Featured News
-
 116Geek
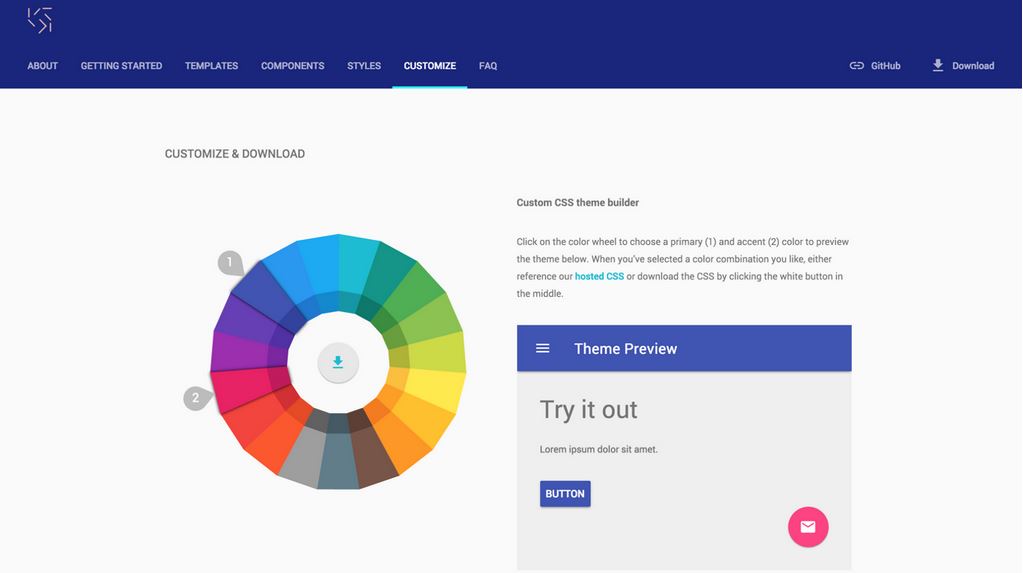
116GeekGoogle Makes Website Making Easy With “Material Design Lite” and Free Website Builder
Google introduced its concept of material design and its specification to make the user interfaces more beautiful and uniform on devices all...
-

 318News
318NewsWebsite of Ministry for Euro-Atlantic Integration of Georgia, NATO Hacked by ISIS Hackers
The ISIS hackers just hacked a high-profile website funded by the European Union. A group of pro-Islamic State (IS, previously ISIS/ISIL) hackers...
-

 331Geek
331GeekPrehensile, a Sophisticated 3D Printable Prosthetic Hand
Lately, we have seen some of the most exciting developments in the futuristic manufacturing industry. Irrespective of you being a specialized professional...
-
 353News
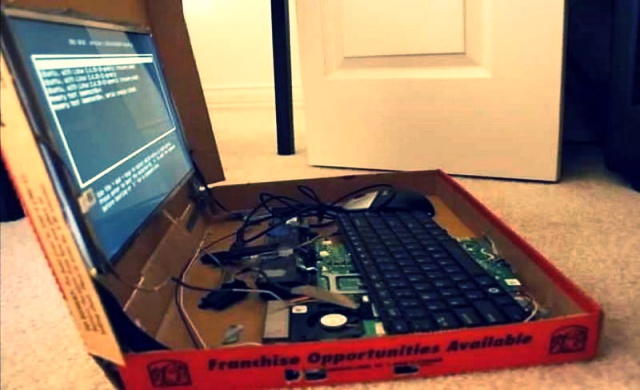
353NewsPizza Hut Israel Website Hacked with a Warning for Indian Government
You’ve seen us posting news about pro-Palestinian hackers targeting Israeli sites or vice versa, but did you ever think of Bangladeshi hackers...
-

 456Privacy
456PrivacyT‑Mobile received the most US data requisition requests
Telco T-Mobile’s US arm received more data requests than its larger peers in 2014.
-
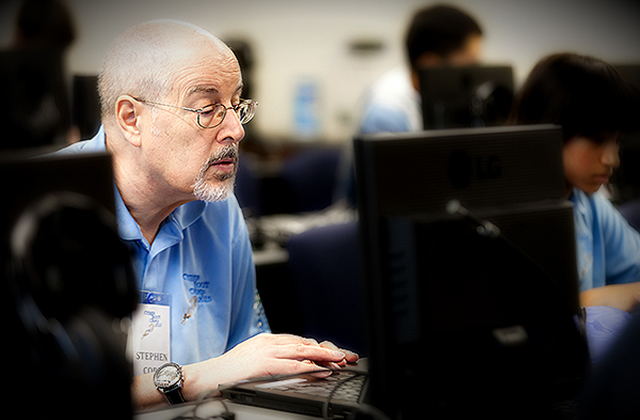
 90Kids Online
90Kids OnlineWhat I learned at Cyber Boot Camp (Instructor Edition)
Teaching computer security to highly motivated students at Cyber Boot Camp reveals a lack of basic computer science education in California Schools.
-

 197Hacked
197HackedRussian Superweapon That Can “Switch Off” All Enemy Satellites
A Topol-M missile on MZKT-79221 mobile launcher (Image: Wikipedia) With the ever advancing technology, the modes of warfare have also developed with...
-
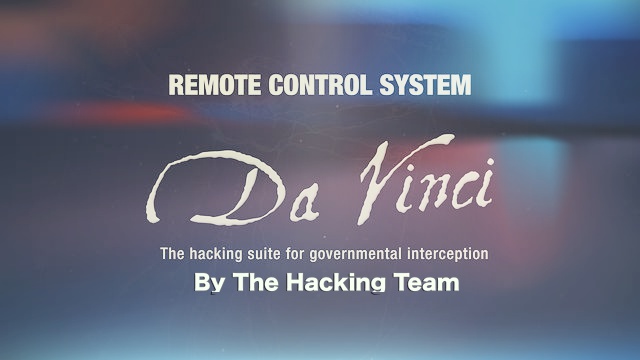
 247News
247NewsHacking The Hacking Team Shows Regimes Love Spying on Its Citizens
The Italy-based security firm Hacking Team, known for providing spying tools to the Drug Enforcement Administration (DEA) in U.S has been hacked. ...
-

 215How To
215How ToHow To Create A Simple Batch File For Windows
Hackers can create very dangerous batch files which can destroy your computer but here we are going to teach you on how to...
-

 286Geek
286GeekRaspberry Pi DIY: How to Preserve and Sync Data in a Mason Jar Using Pi
Enough about storing your data on world’s smallest 128GB memory card or some other invention poised to be the next HDD-killer. Today,...
-
 85Hacked
85HackedHousing.com Site Hacked, Rahul Yadav Says It’s not him
Housing.com is one of the big names in Indian real estate arena that you would encounter if you are looking for a...
-

 106Cyber Crime
106Cyber Crime400GB of info leaked from Hacking Team
The “Hacking Team” Security Company has been hacked and more than 400 GB of confidential info has been leaked by a group...
-

 287Hacked
287HackedHacking Team Becomes “Hacked Team”, Firm Sold Spying Tech to Governments
Hacking Team, a controversial company from Italy which specializes in selling powerful surveillance equipment to governments and their enforcement agencies, has been...
-
 242Geek
242GeekWatch People Code and Learn for Free on Livecoding.tv
Do you want to code, find a direct way to communicate with the like-minded people and get some type of mentorship? Are...
-

 269Data Security
269Data SecurityMasterCard Plans to Use Selfies to Authenticate Online Transactions
Protecting customers from fake online transactions has always been a challenging task for the company’s security division, which has forced a popular...
-

 354Hacked
354HackedHow Do Cyber Criminals Steal Your Money?
Image: shutterstock Today is the world where people worry less about getting mugged on street and more on the internet. With the cyber...
-

 199Data Security
199Data SecurityDude Finds Flaw in World’s Biggest Gambling Site, Steals $1M in Bitcoin
An online gaming/gambling site lost $1 million in bitcoin to an attacker who exploited its random number generation (RNG) system. A leading...
-

 349Data Security
349Data SecurityNew Spam Campaign Spreading Dridex Banking Malware
The latest spam campaign is equipped with the Dridex banking malware and targeting company accountants through deceptive emails. According to Heimdal Security,...
-

 220Cyber Crime
220Cyber CrimeWomen More Vulnerable to Phishing Scams: This Lady Lost Her Life Savings
Studies show women are more vulnerable to phishing scams than men and same has happened with Vivian Gabb who told media how she...
-
 201Cyber Crime
201Cyber CrimeHackers Steal $5 Million Worth of Bitcoin with A Simple Phishing Attack
Back in the month of January, one of the most popular bitcoin exchange namely BitStamp was hacked which resulted in the stealing...
The Latest
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications
-
 Malware
MalwareNSA, FBI Alert on N. Korean Hackers Spoofing Emails from Trusted Sources
-
 Vulnerabilities
VulnerabilitiesFour Critical Vulnerabilities Expose HPE Aruba Devices to RCE Attacks
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Vulnerabilities
VulnerabilitiesWhen is One Vulnerability Scanner Not Enough?
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Vulnerabilities
VulnerabilitiesNew “Goldoon” Botnet Targets D-Link Routers With Decade-Old Flaw
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareZLoader Malware Evolves with Anti-Analysis Trick from Zeus Banking Trojan
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024




