Featured News
-

 267Data Security
267Data SecurityFBI May Have Hacked Innocent TorMail Users
Back in 2013, the FBI seized TorMail, one of the most popular dark web email services, and shortly after started to rifle...
-
 159Incidents
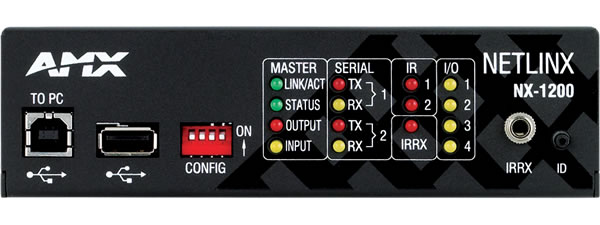
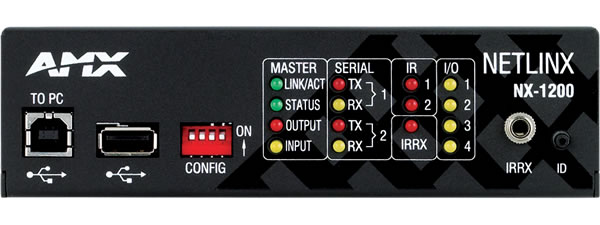
159IncidentsMedia devices sold to feds have hidden backdoor with sniffing functions
Highly privileged account could be used to hack customers’ networks, researchers warn. A company that supplies audio-visual and building control equipment to...
-

 188Data Security
188Data SecurityBritish Government Has Already Created a Data Encryption Protocol Complete With a Backdoor
GCHQ insists on shooting itself in the foot with backdoored VoIP encryption protocol, developed in-house by CESG. Britain’s intelligence agency, GCHQ (Government...
-

 298News
298NewsMore US Voters Data Circulating On The Dark Net
A country who has been spying on every computer in the world can’t protect voter data of its own citizens. Recent chronicles...
-

 282Data Security
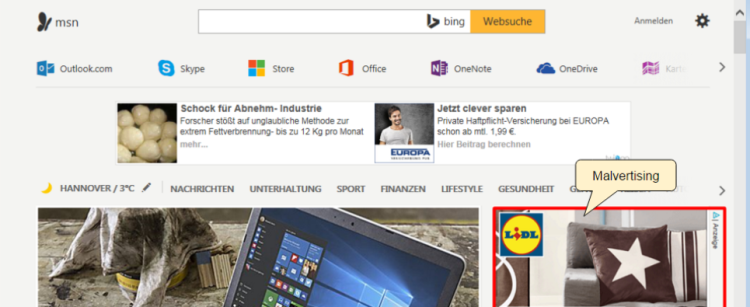
282Data SecurityAlert Users: MSN Main Page Dropping Malware on User PCs
If you visit MSN.com there is a chance your PC has been affected with a malware — Outlook users should also check...
-
 281Geek
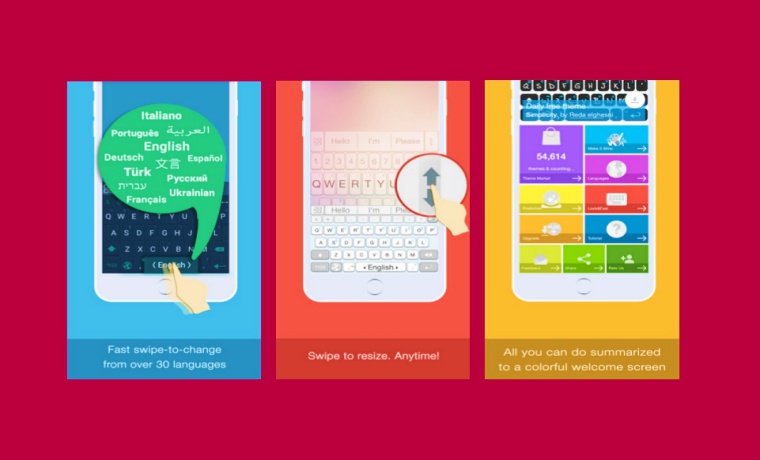
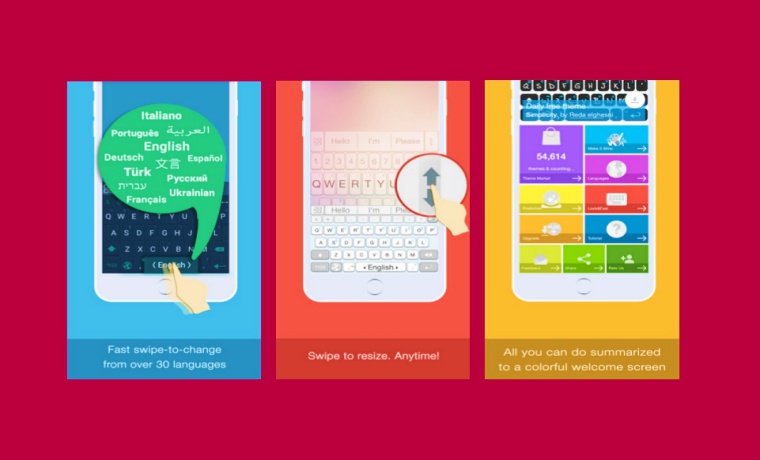
281GeekAI.Type Keyboard Bug on iOS Opens All Premium Features For FREE
Exclusive: An Apple fan has found a bug in AI.Type Keyboard on iOS allowing anyone to open All Premium Features For FREE Apple’s App...
-
 365How To
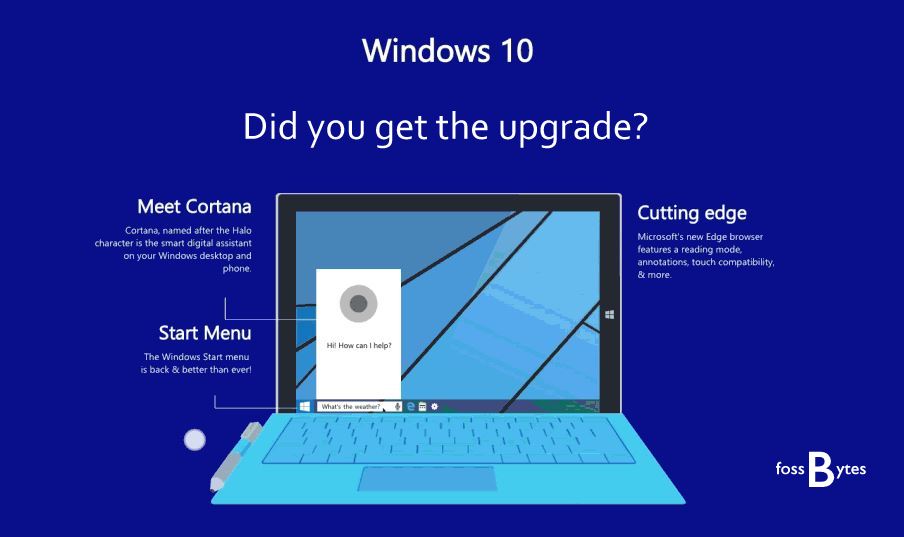
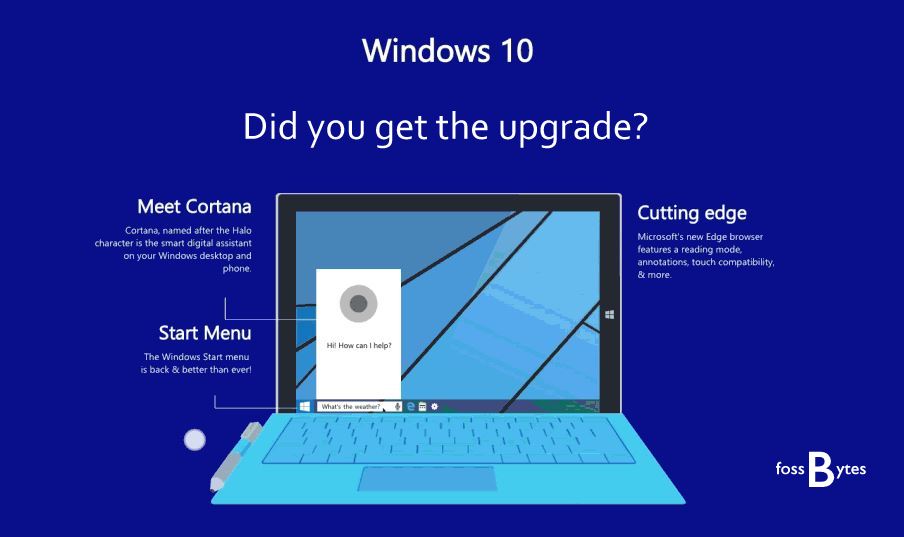
365How ToHow To Remove Pre-installed And Suggested Apps In Windows 10
Short Bytes: Though Windows 10 comes with free updates but along with that, comes a lot of unwanted pre-installed and suggested apps in Windows...
-

 182News
182NewsPsycho Voyeur Hacked Baby Monitor to Scare Toddler with Spooky Sounds
A cybercriminal was heard scaring baby by hacking into the nanny cam — “Wake up little boy, daddy’s looking for you.” “Look someone’s...
-
 83Malware
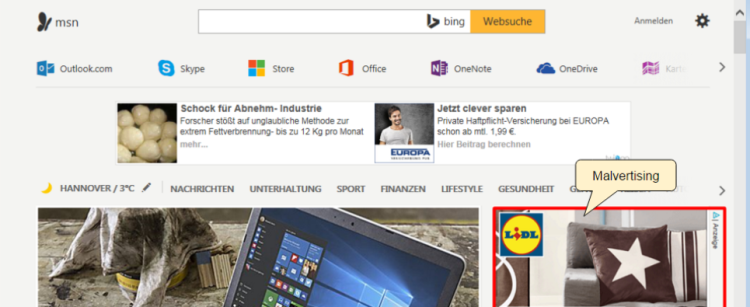
83MalwareMSN Home Page Drops More Malware Via Malvertising
Malvertisers are once again abusing ad technology platform AdSpirit and exposing visitors of the MSN homepage to malware. These attacks appeared to...
-

 175Geek
175GeekWhy Is Linux Foundation’s Latest Change A Bad News For Linux And Open Source?
Short Bytes: Up until recently, the Linux Foundation allowed the individual members to elect two board members and ensure that the voice...
-

 194Data Security
194Data SecurityTeslaCrypt Decrypted: Flaw in TeslaCrypt allows Victim’s to Recover their Files
For a little over a month, researchers and previous victims have been quietly helping TeslaCrypt victims get their files back using a flaw in...
-

 185Vulnerabilities
185VulnerabilitiesIntel Fixes Security Bug to Prevent Attackers From Hijacking the Driver Update Process
Intel-powered laptops are safe again. So are desktops. Intel has released version 2.4 of the Intel Driver Update Utility, fixing a critical...
-

 246News
246NewsTurk Hack Team Conducting DDoS Attacks on Iran and Russian Websites
Turk Hack Team conducted several cyber attacks on top Iranian and Russian Ministry websites since the beginning of the conflict at the...
-

 294News
294News10 Most Notorious Hacking Groups
Here are top 10 hacking and hacktivist groups that changed the world like no one else. Hacking has grown massively in the...
-

 249Geek
249GeekFugitive Tells Police To Use Better Photo of Him on Facebook, Gets Arrested
Ohio man Sends Selfie To Police Saying It is a “better photo” than the “terrible” mug shot and Gets Arrested It has...
-
 93Cyber Crime
93Cyber CrimeNew wave of cyberattacks against Ukrainian power industry
ESET has discovered a new wave of cyberattacks attacks against Ukraine's electric power industry. Interesting, the malware that was used is not...
-

 220Geek
220GeekFacebook Integrates TOR into its Android App For Better Privacy
Privacy seekers and admirers have every reason to rejoice since Facebook is bringing TOR, the free anonymizing software to support its android...
-
 84Cyber Crime
84Cyber CrimeESET Trends for 2016: Threats keep evolving as security becomes part of our lives
ESET's Trends for 2016: (In)Security Everywhere report includes a review of the most important events of last year and outlines trends in...
-

 95Malware
95MalwareAsacub Evolves from Simple Spyware to Full-On Android Banking Trojan
Cyber-crooks secretly develop new Asacub Android malware, deploy it for the first time this Christmas. Over the past six months, security experts from...
-

 451Lists
451ListsThese Are The 10 Best Jobs In Tech Field To Apply For In 2016
Short Bytes: Looking for a new job in tech? Here’s an article telling you the 10 bets jobs in the tech field...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




