Featured News
-

 94Malware
94MalwareGlassRAT Zero-Detection Trojan Targets Chinese Nationals
A previously undetectable remote administration tool has been uncovered, dubbed “GlassRAT” The zero-detection Trojan appears to have operated stealthily for three years,...
-

 170Data Security
170Data SecurityCatching Up With The ‘EITest’ Compromise, A Year Later
We are seeing dozens of WordPress sites compromised recently with the same malicious code redirecting to the Angler exploit kit. The attack involves conditionally...
-

 169Data Security
169Data SecurityDocuments demonstrate NSA continued mass surveillance
Newly disclosed documents show that the NSA had found a way to continue spying on American citizens’ email traffic from overseas. The...
-
 186Data Security
186Data SecurityResearchers Find Multiple Chrome Extensions Secretly Tracking Users
Hidden analytics code tracks everything users do, EVERYTHING Analytics code deeply hidden in popular Google Chrome extensions is being used to track...
-
 196Data Security
196Data SecurityDell does a Superfish, ships PCs with easily cloneable root certificates
Root certificate debacle that hit Lenovo now visits the House of Dell. In a move eerily similar to the Superfish debacle that...
-

 247News
247NewsThis Group Spies on ISIS Rather Than Exposing Twitter Handles
The readers know about Anonymous waging war against ISIS, but hardly anyone knows about a group which has been working quietly (well,...
-

 227Data Security
227Data SecurityAnti-NSA Phone Developers Vow to Keep Their Product Away From Terrorists
Silent Circle, the developer of the self-proclaimed NSA-proof smartphone has announced that it is making sure to distances itself from criminals and terrorists...
-

 276Password
276PasswordIs biometrics the future of secure payments?
Is the idea of biometrics as a secure payment system a fad, fiction or fact? This feature looks at whether DNA is...
-

 307Hacked
307HackedISIS Moving To The Dark Web To Escape Hackers And Spread Its Message
Short Bytes: In order to protect its online operations from security agencies and hackers, and to propel its propaganda, ISIS is looking...
-

 328News
328NewsISIS Releases Another Kill List of US Military and Security Officials
ISIS has unveiled list of U.S. officials who are on their target — The list includes names of both current and former...
-

 266Hacked
266HackedHow Belgians Trolled And Confused ISIS Terror Threats With Cat Pictures On Twitter
Short Bytes: Belgian people have found a new weapon to deal with the terror threats in the form of cat pics. As...
-

 101Data Security
101Data Security‘Spying’ on Islamic State instead of hacking them
In the wake of the Paris attacks, the vigilante hacker group Anonymous has declared war on so-called Islamic State using the internet...
-

 186Data Security
186Data SecurityHere’s the ISIS OPSEC Manual Used to Train Recruits About Cyber-Security
ISIS hijacks Kuwait security firm’s OPSEC manual.Yesterday, various Twitter accounts were tweeting about an ISIS OPSEC manual describing the terrorist group’s cyber-security...
-
 185Data Security
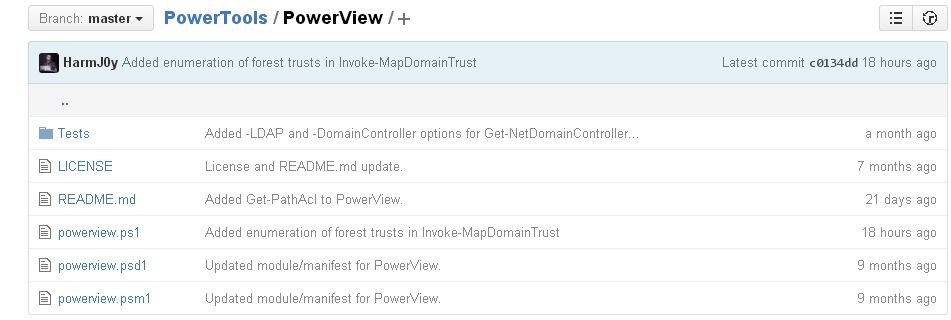
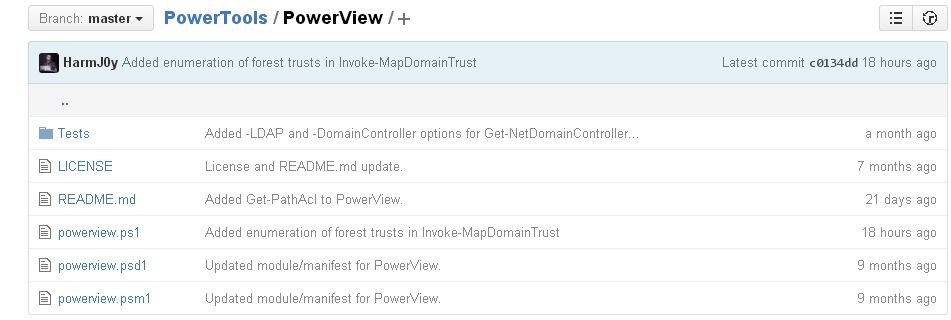
185Data SecurityHacking and exploiting Active Directory Permissions
PowerView is a PowerShell tool to achieve network information on Windows domains for cyber security services and ethical hacking training professionals. It...
-

 263Data Security
263Data SecurityResearchers say they’ve cracked the secret of the Sony Pictures hack
Log wipers, timestompers may have helped hackers stay quiet in terabyte raids. Damballa researchers Willis McDonald and Loucif Kharouni say the attackers...
-
 164Malware
164MalwareCryptInfinite or DecryptorMax Ransomware Decrypted
We have received a lot of reports about a new ransomware that we are calling CryptInfinite based on the Windows Registry key created by this ransomware....
-

 187News
187NewsHackers Target Starwood Hotels, Steal Credit Card Data Using Malware
Chain of hotels owned by Starwood Hotels & Resorts Worldwide properties faced a data breach earlier this year and hackers got access...
-
 183Hacked
183HackedISIS Hackers Post A “Wanted To Be Killed” List Of U.S. Officials
Short Bytes: The ISIS hackers, calling themselves the “Islamic State Cyber Army,” have used Twitter to post the names and addresses of...
-

 283Cyber Crime
283Cyber CrimeSmart eBay Scammer Tricks, Steals Identity of His Investigating Officer
Rohit Jawa, a 25-year-old man, was arrested in Cincinnati, Ohio on 15th June 2015 for scamming on eBay — He was accused...
-

 176Hacked
176HackedAnonymous Warns About Possible “Worldwide Attack By ISIS” Today (Updated)
Short Bytes: The Anonymous hacktivists have claimed that they have uncovered a secret Islamic State plan for a worldwide terror attack this Sunday....
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks




