Featured News
-

 324News
324NewsAnother OPM Hack Rattles 22 Million U.S. Government Personnel
The suspected Chinese hackers have once again managed to break into the United State government’s personnel management agency, leaving more than 22...
-

 345Lists
345ListsTop 5 Reasons Why Voat Could Become the Reddit-killer People Want
Just in case you are not aware of Reddit-revolt, here’s an update: Last week Reddit “Ask Me Anything” moderator Victoria Taylor was...
-

 73Cyber Crime
73Cyber CrimeMillions of records lost in huge OPM US data breach
The US Office of Personnel Management has admitted that the widely-publicised data breach in June was more wide-reaching than at first thought.
-

 186Malware
186MalwareSednit APT Group Meets Hacking Team
The infamous Sednit espionage group is currently using the Hacking Team exploits disclosed earlier this week to target eastern European institutions.
-

 209Geek
209GeekComputer Program ‘Helium’ Fixes Old and Rotten Code Faster than Expert Engineers
Do you know the meaning of term software rot or bit-rot? It’s the gradual deterioration in the performance of a software and...
-

 269News
269NewsNew York City Comptroller Office Website Hacked by Pro-Palestinian Hacker
Hackers have a passion for hacking, but the way they choose their targets is something hard to understand. Just like this unpredictable hack we...
-

 288Hacked
288HackedCongrats Hacking Team: After Governments, Now Terrorists Have Your Tools
This Sunday, in a massive data breach at the Hacking Team, about 400GB of internal documents, spyware source codes, and tools were...
-
 153Cyber Crime
153Cyber Crime“Internet Capacity Warning” Phishing Scam Aims to Steal Your Login Details
Let’s Welcome the New and Upcoming Phishing Scam —“Internet Capacity Warning.” Internet users are receiving an email that claims to be sent...
-

 88Cyber Crime
88Cyber CrimeAspiring singer jailed for hacking Madonna and stealing unreleased tracks
Breaking into the music business is one thing. Breaking into Madonna's computer without permission is quite another.
-

 302Cyber Events
302Cyber EventsAnonymous is Relatively Much Bigger Than You Anticipated
The global Anonymous network is relatively much bigger than your actual anticipation, a recent visual analysis by a University of Copenhagen graduate...
-

 170Data Security
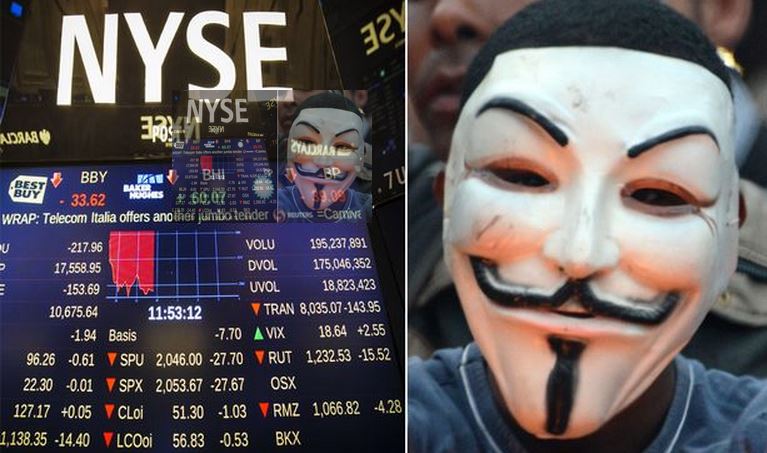
170Data SecurityWas Anonymous Behind NYSE Glitch? They predicted it a Day Before
The mysterious message Tweeted by Anonymous, the widely known hacktivist group, has left many wondering whether they were behind the cyberattack on NYSE,...
-

 103Malware
103MalwareAdobe rushes to patch Flash flaw under attack
Adobe Systems has issued a sizeable security update with patches for 36 vulnerabilities, at least one of which is currently under attack...
-

 96Malware
96MalwareApps on Google Play Steal Facebook Credentials
Over 500,000 Android users targeted by phishing apps harvesting their Facebook credentials. ESET detects these trojans as Android/Spy.Feabme.A.
-

 372Hacked
372HackedTor Honeypot: How to Hack True Identity of Tor Users
Tor is a free software that is widely used by people to protect their identity and avoid network surveillance. The Onion Router...
-

 317Data Security
317Data SecurityTerrorists Can Use Our Leaked RCS Spyware, Hacking Team Says
The infamous spyware dealer, Hacking Team, has now begun to complain that their recently leaked Remote Control System (RCS) spyware tool which...
-
 170Hacked
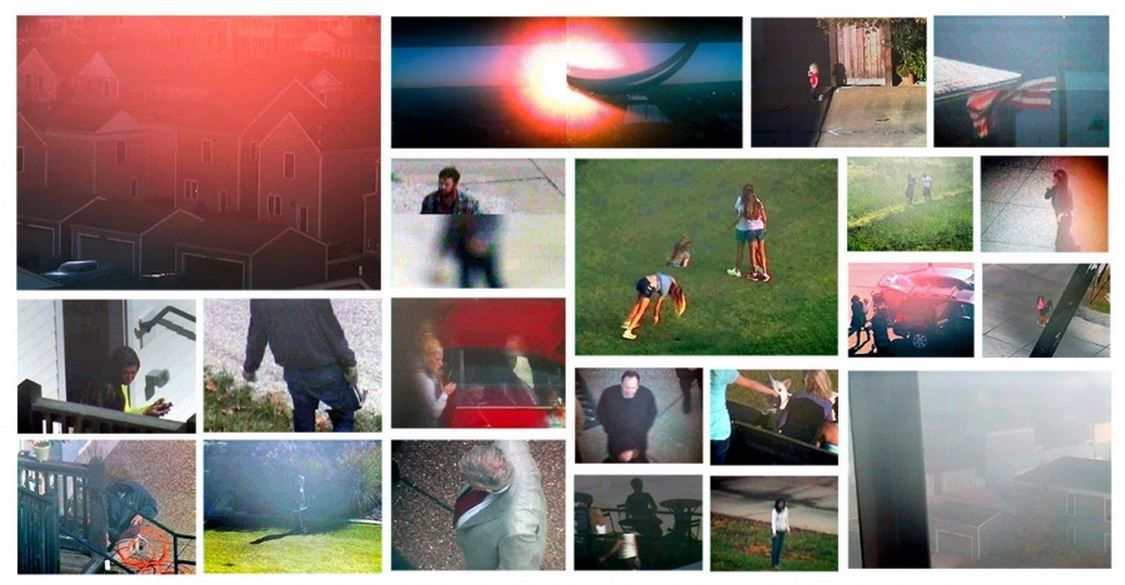
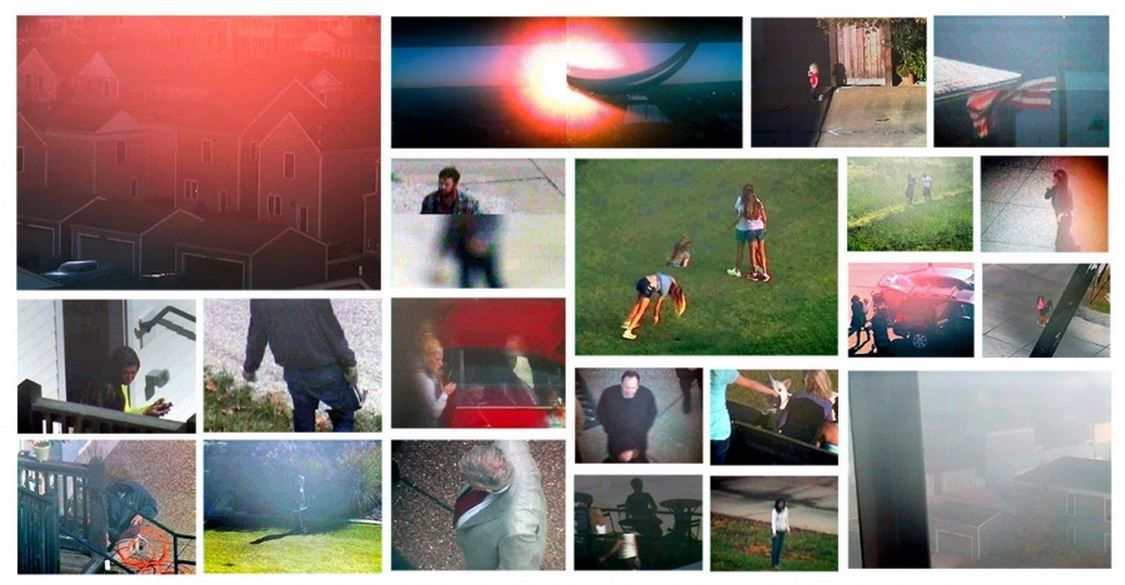
170HackedArtist Hacks Surveillance Cameras to Spy on Town and Makes Photo Album
The New Town photographs by Andrew Hammerand According to a report by IHS, there were 245 million surveillance cameras operating globally in...
-
 202Hacked
202HackedDid Anonymous Hack New York Stock Exchange?
When you have the power of anonymity, you can do things that are unimaginable for others. The hacktivist group Anonymous is well-known...
-

 187Cyber Crime
187Cyber CrimeGoogle Docs Users Targeted with “Confidential Document” Phishing Scam
The purpose of this scam message is to steal Google Account Login credentials. Users are urged to click on a fake link...
-

 286News
286NewsSubdomain of U.S. Dept. of Energy’s Argonne National Lab Hacked by ISIS Hackers
Did you notice the pro-ISIS hackers are targeting high-profile websites without any restriction? Yesterday, we exclusively reported how the State Ministry for Euro-Atlantic...
-
 394How To
394How ToHow To Prevent Your Computer From Overheating
An overheating computer spells trouble. You would want your girlfriend to be smoking hot but trust me, neither you want your computer...
The Latest
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications
-
 Malware
MalwareNSA, FBI Alert on N. Korean Hackers Spoofing Emails from Trusted Sources
-
 Vulnerabilities
VulnerabilitiesFour Critical Vulnerabilities Expose HPE Aruba Devices to RCE Attacks
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Vulnerabilities
VulnerabilitiesWhen is One Vulnerability Scanner Not Enough?
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Vulnerabilities
VulnerabilitiesNew “Goldoon” Botnet Targets D-Link Routers With Decade-Old Flaw
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Data Breach
Data BreachHow to Make Your Employees Your First Line of Cyber Defense
-
 Malware
MalwareZLoader Malware Evolves with Anti-Analysis Trick from Zeus Banking Trojan




