Featured News
-
 219Geek
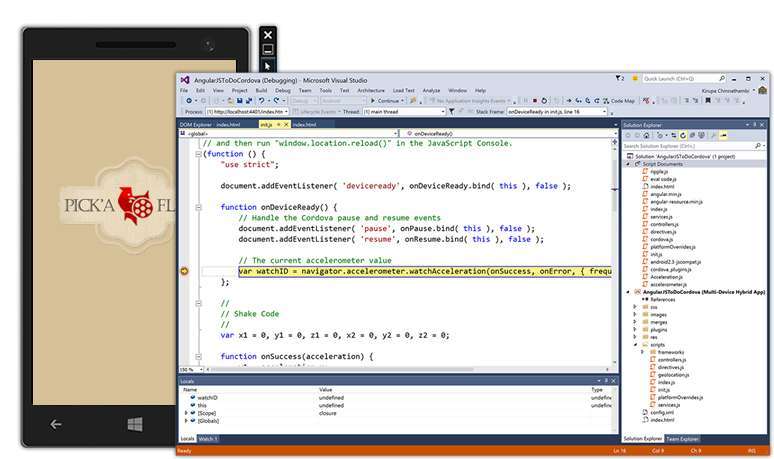
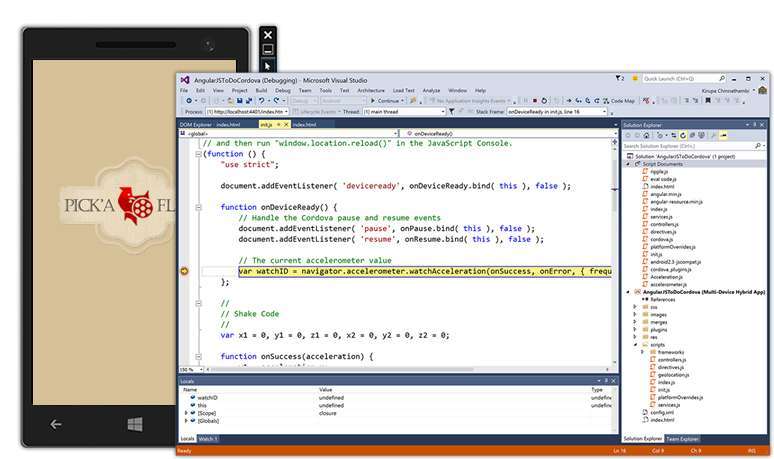
219GeekVisual Studio 2015 and .NET 4.6 Released, Download Now
Today is the Visual Studio 2015 and .NET 4.6 release day. These software from the house of Microsoft have finally graduated exiting...
-

 221News
221NewsHacknet , a real Hacking game.
Developed by Team Fractal Alligator, an Australian one-man studio, Hacknet is “an immersive, terminal-based hacking simulator for PC.” Here’s the official...
-

 132Scams
132ScamsMicrosoft advises ‘spoofed’ Skype users to change passwords
Skype users have been advised by Microsoft to change their passwords following reports that 'spoofed' messages are being sent without user permission.
-

 186Hacked
186HackedInstagram Can Totally Hijack Your Account And Give To Some Celebrity
How cool would it be if somehow your parents were Pitt’s and ended up to name you Brad, or a simple Messi...
-

 105Cyber Crime
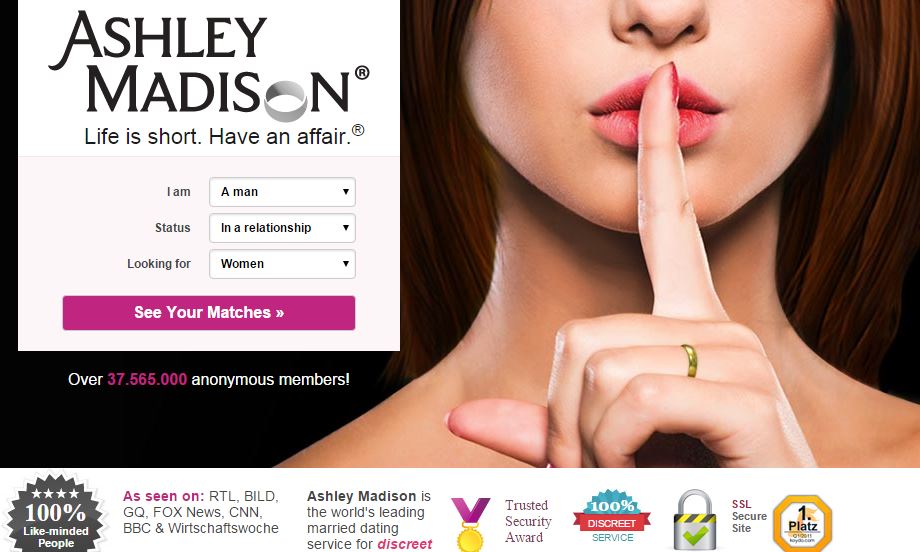
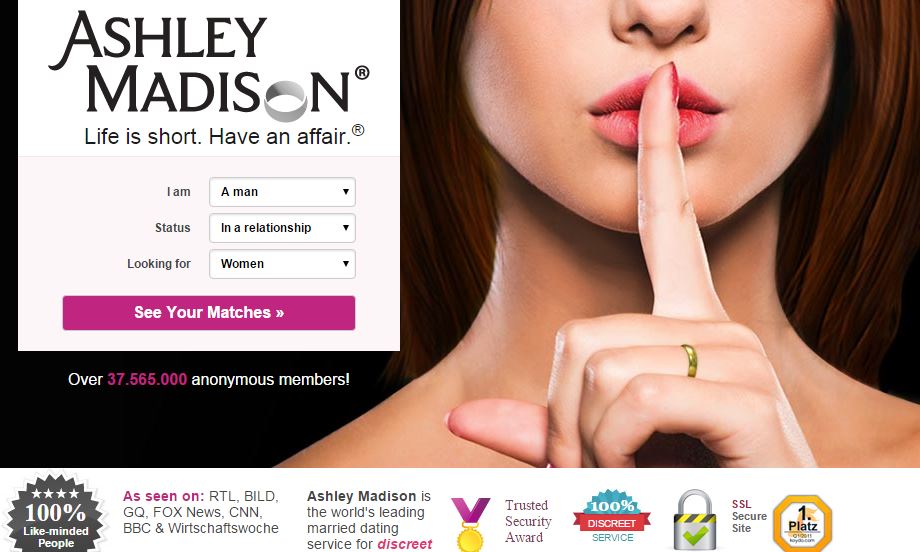
105Cyber Crime37 million relationship cheats could be exposed by Ashley Madison hack
The 37 million users of hacked infidelity site Ashley Madison are at risk of having their names and private details leaked, reports...
-
 388Hacked
388HackedMicrosoft: Free Windows 10 Upgrade Comes With 10 Years of Free Updates
Windows 10 is one of most talked about topics on various online forums. Microsoft is leaving no stone unturned to achieve its...
-
 268Hacked
268Hacked37 Million Adulterers Exposed, Online “Cheating” Site Ashley Madison Hacked
Online cheating website AshleyMadison.com has been hacked, and as a result, large chunks of data has been stolen. The compromised data has...
-
 199Hacked
199HackedCyberGhost Privacy Accelerator Program Offers €100,000 if You Can Make Web a Secure Place
“How Government secretly read your e-mails with this insane law?“ “Snowden’s Revelations: XKEYSCORE is NSA’s search engine.” “Real-Time Cyber Attacks across the globe. ““NSA’s...
-

 281Geek
281GeekTop Netflix Open Source Projects You Must Know
This is the 3rd post in the series covering top open source projects by most popular companies in the world. Today, we...
-
 333News
333NewsCyberwar: Pakistani President’s Website Hacked by Bangladeshi Hackers
Pakistani President Mamnoon Hussain’s website has been hacked by Bangladeshi hackers — 72 other Pakistani government websites have been hacked as well....
-

 232Data Security
232Data SecurityWindows XP Anti-Malware Support Terminated – 180 Million Users Left Vulnerable
Millions of Windows XP users are now left vulnerable to malware attacks as Microsoft has decided to terminate support and security updates...
-

 315Hacked
315HackedThis Hacked Gun Mounted Drone Shoots Bullet in Terrifying Video
The world is getting scarier each day. And I don’t mean the terrorist attacks or cyber threats or global warming, or least...
-
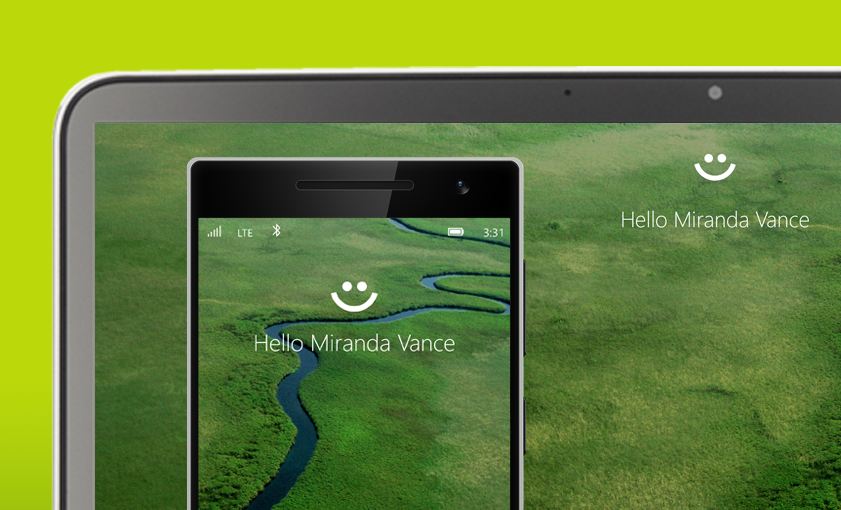
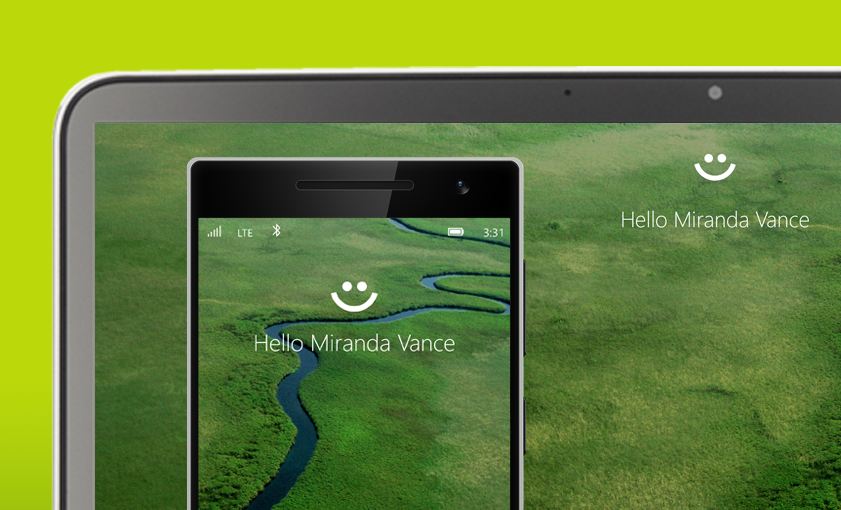 341Hacked
341HackedComplete List of PCs Supporting Windows Hello, the Password Killer Feature of Windows 10
With Windows 10’s Windows Hello feature, you will be able to log into your PCs without any password. Windows Hello users to...
-

 274Geek
274GeekMicrosoft Now Providing Support for Linux Users in Azure
Microsoft Azure cloud platform is very popular among Linux users and now Microsoft has announced that it will be offering limited support...
-
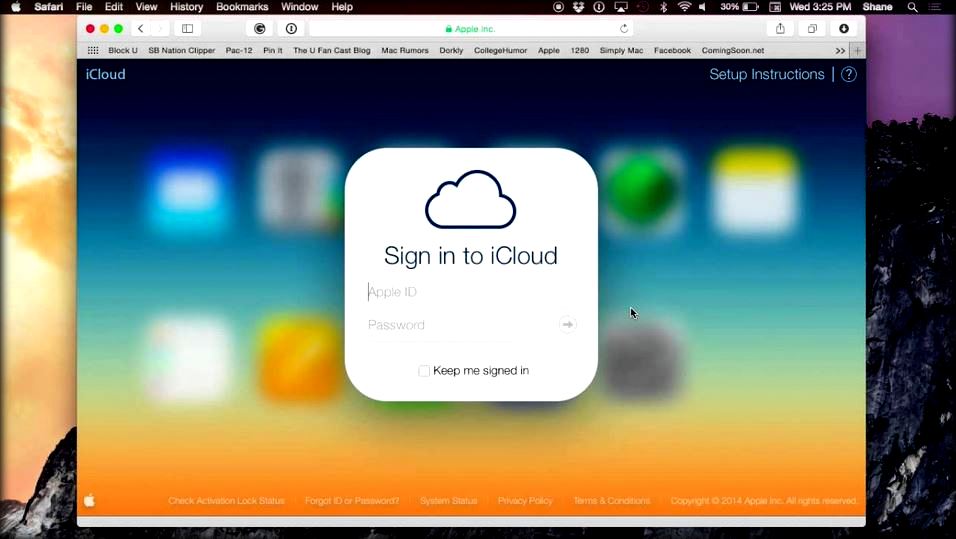
 168Hacked
168HackedHow Apple’s iCloud Drive Deletes Your Files Without Any Warning
iCloud Drive is one of the most-used Apple services as it’s a Dropbox-like solution to keep all your devices’ data in sync....
-

 65Cyber Crime
65Cyber CrimeHuge Morrisons data breach due to employee with grudge, court hears
A Morrisons employee with a grudge was responsible for posting personal data of nearly 100,000 staff onto the internet, a court heard.
-

 319Hacked
319HackedFBI Used Hacking Team’s Help to Track Tor User
Earlier this month, as a part of the massive breach at the infamous Hacking Team, numerous documents were leaked. Since then, analysts...
-

 179Hacked
179HackedAfter ProxyHam’s Disappearance, Here’s How to Make Your Own ProxyHam for Anonymous Browsing
About two weeks ago, we reported about the Raspberry Pi 2 based WiFi router that provided anonymous WiFi by putting you 2.5...
-

 69Cyber Crime
69Cyber CrimeBritish teenager sentenced for massive Spamhaus attack
British teen Seth Nolan Mcdonagh, aka "narko" has been sentenced for his role in a 2013 attack which slowed the internet around...
-

 186Malware
186MalwareUnited Airlines pays out 2 million flight miles for security bugs
United Airlines has paid out two million flight miles to two security researchers who uncovered 14 separate vulnerabilities in the company’s operation.
The Latest
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications
-
 Malware
MalwareNSA, FBI Alert on N. Korean Hackers Spoofing Emails from Trusted Sources
-
 Vulnerabilities
VulnerabilitiesFour Critical Vulnerabilities Expose HPE Aruba Devices to RCE Attacks
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Vulnerabilities
VulnerabilitiesWhen is One Vulnerability Scanner Not Enough?
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Vulnerabilities
VulnerabilitiesNew “Goldoon” Botnet Targets D-Link Routers With Decade-Old Flaw
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Data Breach
Data BreachHow to Make Your Employees Your First Line of Cyber Defense
-
 Malware
MalwareZLoader Malware Evolves with Anti-Analysis Trick from Zeus Banking Trojan




