Featured News
-

 266Data Security
266Data SecurityEmail titled “My New Photo ;)” actually Contains Malware
Email titled “My New Photo ;)” actually Contain Malware – A .Zip file has an attachment Supposedly containing the promised image. Summary: Hackers,...
-

 282Data Security
282Data Security16Mn Devices Compromised by Sophisticated Mobile Malware: Study
According to a study by Alcatel-Lucent’s Motive Security Labs, users around the world are being spied upon by extremely sophisticated mobile malware...
-

 206How To
206How ToHow To Install Windows 10 on Your Phone
Since the very first announcement of Windows 10 by Microsoft, phone users were eager to get their hands on the latest version...
-
 273Cyber Events
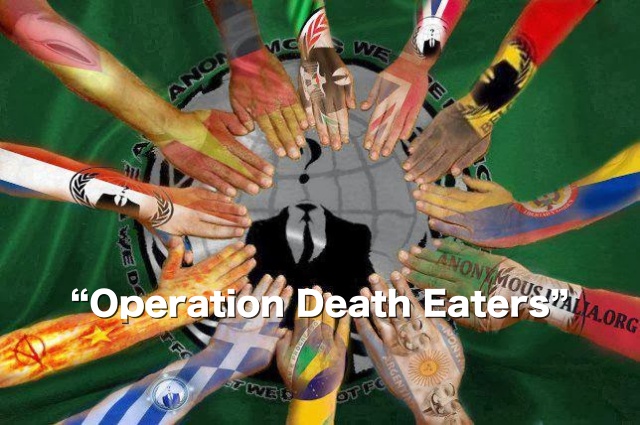
273Cyber EventsOpDeathEaters: Anonymous to hunt “elite” class pedophiles tonight
The online Hacktivist group Anonymous has announced to expose the “elite” class pedophiles involved in or covering-up the child sex abuse, including the senior Westminster figures. The...
-
 307Geek
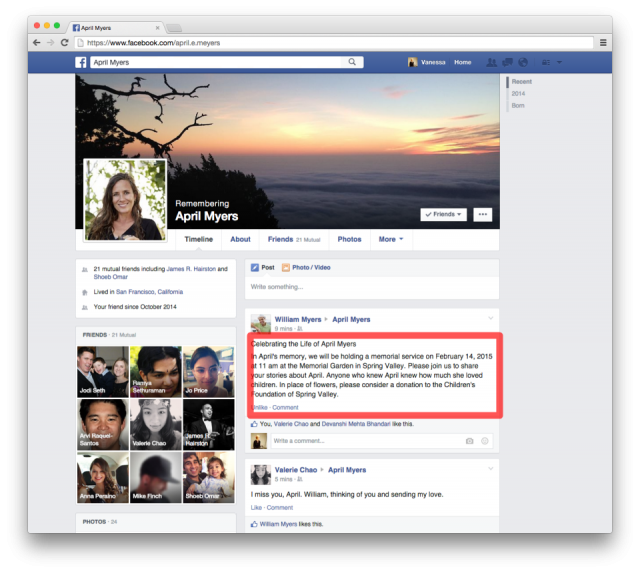
307GeekYou can now decide what will happen to your Facebook profile when you die
Can you decide what happens to your Profile Page after your Death? Facebook can! While rolling out its latest update on Thursday,...
-

 300News
300NewsStandard Chartered Bank hacked — Hackers stole money Via ATMs
Customers of Standard Chartered Bank, Pakistan were recently left stunned after they received transaction alerts via email and SMS. They were informed...
-
 259Data Security
259Data SecurityA Bug can remove all your Facebook Photos within no time
Researcher discovered a flaw that could help him Delete photos from Anyone’s account. To delete someone’s pictures from Facebook is certainly not...
-
 107Cyber Crime
107Cyber CrimeSexy Russian scammers would love to break your heart this Valentine’s Day
That message you received from a sexy Russian lady calling you Mr Dependable? Sorry to burst your bubble, but it's too good...
-
 253Hacked
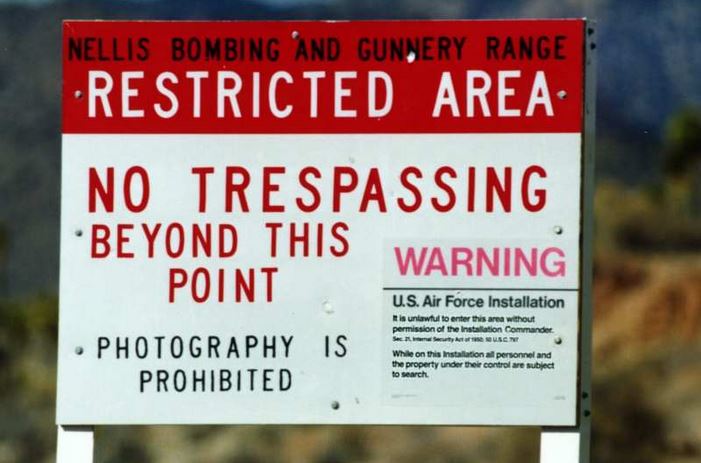
253HackedTop 10 Facts about Area 51 – One of the Best Known Secret Places on Earth
The U.S. military installation, Area 51 located about 100 miles north of Las Vegas, is one of the most known secret and...
-
 322Cyber Crime
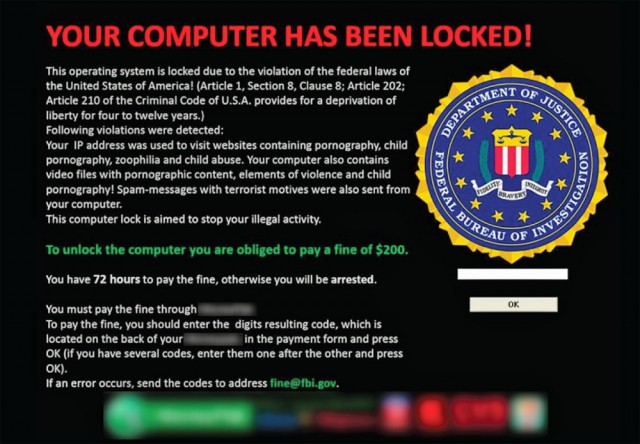
322Cyber CrimeRansomware: Cyber-hijacking Malware now has a new deadly face
Everything formidable is often associated with its negative half and the same can be said of the internet. The origins of functional...
-

 150Social Media
150Social MediaFacebook exploit allowed attackers to remotely delete photos
A Facebook hack that allowed attackers to remotely delete any photo they wanted to from the social network has been patched by...
-

 92Privacy
92PrivacyElectronic health records and data abuse: it’s about more than medical info
After the Anthem mega-breach, questions abound about possible abuses of medical data. Here is a breakdown that offers some context.
-

 281How To
281How ToList of Known Issues in Windows 10 Preview for Phones and Workarounds
Today Microsoft released the very first build of Windows 10 Technical preview for phones. Just like the other previews, it is incomplete...
-

 300Cyber Crime
300Cyber CrimeBeware: eBay ‘Registration Suspension’ Phishing Scam Email targeting users
An email, which appears to be sent from eBay, informs that due to the inaccuracy of your credit card information, your account...
-
 232How To
232How ToHow to Fall in Love With Anyone With By Using an App: Love Actualized
Few weeks ago, an article was published in The New York Times. The article talked about a set of 36 questions and...
-

 335Data Security
335Data SecurityDARPA Builds ‘Memex’ Deep Web Search Engine to Track Sex Traffickers
A project had been announced by the U.S government’s Defense Advance Research Projects Agency (DARPA) last year which was to create a...
-

 232Data Security
232Data SecurityCritical Vulnerability Allows attacker to have full control over LG Smartphones
Search-Lab Ltd. discovered a serious security vulnerability in the On Screen Phone protocol used by LG Smart Phones. A malicious attacker is...
-
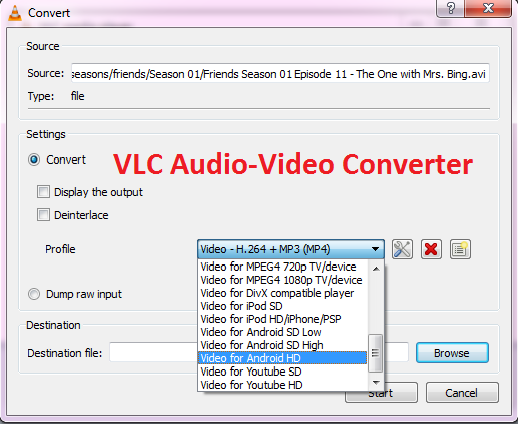
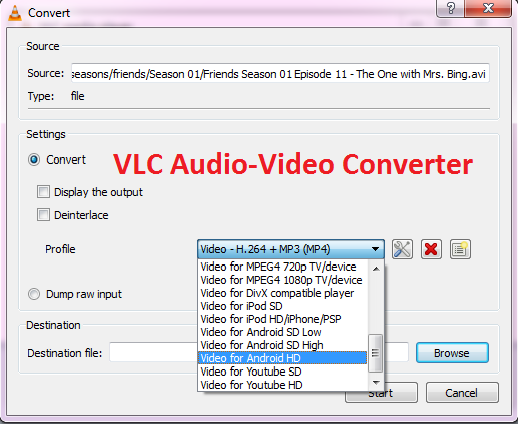 556How To
556How ToHow to Convert Audio or Video Files to Any Format Using VLC?
You can’t deny the fact that sometimes converting audio and video to some other format becomes one heck of a task. We...
-
 247Surveillance
247SurveillanceDEA Making Huge Photo Database of Country’s Drivers, vehicles’ number plates
DEA Maintaining Massive database of the country’s drivers and vehicles’ number plates – Database is used by DEA to track car owners. In...
-

 270Banking
270BankingMyCoin closure leaves $387 million missing in investor funds
Investors fear they may have lost up to $387 million after Bitcoin exchange MyCoin shut down this week, reports ZD Net.
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




