Featured News
-

 115Privacy
115PrivacyThe immortality of data (and people) in the digital age
In the future, everything around us will be managed by data, and those who have data will have power. So, will anonymity...
-

 149Scams
149ScamsHackers phish for data with fake Apple Watch giveaway
Apple fans keen to get their hands on the Apple Watch are advised to think before they click, after hackers exploited a...
-
 260Hacked
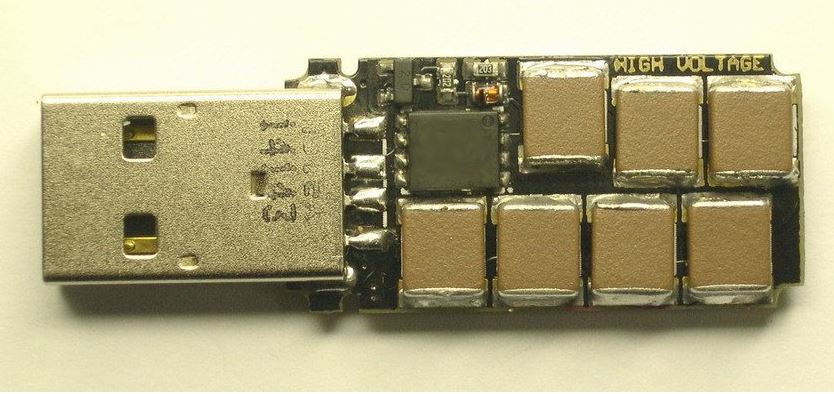
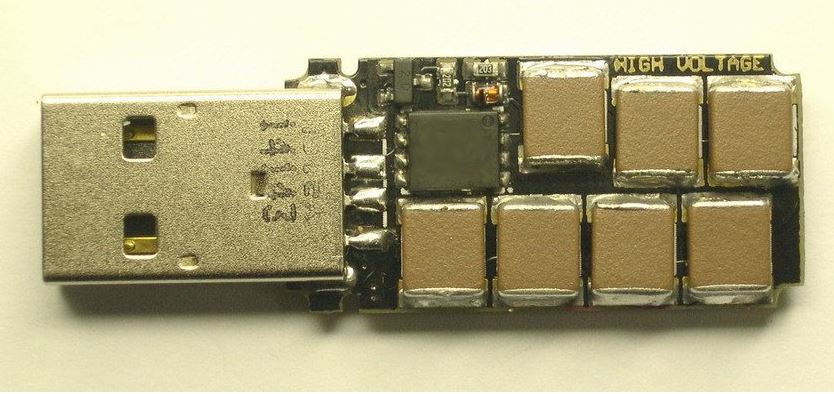
260HackedThis “Killer USB” Flash Drive Will Explode Your Computer
The Killer USB USB drives are known be humble creatures that help you out by transferring your data. But, what if a...
-
 105Privacy
105PrivacySuperfish: Lenovo goes on the bloatware offensive
Its been just under three weeks since February 19th, when Lenovo became entangled in a web of controversy over its preinstallation of...
-
 264Data Security
264Data SecurityWordPress SEO by Yoast’ Plugin Vulnerable to Hackers, Affecting Millions Worldwide
A number of websites have been put at risk due to a very popular plugin of the WordPress content management platform vulnerability...
-

 238Data Security
238Data Security‘Snowden Phone’ by FreedomPop vows to encrypt your calls and data
US Consumers looking for a wireless steal can now get encrypted free monthly phone service thanks to FreedomPop, the firm behind the...
-

 315Data Security
315Data SecurityUS Military to Hire 3,000 New Cybersecurity Professionals by 2016
Around 3,000 new security professionals will be added to the United States military’s infosec unit by 2016, according to reports. It says that...
-
 203Privacy
203PrivacyThe human cost of phone hacking
Phone hacking ruined the lives of celebrities, and - in at least one case - almost drove a victim to suicide.
-
 253News
253NewsRedHack Hacks Istanbul Police Assoc. website, Tributes Berkin Elvan on 1st Death Anniversary
The online Turkish hacktivist group RedHack has hacked and defaced the official website of Istanbul Police Association in tribute to Berkin Elvan, a 15-year-old teenager who...
-

 318Data Security
318Data SecurityVulnerability in WordPress Plugin Allows Hackers to take full control of website
WordPress’s MainWP Child Plugin has vulnerability… and it is very much exploitable. Researchers at Sucuri have identified a vulnerability in the MainWP...
-

 334News
334NewsFacebook Login Bug Lets Hackers Takeover User Accounts with Reconnect Tool
Even after almost a year, Facebook apparently has failed to fix a bug that lets attackers hijack accounts on sites that leverage...
-

 236Surveillance
236SurveillanceStop spying on us: Wikipedia sues NSA over mass Internet surveillance
A lawsuit has been filed against NSA (National Security Agency) to preserve the rights of the 500 million Wikipedia users who visit...
-

 75Cyber Crime
75Cyber Crime80 percent of global merchants fail card data security tests
Around 80 percent of global merchants including retailers, financial institutions and hospitality firms have failed interim tests which show they are not...
-

 305Geek
305GeekRegistrations for Google Code Jam 2015 Now Open
Google has opened the registration for the 12th Annual Google Code Jam competition for programmers. To register yourself, click on the blue...
-

 145Geek
145Geek‘Sesame’ – World’s First Touch-Free Smartphone That Disabled can Control With A Nod
Sesame Enable is the world’s first touch-free smartphone that will allow users (especially disabled) to use without even using their finger. Just...
-
 300Geek
300GeekCIA spent years to hack iPhone, iPad, say new leaked Snowden documents
American journalist Glenn Greenwald who’s running The Intercept publication has shared more shocking documents obtained from the ex-NSA spy Edward Snowden. The latest revelation...
-

 267Data Security
267Data SecurityCops Need Warrants To Get Phone Location Data
A number of states already have laws preventing the police from prying on your phone’s location history without a warrant, but they...
-

 201Privacy
201PrivacyUS lawmakers want taxi apps to check driver fingerprints
Ride-sharing taxi apps Uber, Lyft and Sidecar have been asked by US lawmakers to adopt fingerprint-based background checks for their drivers,
-
 302News
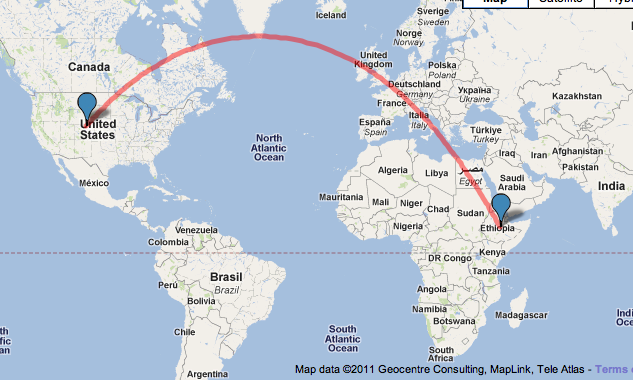
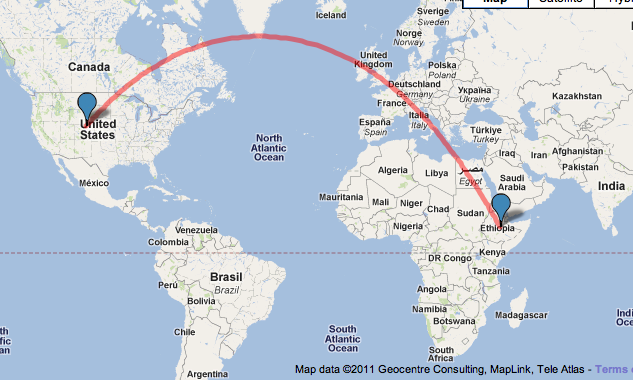
302NewsEthiopia is Hacking US Journalists in Virginia Using Spyware
Italy’s security firm Hacking Team is providing Ethiopia with off-the-shelf spyware, and have been expanding their repressive reach far overseas in the...
-

 142Cyber Crime
142Cyber CrimeUS military looks to 3,000 new security hires by 2016
The United States' military is looking to hire 3,000 cybersecurity professionals to man its infosec unit over the next nine months.
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




