Featured News
-

 275Cyber Events
275Cyber EventsMost Americans Want Apple to Cooperate with the FBI- Claims Pew Survey
The survey shows Americans are actually supporting FBI on the iPhone encryption issue. We all know about the heated debate going on...
-

 413Geek
413GeekWhat Is Programming And Why You Should Learn To Code?
Short Bytes: With the advent of new online opportunities, learning how to code is easier than ever. Read more to know why...
-

 174Data Security
174Data SecurityNSA Data Center Experiences Up to 300 Million Cyber-Attacks per Day
Six years ago, the cyber-attacks barely reached 25,000. Utah officials are saying that the number of cyber-attacks they’ve seen against local state organizations...
-
 183Android Hacking
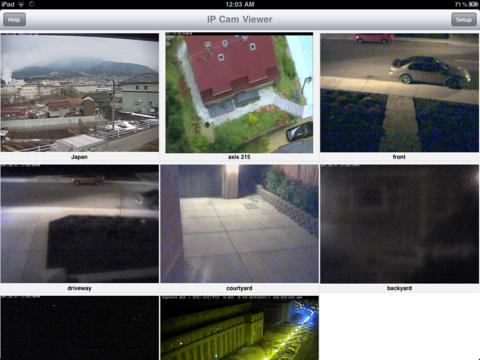
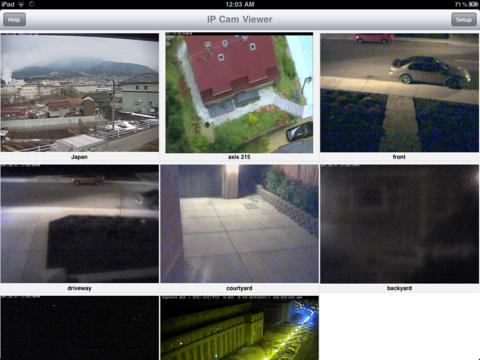
183Android HackingTurn old Smart Phone to Security Camera
If you have a lot of old smart phones at home, but don’t know what to do with them? Well here’s a...
-
Malware
Android porn clicker on Google Play: Appendix
Trojan clicker servers Google Play information Package names of trojan clickers found on the infected servers
-

 238Kids Online
238Kids OnlineDigital childhoods: How different nations bring up their kids
ESET has looked deeper into what parents in the United States, Germany, the United Kingdom and Russia regard as the appropriate age...
-

 461Kids Online
461Kids Online4 internet‑savvy countries agree: Kids go digital too early
Online surveys by ESET show that a majority of parents in Russia, the United Kingdom, Germany and the United States are not...
-
 58Data Security
58Data SecurityRussian bank employees received fake job offers in targeted email attack
Employees at six Russian banks were sent spoofed emails delivering Trojan.Ratopak in a narrow, targeted attack. In December 2015, employees from several...
-
 291Hacked
291HackedBill Gates Says Apple Should Unlock Shooter’s iPhone For FBI
Short Bytes: The big names of American tech industry have expressed their support for Apple in its fight against the government’s demand...
-

 93Incidents
93IncidentsHTTP GZIP Leaks Data on the General Location of Tor Websites
Some Tor servers may leak timezone info via gzipped files. Jose Carlos Norte, developer for the eyeOS virtual desktop project, has discovered an...
-
 96Malware
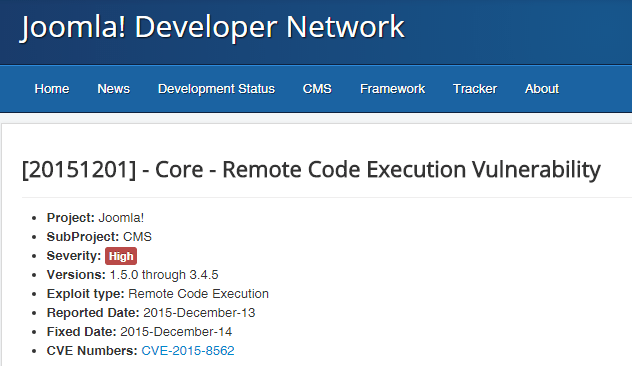
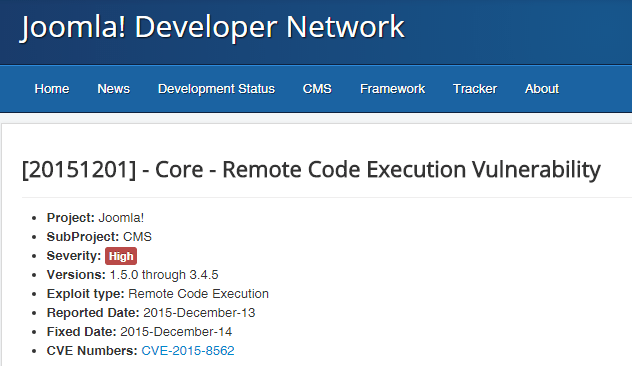
96MalwareAdmedia attacks now rely also on Joomla to serve ransomware
Operators running websites based on the WordPress and Joomla must be aware of a spike in the number of compromised platforms used...
-

 321News
321NewsAnonymous Leaks Data of Cincinnati Police Department Officers
The Anon Verdict hacktivists from Anonymous leaked personal information of around 52 Cincinnati Police Department employees on Sunday — Motive: Death of...
-

 254News
254NewsHackers Compromise the Download Link for Linux Mint with Backdoor
Hackers Compromise the Download Link for Linux Mint Deemed to be a “modern, elegant and comfortable operating system which is both powerful and easy to...
-
 103Data Security
103Data SecurityHack This: Scripting Deeper, Better Hacks in Python
Part of the point in presenting small, hack-minded tutorials a la “Edit an Image in Python” or “Send an Email from Python”...
-

 298Incidents
298IncidentsAnonymous took down several government websites of Saudi Arabia
Anonymous launched a series of cyber attacks against government websites of Saudi Arabia to protest the execution of 47 people, including Mr....
-

 292Data Security
292Data SecurityGPS hacking (PART 1)
GPS hacking has alway been a hot topic on security conferences over the past few years. But the contents are over academic...
-

 108Incidents
108IncidentsNSA Data Center effect : This state experiences 300,000,000 hacking attacks a day
Utah state computer systems experiences 300 million hacking attacks a day due to NSA data center in the state. 300,00,000 hacking attempts in...
-
 94Data Security
94Data SecurityLinux Mint was hacked, website served malicious ISO on Saturday
The Linux Mint website had been hacked, on Saturday, intruders were able to compromise it and serve malicious ISO of Linux Mint...
-
 278Cyber Crime
278Cyber CrimePublic Concerns for Zika Virus Exploited by Scammers to Spread Malware
Using a Public Health Emergency for Malicious Purposes — There’s nothing lower Cybercriminals are nothing but a bunch of lowlives who will...
-

 261Android Hacking
261Android HackingZanti – Android App for Hackers
zANTI is a penetration testing toolkit developed by Zimperium Mobile Security for cyber security professionals. Basically, it allows you to simulate malicious...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




