Featured News
-

 279Password
279PasswordIs biometrics the future of secure payments?
Is the idea of biometrics as a secure payment system a fad, fiction or fact? This feature looks at whether DNA is...
-

 310Hacked
310HackedISIS Moving To The Dark Web To Escape Hackers And Spread Its Message
Short Bytes: In order to protect its online operations from security agencies and hackers, and to propel its propaganda, ISIS is looking...
-

 330News
330NewsISIS Releases Another Kill List of US Military and Security Officials
ISIS has unveiled list of U.S. officials who are on their target — The list includes names of both current and former...
-

 271Hacked
271HackedHow Belgians Trolled And Confused ISIS Terror Threats With Cat Pictures On Twitter
Short Bytes: Belgian people have found a new weapon to deal with the terror threats in the form of cat pics. As...
-

 102Data Security
102Data Security‘Spying’ on Islamic State instead of hacking them
In the wake of the Paris attacks, the vigilante hacker group Anonymous has declared war on so-called Islamic State using the internet...
-

 190Data Security
190Data SecurityHere’s the ISIS OPSEC Manual Used to Train Recruits About Cyber-Security
ISIS hijacks Kuwait security firm’s OPSEC manual.Yesterday, various Twitter accounts were tweeting about an ISIS OPSEC manual describing the terrorist group’s cyber-security...
-
 188Data Security
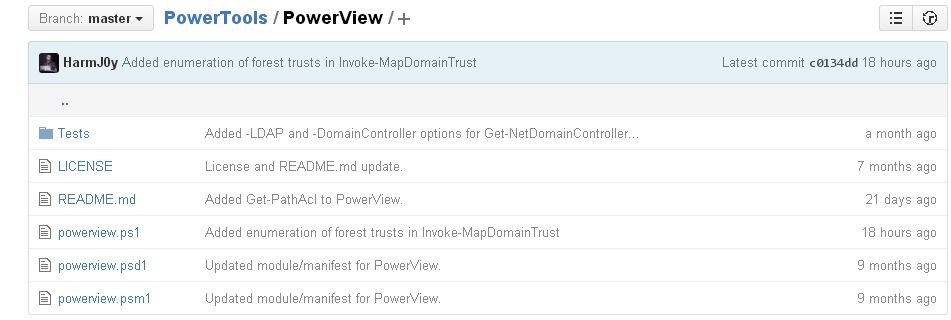
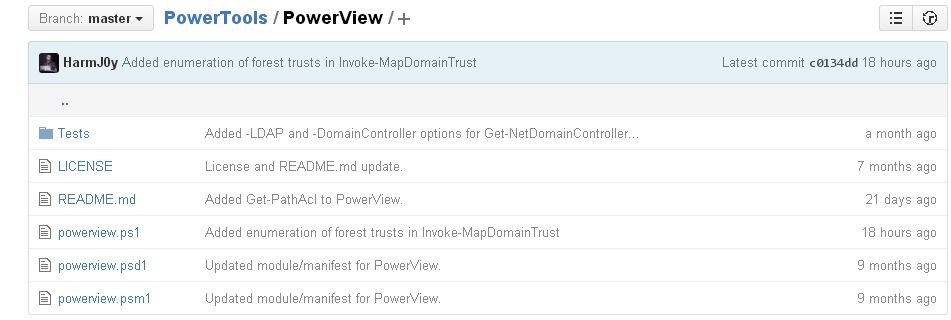
188Data SecurityHacking and exploiting Active Directory Permissions
PowerView is a PowerShell tool to achieve network information on Windows domains for cyber security services and ethical hacking training professionals. It...
-

 267Data Security
267Data SecurityResearchers say they’ve cracked the secret of the Sony Pictures hack
Log wipers, timestompers may have helped hackers stay quiet in terabyte raids. Damballa researchers Willis McDonald and Loucif Kharouni say the attackers...
-
 166Malware
166MalwareCryptInfinite or DecryptorMax Ransomware Decrypted
We have received a lot of reports about a new ransomware that we are calling CryptInfinite based on the Windows Registry key created by this ransomware....
-

 191News
191NewsHackers Target Starwood Hotels, Steal Credit Card Data Using Malware
Chain of hotels owned by Starwood Hotels & Resorts Worldwide properties faced a data breach earlier this year and hackers got access...
-
 187Hacked
187HackedISIS Hackers Post A “Wanted To Be Killed” List Of U.S. Officials
Short Bytes: The ISIS hackers, calling themselves the “Islamic State Cyber Army,” have used Twitter to post the names and addresses of...
-

 289Cyber Crime
289Cyber CrimeSmart eBay Scammer Tricks, Steals Identity of His Investigating Officer
Rohit Jawa, a 25-year-old man, was arrested in Cincinnati, Ohio on 15th June 2015 for scamming on eBay — He was accused...
-

 178Hacked
178HackedAnonymous Warns About Possible “Worldwide Attack By ISIS” Today (Updated)
Short Bytes: The Anonymous hacktivists have claimed that they have uncovered a secret Islamic State plan for a worldwide terror attack this Sunday....
-
 283News
283NewsAnonymous Has Shutdown 28,000+ ISIS’ Twitter Accounts Since OpParis Began
The online hacktivist Anonymous shut down 8824 Twitter accounts of ISIS members + followers in the first phase of OpParis — In...
-

 326News
326NewsSelf-Proclaimed Anonymous Hacktivists Predict Potential ISIS Terror Attacks
Someone is using Anonymous’s name to spread rumors about ISIS planning to target different events worldwide. A Pastebin post posted by someone claiming to have a...
-

 319Cyber Crime
319Cyber CrimeCrooks Hack World Bank SSL Certificate To Host PayPal Phishing Scam
Hackers have again attacked PayPal but this time by making a clone site that even had an SSL certificate of the World...
-

 317Data Security
317Data SecurityAnonymous Has Now Taken Down 20,000 ISIS Twitter Accounts, Promises to Go On
Hacking group remains as focused as one week ago Quite a lot has happened after Anonymous declared cyber-war on ISIS members last...
-

 116Data Security
116Data SecurityHow to Baffle Web Trackers by Obfuscating Your Movements Online
ONLINE AD NETWORKS and search engines love it when you surf around. Everything you do—every page you load, every query you type—helps...
-
 218Vulnerabilities
218VulnerabilitiesVMware Patches Pesky XXE Bug in Flex BlazeDS
VMware has patched an information disclosure vulnerability affecting a number of its products that use Flex BlazeDS. The original vulnerability was discovered...
-

 217Incidents
217IncidentseBay Scammer Steals Identity of the Police Officer Investigating His Case
Rohit Jawa fools officer into revealing personal details. Police officers investigating an eBay scammer must have been very surprised when the criminal, in...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




