Featured News
-

 85Cyber Crime
85Cyber CrimeHome Depot calls on court to dismiss consumer data breach case
The Home Depot has called upon a federal court to dismiss a lawsuit brought about by consumers claiming they were hurt by...
-

 90Cyber Crime
90Cyber CrimeOnline threats only illegal if intentional, rules Supreme Court
The Supreme Court has reversed the decision to convict a Pennsylvania man who directed violent online threats at his ex-wife, citing intent...
-

 238Data Security
238Data SecurityFacebook Adding PGP Encryption to Prevent Email Hacks
The feature of adding OpenPGP public keys to profiles is launched by Facebook to prevent your notification emails from prying eyes of...
-

 284News
284NewsJapan Pension Service Hack Affects Data of 1.25million People
Japan’s national pension system was hacked due to which personal data of 1.25million people got leaked. On Monday, the Japan Pension Service...
-
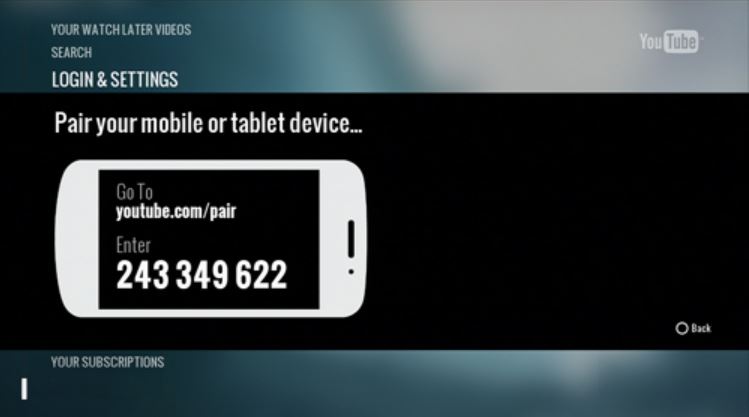
 567How To
567How ToHow To Control YouTube In PC With Your Smartphone Without Any App
Suppose you are chatting with your girlfriend and watching a movie or video on YouTube alongside, but you don’t want to touch...
-

 151Privacy
151PrivacyIs your GoPro camera secretly spying on you?
Poor choices of passwords can lead to your privacy being breached, after researchers revealed just how easy it could be for hackers...
-

 122Opinion
122OpinionHow goes the switch to Chip & Signature cards in the US?
With the deadline for the switchover now just months away, how are vendors doing? Have they begun the conversion already, or will...
-

 205How To
205How ToHow to record Android screen without Root
Screen recording may be an important part of your work if you are a youtuber. But some people like to record their...
-
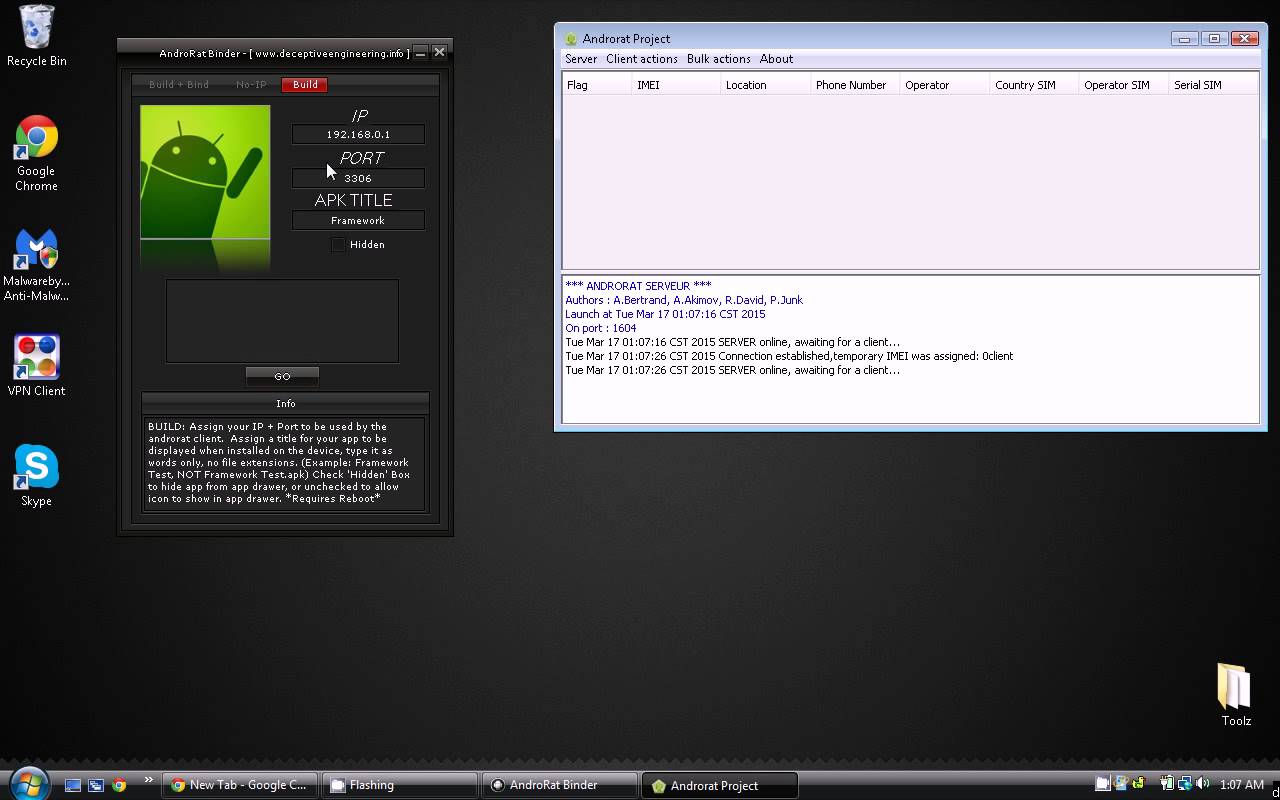
 297How To
297How ToHow To Hack Android Phones With Androrat
In this tutorial we are going to show you how to hack Android phones with Androrat. In our tutorials we only EVER hack...
-
Hacking Tutorials
Penetration Testing Procedures
Penetration testing (otherwise known as pentesting, or the more general security testing) is the process of testing your applications for vulnerabilities, and...
-

 206Data Security
206Data SecurityAre hackers experiencing karma in the Underground Economy?
The underground economy is a large group of websites that make it possible for hackers and fraudsters to trade illegal services and stolen...
-

 205Surveillance
205SurveillanceExperts Warn Killer drones and robots will Leave Humanity ‘Utterly Defenceless’
These small and agile drones have been designed to kill might be devastating for us and we could be left “utterly defenceless”...
-
 219Hacked
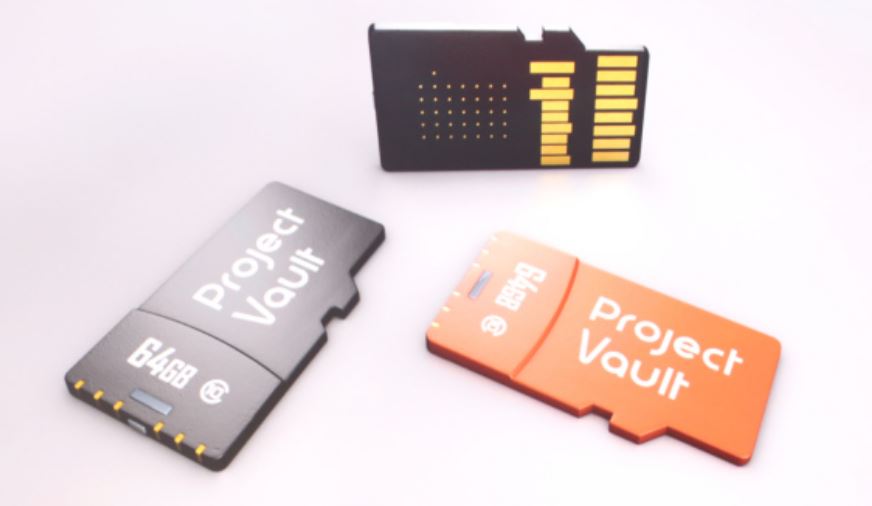
219HackedGoogle’s Project Vault: A Secure Computer On A Micro SD Card
From the stage of Google I/O 2015, Google’s Regina Duggan introduced something that wants you to forget the passwords and become one...
-

 333How To
333How ToHow to Record iPhone screen without Jailbreak
More than a billion people on this world have iPhones and iPads. Demand for the Apple devices are increasing very much these...
-
 251How To
251How ToHow to download torrent files using IDM
There may be many reasons to download torrent files using IDM. It may be that you get good speed using IDM, no...
-

 306Data Security
306Data SecurityiPhone Message Crash Bug now targeting Snapchat, Twitter, Mac OS X
Summary: The iOS bug that attacks via Messages app in iOS devices and effectively crashes them has now broken Twitter, Snapchat and...
-

 383Cyber Crime
383Cyber CrimeSilk Road Creator, Mastermind Ross Ulbricht sentenced to Life in Prison
Ross Ulbricht, 31, the accused brain and mastermind behind dark web marketplace Silk Road has been sentenced to life in prison on...
-
 229Geek
229GeekResearchers used “3D Printing” in tests for finding Cure of Type-1 Diabetes
Apparently, scientists are a step closer to reducing the grave effects of Type-1 Diabetes after discovering a way to implant insulin-creating cells...
-

 186Geek
186GeekFacebook now supports GIFs: Here’s how to post them
Facebook confirmed that it will now support animated GIFs on its News Feed, but at the moment not every user will be able to...
-

 317Surveillance
317SurveillanceNew Laws Force Google, Snapchat, WhatsApp to share chats with GCHQ
Summary: New surveillance laws will be formed to force the leading Internet firms such as Apple, Facebook and Google to hand over encrypted...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




