Featured News
-
 124Geek
124GeekRacket-lang: A Programmable Programming Language
You must have read our coverage on programming language and its development. If not, I would recommend you to go through it once....
-
 271Geek
271GeekThese Wearable Glasses Lets Legally Blind People See Again
SmartSpecs are wearable glasses developed by Startup VA-ST using augmented reality so that visually impaired could see clearly once again. A University...
-

 196Geek
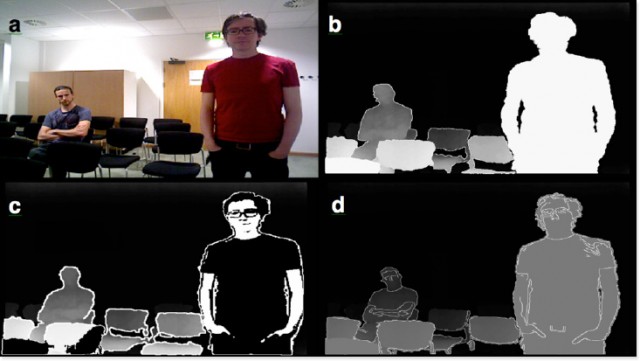
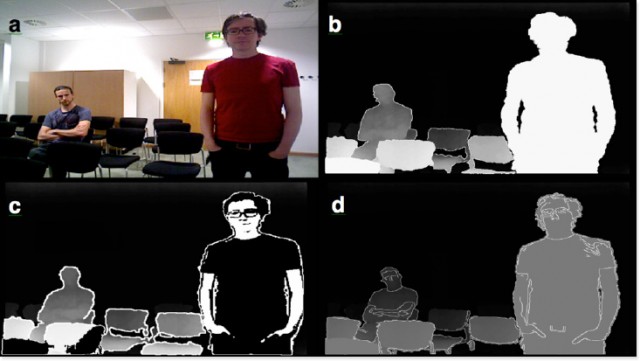
196GeekFacebook Algorithm Recognise You in Images Even if You’re Not Looking
Facebook’s new Algorithm powerful enough to identify you even if you aren’t looking at the camera. Facebook’s AI/artificial intelligence lab introduced an...
-

 113News
113NewsCredentials of over 47 U.S Government Agencies Leaked on the Internet
Reportedly, login credentials of around 47 U.S government institutions across 89 different domains have been leaked. Apparently, in the earlier part of...
-
 206Surveillance
206SurveillanceSecret Audio Recording Exposes Doctors Making Fun of Patient’s Penis
Patient Records Audio While being Operated- Hears doctors Making Fun of His Penis. You surely wouldn’t expect doctors to laugh at your...
-

 276Reviews
276ReviewsBayangtoys X7 Quadcopter is Your Ultimate Affordable Flying Machine
We have been writing about various types of drones from a long time on fossBytes and in the continuously expanding drone universe,...
-

 144Scams
144ScamsPhone Scams: Increasing Numbers, Wider Scope
There's a lot more to phone scams than tech support, giving rise to an escalating number of complaints. Here's what two recent...
-
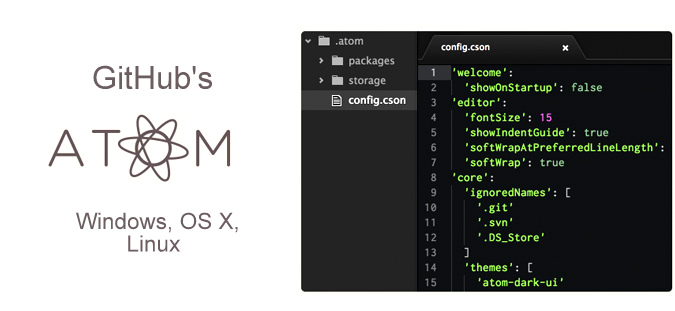
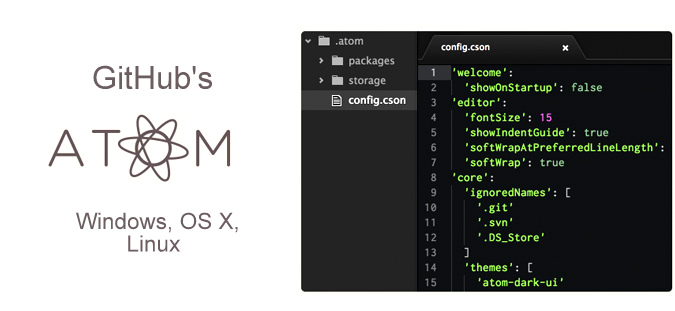 276Geek
276GeekGitHub’s Very Own Hackable Text Editor Atom Hits 1.0, Get it Now
About eighteen months ago, GitHub launched its homegrown text editor named Atom. Atom was a result of about six years of research...
-

 241News
241NewsOpBillC51: Anonymous Hacks Police Association of Ontario, Leaks Trove of Data
When Anonymous goes against you, there’s no way out! Same is going on with Canadian government who’s constantly under cyber attack against...
-

 261Data Security
261Data SecurityFacebook Join Forces with Kaspersky to Spot Malware on Computers
The problem with Facebook is thousands of active phishing scams but the social media giant has partnered with popular security software developer firm...
-
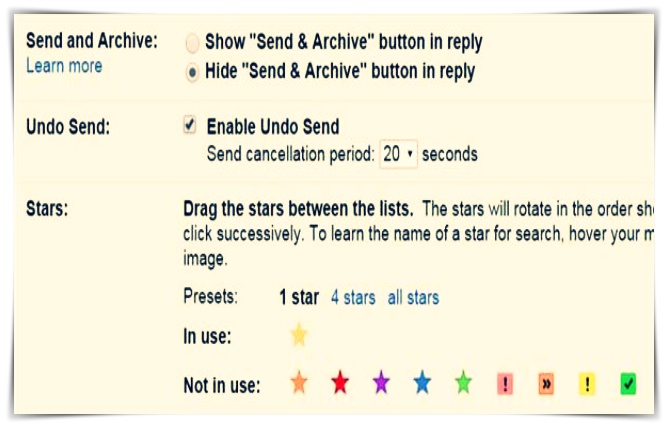
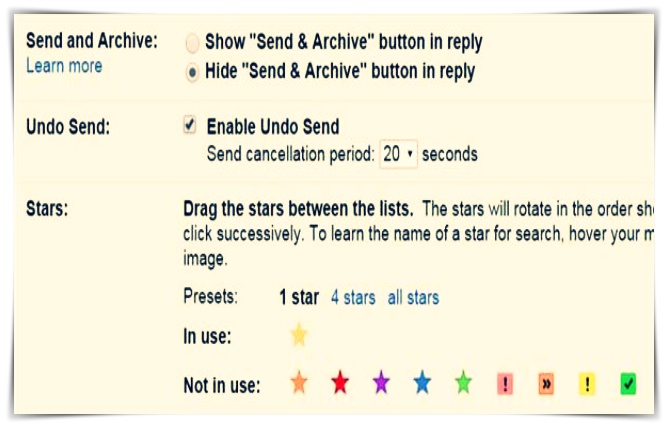 493Geek
493GeekDon’t Worry About Typo, Gmail Users Can ‘Undo Send’ Emails
In 2013, we came up with a tutorial on How to undo sent emails on gmail. Now a new email tool has...
-

 264Geek
264GeekU.S Army to be Equipped with Hoverbikes
U.S Defense Department, as well as its security agencies, have always wanted UK style hoverbikes that although perform all the functions that...
-
 145How To
145How To4 tips for recovering from an attack
Recent high-profile data breaches have illustrated criminals’ insatiable appetite for data and financial reward. Here's some information on what to do after...
-

 103Privacy
103PrivacyNew iPhone update blocks apps from seeing other apps you’ve installed
Apple will reportedly introduce a new privacy update for the iPhone that will prevent installed iOS apps from seeing which other apps...
-
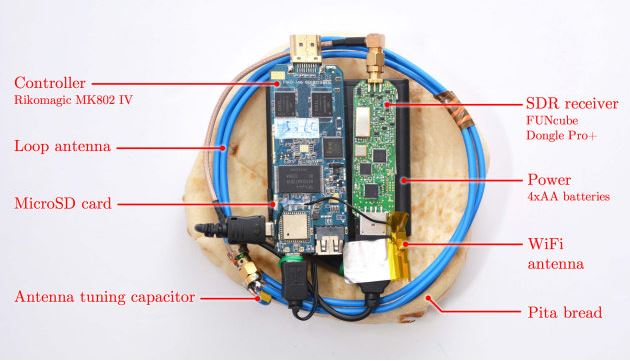
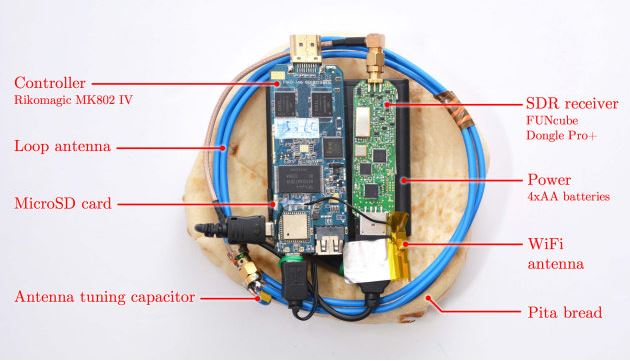 240Hacked
240HackedA Homemade Device That Can Steal Keys and Hack Data From Your PC: PITA
When someone talks about stealing some data from a PC, what is the suspected source according to you? You may end up...
-
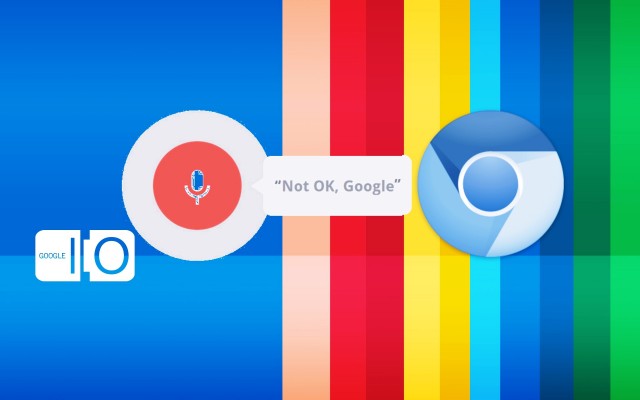
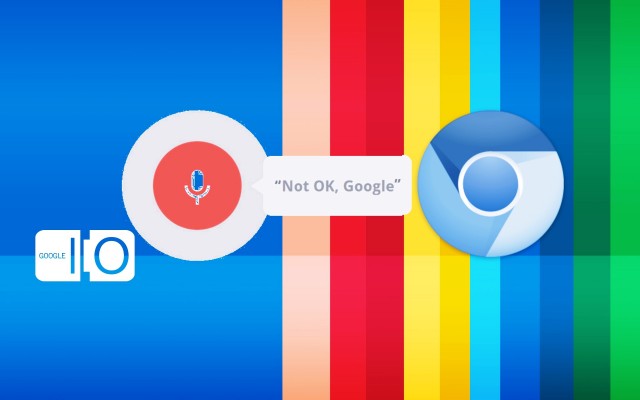 404Surveillance
404SurveillanceGoogle Chrome Browser Listening To Your Conversations without Permission
Recently, a researcher revealed that Google might be spying on all of its Chromium web browser users by stealth downloading audio listeners...
-
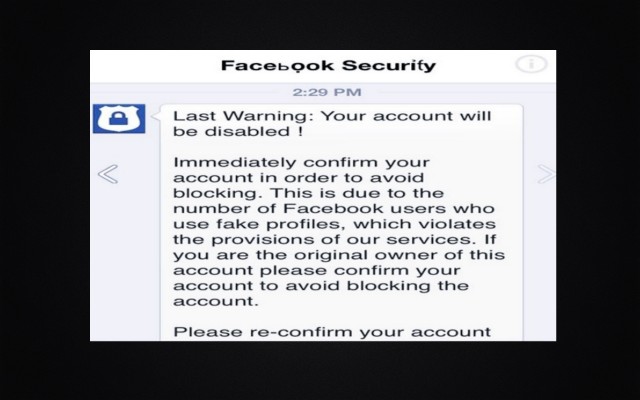
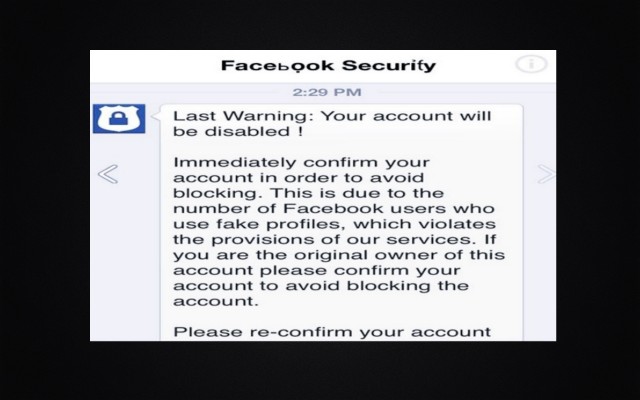 245Cyber Crime
245Cyber Crime“Last Warning – Your Account Will Be Disabled”, Another Facebook Phishing Scam
Another day, another Facebook phishing scam — The email claims to be sent by Facebook Team and warns recipients that they have...
-

 179Hacked
179HackedGoogle Finally Removes ‘Revenge Porn’ From Search Results
For people who have been hit by the menace of revenge porn, a recent announcement by Google will bring some relief. Google...
-

 300Operating Systems
300Operating SystemsReview of Kali Linux – The Successor of backtrack
Kali Linux is a penetration testing and security auditing Linux distribution. After its release in March 2013, Kali Linux has quickly become...
-

 195Hacked
195HackedSamsung Quietly Disabling Windows Update, Risking Systems Open to Hackers
You are using your laptop and it has a software updater tool – what do you expect it to do? You expect...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




