Featured News
-
 428How To
428How ToHow to Get Free Genuine Windows 10 Even If You Don’t Have Windows 8 or 7
It’s an old news that Windows 10 will be available as a free download to Windows 7 and Windows 8 users. This...
-
Hacking Tutorials
How to inbox Facebook users from anyone’s account
Facebook hacking has been a major “topic” for the curious user,but today i’ll be focusing on an easy trick to send messages...
-

 238News
238NewsWikiLeaks Releases 275k+ Hacked Sony Documents
WikiLeaks, a whistle-blowing site has published 276,394 new docs taken from Sony in Nov by an anonymous attacker. It adds to the...
-
 304Geek
304GeekDivorced Man Cuts all his Stuff in Half to share Belongings with Ex-wife
Remember that Russian paramedic Tatiana Kulikova? Remember her habit of taking selfies with Dying Patients and uploading them on social media? Well, she was...
-

 203Geek
203GeekIs Anonymous Trying to Create its own Social Network?
Facebook’s current rival apparently being backed by the famous hacker group Anonymous. A new social network is hoping to surpass Facebook and other...
-

 238Hacked
238HackedDuckDuckGo Search Traffic Grows by 600% After NSA Leaks
Since the last two years, the privacy focused search engine DuckDuckGo has witnessed a phenomenal 600% growth. The search engine was launched...
-

 336How To
336How ToHow To Recover Deleted Contacts From Android Phone?
Did you ever face a problem of losing your contacts from your Android phone? Ahh…it really gets me when I accidentally delete...
-
 182Privacy
182PrivacyReddit goes HTTPS, joins Wikipedia at security table
Popular meme site Reddit has announced that it will soon encrypt all traffic with HTTPS by default.
-

 128Geek
128GeekHackerville: Inside the World’s Most Dangerous Town
Have you ever heard of a small town named Râmnicu Vâlcea from Romania? I’m pretty sure that your answer is no. This...
-

 280Geek
280GeekGetting Started with Linux: Part II (Installation and more)
Read the Part 1 and Part 3 of Getting Started with Linux : Choosing the desired Linux distribution and Command Line After downloading a...
-

 281Surveillance
281SurveillanceTeen Tracking Lost Phone Using App Shot Dead
Teen shot dead while using mobile phone tracking app — All that it took to take the life of an innocent teen was a...
-
 111Opinion
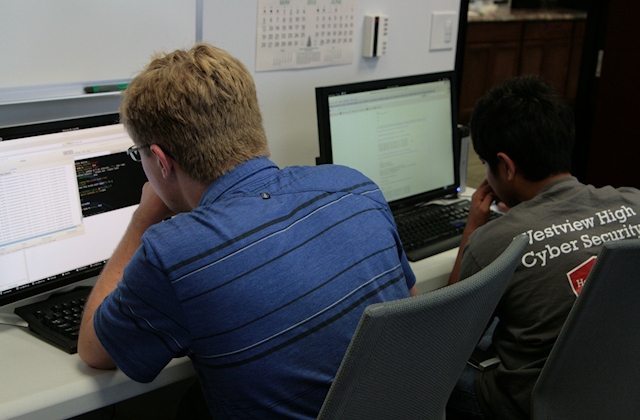
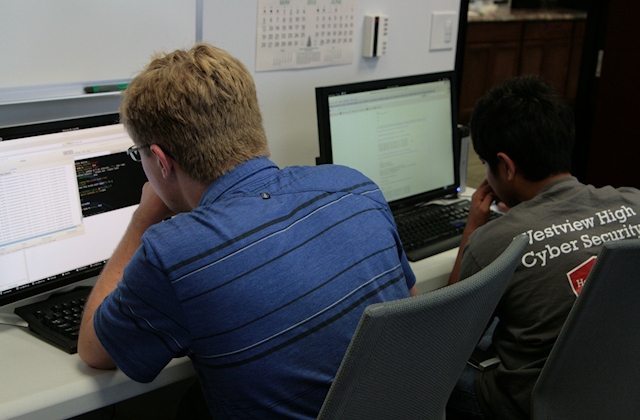
111OpinionCyber Boot Camp: a head start for tomorrow’s cyber workforce
Every June, a select group of students from high schools and middle schools in San Diego County, California, get five days of...
-
 120News
120NewsAnti-US Govt Surveillance Website by Microsoft Hacked
Microsoft, just like all other software companies, constantly asks its customers to update their applications on their computers to remain fully secure...
-

 116Privacy
116PrivacyDuckDuckGo traffic up after Apple integration and privacy issues
Privacy search engine DuckDuckGo has seen traffic rocket after recent widely publicized privacy scares, according to the company.
-

 201Hacked
201HackedMicrosoft’s Website to Fight Government Surveillance Just Got Hacked
Microsoft’s dedicated website to fight the US government surveillance and privacy breachings has just been hacked. While Microsoft is aiming to bring...
-

 270Geek
270GeekGoogle, Microsoft, Apple and Mozilla Working Together On WebAssembly For Faster Web
The genius minds at Google, Microsoft, Mozilla and Apple are coming together to create WebAssembly (also known as wasm). This is a...
-

 252Cyber Events
252Cyber EventsAnonymous Shuts Down Canadian Govt Websites Against Bill C-51
The online hacktivist Anonymous claimed responsibility for conducting DDoS attacks on Canadian government servers against the approval of anti-terror law C-51 that...
-
 278Data Security
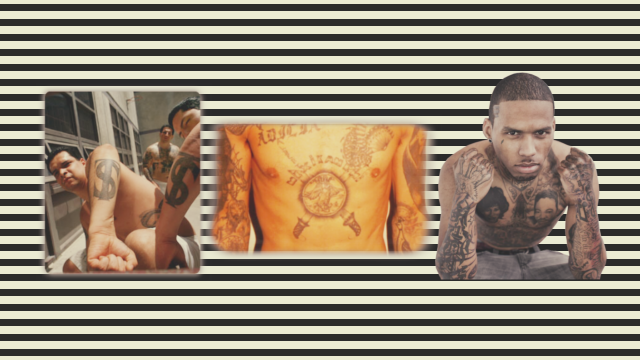
278Data SecurityTattoo Recognition System Could Identify Criminals Very Soon
Tattoo Recognition System is coming! Recently committed a crime? Do you happen to have a large visible tattoo? Then you could soon...
-
 299Geek
299GeekBelgian Watchdog Sues Facebook for Tracking Users
Facebook is in hot water. The social media giant is being taken to court by Belgium’s Privacy Commission (BPC), among accusations that...
-
 203Data Security
203Data SecurityEmojis To Be Your New Pin Codes
So long Password1234 or surname1, there is a new, more readily memorable password system on our doorstep — That is what Intelligent...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




