Featured News
-

 315Data Security
315Data SecurityTerrorists Can Use Our Leaked RCS Spyware, Hacking Team Says
The infamous spyware dealer, Hacking Team, has now begun to complain that their recently leaked Remote Control System (RCS) spyware tool which...
-
 168Hacked
168HackedArtist Hacks Surveillance Cameras to Spy on Town and Makes Photo Album
The New Town photographs by Andrew Hammerand According to a report by IHS, there were 245 million surveillance cameras operating globally in...
-
 201Hacked
201HackedDid Anonymous Hack New York Stock Exchange?
When you have the power of anonymity, you can do things that are unimaginable for others. The hacktivist group Anonymous is well-known...
-

 185Cyber Crime
185Cyber CrimeGoogle Docs Users Targeted with “Confidential Document” Phishing Scam
The purpose of this scam message is to steal Google Account Login credentials. Users are urged to click on a fake link...
-

 284News
284NewsSubdomain of U.S. Dept. of Energy’s Argonne National Lab Hacked by ISIS Hackers
Did you notice the pro-ISIS hackers are targeting high-profile websites without any restriction? Yesterday, we exclusively reported how the State Ministry for Euro-Atlantic...
-
 391How To
391How ToHow To Prevent Your Computer From Overheating
An overheating computer spells trouble. You would want your girlfriend to be smoking hot but trust me, neither you want your computer...
-
 329Data Security
329Data SecurityKovter AdFraud Malware Updates Flash Plugin to Latest Version
We all know that one of the basic procedures to keep our computer system secure and free from viruses and malware is...
-

 225Hacked
225HackedKali Linux 2.0 Release Day Scheduled: Kali Sana Coming, Powerful Than Ever
Ever since its debut in the year 2013, Kali Linux users were waiting for a new and revamped version of the hack-friendly...
-

 171How To
171How ToHow to mirror your Android mobile screen to PC screen
These days, we can almost connect any two devices wirelessly on the same network. Mirroring your Android device can be very useful...
-
 114Geek
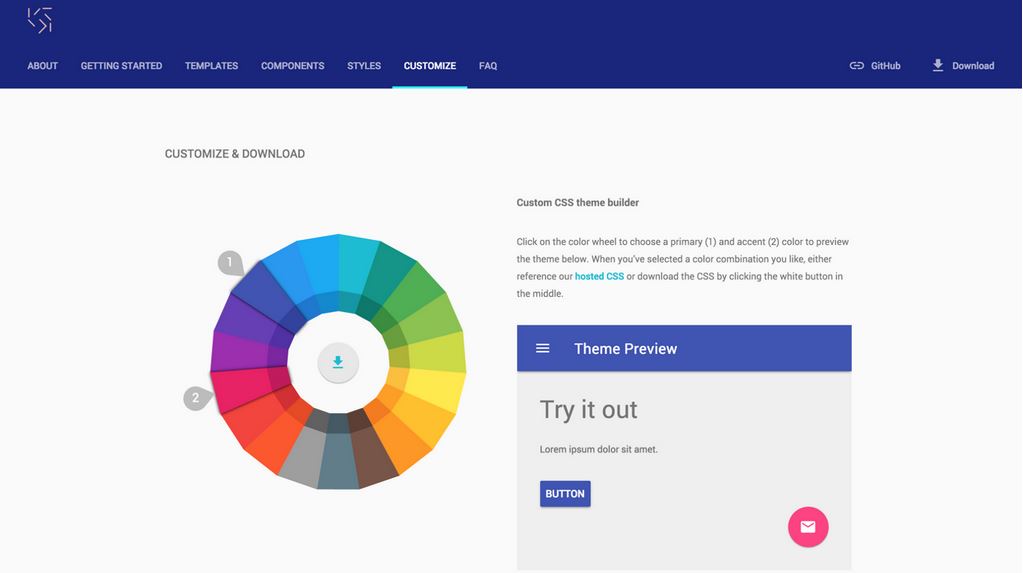
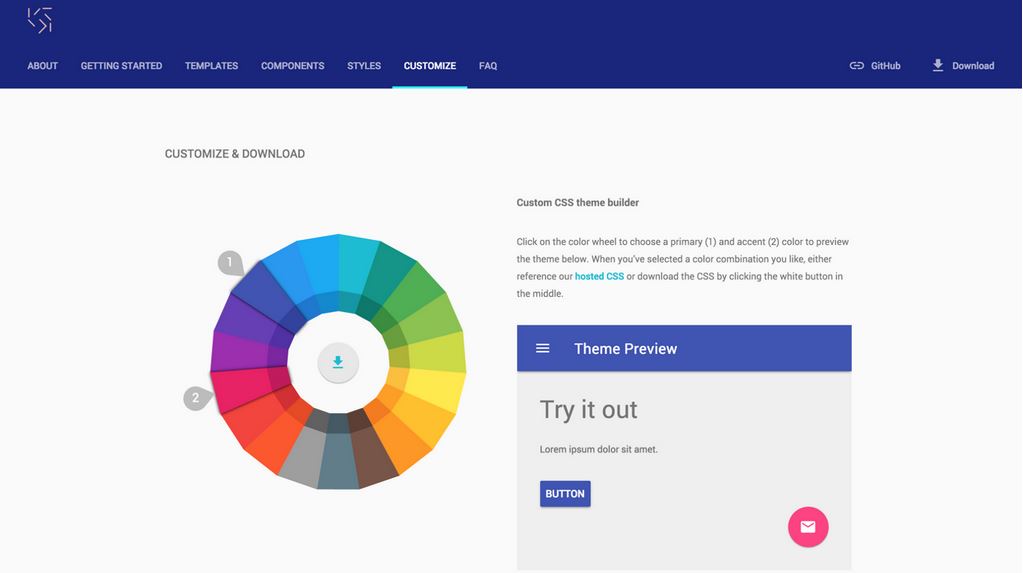
114GeekGoogle Makes Website Making Easy With “Material Design Lite” and Free Website Builder
Google introduced its concept of material design and its specification to make the user interfaces more beautiful and uniform on devices all...
-

 317News
317NewsWebsite of Ministry for Euro-Atlantic Integration of Georgia, NATO Hacked by ISIS Hackers
The ISIS hackers just hacked a high-profile website funded by the European Union. A group of pro-Islamic State (IS, previously ISIS/ISIL) hackers...
-

 331Geek
331GeekPrehensile, a Sophisticated 3D Printable Prosthetic Hand
Lately, we have seen some of the most exciting developments in the futuristic manufacturing industry. Irrespective of you being a specialized professional...
-
 353News
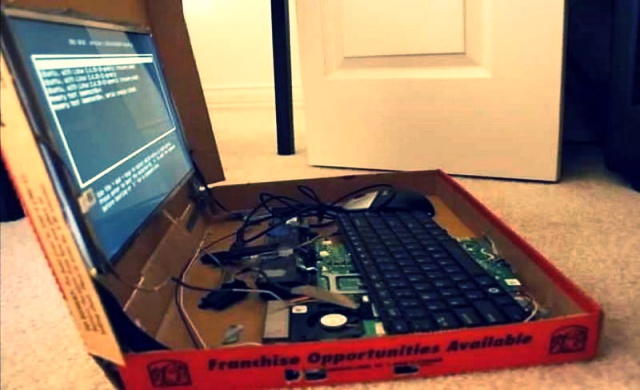
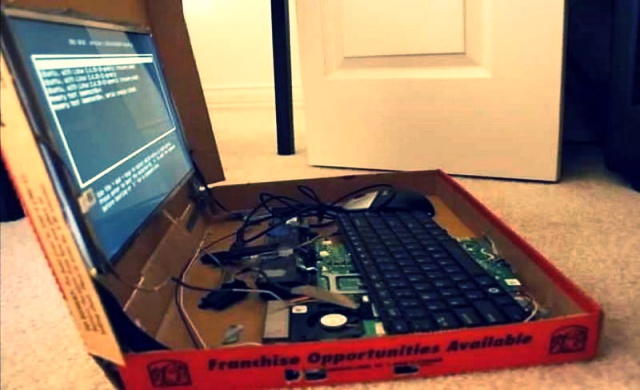
353NewsPizza Hut Israel Website Hacked with a Warning for Indian Government
You’ve seen us posting news about pro-Palestinian hackers targeting Israeli sites or vice versa, but did you ever think of Bangladeshi hackers...
-

 452Privacy
452PrivacyT‑Mobile received the most US data requisition requests
Telco T-Mobile’s US arm received more data requests than its larger peers in 2014.
-
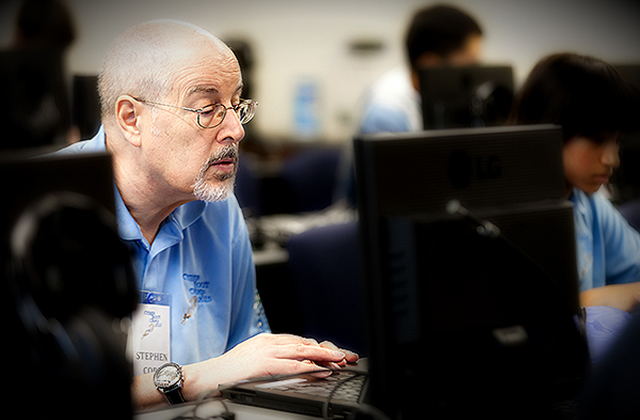
 87Kids Online
87Kids OnlineWhat I learned at Cyber Boot Camp (Instructor Edition)
Teaching computer security to highly motivated students at Cyber Boot Camp reveals a lack of basic computer science education in California Schools.
-

 193Hacked
193HackedRussian Superweapon That Can “Switch Off” All Enemy Satellites
A Topol-M missile on MZKT-79221 mobile launcher (Image: Wikipedia) With the ever advancing technology, the modes of warfare have also developed with...
-
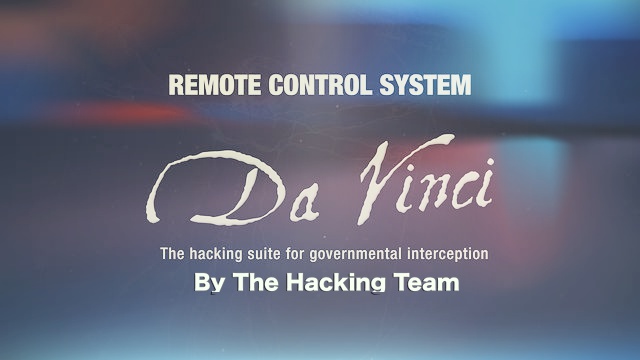
 245News
245NewsHacking The Hacking Team Shows Regimes Love Spying on Its Citizens
The Italy-based security firm Hacking Team, known for providing spying tools to the Drug Enforcement Administration (DEA) in U.S has been hacked. ...
-

 214How To
214How ToHow To Create A Simple Batch File For Windows
Hackers can create very dangerous batch files which can destroy your computer but here we are going to teach you on how to...
-

 283Geek
283GeekRaspberry Pi DIY: How to Preserve and Sync Data in a Mason Jar Using Pi
Enough about storing your data on world’s smallest 128GB memory card or some other invention poised to be the next HDD-killer. Today,...
-
 81Hacked
81HackedHousing.com Site Hacked, Rahul Yadav Says It’s not him
Housing.com is one of the big names in Indian real estate arena that you would encounter if you are looking for a...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




