Featured News
-

 286Data Security
286Data SecuritySecurity Flaw in Samsung Keyboard Puts 600m Android Devices Vulnerable
Android phone users have long shared the view that, despite the continual announcements of ongoing security breaches in an evermore technological world,...
-

 113Password
113PasswordUK Consumers willing to share DNA with banks to secure identity
Consumers in the UK would be happy to share their DNA if it would help secure their financial and personal information, according...
-

 267Cyber Crime
267Cyber CrimeOnline Predators Hunting Users with Video Chat Extortion Scams
In October last year, we reported how a 10-year-old filipino virtual girl “sweetie” takes pedophile to prison in Australia for good. Now a...
-

 82Cyber Crime
82Cyber CrimeTop US baseball team accused of hacking rival
The St. Louis Cardinals, one the United States's top major league baseball teams, is being investigated for allegedly hacking into the computer...
-

 275News
275NewsLithuanian Armed Forces Website Hacked, Defaced with False Information
Someone hacked the official website of Lithuanian Armed Forces and posted false information about NATO ready to attack Kaliningrad Oblast. A group of unknown...
-

 314Cyber Crime
314Cyber CrimeBeware of New ‘Forbidden Content’ Facebook Phishing Scam Hitting Inbox
Another day, another Facebook phishing scam — Facebook users must be cautious since a new phishing scam message is circulating on the...
-
 300Geek
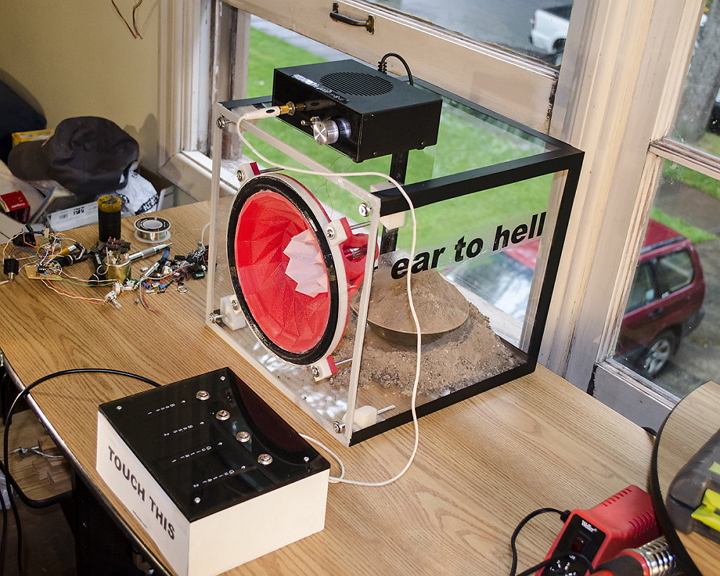
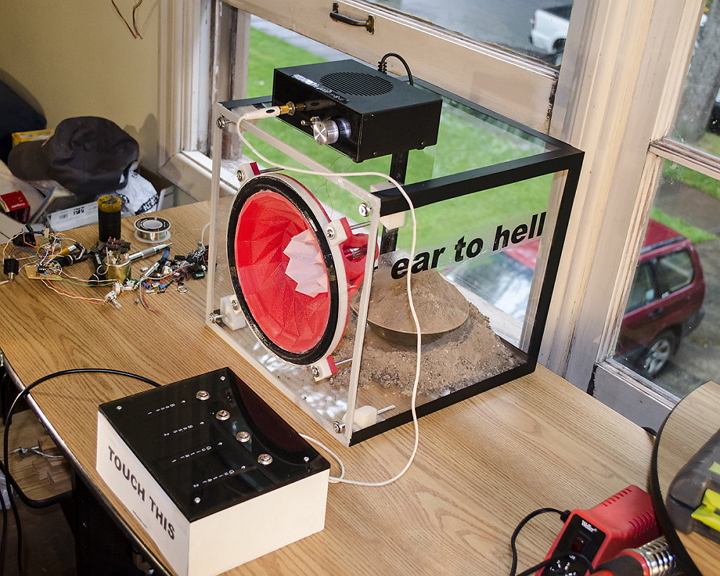
300GeekHere’s a 3D Printed Remaking of ‘Ear of Hell’ Classic Audio Speakers
A San Francisco Bay Area based artist and designer Ted Kessler has always yearned to merge art with science. A bachelor in...
-
 319Data Security
319Data SecurityHackers Used ‘Stolen Foxconn certs’ to Hack Kaspersky Via Duqu 2.0 Malware
‘Stolen Foxconn certs’ used for embedding Duqu 2.0 malware into Windows PC — The crafty super-sophisticated malware infiltrated Kaspersky Labs. Reportedly, Duqu...
-

 110Privacy
110PrivacyEU data protection regulation overhaul inches closer
The 28 EU member states have taken a significant step towards a historic overhaul of EU-wide data protection laws, first proposed three...
-

 238Geek
238GeekFacebook launches new photo sharing App, Moments
Do you remember asking your friend with a Camera on a Trip to share the photographs with you? Or do you remember...
-

 377Hacked
377HackedAnonymous is Supporting New Social Network “Minds”: Facebook’s Latest Challenge
Just when you thought that you’ve had enough social networking today and you definitely need a new social network around, here comes...
-
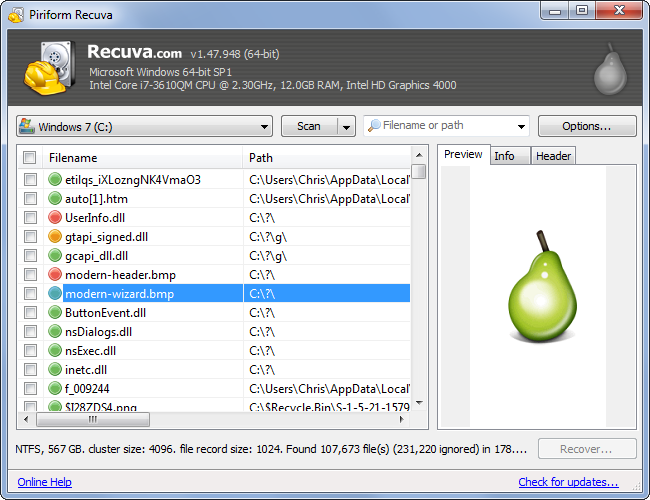
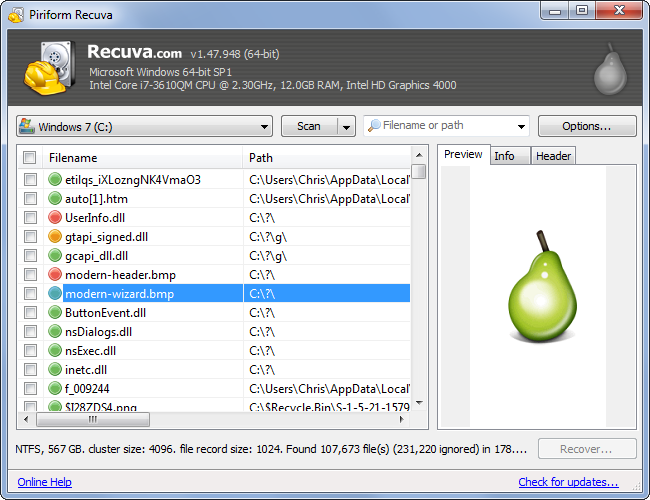 221Computer Forensics
221Computer ForensicsRecovering your Deleted Files
It has happened to most of us. You deleted a file and realize you need it back. But is it really deleted?...
-

 114News
114NewsUber Petition Website Hacked- Hacker Uploaded Ad of Rival Firm Lyft
Due to a security flaw, researcher Austin Epperson took control of a page of Uber’s website and displayed the ad of its arch-rival...
-

 262News
262NewsLeading Password Security Company LastPass Hacked
Joe Siegrist from LastPass, a famous password manager program, admitted that its database comprising of email addresses, server per user salts, password...
-

 208Password
208PasswordPassword security firm LastPass compromised
Popular online password vault provider LastPass has warned users to update their master account passwords after their network was hacked.
-

 117How To
117How ToA beginner’s guide to starting in InfoSec
Much ink has been spilt about the shortage of people trained in information security – especially the lack of women in the...
-

 267Cyber Crime
267Cyber CrimeNew Facebook Phishing Scam Posts Links on Friends Timeline
Facebook timelines nowadays are displaying a new phishing scam message with the title “Here’s the Link HeHe.” The text of this scam...
-
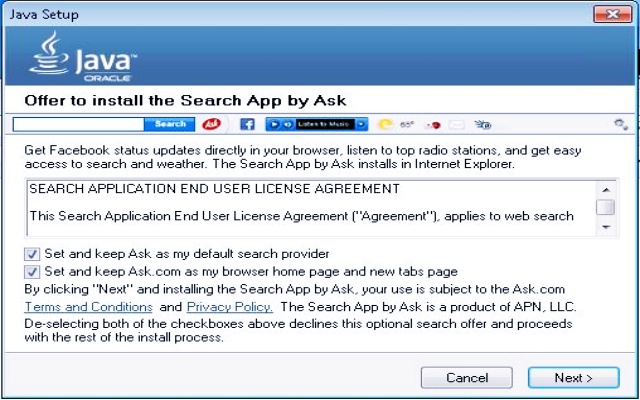
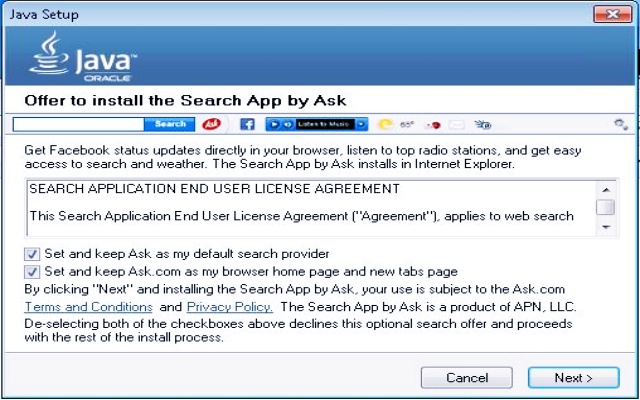 178Data Security
178Data SecurityMicrosoft Declares Ask toolbar as Dangerous Malware
In April 2015, we reported how Ask.com toolbar is working as a malware to hijack your computer. Now proving our claim right, previous...
-
 210Surveillance
210SurveillanceGood News for Wikipedia Readers- Encrypted Connections Coming Soon
Awesome News for Wikipedia Readers- Encrypted Connections Coming Your Way Pretty Soon. Currently, data between users and Wikipedia.com is unencrypted, and this increases...
-

 234Data Security
234Data SecurityUnpatched Security Flaws Openly Solicited by US Navy
Governments unsurprisingly are trying to buy unpatched security exploits in the name of surveillance or cyber defence but refrain from admitting it....
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




