Featured News
-
 311News
311NewsISIS Leakes Military Data Against ‘Anonymous ISIS Troll Day’
ShortRead: Anonymous trolled the ISIS terrorists a couple of days ago but rather than replying to the hacktivists, the group leaked personal...
-

 274Geek
274GeekIBM’s New Open Source OMR Project Will Boost Python, Ruby, And Other Languages
Short Bytes: IBM is taking the parts from its JVM project by separating it from Java and making them usable for any...
-
 285Data Security
285Data SecurityTor Hires Top Privacy Advocate Shari Steele As New Executive Director
Tor has hired a former Electronic Frontier Foundation (EFF) executive director to lead its project that is aimed for making the cyber...
-

 105Cyber Crime
105Cyber CrimeMoonfruit takes customers’ sites offline, as it prepares for DDoS attack
A UK company which helps consumers and small businesses create websites and online stores has taken itself and its customers' sites offline,...
-

 273Cyber Events
273Cyber EventsTwitter Alerting Users on State-Backed Attacks, Urging Use of Tor
After Facebook and Google, Twitter also has started warning message regarding state sponsored attack to some of its users — Alert urges...
-

 159Vulnerabilities
159Vulnerabilities‘Fairly bad core bug’ crushed in Linux 4.4-rc5
Linus Torvalds says almost no-one ‘actually ever hit the problem’, or will code at Xmas. Linux Lord Linus Torvalds says the fourth...
-

 159Kids Online
159Kids OnlineMaking devices secure this Christmas
Increasingly, on special occasions like birthdays and Christmas, parents are buying mobile and internet connected devices for their children. Our guide looks...
-

 291Hacked
291HackedPlayStation 4 Jailbreak Confirmed By Hacker, Pirated Games Now A Possibiltiy
Short Bytes: Sony’s PlayStation 4 is now successfully jailbroken. A hacker has claimed to have developed a completely jailbroken version of the...
-
 276Data Security
276Data SecurityMIT Creates Untraceable Anonymous Messaging System Called Vuvuzela
Researchers are still looking for a Tor alternative.Scientists at the MIT Computer Science and Artificial Intelligence Laboratory (CSAIL) have created an anonymous...
-
 240Hacked
240HackedAnonymous Hacks European Space Agency “Just For The Lulz”
Image: fossBytes Short Bytes: Anonymous is known for taking up different causes and defacing the offensive websites. However, this time, the hacktivist group...
-
 245Geek
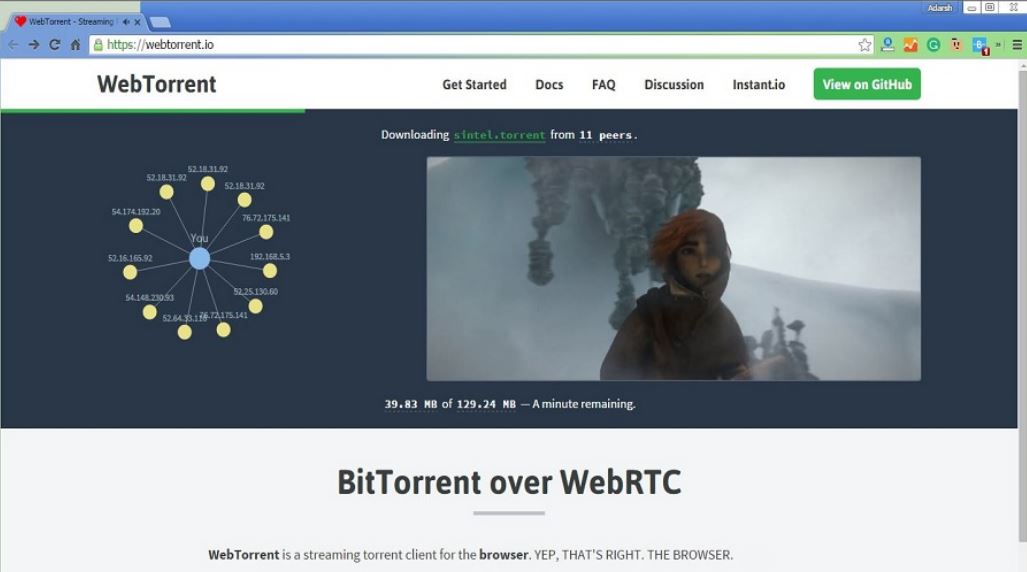
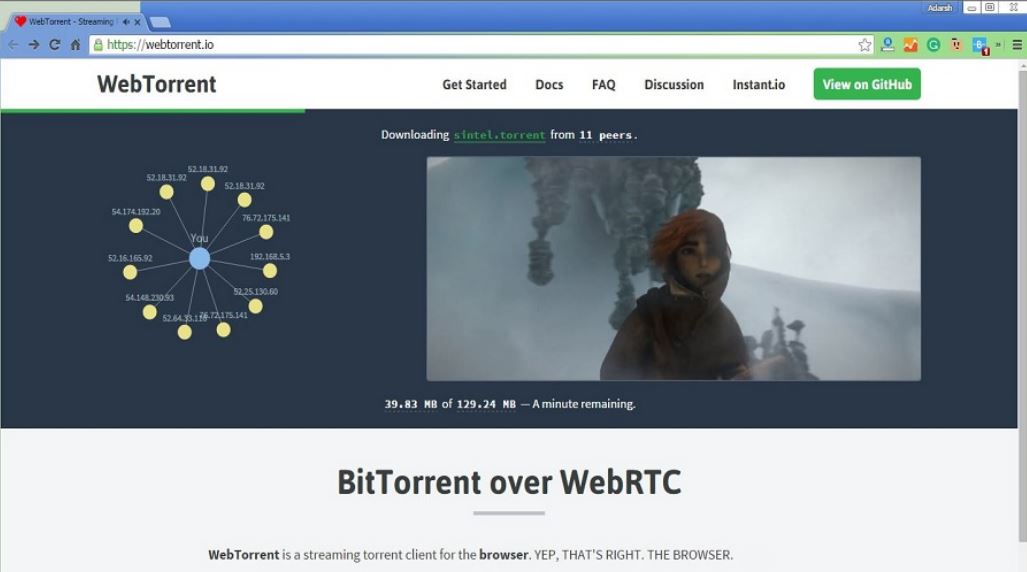
245GeekWebTorrent – World’s First BitTorrent Client For Your Web Browser, Written in JavaScript
Short Bytes: WebTorrent is a BitTorrent client written for the web in JavaScript. It uses WebRTC for P2P transport and you don’t need...
-
 161Data Security
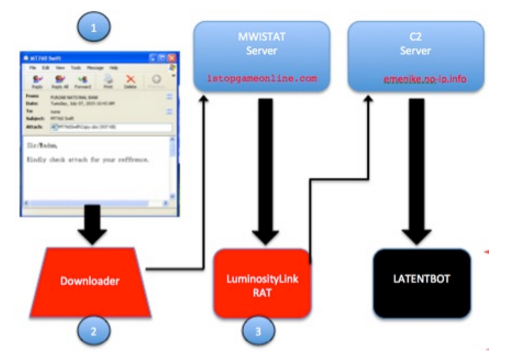
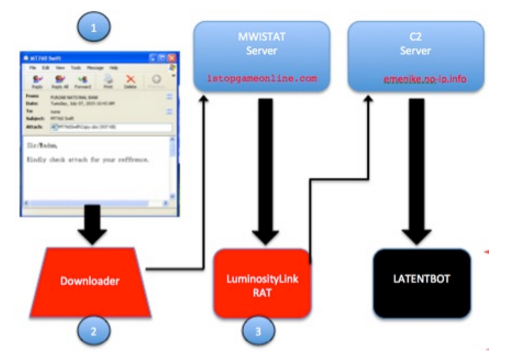
161Data SecurityLATENTBOT, one the highly obfuscated backdoor in the wild
Experts at FireEye have discovered a stealthy botnet relying on a backdoor called LATENTBOT has compromised companies around. Experts at FireEye have discovered...
-

 116Incidents
116IncidentsAnonymous Hacks European Space Agency Just for Fun
he hacker did it “for the lulz,” no other reason.Anonymous have just released data online belonging to the European Space Agency (ESA)....
-

 276Surveillance
276SurveillanceUK May Approve Bill Allowing Spying on Individuals via Their Kids Toys
British government’s new investigatory bill (pdf) has a proposal on making it legal to hack smart toys in order to allow investigators to...
-

 112News
112NewsAnonymous Hacks European Space Agency Domains
ShortRead: The online hacktivist Anonymous has breached the subdomains of the European Space Agency website and leaked personal and login credentials of thousands of...
-

 344Hacked
344HackedWhat Is Anonymous And How Big It Is?
Short Bytes: Anonymous is a decentralized hacktivist group that has been into existence since 2003. It is hard to predict the actual size...
-

 300Geek
300GeekMicrosoft Getting Desperate To Force Upgrade PCs to Windows 10
It’s not surprising to know that Microsoft is desperate to have Windows 10 on user’s PCs. As for users still running Windows...
-

 295Geek
295GeekThese Anti-Surveillance Tools Will Protect Activists and Their Privacy
In a world where government surveillance is a big thing there is a need for tools countering the whole idea of keeping...
-

 1.7KData Security
1.7KData Security“Vuvuzela” SMS Text Messaging System More Secure Than Tor
MIT researchers claim they have developed “Vuvuzela” SMS Text Messaging System which is way more secure than Tor and provides guaranteed untraceable communication....
-
 111Cyber Crime
111Cyber CrimeAttacker Embeds Malware in The Guardian’s Cybercrime Article
An article published by The Guardian in 2011 on the topic Cybercrime: is it out of control? received a nasty response from a...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




