Featured News
-

 330Hacked
330HackedHow To Set-up VPN on Android Devices (No Software Needed)
Public Wi-Fi networks seem really convenient don’t they! Whether you are at McDonald’s (or just any other food joint offering an open...
-

 217Hacked
217HackedFacebook is Probably Tracking Your Rainbow Profile Picture
The US Supreme Court ruling to legalize gay marriages all across the nation was a revolutionary step and it was received with...
-

 218Cyber Events
218Cyber EventsRussian MP Sick of LGBT Rainbow Flag Wants Facebook Blocked
The sitting MP of the regional parliament of Saint Petersburg, Vitaly Milonov, has introduced a new law to shut down the social...
-
 232Operating Systems
232Operating SystemsReview of Parrot OS
Parrot Security OS is a security oriented operating system designed for Pentesting, Computer Forensic, Reverse engineering, Hacking, Cloud pentesting, privacy/anonymity and cryptography....
-
 130News
130NewsHacker Series – Enough to motivate you?
With the amount of hackers expanding in the modern world, so does TV shows start to react. Time to get your ‘mode’...
-

 244Hacked
244HackedOne of the Best Anti-Virus Malwarebytes Offers Free 1-Year Premium Keys
“The Internet is full of pioneers and cowboys. It’s also got its fair share of pirates and trolls.” Piracy is the biggest...
-

 114Privacy
114PrivacyICANN policy changes trigger privacy concerns
Internet name authority ICANN has unsettled privacy advocates after a new working group document flagged changes to the way domain proxy services...
-

 196Surveillance
196SurveillanceUsing Drone for Abortion: Here Comes The Abortion Drone
Dutch based campaigners are focusing on women’s access to “easy and safe” method to bring an end to pregnancy with the help of...
-

 179Lists
179ListsTop 5 Supercomputers Of The World
Courtesy: Prof. Jack Dongarra Supercomputers of today are the retrogressive image of the one’s in 1960s i.e. a gigantic machine racking up an...
-

 177Surveillance
177SurveillanceHackers Posting Nude Pictures of Women without Their Knowledge
Nude pictures of more than 700 Aussie females leaked online without their permission or knowledge. An individual hosting the cache in a cloud...
-

 238News
238NewsHackers Target Gospel News Portal, Leave LGBT Flag Behind
The U.S supreme court yesterday ruled in favor of same-sex marriages nationwide. Some are celebrating and some are unhappy with the ruling, but...
-
 205Operating Systems
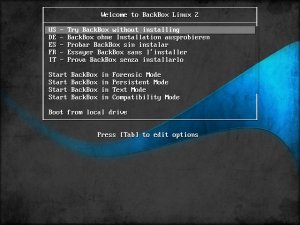
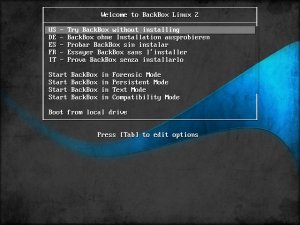
205Operating SystemsBackbox – Turning heads in the pentesting scene
A relative newcomer to the forensic and penetration testing live CD scene, Italian project BackBox is already turning heads as it hits...
-

 217Android Hacking
217Android HackingTurning your Android into a hacking device
Now days, smartphones and tablets are the most popular gadgets. The reason behind this is that people utilize tablets for most of...
-
 330How To
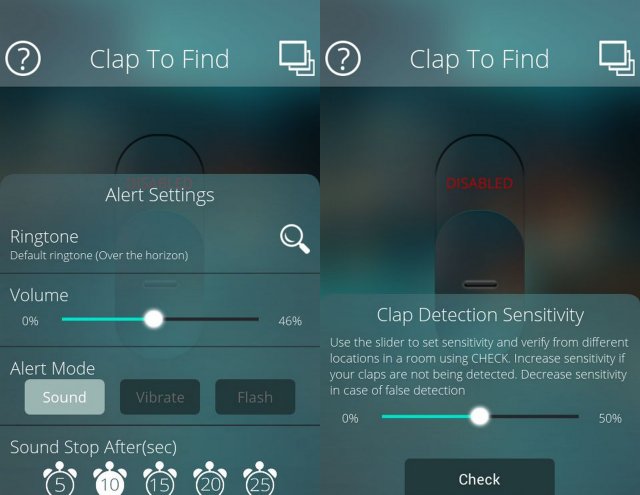
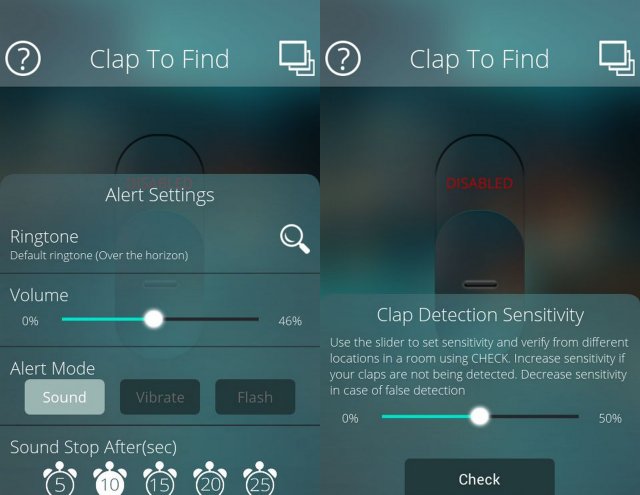
330How ToHow to find your Silent Phone in a room without Internet
When busy with an important task, people like to put the mobile phone on Silent Mode. But what if you misplaced your...
-

 233Lists
233ListsMIT Lists 50 Smartest Companies That Owned the Year 2015
Short Bytes: This is an era of technological amelioration and every tech giant is striving to be the best. This article presents...
-
 119Hacked
119HackedHow To Remove Your Embarrassing Photos From All Social Media Websites
Work Hard and Party Even Harder. That’s the byword of today’s generation. Most of us have the same motto, myself being its hardcore...
-
 438Hacked
438HackedWatching Porn In Incognito Mode In Your Browser Isn’t As Safe As You Think
Short Bytes: The web browsers we use are shipped with settings that promise private browsing to the users. In Google Chrome, this...
-
 128Geek
128GeekRacket-lang: A Programmable Programming Language
You must have read our coverage on programming language and its development. If not, I would recommend you to go through it once....
-
 280Geek
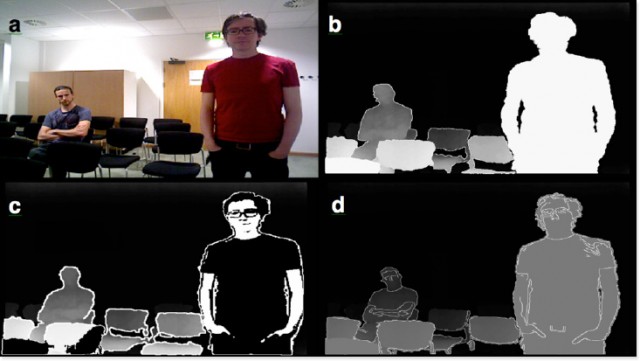
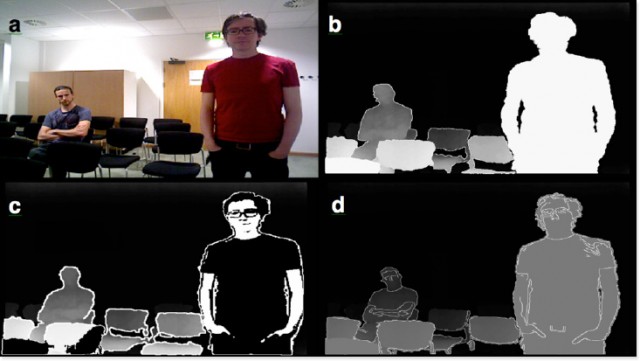
280GeekThese Wearable Glasses Lets Legally Blind People See Again
SmartSpecs are wearable glasses developed by Startup VA-ST using augmented reality so that visually impaired could see clearly once again. A University...
-

 200Geek
200GeekFacebook Algorithm Recognise You in Images Even if You’re Not Looking
Facebook’s new Algorithm powerful enough to identify you even if you aren’t looking at the camera. Facebook’s AI/artificial intelligence lab introduced an...
The Latest
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications
-
 Malware
MalwareNSA, FBI Alert on N. Korean Hackers Spoofing Emails from Trusted Sources
-
 Vulnerabilities
VulnerabilitiesFour Critical Vulnerabilities Expose HPE Aruba Devices to RCE Attacks
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Vulnerabilities
VulnerabilitiesWhen is One Vulnerability Scanner Not Enough?
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Vulnerabilities
VulnerabilitiesNew “Goldoon” Botnet Targets D-Link Routers With Decade-Old Flaw
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Data Breach
Data BreachHow to Make Your Employees Your First Line of Cyber Defense
-
 Malware
MalwareZLoader Malware Evolves with Anti-Analysis Trick from Zeus Banking Trojan




