Featured News
-

 926Cyber Crime
926Cyber CrimeBarclays compensates customers after personal data trove uncovered
Barclays bank is to pay out around £500,000 in compensation to 2,000 customers whose personal data was found on a USB stick...
-

 208Geek
208GeekAmazon Launches AWS Device Farm, Now Test Your Apps on Real Devices
To benefit the hard-working app developers and programmers, Amazon is starting a cloud-based service named AWS Device Farm. AWS Device Farm will...
-

 168Lists
168Lists10 Reasons Why You Should NOT Work for Facebook
Today, Facebook is one of the biggest company to work for. The name itself creates an aura around you (if you are...
-
 345Hacked
345HackedWebsite of ISRO’s Commercial Arm Antrix Hacked by Chinese Hackers
The website of Indian Space Agency ISRO’s commercial wing Antrix Corporation was hacked on Sunday. This attack comes two days after ISRO...
-

 175Hacked
175HackedPopular Game Malware Affecting More than 1 Million Android Users
Do you love playing games on your Android tablet and smartphone? Well, the innocent games you play, could be a route to...
-

 222Cyber Events
222Cyber EventsDDoS Ransom Notes, to Honor or Not to Honor?
In the wake of cyber crimes, a DDoS (Distributed Denial of Service) attack is something to be on the look-out for. Lately,...
-
 184Surveillance
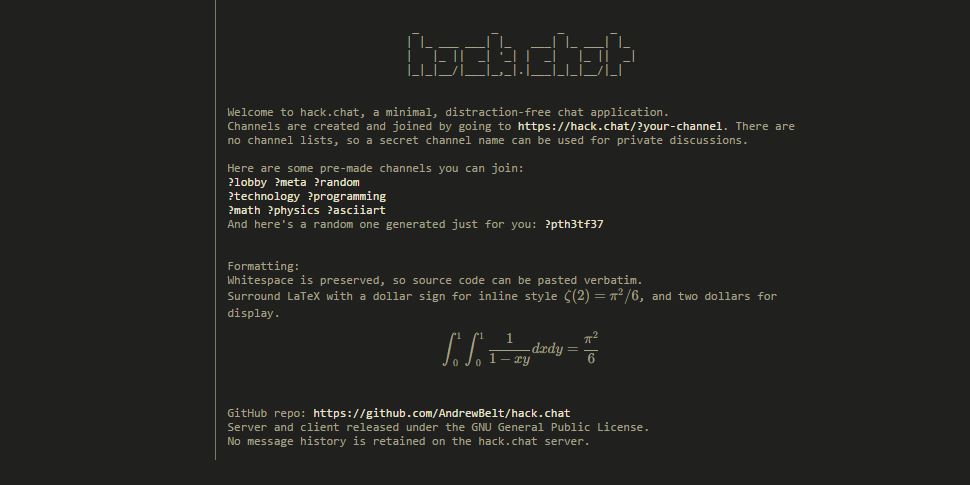
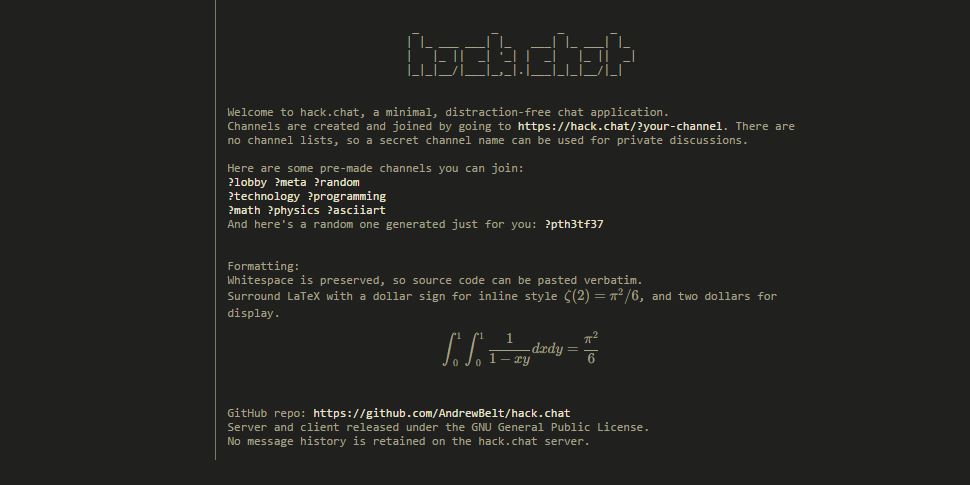
184SurveillanceHack.Chat – Instantly Create A Disappearing Chat Room and Chat Anonymously
From instant messaging to apps like WhatsApp and SnapChat, there are plenty of possibilities to chat on the Web, and many social...
-

 295Surveillance
295SurveillanceYou Can Now Delete Your Google Voice Search History
You know it’s easy to download and delete your searches from Google Search, but did you know you can also delete or manage...
-
 258How To
258How ToHow Hack.chat Makes Private and Disappearing Chatrooms in 5 Seconds
There is no dearth of instant messaging applications these days and people are addicted to Facebook Messenger, WhatsApp, SnapChat, IM on Twitter,...
-
 177How To
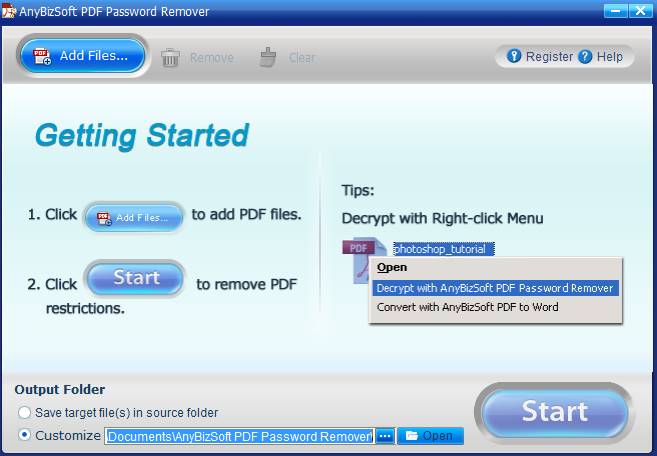
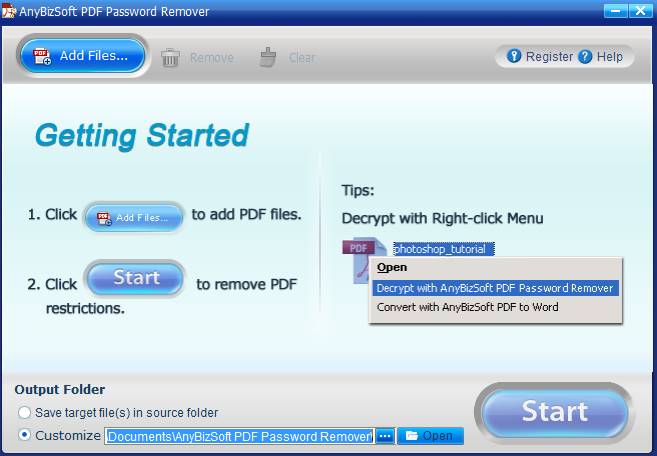
177How ToHow to remove password protection from PDF files
Now a days, we all save our data in a Word file or a PDF file. Some have basic information and some...
-
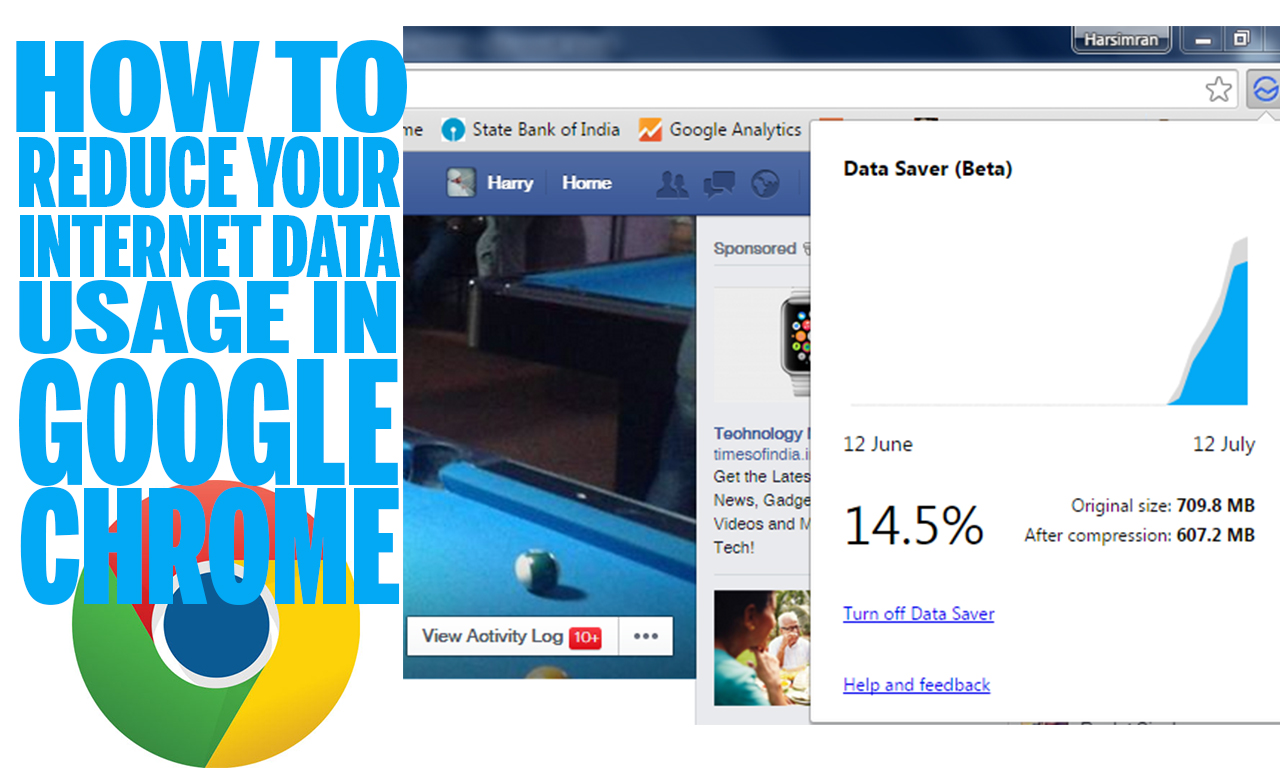
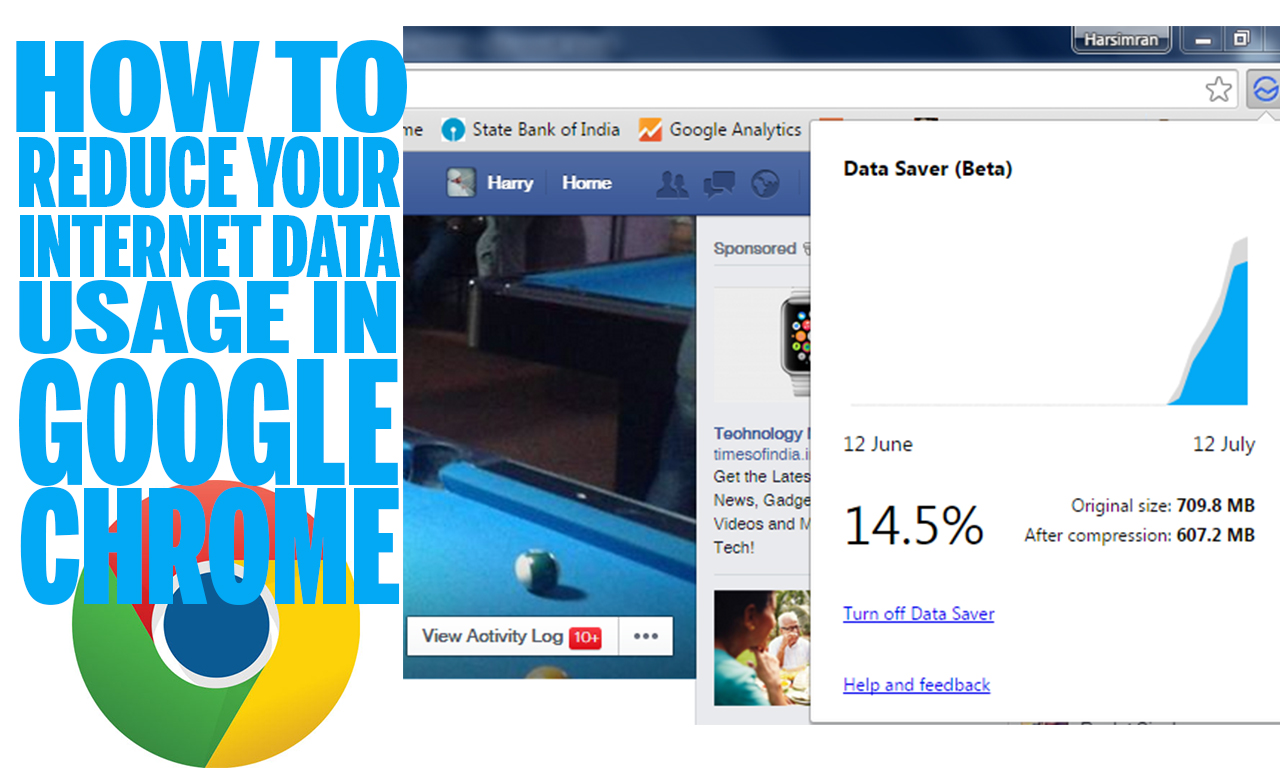 141How To
141How ToHow to reduce your Internet data usage in Google Chrome
Almost everyone uses the Internet now a days. Some people use mobiles and tablets where we all have to pay data usage...
-
 128Cyber Events
128Cyber EventsAnonymous Fights Animal Cruelty by Exposing Email Orders to Kill Bear Cubs
This weekend, Bryce Casavant who is a Canadian conservation officer was suspended from duty when he denied the orders to kill two...
-

 193News
193NewsOne Million Android Users Infected With Facebook Hacking Malware Apps
Ever wondered about the number of users an Android-based malware app can infect after getting approved and published on the Google Play...
-
 294Geek
294GeekTop 15 Facebook Open Source Projects You Must Know
This is the first article of the series where we will be publishing about top open source projects made by big blue...
-
 128Cyber Crime
128Cyber CrimeBeware: Hackers Target Users with Adobe Phishing Scam
Taking Advantage of Hacking Team Leak, Hackers Target Users with Adobe Phishing Email. As you know Adobe flash is a software used...
-
 203Hacked
203HackedPirate Bay Founders Not Guilty in Criminal Copyright Case, Court Rules
The Pirate Bay is one of the most popular torrenting sites of the world, and it has constantly been into the limelight...
-

 312Data Security
312Data SecurityBeware of Fake Apps: Google Deletes Fake BatteryBot Pro Malware App
Last week we reported hackers are developing Android malware every 17 seconds, making it one of the most vulnerable OS ever. Now...
-
 187News
187NewsObama’s Election Campaign Social Network Domain Hacked by Yemeni Hacker
A Yemeni hacker going with the handle of “Lov3rDns” has hacked and defaced the official social network domain of U.S president Barack...
-

 225Cyber Crime
225Cyber CrimeSextortionist jailed for life, FBI searching for 350 online victims
31-year old Lucas Chansler is set to serve 105 years, perhaps the remaining days of his life, in prison after admitting to...
-

 92Hacked
92HackedWhatsApp Will be Banned Soon In UK Over Security Reasons
Get ready to bid farewell to your favourite messaging apps. These could be the last days for Britons to use the immensely...
The Latest
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications
-
 Malware
MalwareNSA, FBI Alert on N. Korean Hackers Spoofing Emails from Trusted Sources
-
 Vulnerabilities
VulnerabilitiesFour Critical Vulnerabilities Expose HPE Aruba Devices to RCE Attacks
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Vulnerabilities
VulnerabilitiesWhen is One Vulnerability Scanner Not Enough?
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Vulnerabilities
VulnerabilitiesNew “Goldoon” Botnet Targets D-Link Routers With Decade-Old Flaw
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Data Breach
Data BreachHow to Make Your Employees Your First Line of Cyber Defense
-
 Malware
MalwareZLoader Malware Evolves with Anti-Analysis Trick from Zeus Banking Trojan




