Featured News
-

 99Cyber Crime
99Cyber CrimeWatch how car hackers can disable brakes and steal your personal data
Modern cars are more and more dependent on computer systems. And guess what? They can be hacked.
-
 328Hacked
328HackedHacktivist Group Anonymous Takes Down ISIS Social Media Accounts (#OpISIS)
The hacktivist group Anonymous has attacked the terrorist organization Islamic State (ISIS) on a large scale. ISIS has a very strong social...
-
 276How To
276How ToHow To Become A Data Scientist in Simple Steps: The Infographic
IBM defines a data scientist as an individual evolved from the data analyst or business role. The person needs a solid foundation in...
-

 138Scams
138ScamsAnthem hack victims hit with phishing scams
Victims of the Anthem Inc health insurance hack are being bombarded with phishing scams including fraudulent emails and cold calls, reports Slashgear.
-

 143Privacy
143PrivacyUK Government publishes its guidelines for ‘equipment interference’
The British government has released a document outlining the rules that British spy and law enforcement agencies have to follow in their...
-

 265Scams
265ScamsCommon eBay scams and how to avoid them
Buying and selling on eBay can be great, but it can also be fraught with risk. Here are some of the most...
-

 127Privacy
127PrivacyStop talking in front of Samsung TVs… if you value your privacy
Your internet-enabled Samsung Smart TV could be listening to everything you say, and sharing it with third parties.
-

 276Hacked
276HackedUK Government Releases its Hacking Guidelines, But What About the US?
It’s is an undeniable fact that different governments use hacking as a security and a way to keep an eye on its citizens...
-

 84Hacked
84HackedLeaked Picture of Samsung Galaxy S6 Hints At 5 Different Versions
As the launch dates of anticipated products approach, the leaked pictures and videos start pouring in. Samsung did an amazing job till now...
-

 328Geek
328GeekHow is Ubuntu Phone Different from Android, iOS and Windows?
The world’s first Ubuntu phones have arrived and they are available online. Here I’ll be talking about the difference this Ubuntu phone brings to...
-

 266Geek
266GeekWorld’s First Ubuntu Smartphone Aquaris E4.5 Goes On Sale
World’s First Ubuntu based Smartphone will go on sale for just €170 in Europe via BQ.com through a series of flash sales. Ubuntu announced...
-
 107Malware
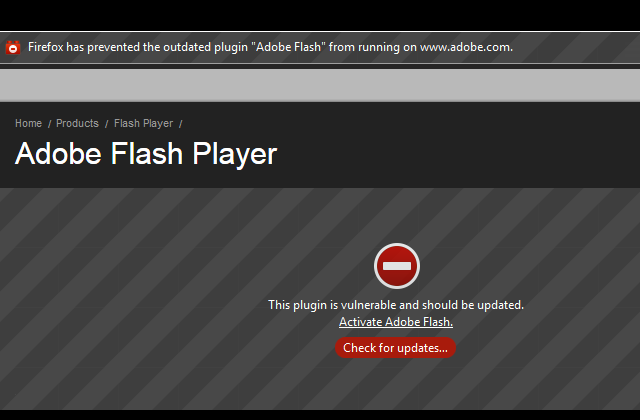
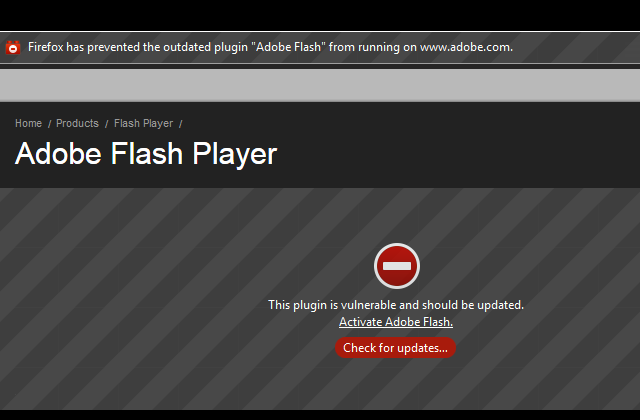
107MalwarePatch Now – Adobe Vulnerabilities Under Attack
This has not been a great week for Adobe; they have been scrambling to fix a number of critical vulnerabilities in their...
-

 83Cyber Crime
83Cyber CrimeAustralian cybersecurity video plays dumb to raise awareness, but will it work?
A new cybersecurity video from the Australian Cyber Security Centre (ACSC) has taken an unusual approach to raising awareness, playing dumb in...
-

 238News
238NewsSubdomain of Arizona Army National Guard website hacked by 3xp1r3 Cyber Army
The famous Bangladeshi hackers from 3xp1r3 Cyber Army are back in action. This time the hackers hacked and defaced the sub-domain of the...
-

 109Cyber Crime
109Cyber CrimeAnthem breach: 5 defensive tips to take now
Yesterday the Anthem breach, the biggest healthcare-related breach to date was announced, as attackers accessed a database containing the records of current...
-

 332News
332News“Stop Supporting ISIS”: Anonymous Kurdistan Hacks Turkish Govt. Websites
On Thu, 02 Jan 2014, a Kurdish hacker going with the handle of Anonymous Kurdistan & Muhmad Emad hacked two Turkish government...
-

 136Mobile Security
136Mobile SecurityAmerica is the leading developer of “risky mobile apps”, claims report
A survey of more than a million apps on the Google Play and iOS App Store has found that more than 40...
-

 133Cyber Crime
133Cyber CrimeFake WhatsApp for Web Spams the Internet, heaven for cyber criminals
The CEO of WhatsApp, Jan Koum informed on January 21 that the very popular and well-known mobile application has a web client...
-

 136Privacy
136PrivacyAnthem hack could affect 80 million health insurance customers
Anthem Inc. has suffered an attack on its database which is likely to be the biggest data breach ever disclosed by a...
-
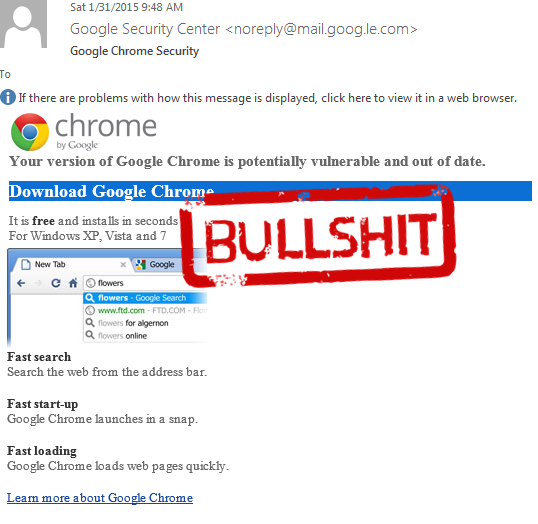
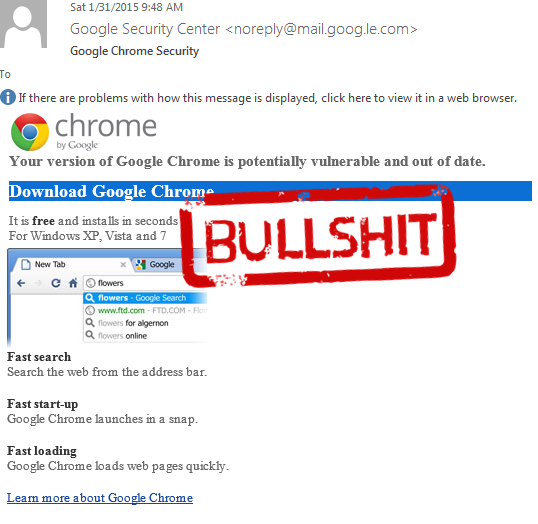 292Cyber Crime
292Cyber CrimeFake Google Chrome update leads to CTB Locker/Critroni Ransomware
A ransomware kind of threat has been on the loose that works by encrypting the data on the infected computer and then...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks




