Featured News
-
 173Cyber Crime
173Cyber CrimeHackers Target Users with “Facebook Account Recovery” Phishing Message
Researchers have spotted a j.mp shortened URL being shared by fake accounts within Facebook recently targeting users with phishing link. Hackers are sending...
-
 141News
141NewsWebsite of Nepali Embassy in US hacked, left with anti-American content
The official website of embassy of Nepal in Washington was hacked by a group of Moroccan hacker not happy with American invasion of Iraq and...
-
 75Cyber Crime
75Cyber CrimeIRS hacker attack puts US tax payers at risk
The IRS has admitted that for more than two months malicious hackers targeted its systems, and managed to gain access to information...
-
 330Cyber Crime
330Cyber CrimeUsing middle finger emoji in UAE: A crime that could land you in court
Dubai: If you are living in UAE, you should know the dangers of flipping middle finger at someone as it could land you in prison. Nonetheless,...
-

 214How To
214How ToHow To Add Pattern Lock Security On Windows
Every Android user should be familiar with pattern lock security system. Every Smartphone has the option called Patter Lock which is very popular...
-

 102Privacy
102PrivacyBluetooth fitness trackers ‘a threat to privacy’
Devices using Bluetooth Low Energy (BLE) to transmit their data can be intercepted by hackers, potentially exposing a trove of fitness data...
-

 387Password
387PasswordDissecting Linux/Moose: a Linux Router‑based Worm Hungry for Social Networks
A malware family that primarily targets Linux-based consumer routers but that can infect other Linux-based embedded systems in its path: Dissecting Linux/Moose.
-
 219Cyber Crime
219Cyber CrimeMoose – the router worm with an appetite for social networks
A new worm is infecting routers in order to commit social networking fraud, hijacking victims' internet connections in order to "like" posts...
-
 268Geek
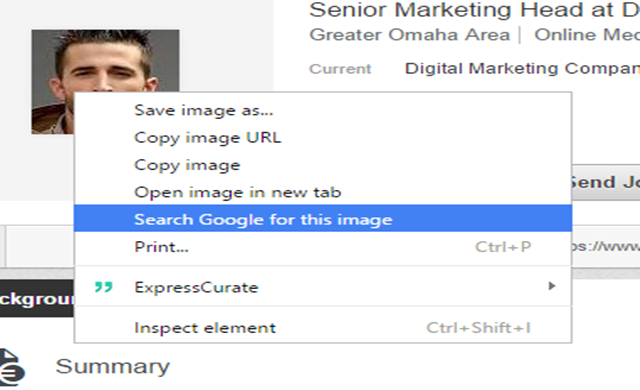
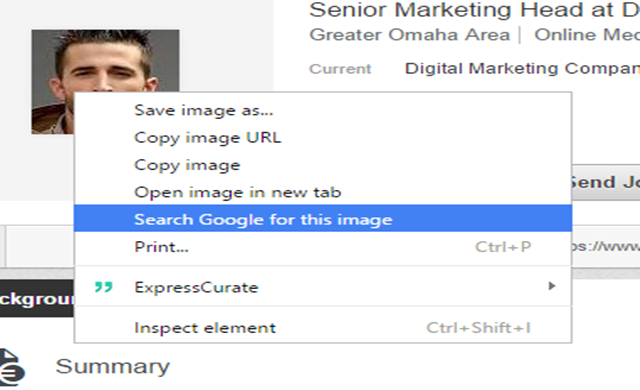
268GeekIdentifying Fake Social Media Profiles Possible with Google Image Search
Creating fake social media accounts has been the favorite trick of hackers and scammers for interacting with potential victims. However, thanks to...
-

 302Cyber Events
302Cyber EventsTeen hires attacker to DDoS his school district
A high school boy might have to face state and federal charges for allegedly hiring a third party and launching a DDoS...
-

 233Geek
233GeekDoes Wi-Fi Makes People Sick? Probably Yes!
From using PCs and cell phones to watch online movies and playing games, wireless technology has advanced greatly and made life easier...
-

 396News
396NewsHackers target Bitcoin Exchange BitFinex’ Hot Wallet
Reportedly BitFinex was hacked but due to strict security measures implementation just minimal amount was lost. BitFinex keeps more than 99.5% of...
-

 291How To
291How ToTips To Keep Your Android Device Safe and Sound
It would not be an exaggeration to say that the present age is the age of smartphones. They have invaded our lives...
-

 151Hacked
151HackedMozilla: Firefox Tracking Protection Speeds Up Web Pages by 44%
Do you know that not all web sites honor the native Do Not Track feature of your web browser? Even in the...
-

 69Cyber Crime
69Cyber Crime5 hackers who came over from the dark side
Five reformed hackers who turned their lives around to help in the fight against cybercrime, leaving their blackhat past behind.
-
 156Hacking Tutorials
156Hacking Tutorials6 Ways to Secure a Wireless Wi-Fi Network
Wireless Networking (Wi-Fi) has made it so easy for anyone to use Internet on your computer, mobile phones, tablets and other wireless...
-

 266Hacked
266HackedNSA Prepares to SHUT DOWN Mass Phone Tracking Program
As a result of a midnight session, the American Senate has voted down the USA Freedom Act- the basis of NSA’s mass...
-

 286News
286NewsAnonymous Breaches Thailand Senate Website against Human Trafficking
The online hacktivist Anonymous breached into the official website of Thailand Senate and Public Health Ministry, ending up leaking login credentials against country’s alleged...
-

 236News
236NewsWebsite of Uzbek Embassy in Kuwait hacked by anti-Assad Hacker
The anti-Bashar Al Assad hacker from Syria hacked into the official website of Uzbekistan Embassy in Kuwait and demanded governments around the world...
-
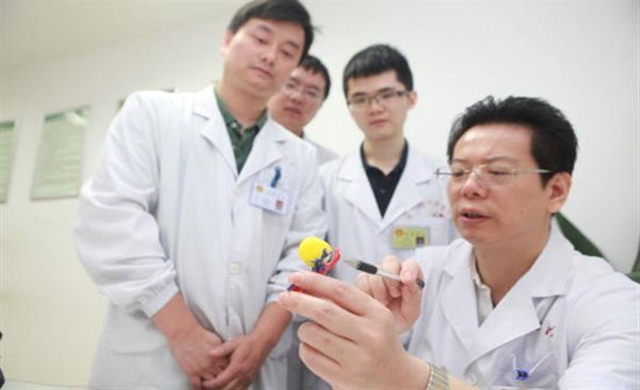
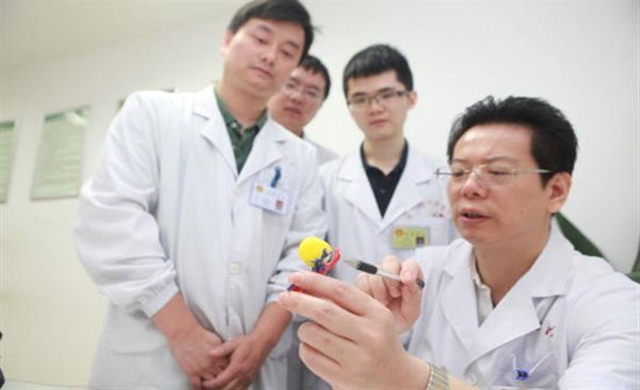 289Geek
289GeekMiracle Miracle! A woman’s kidney tumor cured by 3D printing
When it’s about performing surgeries on vital organs, today’s advanced imaging techniques such as CT scans, MRIs and ultrasound machinery have made...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




