Featured News
-
 177Geek
177GeekLakka Is A Linux OS That Converts Any Computer Into A Gaming Console
Short Bytes: Lakka is a lightweight Linux distribution for converting any computer into a full-fledged retro gaming console. Based on OpenELEC and...
-
 182Geek
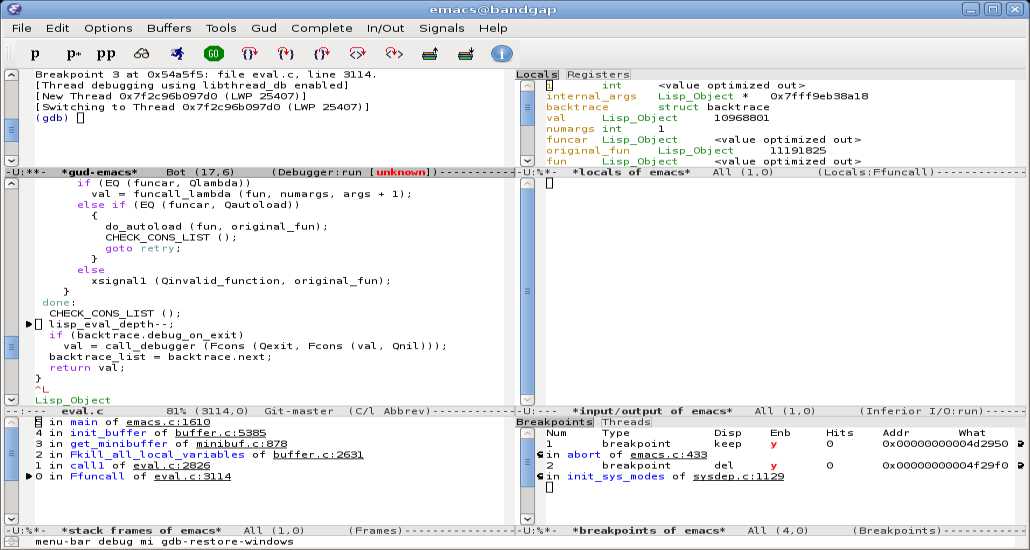
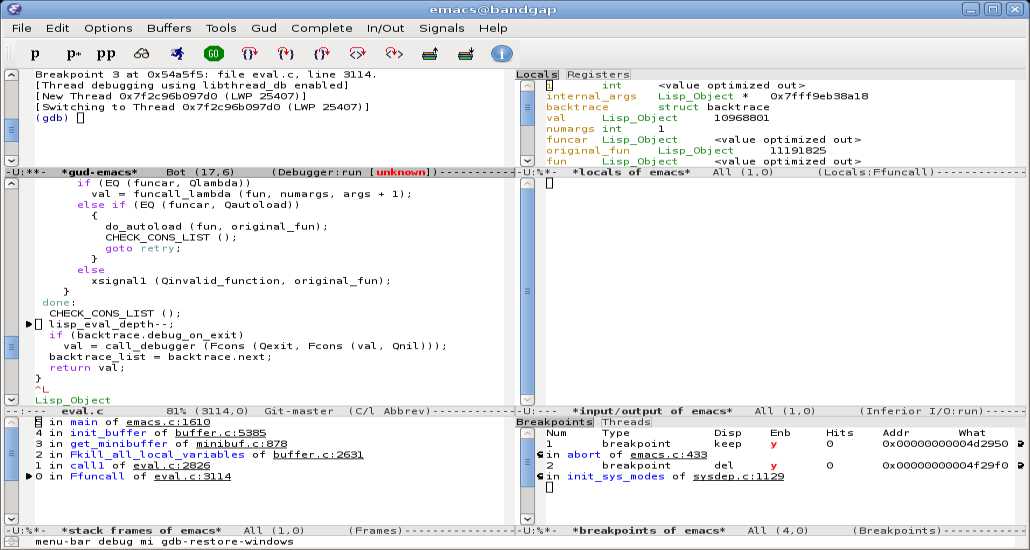
182GeekGNU Emacs Tutorial: How To Edit A File (Cheat Sheet Included)
Short Bytes: Do you want to learn the basics of Emacs text editor? Well, here is a basic tutorial for you to get...
-

 192Hacked
192HackedThis New Crashsafari.com Bug Can Crash Anyone’s Smartphone And Computer
Image | Apple Short Bytes: After the mischievous 16-character Google Chrome bug, it’s time to bear the nonsense of crashsafari.com bug. This...
-

 339Geek
339GeekAvoid Clicking CrashSafari.com! It Crashes Android, iOS Devices + Web Browsers
Some trolls have been using short URLs to trick users into clicking the link CrashSafari.com that crashes and reboots Android, iOS devices and web...
-

 234News
234NewsHacker Claims Breaching FBI Server, Exposes Details of 80 Miami Police Officers
A hacker linked with the ”Cracka with Attitude” group claims to hack FBI’s service and steal personal information of over 80 Miami Police...
-

 263Lists
263Lists41 Toughest Google Job Interview Questions
Short Bytes: What are the toughest questions asked at Google’s job interviews? To give you an idea about how things proceed during...
-
 195Geek
195GeekSkype Issues New Update to Hide IP addresses Automatically
Skype finds cure to Online Harassment- Releases new Update to Hide IP addresses automatically In 2015, we reported that scammers/predators are tricking...
-

 345News
345NewsThe Anonymous Group: What is it and How big is it
Research proved that Anonymous hacktivists group is relatively much bigger than you anticipated and become quite popular among people all over the world but...
-

 132Data Security
132Data SecuritySimple Yet Efficient Linux Backdoor Trojan Discovered
Linux. BackDoor.Xunpes trojan lets cyber-crooks take control and execute commands on your Linux machine. Threats to Linux computers are now appearing on a...
-

 327Incidents
327IncidentsOpKillingBay – Anonymous shut down Japanese airport site to protest against slaughter of Dolphin
OpKillingBay – A group of hackers linked to the Anonymous collective shut down the Japanese Airport Website to protest against the slaughter of Dolphin....
-
 248Data Security
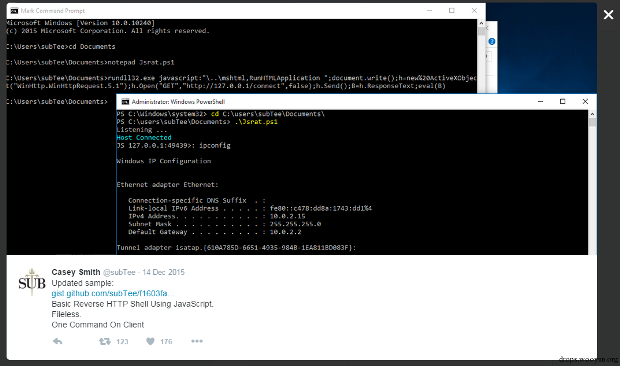
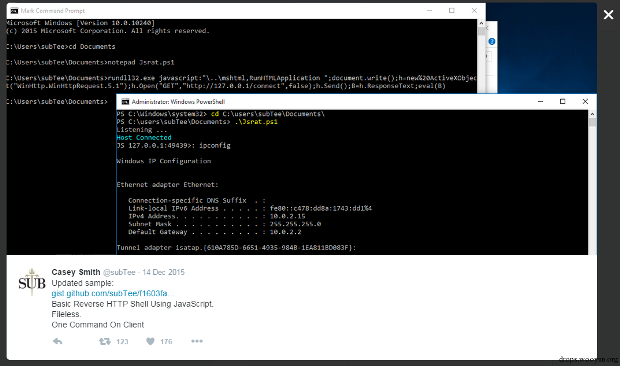
248Data SecurityJavaScript Backdoor
Casey Smith recently shared his research on twitter, which is to reverse HTTP Shell by using JavaScript. I found it rather interesting...
-
 2.6KGeek
2.6KGeek10 Most Common Mistakes Every Beginner Java Programmer Makes
Short Bytes: According to you, which is the most common mistake every beginner makes while coding in Java programming language? Well, there...
-
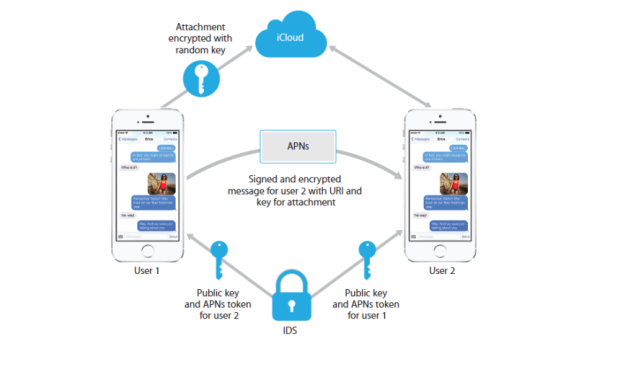
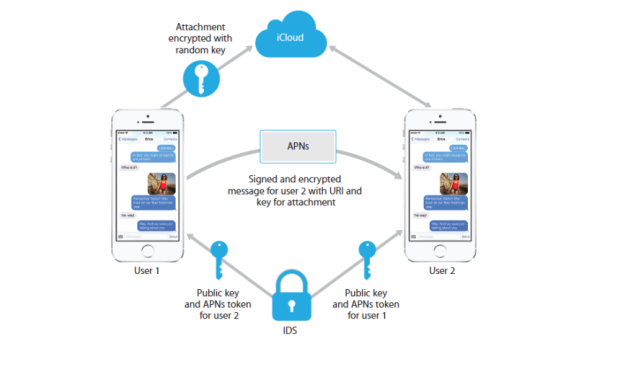 105Incidents
105IncidentsApple Can Still See Your iMessages If You Enable iCloud
Apple has taken a strong stance on privacy ever since the FBI began loudly demanding encryption backdoors into its products. The company’s...
-
 207Hacked
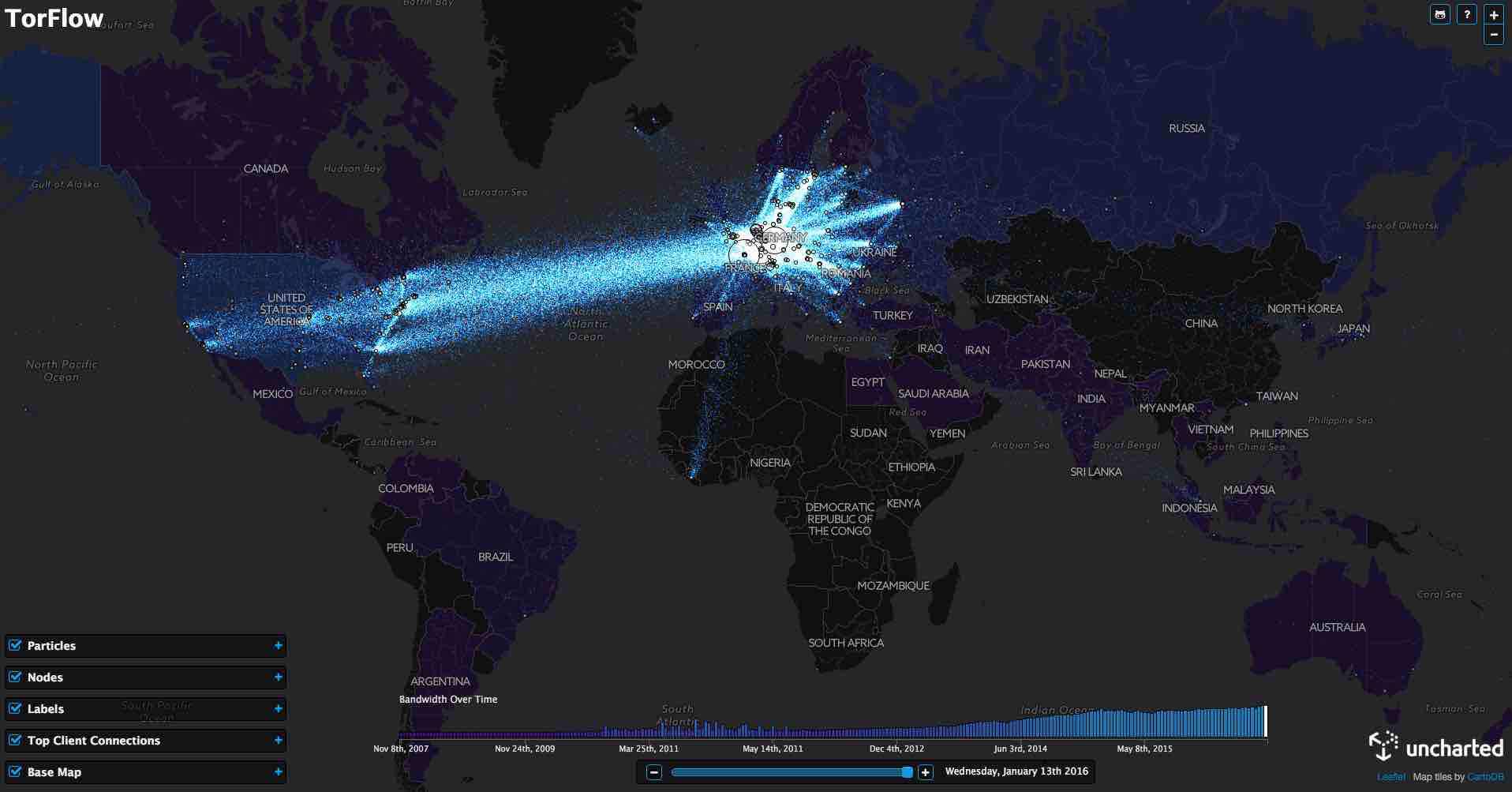
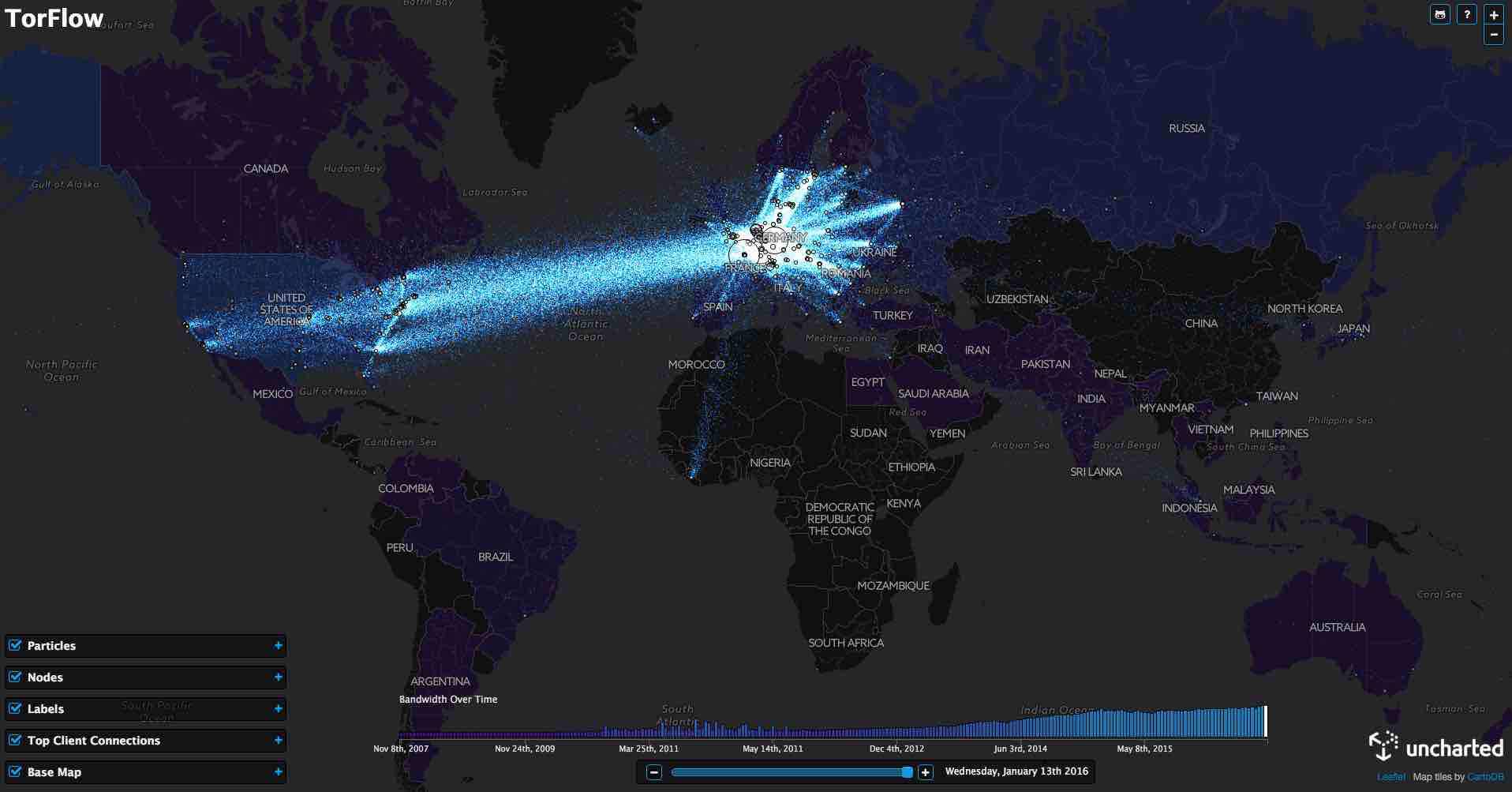
207HackedThis TorFlow Map Shows How TOR’s Data Looks As It Flows All Around The World
Short Bytes: Using the publicly available data, data visualization software firm Uncharted has prepared TorFlow — a map for visualizing how TOR’s...
-

 226Incidents
226IncidentsEDA2 Open-Source Ransomware Code Used in Real-Life Attacks
Another educational open-source ransomware project goes bad. Cyber-crooks have used the open-source code of the EDA2 ransomware to create the Magic ransomware...
-

 196News
196NewsAnonymous Shut Down Japanese Airport Website Against Dolphin Slaughter
Anonymous hackers shut down Japan’s Narita International Airport website against Dolphin slaughter. The online hacktivist Anonymous conducted a powerful DDoS attack on the...
-

 71Cyber Crime
71Cyber CrimeSkype finally hides your IP address, to protect against vengeful gamers
For too long streaming video gamers have suffered denial-of-service attacks and raids from police SWAT teams, often assisted by Skype leaking private...
-

 117Cyber Crime
117Cyber CrimeFBI Randomly Used Malware on TORMail Users While Busting Pedophiles
Report Hints on Possible Invading of TORMail users Privacy for Capturing Global Child Porn Gang by the FBI In 2013, the Federal...
-
 184Hacked
184HackedJohn McAfee: “Obama Administration Doesn’t Know The Meaning Of Privacy”
Short Bytes: The maker of McAfee antivirus and privacy advocate John McAfee is again in the headlines. In his latest op-ed, he stresses...
-

 440Social Media Hacking
440Social Media Hacking5 Tools to protect your Social Media accounts
You should have these five tools to protect your Facebook, Twitter, LinkedIn and other social media accounts Social media has taken the...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




