Featured News
-

 82Incidents
82IncidentsHack Brief: Hello Kitty Sites Spill Details of 3.3 Million Users
SANRIO, THE TOKYO-BASED owner of the Hello Kitty brand, may be Japan’s global purveyor of kitschy cuteness. But the leak of 3.3...
-

 130Data Security
130Data SecurityGomasom Ransomware Decrypted, Get Your Files Back for Free
Some lucky users are about to have a merry Christmas.Users that had the bad luck of getting infected with the Gomasom ransomware...
-
 180Hacked
180HackedAnonymous Hacks 100 Websites To Protest Against Whale Killing
Short Bytes: This Sunday, Japan police revealed that the hacktivist collective Anonymous has attacked about 100 websites in Japan since September. The group...
-

 341News
341NewsHello Kitty Hacked, 3.3 Million Accounts Exposed
The IT security researcher “Chris Vickery” who exposed MacKeeper and Hzone data breach has now discovered a hack of database belonging to...
-

 266News
266NewsTwitter Account of Pharma CEO Martin Shkreli Hacked
Twitter account of the former CEO of Turing Pharmaceuticals Martin Shkreli aka pharma bro has been hacked by an unknown hacker who...
-

 100Data Security
100Data SecurityEvolving Microsoft SmartScreen to protect you from drive-by attacks
Microsoft SmartScreen, integrated with Microsoft Edge, Internet Explorer, and the Windows operating system, has helped protect users from socially engineered attacks such...
-
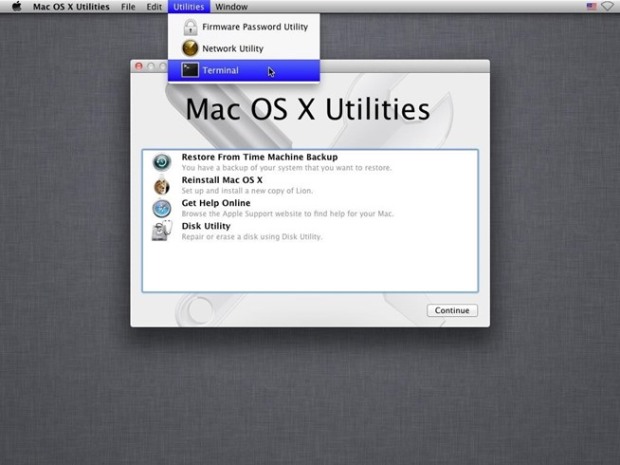
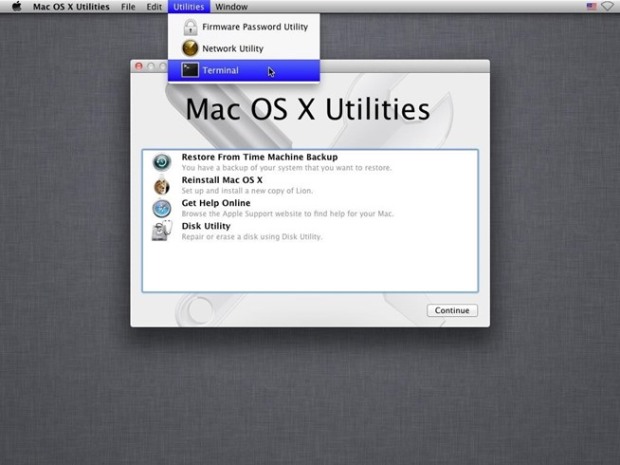 164Data Security
164Data SecurityHow to Hack into a Mac Without the Password
Imagine this. Your girlfriend needs to type a very important report for her Accounting class but she forgot the password to her...
-

 163Data Security
163Data SecurityDeadline for Better Encryption on Payment Systems Pushed Back Two Years
Banking industry needs more time, has too much on its plate.The Payment Card Industry Security Standards Council (PCI SSC) has announced that...
-
 192Geek
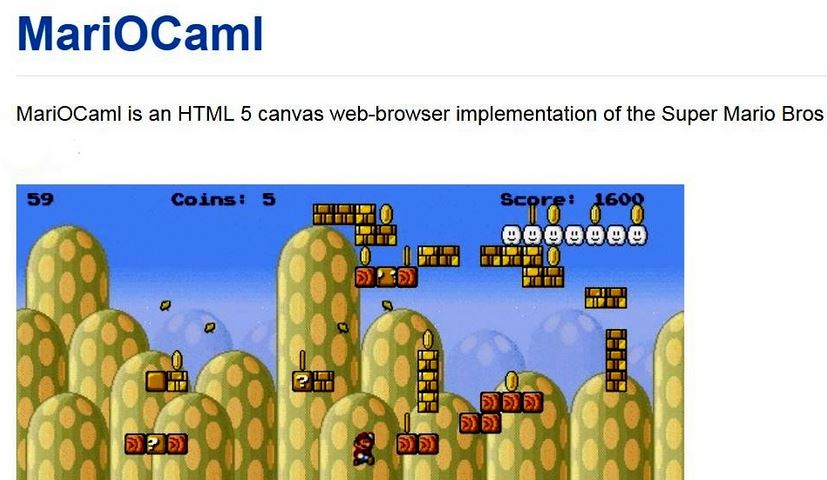
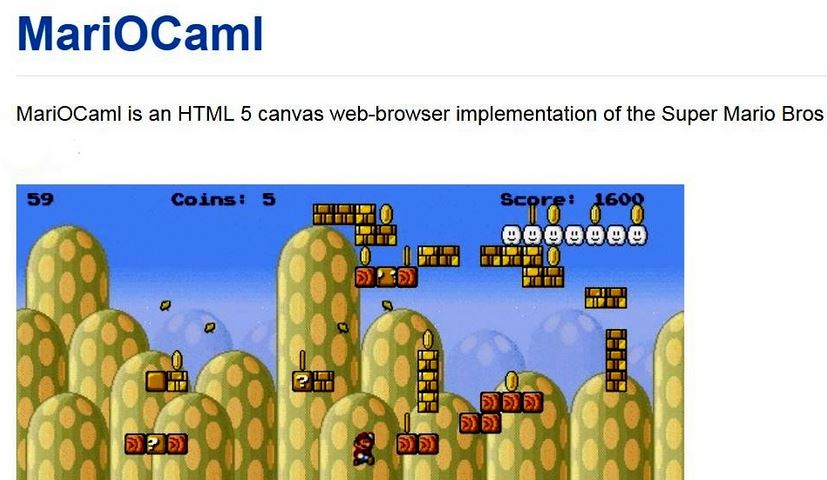
192GeekCoder Creates “HTML5 Mario” Written in OCaml – Play It Right Now In Your Browser
Short Bytes: While playing Super Mario Bros in your desktop web browser was already possible, a coder has given us another reason to...
-
 215Data Security
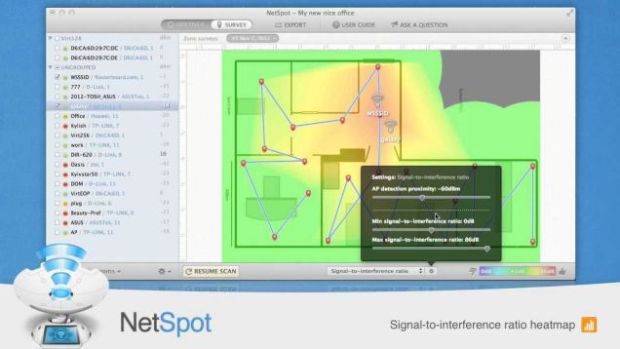
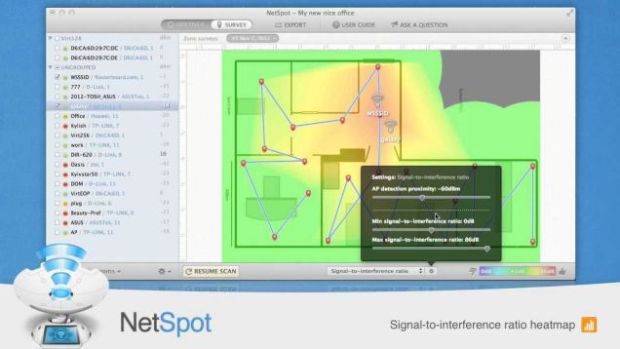
215Data SecurityNetSpot Maps Your Wi-Fi Network and Diagnoses Signal Problems for Free
OS X: NetSpot is a free utility that makes it easy to map out your wireless network, do a site survey if...
-

 107Incidents
107IncidentsData Breach on Hello Kitty Servers, Over 3.3 Million Accounts Exposed
After VTech, another kids service suffers a data breach.Personal details on 3.3 million accounts of Hello Kitty fans are available online, most...
-

 251News
251NewsAnonymous Claims Responsibility For 40 Gbps DDoS Attack on Turkish Servers
The online hacktivist Anonymous has claimed the responsibility for a massive 40Gbps DDoS attack on Turkish DNS Servers under NIC.tr — The reason...
-

 285Geek
285GeekWhy Hoverboards Are Catching Fire and How To Avoid It?
As hoverboards become the number one item on almost every child’s (and some adults) Christmas wish list, reports have emerged over the...
-

 256Geek
256GeekSocial Media Pressure Forces Google To Restore Deleted Cyber Security App
On 17th October 2015, a generous man uploaded an application on Google Play Store named “Cybrary”. The application was meant for people...
-
 195Lists
195ListsBest Antivirus Software for Mac OS X, According To Tests
Short Bytes: OS X is considered comparatively safer than Windows, but it does not necessarily conclude that MAC OS X does not have any...
-
 327News
327NewsArmenian Hackers Leak Sensitive Data from Azerbaijan Ministry Servers
The cyber war between Armenians and Azerbaijani hackers seems never ending — Like this recent cyber attack in which the Armenian hackers...
-

 293News
293NewsLatest Hack May Open Doors For Hackers To Spy on US Government
Juniper network has had a major breach which has led to suspicions of a group of foreign hackers spying on the encrypted...
-
 463How To
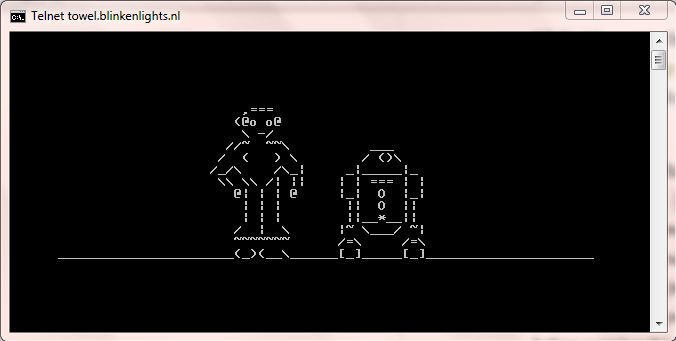
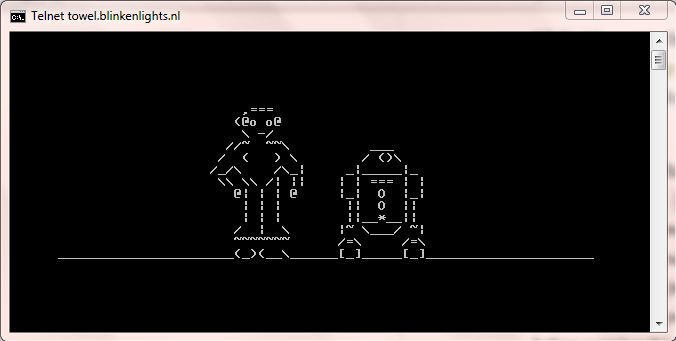
463How ToHow To Watch Star Wars In Command Prompt Via Telnet
Short Bytes: Before driving to your nearest cinema to catch the latest Star Wars movie, here’s something Master Yoda wants you to do....
-

 182Malware
182MalwareSimple Pro POS Malware Could Cause Retail Havoc this Christmas
Security experts have warned US businesses which still haven’t invested in chip and PIN (EMV) readers to remain extra vigilant this holiday...
-
 187Data Security
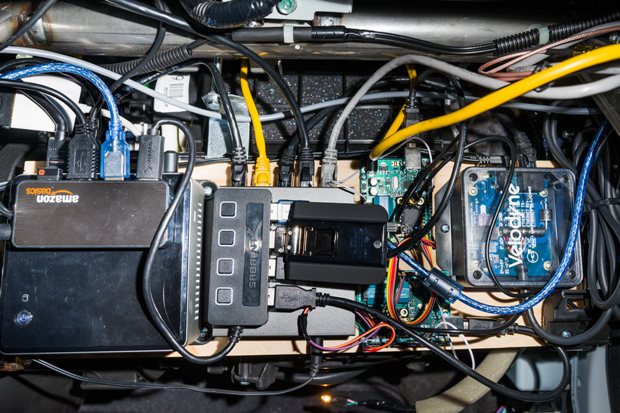
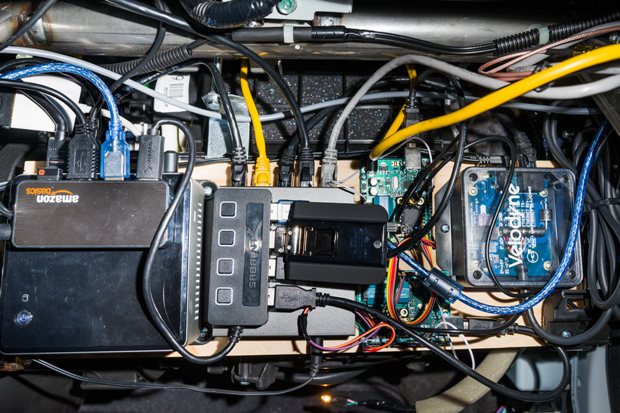
187Data SecurityThe First Person to Hack the iPhone Built a Self-Driving Car. In His Garage
A few days before Thanksgiving, George Hotz, a 26-year-old hacker, invites me to his house in San Francisco to check out a...
The Latest
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment
-
 Data Security
Data SecurityHow Safe is Your TinyProxy? Step-by-Step Guide to Exploiting Tinyproxy’s Zero Day Vulnerability
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications




