Featured News
-

 206Data Security
206Data SecurityProtecting Your Smartphone From Government Spies amid NSA SIM Hack
With the recent reports making media headlines about how the NSA and GCHQ have compromised millions of SIM keys manufactured by Gemalto,...
-

 1.8KPrivacy
1.8KPrivacyKris Jenner reveals naked video could be leaked in iCloud hack
Kris Jenner is reportedly being blackmailed over a naked video that was stolen from her iCloud and could be released in the...
-

 251How To
251How ToHow Everyone Can Get Whatsapp Voice Calling Feature Right Now
[Updated] A recent update in the instant messaging app WhatsApp has rolled out the WhatsApp voice calling feature to everyone. Now, Whatsapp...
-

 200Data Security
200Data SecurityHow pervert security guards stalk women via CCTV
Women Stalked by Security Guards via CCTV – “Sleaze File” contains images of pretty women Five security guards of a high-profile shopping complex...
-

 314News
314NewsSnowden Leak: NSA, GCHQ hacked millions of SIM encryption keys, including yours?
The US surveillance agency, National Security Agency (NSA) along with its British counterpart the Government Communications (GCHQ) has compromised one of the...
-

 341Cyber Crime
341Cyber CrimeFacebook “Copyright Violations” Message: A Phishing Scam
Researcher dedicated to debunking hoaxes and exposing scams, have discovered a phishing scam doing rounds on the Facebook. It comes as a...
-
 242How To
242How ToSpytector Employee Monitoring Made Easy (Review)
It is somewhat a proven fact that Computer & Internet have brought a new era of productivity into the human life in...
-
 336How To
336How ToHow To Make Mozilla Firefox Faster For Web Browsing
Firefox browser from Mozilla is one of the most popular web browsers available. It has a big user base and market share. Mozilla...
-
 132Privacy
132PrivacyFer O’Neil: Say What? Required contents of notice in data breach notifications
With so many data breaches happening these days, Americans are getting a lot of breach notification letters and emails, but do they...
-
 199How To
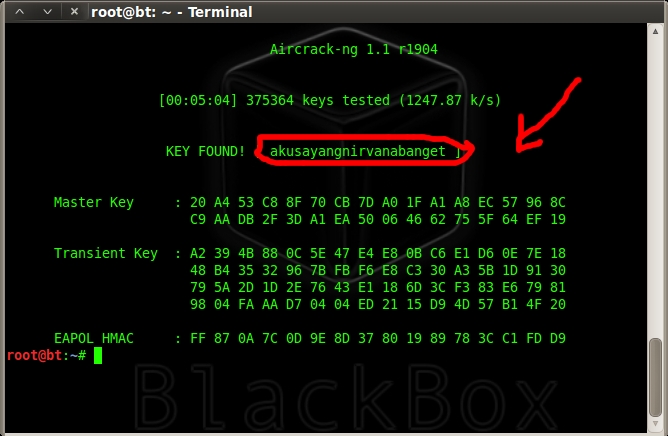
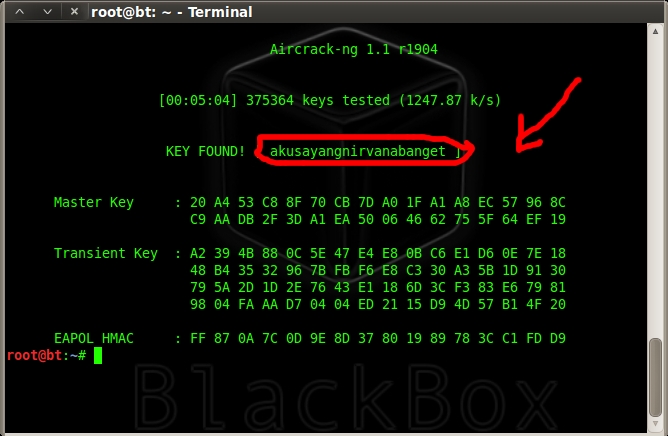
199How ToCracking WPA/WPA2 – PSK Encryption
About a month ago, to my embarrassment, I learned that my Wi-Fi password was so weak that even my 10 year old...
-

 207Scams
207ScamsLenovo and Superfish? Don’t panic, you may not be affected
Lenovo's installation of a security-breaking app called Superfish on some computers has customers justifiably angry, but some folks are now unnecessarily confused...
-

 432Privacy
432PrivacyLenovo apologizes over pre‑installed tracking software
Lenovo has issued a public apology, admitting it "messed up badly" by selling laptops with a controversial tracking software pre-installed.
-
 322Hacked
322HackedHackers Versus Cyber Criminals: Know the Difference
Short Bytes: People are often confused between two terms: hackers and cyber criminals. In this article, I’m sharing a video that tells...
-
 153Hacked
153HackedHow to Check if Your Lenovo is Infected with Superfish Adware and Remove it
Lenovo, the World’s largest PC maker, had pre-installed a virus-like software which makes the computer vulnerable to the hacking attacks. These laptops...
-

 280Geek
280GeekTop Programming Languages on GitHub, JavaScript Tops the List
Hello Everyone, Yesterday I wrote about the what code should you learn in 2015?. Today I’m covering the trends of the top programming...
-
 201Cyber Events
201Cyber EventsOpSaudi: Hackers Shutdown Saudi Bank Website
On Wednesday 17th Feb, 2015, a group of hacktivists calling themselves “The oppressed defenders” conducted a cyber attack on Saudi Arabian based bank AlJazira in...
-

 246How To
246How ToHow to Convert Scanned PDF and Images to Text Using Google Drive
Last month I felt the need to convert some image to editable text, so I searched the web and came across few...
-

 340Geek
340GeekOver 60% of Famous Dating Apps Expose Smartphones to Hackers
Over 60% Dating Apps Detected Unsafe by IBM Security – Popular Dating Apps Making Users Vulnerable to a Variety of Cybercrimes. Mobile Dating...
-

 185News
185NewsBigFish Games hacked; sensitive data compromised
Hackers have breached the billing and payment pages of BigFish Games and stolen sensitive information, according to the company’s notification letter published...
-

 95Password
95PasswordHacker puts words into wrestler’s mouth in WWE Twitter hack
WWE superstar Antonio Cesaro was the victim of a Twitter hack this week, as a wrestling fanatic hacked his account to vent...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks




