Featured News
-

 104Cyber Crime
104Cyber Crime400GB of info leaked from Hacking Team
The “Hacking Team” Security Company has been hacked and more than 400 GB of confidential info has been leaked by a group...
-

 287Hacked
287HackedHacking Team Becomes “Hacked Team”, Firm Sold Spying Tech to Governments
Hacking Team, a controversial company from Italy which specializes in selling powerful surveillance equipment to governments and their enforcement agencies, has been...
-
 239Geek
239GeekWatch People Code and Learn for Free on Livecoding.tv
Do you want to code, find a direct way to communicate with the like-minded people and get some type of mentorship? Are...
-

 268Data Security
268Data SecurityMasterCard Plans to Use Selfies to Authenticate Online Transactions
Protecting customers from fake online transactions has always been a challenging task for the company’s security division, which has forced a popular...
-

 352Hacked
352HackedHow Do Cyber Criminals Steal Your Money?
Image: shutterstock Today is the world where people worry less about getting mugged on street and more on the internet. With the cyber...
-

 198Data Security
198Data SecurityDude Finds Flaw in World’s Biggest Gambling Site, Steals $1M in Bitcoin
An online gaming/gambling site lost $1 million in bitcoin to an attacker who exploited its random number generation (RNG) system. A leading...
-

 348Data Security
348Data SecurityNew Spam Campaign Spreading Dridex Banking Malware
The latest spam campaign is equipped with the Dridex banking malware and targeting company accountants through deceptive emails. According to Heimdal Security,...
-

 218Cyber Crime
218Cyber CrimeWomen More Vulnerable to Phishing Scams: This Lady Lost Her Life Savings
Studies show women are more vulnerable to phishing scams than men and same has happened with Vivian Gabb who told media how she...
-
 200Cyber Crime
200Cyber CrimeHackers Steal $5 Million Worth of Bitcoin with A Simple Phishing Attack
Back in the month of January, one of the most popular bitcoin exchange namely BitStamp was hacked which resulted in the stealing...
-

 207Hacked
207Hacked20-year-old Trojan King Revealed, Maker of over 100 Banking Trojans
A 20-year-old Brazilian kid has been revealed as the maker of more than 100 banking trojans by the security firm Trend Micro....
-

 311Hacked
311HackedXKEYSCORE: NSA’s Search Engine to Hack Into Your Lives is as Simple as Google
We all know NSA is powerful. Getting into your email accounts and accessing all the private information that include your pictures, voice...
-
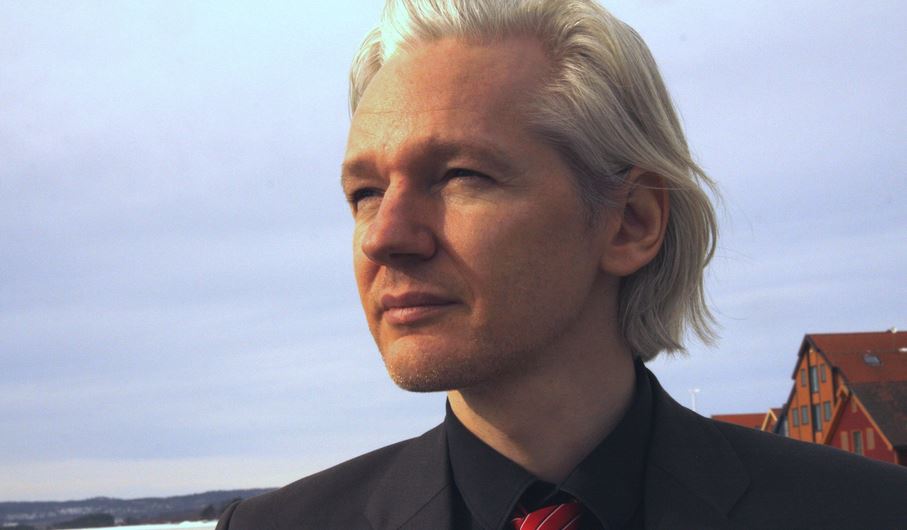
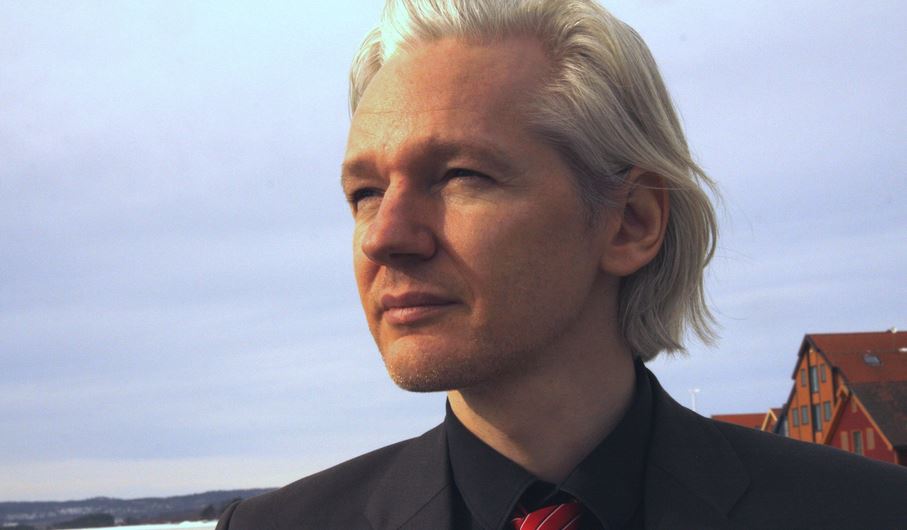 296Hacked
296HackedWikiLeaks Founder Julian Assange’s Protection Request Denied by France
WikiLeaks founder Julian Assange has revealed many controversial documents in the past couple of weeks related to Germany and France. Recently he...
-

 297Data Security
297Data SecurityHackers Develop Android Malware Every 17 Seconds
By the first quarter of 2015, hacker/cyber-attackers have optimized their efforts to design Android Malware to such an extent that every seventeen...
-

 174News
174NewsPrivate Messages Leaked after Plex Forums Hack
Plex Media Sever forum’s registered users received an email from the firm announcing that a breach of their system has exposed private...
-
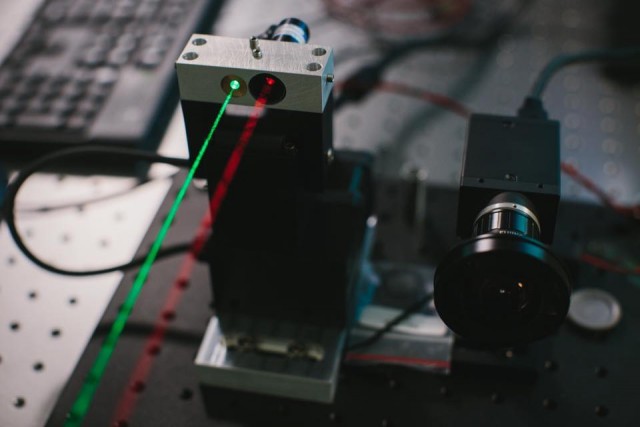
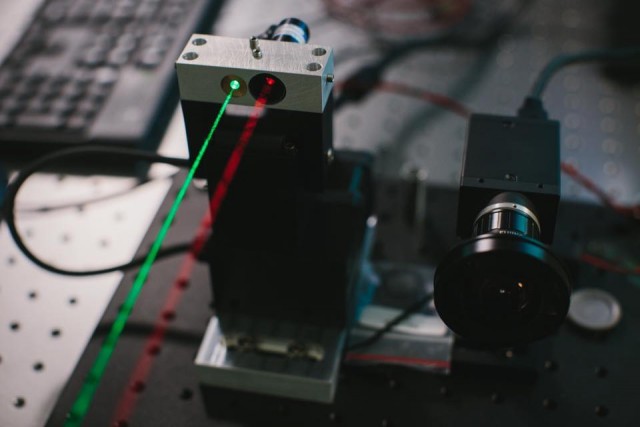 210Geek
210GeekDon’t have Internet Access? Facebook Laser Beam will Bring it to you
Mark Zuckerberg vows to make Internet and Facebook available in remote communities through LASERS — Facebook Laser Beam is coming. Mark Zuckerberg, Facebook’s...
-

 338How To
338How ToTop 20 Best Google Search Tips and Tricks That You Must Know
Web search has become synonymous with Google search. Other search engines like Bing and Yahoo are trying their best to give a...
-

 166Data Security
166Data SecurityAnonymously Access Wi-Fi Located Up To 2.5 Miles Away Using This Device
In this era of government surveillance, remaining anonymous has become next to impossible for every Internet user. There is almost nothing we...
-

 191Password
191PasswordMastercard trials selfies as password replacement
A new app could see Mastercard accepting selfies instead of passwords to make purchases online.
-

 178How To
178How ToHow To Get More Likes On Facebook Posts
While you share an incredibly happy moment or a deep thought on social media or change to a new dashing profile picture,...
-

 97Cyber Events
97Cyber EventsExclusive: Anonymous Breaches Canadian Government Servers Again!
Not so long ago, Canadian servers were working under peace, but after the approval of controversial anti-terror bill C-51, there’s no peace...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




