Featured News
-
 156Geek
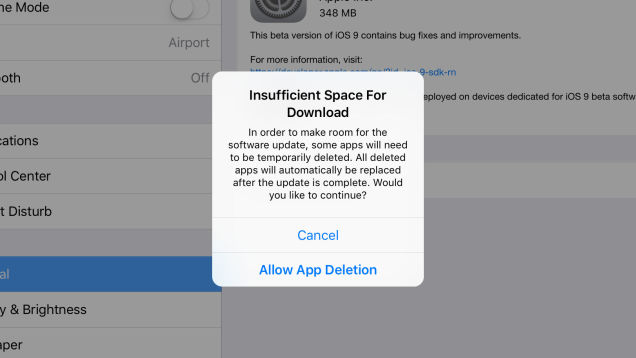
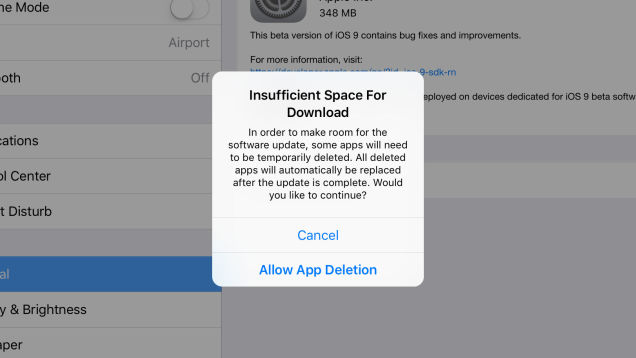
156GeekiOS 9 will Delete Your Existing Apps to Make Room for Updates
A MacRumors Forum user has stumbled upon the fact that when installing the iOS 9 (beta version), the operating system will delete...
-

 306Surveillance
306SurveillanceEuropol to Hunt Extremists Spreading ISIS Propaganda on Social Media
Europol is going after people using social media platforms to spread ISIS propaganda. It was the Anonymous hacktivist group who took the...
-

 305Surveillance
305SurveillanceFacebook Moments App Sends Your Images From Camera Roll With Facial Recognition
A new photo-sharing application has been released by Facebook this week called Moments. This app utilizes facial recognition technology to tag and...
-

 242News
242NewsAnonymous Hacks Montreal Police Union, Transportation Systems Websites
The online hacktivist Anonymous hacked and defaced the the official website of Montreal Police Union (Fraternité des policiers et policières de Montréal)...
-
 106Privacy
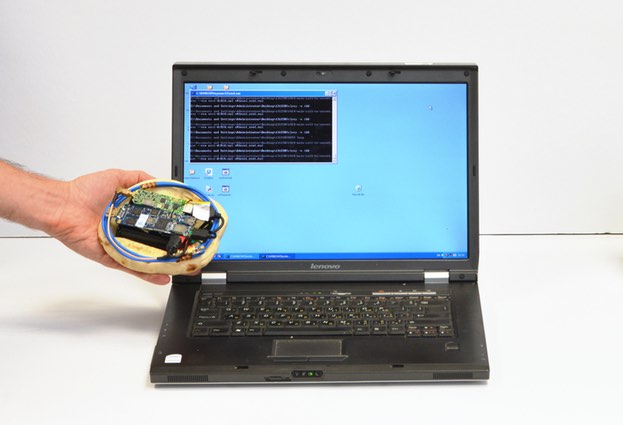
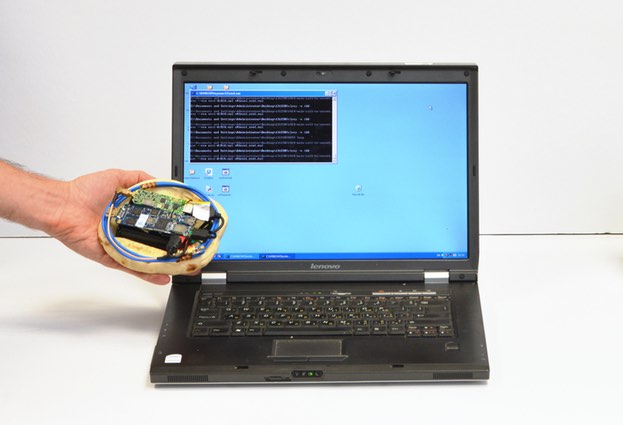
106PrivacyHow to steal PGP encryption keys (using radio waves and pita bread)
An ingenious team of Israeli security researchers at Tel Aviv University have discovered a way to steal secret encryption keys using a...
-

 197Malware
197MalwareThe role of proxies and protocols in malware investigations
What is a proxy and what types of proxies exist? What protocol are used in the anonymization process? How does anonymity help...
-

 353Hacked
353HackedNSA Hacked Kaspersky Labs and Other Anti-virus Software to Track Users
According to the latest documents revealed by NSA whistleblower Edward Snowden, the National Security Agency (NSA) and its British counterpart, Government Communications...
-
 294Hacked
294HackedFacebook Can Now Recognize You in Photos Without Even Seeing Your Face
I’m fan of Facebook’s facial recognition technology and how efficiently is tags you automatically in pictures. Facebook is constantly improving its technology...
-
Operating Systems
Linux…. Where did it come from?
Linux was originally developed as a free operating system for personal computers based on the Intel x86 architecture, but has since been...
-

 66Cyber Crime
66Cyber CrimePolish airline LOT grounded by ‘first attack of its kind’
Hackers are being blamed for an attack which grounded 1,400 passengers set to fly on Polish airline LOT.
-

 212Hacked
212Hacked10 Flights and 1,400 Passengers Grounded by Hackers in Poland
Yesterday in Poland, 10 flights operated by Poland’s national airline LOT were grounded after facing a flight hack attack on its computer...
-

 284News
284NewsGoogle Vanuatu Domain Hacked, Left with Anti-Morocco Messages
A Sahrawi hacker going with the handle of Kuroi’SH hacked and defaced the Google Vanuatu domain in support for the freedom of Western Sahara....
-
 193Hacked
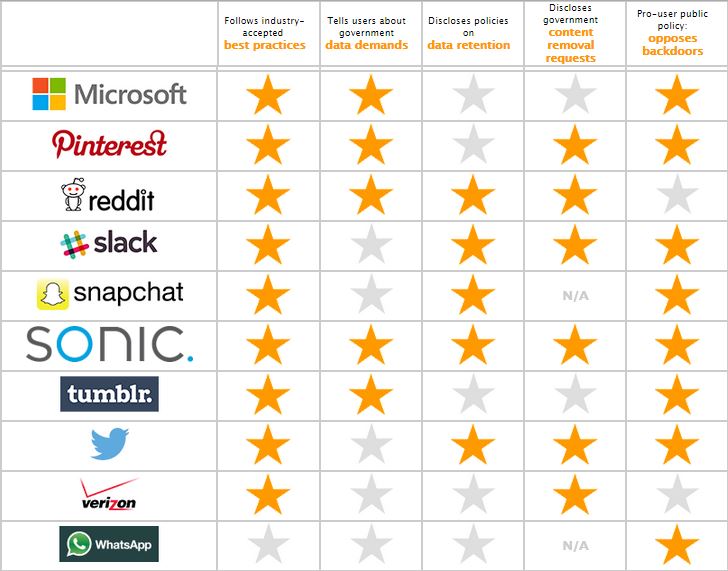
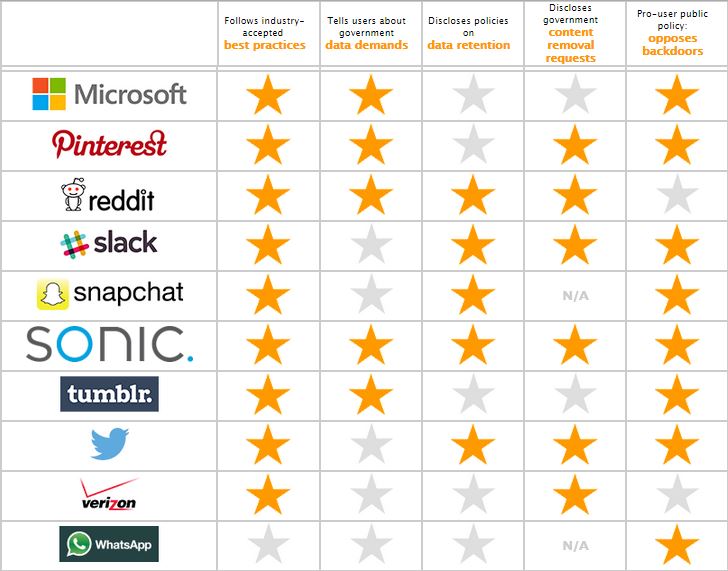
193HackedEFF Report: WhatsApp Ranked Worst At Keeping Your Data Safe
In the annual report of the Electronic Frontier Foundation, big players like WhatsApp and AT&T have been ranked worst in protecting your...
-

 195News
195NewsKatie Hopkins Twitter Account Hacked, Threatens To Leak Sex Tape
Someone hacked the official Twitter account of UK based controversial Television personality, The Sun’s columnist Katie Hopkins and threatened to leak a sex...
-

 371How To
371How ToHow To Pick Your First Programming Language (4 Different Ways)
Learning coding from scratch could be a tough task and it could take years of hard work to master a language. So,...
-

 418Hacked
418HackedHow Attacker Can Hack Your Email Account Just With Your Phone Number
With the increased intrusion of technology, the threats of security breaches into out internet-governed lives have increased manifold. Each day we get...
-

 294Data Security
294Data SecurityAndroid Bug Bounty Program Launched by Google
Android Bug Bounty Program is here and it’s your time to report bugs and get paid. Google’s bug bounty or security rewards...
-
 421How To
421How ToHow to Get Free Genuine Windows 10 Even If You Don’t Have Windows 8 or 7
It’s an old news that Windows 10 will be available as a free download to Windows 7 and Windows 8 users. This...
-
Hacking Tutorials
How to inbox Facebook users from anyone’s account
Facebook hacking has been a major “topic” for the curious user,but today i’ll be focusing on an easy trick to send messages...
-

 233News
233NewsWikiLeaks Releases 275k+ Hacked Sony Documents
WikiLeaks, a whistle-blowing site has published 276,394 new docs taken from Sony in Nov by an anonymous attacker. It adds to the...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




