Featured News
-

 196Data Security
196Data SecurityRemotely Disabling a Wireless Burglar Alarm
Countless movies feature hackers remotely turning off security systems in order to infiltrate buildings without being noticed. But how realistic are these...
-

 130Cyber Crime
130Cyber CrimeHow the threat experts see it …
A unique survey among threat experts has revealed that most cyberattacks against a typical IT infrastructure take less than 24 hours to...
-

 113Incidents
113IncidentsWordPress Sites Leveraged in Layer 7 DDoS Campaigns
We first disclosed that the WordPress pingback method was being misused to perform massive layer 7 Distributed Denial of Service (DDoS) attacks back in...
-

 305Hacked
305HackedAnonymous Hacker Arrested By The FBI In Hospital Computer Hacking Case
Short Bytes: Martin Gottesfeld, the alleged Anonymous hacker responsible for 2014’s hacking attack at Boston Children’s Hospital, has been arrested by the FBI....
-

 167Vulnerabilities
167VulnerabilitiesMillions of AirDroid Users Exposed to Severe Vulnerability
A new vulnerability in the AirDroid App was revealed by Check Point. This vulnerability affects the 50 million AirDroid users around the...
-
 290Hacked
290HackedThe Most Important Fight For Data Security: Why Apple Must Win Against FBI?
ShortBytes: In response to the Federal court order which was issued to Apple, the maker of iPhone, to help the FBI hack...
-

 106Malware
106MalwareWhy Tim Cook is right to call court-ordered iPhone hack a “backdoor”
Custom version of iOS could undo years of work Apple put into securing iPhones. Tuesday’s court order compelling Apple to hack the iPhone...
-

 347Geek
347GeekApple defiant in San Bernardino Shooting Case; says no to backdoor access
Judge Issues Order to Apple to Unlock iPhone Vital in the San Bernardino Shooting Case — Apple refuses to follow orders The...
-

 122Data Security
122Data SecuritySouthampton University Creates 5D Storage Disc That Can Store 360TB Data
The mindblowing invention will revolutionise the way we store data Last year the researchers came up with a processor capable of transmitting...
-

 177How To
177How ToHow To Access Your Chrome Passwords Remotely From Any Browser?
Short Bytes: Google has introduced a new online feature where a user can sync its passwords to Google and access Chrome passwords...
-

 319Cyber Crime
319Cyber CrimeCybercriminals Hack Hospital PCs Demand Whopping 9000 BTC Ransom
Ransomware Infects Hollywood HealthCare Facility Computers – Attackers Demand $3.6M Computers are an integral part of almost every field and industry nowadays...
-

 274Data Security
274Data SecurityThe NSA’s SKYNET program may be killing thousands of innocent people
“Ridiculously optimistic” machine learning algorithm is “completely bullshit,” says expert. In 2014, the former director of both the CIA and NSA proclaimed that...
-

 235Vulnerabilities
235VulnerabilitiesHow to bypass this LG smartphone’s fingerprint security in just 30 seconds
A troubling vulnerability has been uncovered that may make you think twice about ever even temporarily allowing a friend, partner or acquaintance...
-

 185Malware
185MalwareDridex: Financial Trojan aggressively spread in millions of spam emails each day
Built to harvest the banking credentials of victims, the virulent Dridex is now one of the most dangerous pieces of financial malware...
-
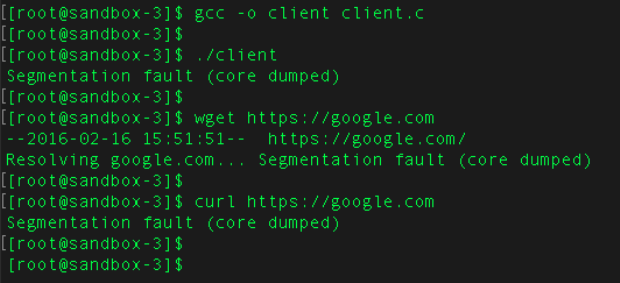
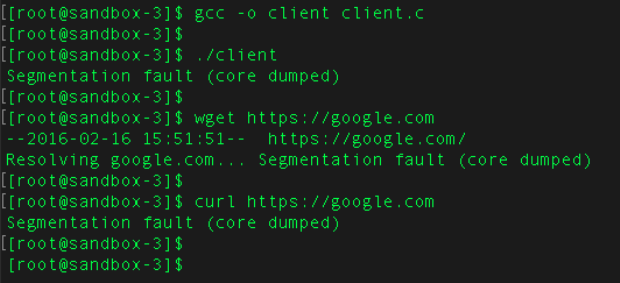 148Vulnerabilities
148VulnerabilitiesExtremely severe bug leaves dizzying number of software and devices vulnerable
Since 2008, vulnerability has left apps and hardware open to remote hijacking. Researchers have discovered a potentially catastrophic flaw in one of the...
-

 103Malware
103MalwareBackdoor in MVPower DVR Firmware Sends CCTV Stills to an Email Address in China
IoT security experts from Pen Test Partners have confirmed the presence of a backdoor in the firmware used by some DVR devices...
-

 411Lists
411Lists10 Best Free VPN Services Of 2016: Which One Shall I Choose?
Short Bytes: Due to restrictions and localization of different internet services and sites like YouTube, Netflix, live sports etc., internet users like...
-
 228Data Security
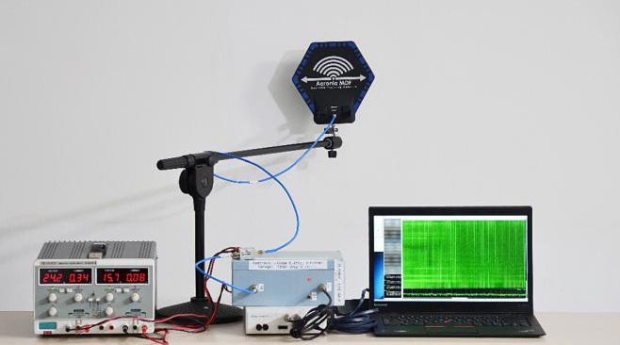
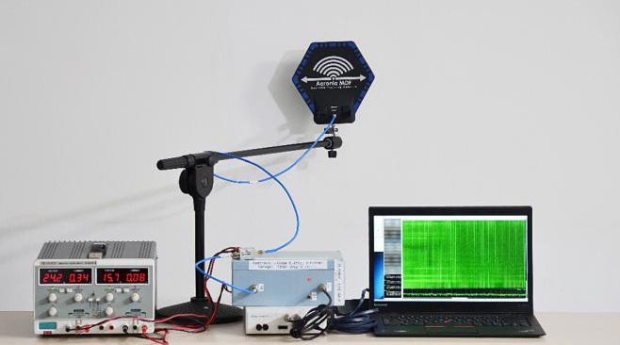
228Data SecurityHow White Hat Hackers Stole Crypto Keys from an Offline Laptop in Another Room
Last year, it was revealed that hackers can steal data from any computer via heat and how some technologies can hack into...
-

 266News
266NewsAnonymous’ #OpAfrica Claims 64,000 Workers Data of Tanzanian Telecom Firm
The online hacktivist Anonymous has breached into the server of a Tanzanian Telecom Firm and leaked personal data of about 64,000 employees. OpAfrica is...
-

 193News
193NewsHackers To Demonstrate How To Hack An Offline Laptop
White Hat Hackers show us how to Steal Crypto Keys from a Laptop in Another Room Sans Internet Connection Last year, it...
The Latest
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment
-
 Data Security
Data SecurityHow Safe is Your TinyProxy? Step-by-Step Guide to Exploiting Tinyproxy’s Zero Day Vulnerability
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications




