Featured News
-

 112Privacy
112PrivacyEU data protection regulation overhaul inches closer
The 28 EU member states have taken a significant step towards a historic overhaul of EU-wide data protection laws, first proposed three...
-

 240Geek
240GeekFacebook launches new photo sharing App, Moments
Do you remember asking your friend with a Camera on a Trip to share the photographs with you? Or do you remember...
-

 379Hacked
379HackedAnonymous is Supporting New Social Network “Minds”: Facebook’s Latest Challenge
Just when you thought that you’ve had enough social networking today and you definitely need a new social network around, here comes...
-
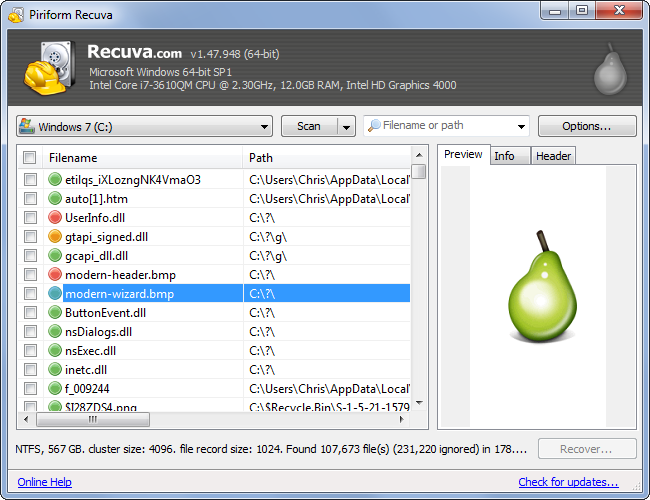
 224Computer Forensics
224Computer ForensicsRecovering your Deleted Files
It has happened to most of us. You deleted a file and realize you need it back. But is it really deleted?...
-

 116News
116NewsUber Petition Website Hacked- Hacker Uploaded Ad of Rival Firm Lyft
Due to a security flaw, researcher Austin Epperson took control of a page of Uber’s website and displayed the ad of its arch-rival...
-

 264News
264NewsLeading Password Security Company LastPass Hacked
Joe Siegrist from LastPass, a famous password manager program, admitted that its database comprising of email addresses, server per user salts, password...
-

 210Password
210PasswordPassword security firm LastPass compromised
Popular online password vault provider LastPass has warned users to update their master account passwords after their network was hacked.
-

 120How To
120How ToA beginner’s guide to starting in InfoSec
Much ink has been spilt about the shortage of people trained in information security – especially the lack of women in the...
-

 270Cyber Crime
270Cyber CrimeNew Facebook Phishing Scam Posts Links on Friends Timeline
Facebook timelines nowadays are displaying a new phishing scam message with the title “Here’s the Link HeHe.” The text of this scam...
-
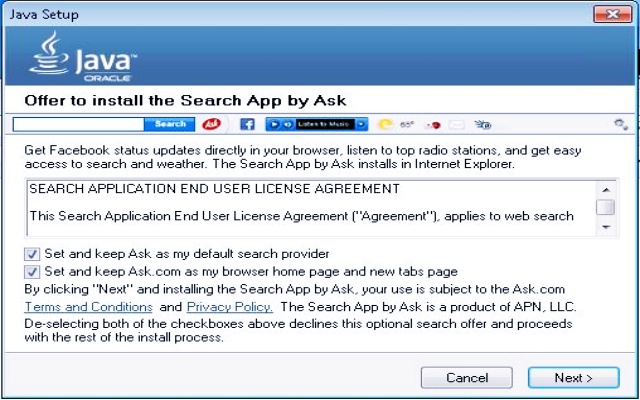
 180Data Security
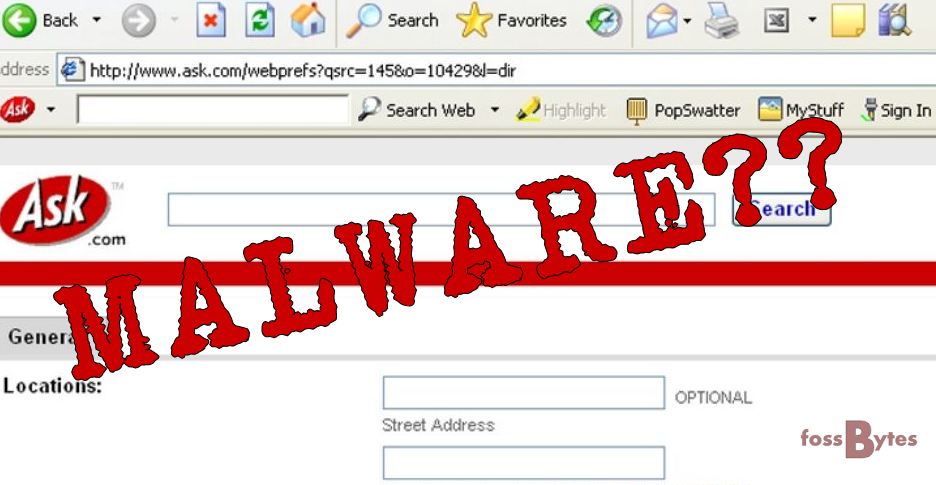
180Data SecurityMicrosoft Declares Ask toolbar as Dangerous Malware
In April 2015, we reported how Ask.com toolbar is working as a malware to hijack your computer. Now proving our claim right, previous...
-
 214Surveillance
214SurveillanceGood News for Wikipedia Readers- Encrypted Connections Coming Soon
Awesome News for Wikipedia Readers- Encrypted Connections Coming Your Way Pretty Soon. Currently, data between users and Wikipedia.com is unencrypted, and this increases...
-

 238Data Security
238Data SecurityUnpatched Security Flaws Openly Solicited by US Navy
Governments unsurprisingly are trying to buy unpatched security exploits in the name of surveillance or cyber defence but refrain from admitting it....
-

 518How To
518How ToHow To Get Windows 10 Upgrade Icon If Missing – Official Method by Microsoft
Microsoft is trying desperately to convince the users to upgrade their Windows 7 and Windows 8.1 PCs to the next iteration to...
-
 205How To
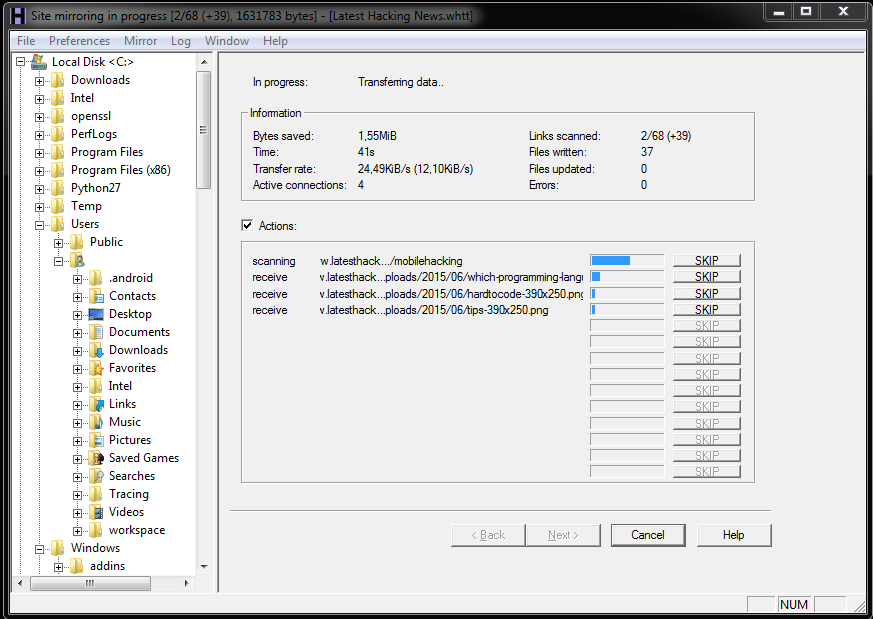
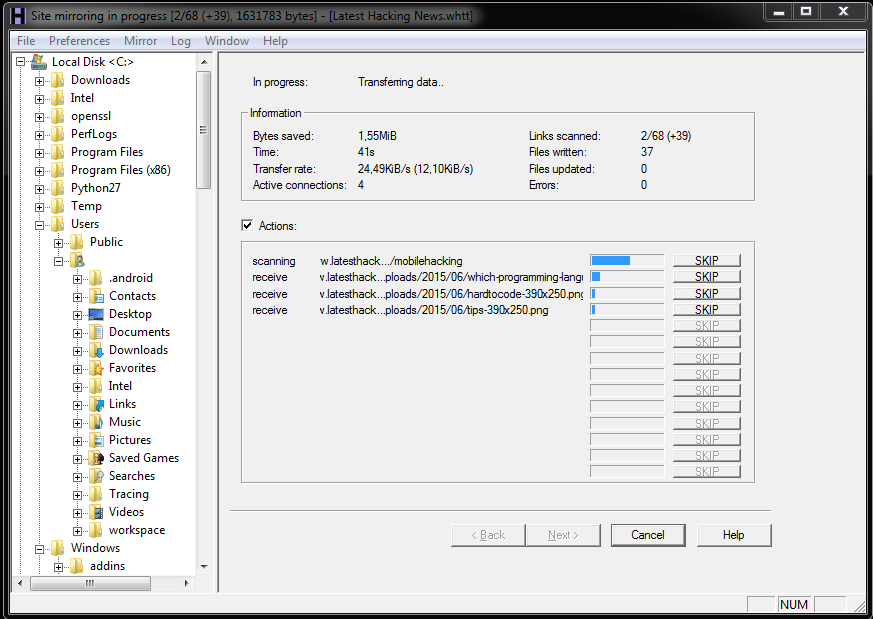
205How ToHow To Download And View Website Offline
Few times you have to give up on loading multiple website with slow internet connection or having problem with internet, or when...
-

 198Privacy
198PrivacyWikipedia switches to HTTPS by default
Wikimedia has announced that all of its web properties – including the enormously popular crowd-sourced dictionary Wikipedia – will now use HTTPS...
-
 226Hacked
226HackedAsk Toolbar in Your Browser is a Malware: Microsoft
The vintage Ask toolbar that you can spot in your computer’s web browser has now been termed as threat to your PC...
-
 163Tricks & How To's
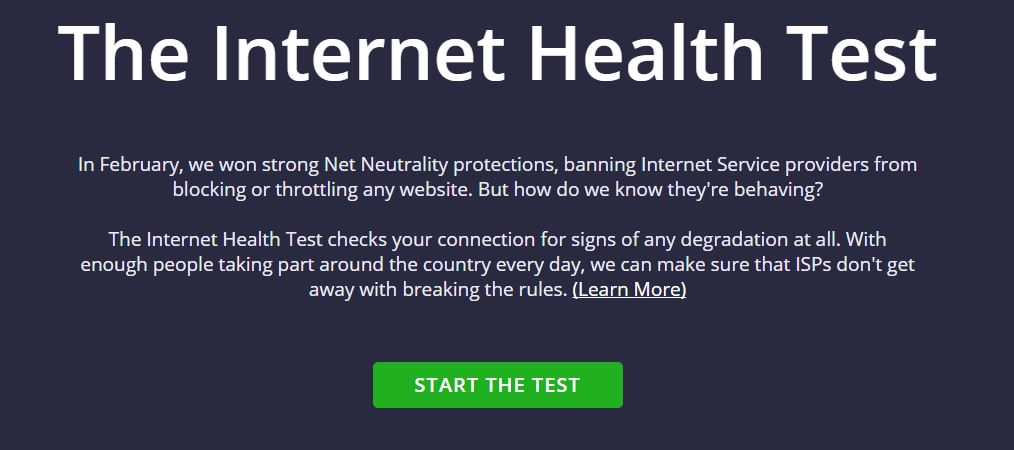
163Tricks & How To'sHow to check whether your ISP is Throttling your Internet speeds.
You, the usual and the average consumer, doesn’t know the boundaries that define the exploitation when it comes to the net neutrality...
-

 310How To
310How ToA Complete Guide On Facebook Tips And Tricks
Who would have thought something that started as a mischief could go on to become the heart of a billion people’s social...
-

 291Data Security
291Data SecurityHacker Targets Pedophiles with TOX Ransomware
Tox is yet another example of cyber justice that has been meted out by cyber criminals. In this case, Tox sends a...
-

 188Geek
188GeekNew Computer Algorithm Learns Rap Lyrics and Writes Its Own Rap Song
Have you ever wondered how musicians write music? Do you think it’s possible to technically generate a composition and write lyrics to...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




