Featured News
-
 248Cryptography
248CryptographyHow to set your Pendrive as your password protector for PC
If you prevent access to your computer with just a password, you are missing out on an alternate (and more secure) way...
-

 235Geek
235GeekThis New Gadget Transforms Paper Airplanes into Powerful Drones
Powerup and French drone-maker firm Parrot collaborated together to create a revolutionary new gadget that easily converts something as insignificant like a...
-
 182Geek
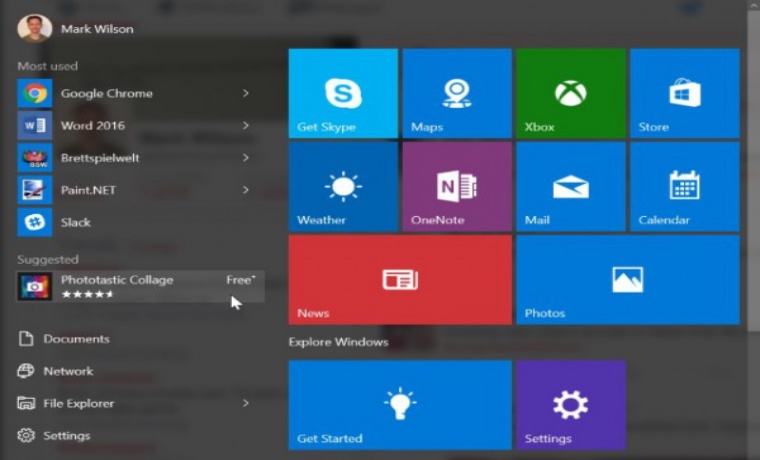
182GeekWindows 10 Start Menu- Microsoft’s Chosen Platform for Displaying Online Ads
Microsoft’s Windows 10 is known for collecting personal data of its users, but who thought the firm will be forcefully displaying ads...
-
 208Cyber Crime
208Cyber CrimeKosovan Hacker Detained in Malaysia for Hacking, Sharing Military Data to IS
A Kosovan man named Ardit Ferizi has been arrested in Malaysia for suspected hacking of US military databases comprising of personal information of...
-

 159News
159NewsDid Russians Hack Dow Jones for Trading Tips?
Dow Jones Hacked by Russians for Obtaining Trading Tips — No one knows how much money the made. A group of Russian...
-

 153Data Security
153Data SecurityYahoo only the latest at “kill the password” altar
Industry looking to improve access controls and authentication, but decisions still governed by security requirements, use cases, hacker disruption. Yahoo this week...
-

 166Data Security
166Data SecurityRussian Hackers of Dow Jones Said to Have Sought Trading Tips
A group of Russian hackers infiltrated the servers of Dow Jones & Co., owner of the Wall Street Journal and several other...
-

 92Vulnerabilities
92VulnerabilitiesFirst Major Ubuntu Touch Exploit Is a Wake-up Call for Canonical
Developers have been quick to fix the problem. An important security issue on Ubuntu phone that has been revealed this morning has been...
-

 166Malware
166MalwareMicrosoft is ready to save your PC from huge ransomware infection
TeslaCrypt doesn’t mean anything to many PC users, but there are thousands of people who have somehow contracted this infectious malware program that...
-
 281Hacked
281HackedInternet Inventor Vint Cerf and Experts Suggest 5-Points to Improve WiFi Router Security
Short Bytes: The FCC is on the receiving end over its proposed rules to alter WiFi routers to make them secure as...
-

 200Geek
200GeekHere are few things you should know about Facebook privacy before it’s too late
Facebook is a great platform for those who are looking for new friends, finding old ones or to promote their business. In...
-

 195Incidents
195IncidentsUltraDNS Server Problem Pulls Down Websites, Including Netflix, for 90 Minutes
UltraDNS, a web content delivery service, went down Thursday afternoon, taking with it a number of popular websites, including Netflix and Expedia....
-
 277Hacked
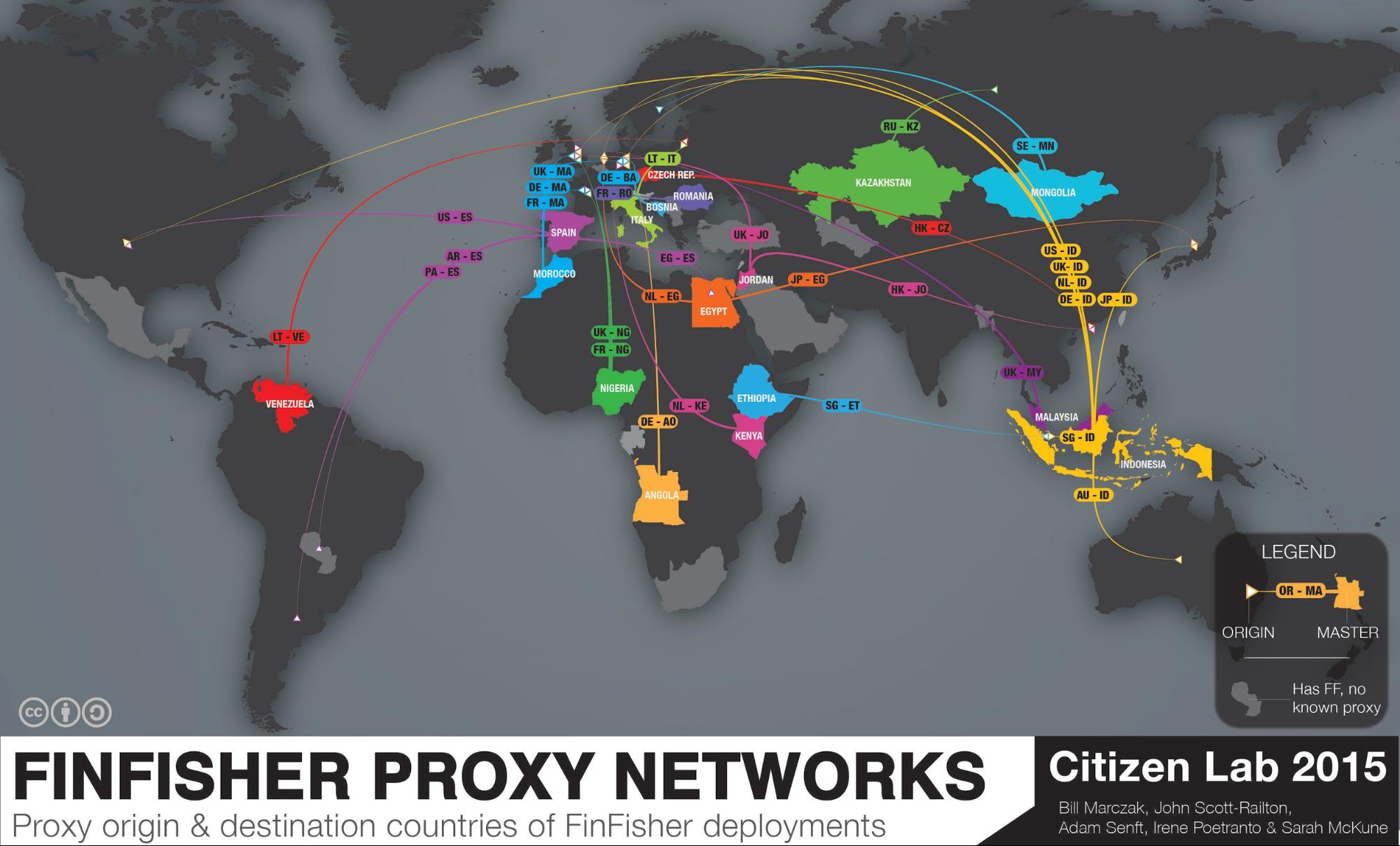
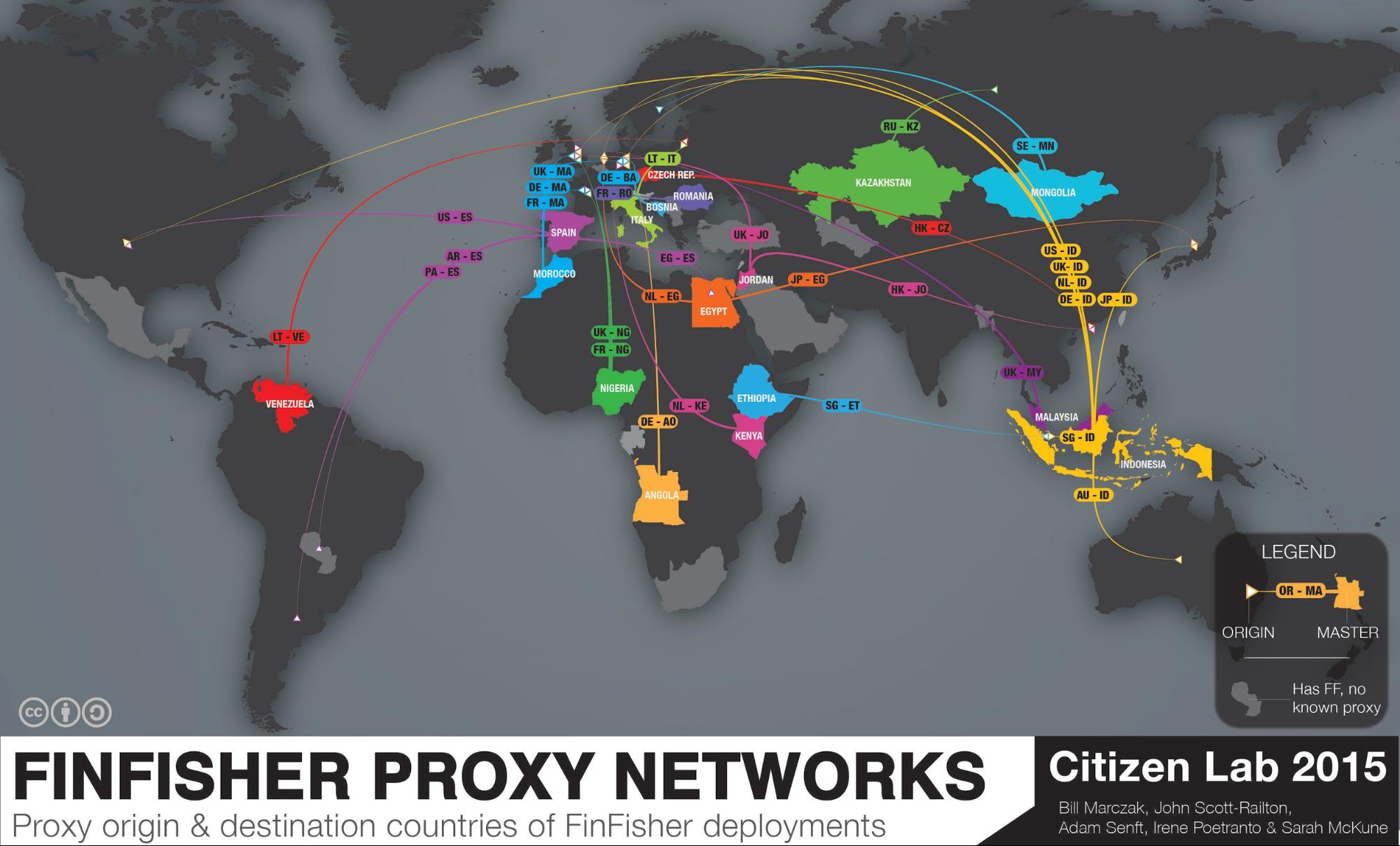
277HackedThis Nearly “Impossible to Trace” Spyware is Used by 32 Governments to Spy on You
Short Bytes: In 2015, the infamous spyware FinFisher is spread in 32 countries to perform advanced citizen surveillance. Citizen Lab, a security watchdog,...
-
 179Data Security
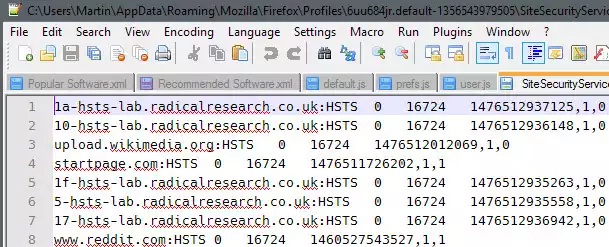
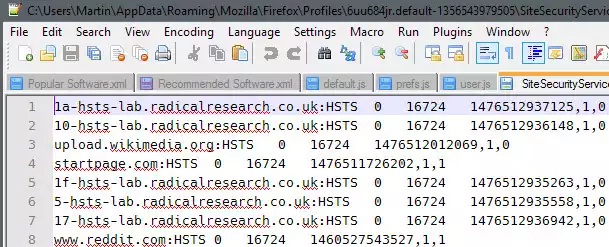
179Data SecurityHow to prevent HSTS tracking in Firefox
HTTP Strict Transport Security (HSTS) was designed to help secure websites (those using HTTPS) by declaring to web browsers that they should...
-

 178Hacked
178HackedFacebook Scans Your Phonebook To Guess Who You Are Dating Online
Short Byte: In a bizarre incident, Facebook users are reportedly seeing increasing friend suggestions of the people they have dated before through...
-

 203Lists
203ListsBest Flying Cars of The Future, Pick Your Ride
Short Bytes: Flying cars dream would soon change into a reality. So, get ready and pick your ride in advance. Good luck...
-

 200Vulnerabilities
200VulnerabilitiesWordPress Fixes Critical Stored XSS Error in Akismet
Developers at Automattic, the parent company behind the blogging platform WordPress, fixed a nasty stored cross-site scripting error this week in Akismet,...
-

 78Data Security
78Data SecurityBrolux trojan targeting Japanese online bankers
A banking trojan, detected by ESET as Win32/Brolux.A, is targeting Japanese internet banking users and spreading through at least two vulnerabilities: a...
-

 140Data Security
140Data SecurityHow the NSA can break trillions of encrypted Web and VPN connections
Researchers show how mass decryption is well within the NSA’s $11 billion budget. For years, privacy advocates have pushed developers of websites,...
-

 171Geek
171GeekHackers show Google Now and SIRI can be hacked via Radio waves
Hacking SIRI and Google Now silently from 16feet away now possible via Headphones, claim ANSSI Researchers. French researchers at the government’s information...
The Latest
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment
-
 Data Security
Data SecurityHow Safe is Your TinyProxy? Step-by-Step Guide to Exploiting Tinyproxy’s Zero Day Vulnerability
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications




