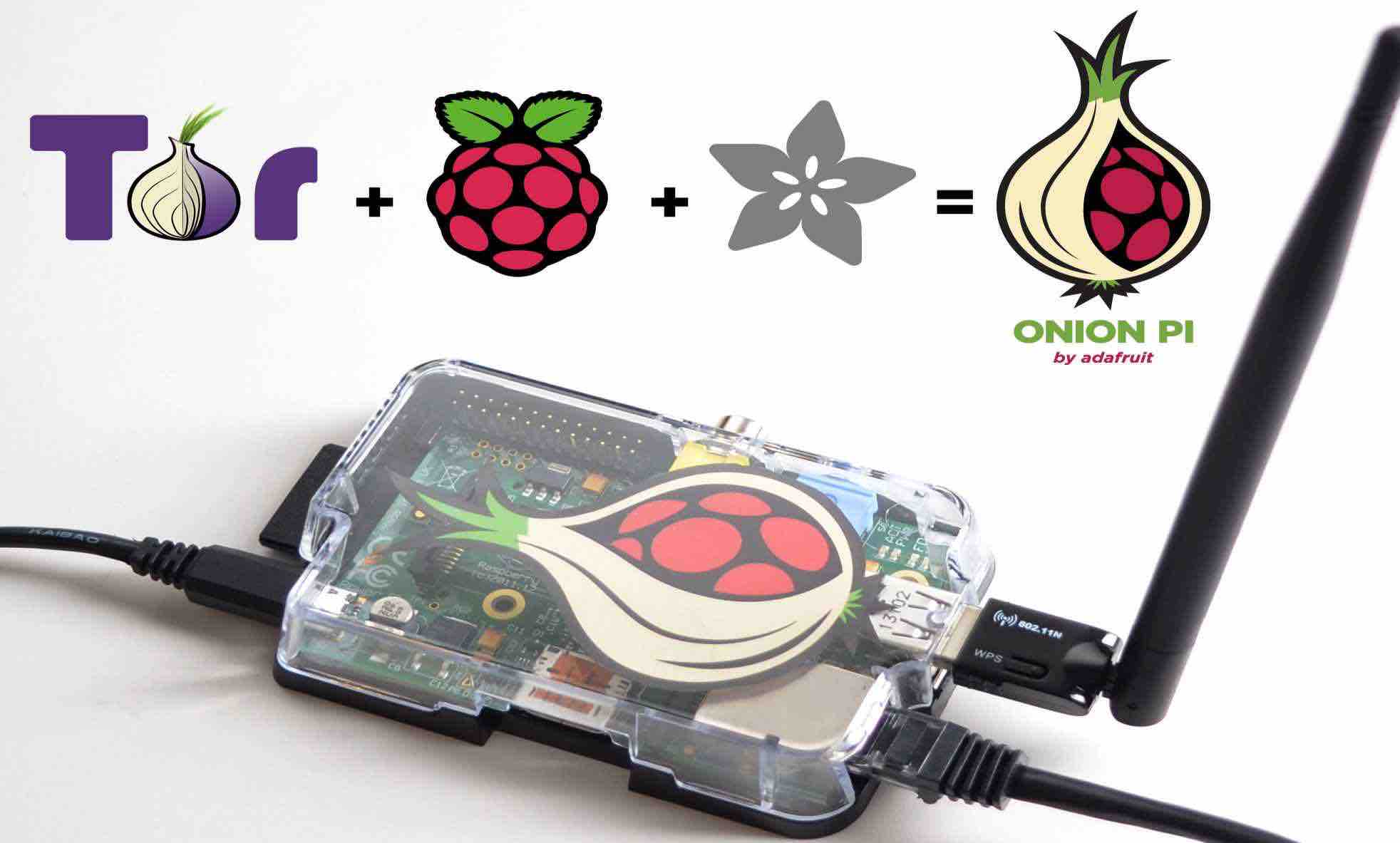
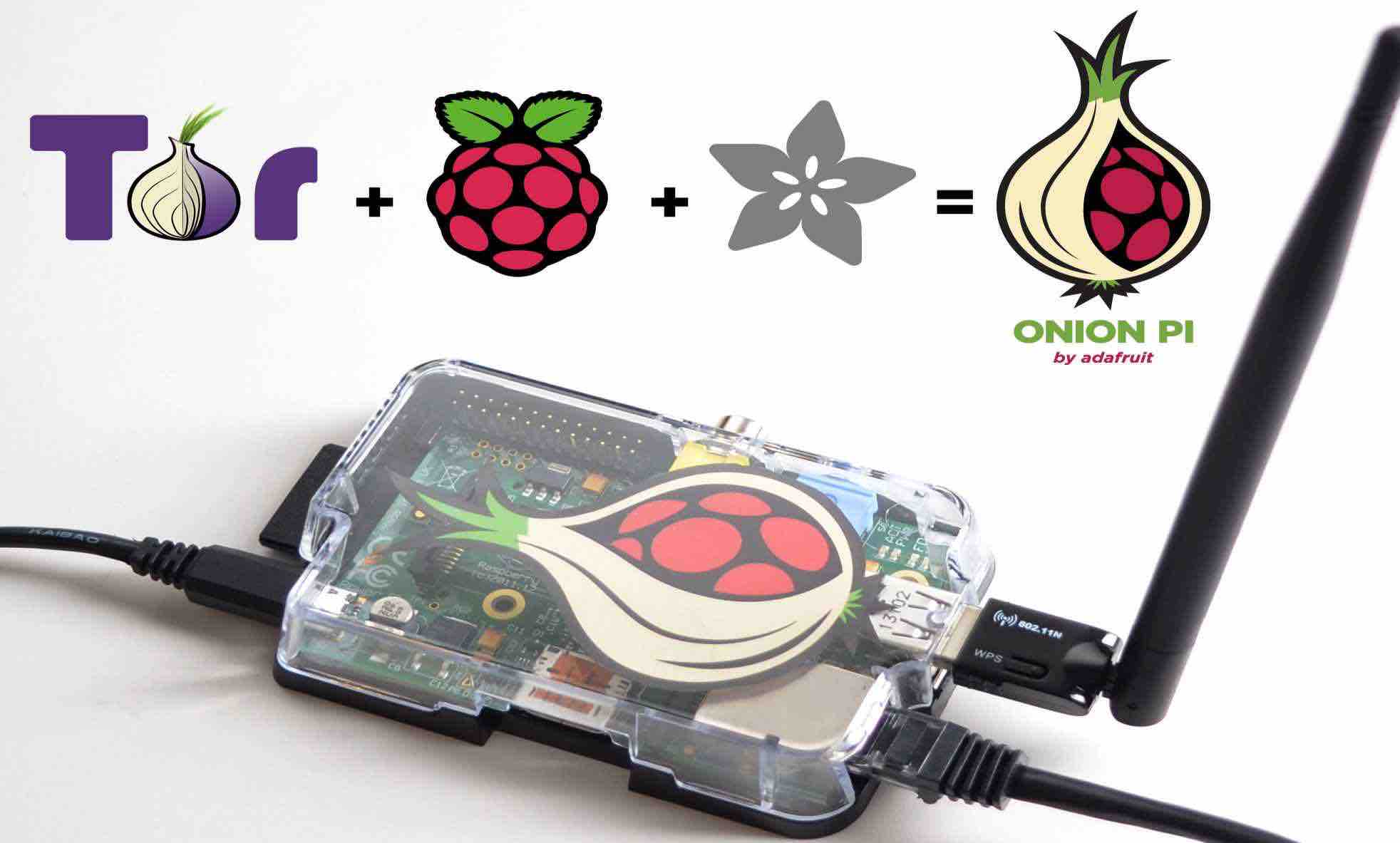 430How To
430How ToHow To Make Your Own TOR Proxy Router With A Raspberry Pi
Short Bytes: By investing some time and money, now you can make a portable Raspberry Pi TOR proxy router. Using this device, you...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




